Immutability Without Identity Isolation Is a Lock With a Skeleton Key.
Most immutable backup implementations are compliance theater. Object Lock is configured. WORM storage is provisioned. The retention policy is set. The dashboard shows protected. None of that matters if the management plane that set the lock can also unset it — and in most environments, it can.
Organizations conflate immutable storage with hardened data. They are not the same. Immutable storage is a feature a storage platform provides. Hardened data is an architectural posture that survives adversarial conditions — where an attacker who has owned the environment for days, deleted the backup catalog, and shortened the retention window still cannot reach the data they need to make recovery impossible.
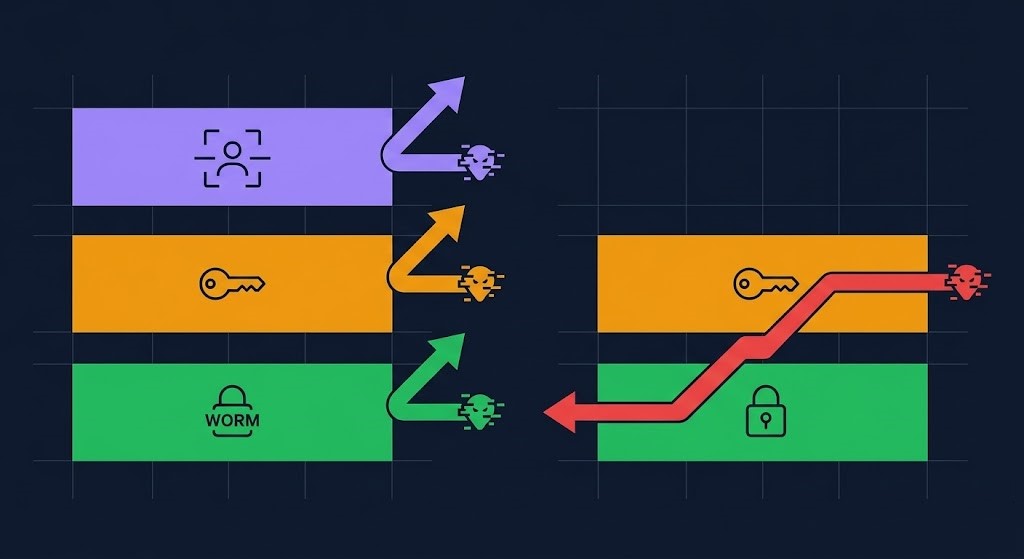
Data hardening operates across three integrated layers. Immutability — the data cannot be deleted or modified during a defined window, enforced at the storage layer, not the management layer. Encryption — the data cannot be read without a key that lives in a separate trust domain from the data itself. Identity isolation — the data cannot be reached by any credential that exists in the compromised environment. Ransomware defeats all three when they are not integrated. Most architectures implement one and assume the others follow.
This page covers the architecture that makes hardening real — not the configuration that makes it appear real. The Data Protection Architecture pillar covers the broader three-plane framework. The Backup Architecture page covers the recovery mechanics that hardening exists to protect. This page covers the layer between them — the architectural controls that determine whether data survives destruction.
WINDOW
SEPARATION
BOUNDARY
ISOLATION
LEVEL
RADIUS
Before the sections that follow, one mental model distinction to plant: time-bound immutability defines how long data cannot be deleted. Authority-bound immutability defines who — if anyone — can override that window. Most implementations are strong on time-bound and silent on authority-bound. The attack surface is always the authority model, not the retention timer.
What Data Hardening Actually Is
Data hardening is three disciplines operating as an integrated architecture. Each one addresses a different attack vector. None of them substitute for the others.
Immutability prevents destruction. WORM storage, object lock, snapshot lock policies — the controls that make data undeletable and unmodifiable during a defined retention window. Immutability addresses the ransomware tactic of deleting backup catalogs and snapshot schedules before encryption runs. It does not protect data that can be read without authorization, and it does not survive identity compromise if the authority model is shared with the compromised environment.
Encryption prevents unauthorized reading. AES-256 at rest, TLS in transit, customer-managed keys in a separate trust domain — the controls that make data unreadable without a key that exists outside the compromised environment. Encryption addresses exfiltration and unauthorized access. It does not prevent deletion of data the attacker can reach, and it provides no protection when the keys are stored in the same identity plane as the compromised admin credentials.
Identity isolation prevents reach. Separate credential planes, network segmentation, management plane boundaries that keep backup admin credentials out of the production identity domain — the controls that prevent a compromised production environment from being able to access, modify, or destroy hardened data at all. Identity isolation is the layer that makes both immutability and encryption survivable. Without it, both collapse when the identity plane collapses.
| Discipline | Purpose | What It Doesn’t Do | Failure Mode |
|---|---|---|---|
| Backup | Create recoverable copies of data at defined intervals | Protect those copies from deletion or unauthorized access | Unrecoverable if recovery path is severed before incident |
| DR | Restore systems to production state after a failure event | Distinguish between clean state and compromised state | Replicates compromised state if recovery environment is not isolated |
| Hardening | Prevent destruction, unauthorized access, and identity-plane reach | Substitute for backup frequency or DR sequencing | Fails under identity compromise when layers are not integrated |
Data hardening operates across three integrated layers. Each layer addresses a different attack vector. Each has a different failure mode. The architecture that survives adversarial conditions requires all three — not as independent controls, but as a connected system where identity isolation makes immutability real and encryption meaningful.
Immutability — What It Actually Means
Immutability is the most misunderstood property in data protection architecture. Most implementations that claim immutable backup are not immutable at the layer that matters — because the distinction between time-bound and authority-bound immutability is almost never made explicit, and the attack surface is always the authority model.
Time-bound immutability defines the retention window — the period during which data cannot be deleted or modified. Every WORM implementation has this. It is the property that vendors lead with and auditors check for. It is necessary and insufficient.
Authority-bound immutability defines who, if anyone, can override that window. This is the property that determines whether time-bound immutability survives adversarial conditions. If a privileged credential can call an API that shortens the retention window, deletes the lock, or overrides the WORM policy — the immutability is a delay mechanism, not a protection mechanism. The retention timer is the attack surface.
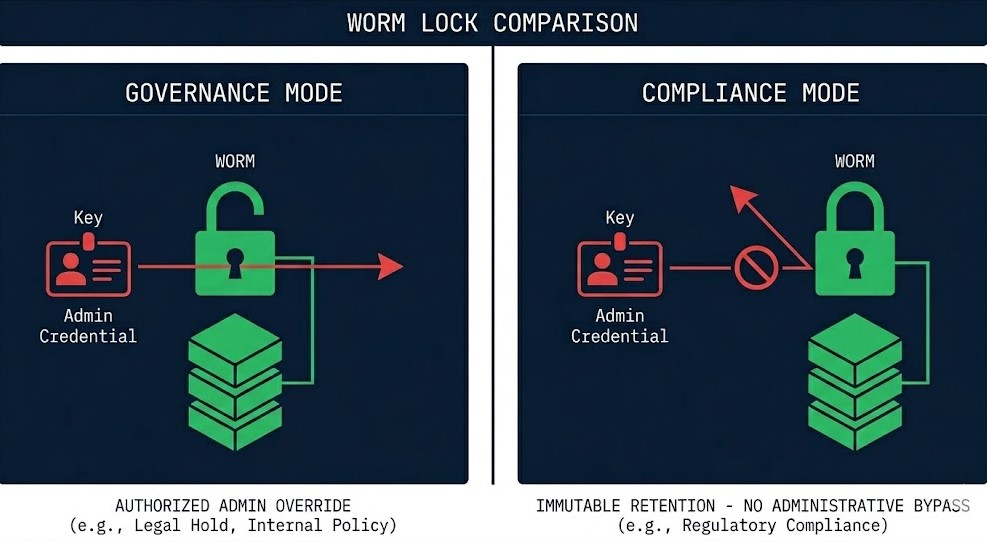
The specific implementation decision that most architectures get wrong: governance mode vs compliance mode in S3 Object Lock, Azure Blob immutable storage, and GCS Bucket Lock. Governance mode allows accounts with the s3:BypassGovernanceRetention permission — or equivalent — to modify or delete objects before the retention period expires. Compliance mode does not. No credential, including root, can override a compliance mode lock during the retention window. Most architectures deploy governance mode and describe the result as immutable. It is not. It is deletion-resistant against non-privileged accounts. Against a compromised admin credential with bypass permissions, it provides no protection.
Platform-level immutability implementations follow the same authority-bound logic. Rubrik’s appliance architecture enforces immutability at the hardware layer — the management API cannot override the retention window because the enforcement is below the software layer. Veeam’s hardened Linux repository enforces immutability at the OS layer through a service account with restricted permissions — the immutability is as strong as the access controls on that service account. The difference between hardware-enforced and software-enforced immutability is the difference between an authority-bound guarantee and an authority-bound assumption. The object lock implementation gaps that make immutability fail in production are almost always authority-bound, not time-bound.
The Three Ways Immutability Fails
Immutability fails in three predictable patterns. All three are authority-bound failures, not time-bound failures. The retention window is intact. The lock is configured. The data exists. And the attacker can still reach it.
All three failure modes share a root cause: the authority model was not isolated from the compromised environment. The six attack patterns that defeat standard backup architecture all exploit this gap — not the immutability implementation, but the identity plane that governs it.
Encryption Architecture — At Rest, In Transit, In Use
Encryption is the layer that makes data unreadable without authorization. It is also the layer most commonly deployed in a way that provides the appearance of a security boundary without the substance of one — because the key lives in the same trust domain as the data it protects, and the identity plane that can read the data can also read the key.
Encryption at rest covers stored data — backup repositories, object storage vaults, database volumes, archived files. Platform-managed encryption (SSE-S3, Azure Storage Service Encryption) provides encryption without customer key management overhead. It is the correct default for data where the threat model does not include the cloud provider itself. Customer-managed encryption (CMEK, SSE-KMS, Azure CMK) places the key in a customer-controlled KMS — adding the separation layer that survives a cloud provider credential compromise or a misconfigured bucket policy. The critical implementation question: is the KMS in the same IAM context as the data? Same IAM = no boundary. The encryption exists. The key is still reachable.
Encryption in transit covers data moving between systems — backup jobs writing to repositories, replication streams, API calls to management planes. TLS 1.2 minimum, TLS 1.3 preferred. Mutual TLS for service-to-service communication within the backup architecture — both sides authenticate, eliminating man-in-the-middle attack surfaces on backup replication paths. Certificate management is the operational failure mode: expired certificates that disable encrypted channels silently, or self-signed certificates deployed for convenience that introduce verification gaps.
Key management architecture is where encryption either produces a real security boundary or collapses into compliance theater. HSM-backed keys (AWS CloudHSM, Azure Dedicated HSM, on-premises HSM) provide tamper-resistant key storage where the key material never leaves the hardware boundary in plaintext. Key rotation policy defines the operational window during which a compromised key is useful — annual rotation as a minimum for long-term backup encryption keys. Split custody — requiring multiple parties to reconstruct a key — is the authority-bound equivalent for encryption: no single compromised credential can access both key components. The attack surface reduction principles that apply at the OS layer apply identically to key management architecture — minimize the credentials that can reach the key, minimize the network paths that lead to the KMS, and minimize the window during which any single credential is valid.
For database backup specifically, encryption interacts with application consistency in ways that most architectures don’t model explicitly. An application-consistent database backup that is encrypted with a key the recovery environment cannot reach is not a recoverable backup. Encryption and application consistency must be tested together, not independently.
The Management Plane Problem
Every hardening failure traces back to the management plane. Not to the storage configuration, not to the encryption algorithm, not to the retention policy — to the identity and network architecture that determines whether the management plane governing those controls is reachable from a compromised environment.
Ransomware operators don’t attack the data first. They attack the management plane. The backup orchestration system. The KMS API. The retention policy management interface. The snapshot schedule configuration. These are the systems that, once owned, allow an attacker to disable every hardening control in the environment before the visible attack event — without triggering any alert that a security team is watching for.
The management plane problem has two dimensions. Network reachability — can the management API that governs immutability locks, encryption keys, and backup retention be reached from a network path that a compromised production workload can access? If yes, the management plane is inside the blast radius. Identity reachability — do admin credentials that govern the management plane exist in the same identity provider as production admin credentials? If yes, a single credential compromise covers both. Identity is the real control plane — and in backup hardening architecture, it is the specific control plane that determines whether every other layer survives.
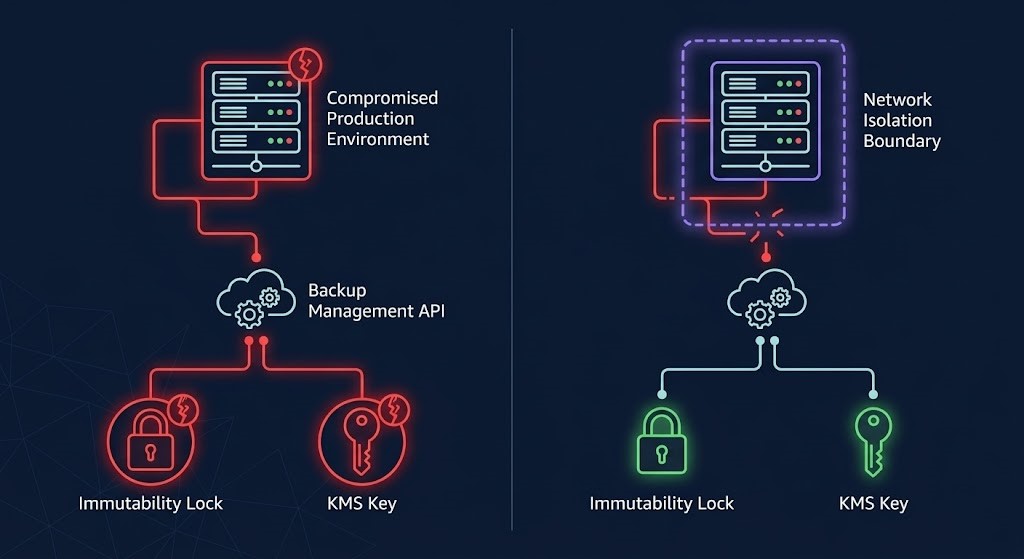
The three management plane controls that determine hardening survivability:
Separate identity planes — backup admin credentials must not exist in the same identity provider as production admin credentials. If the production Active Directory is compromised, the backup management console must require a credential that was never in that directory. This is not a nice-to-have for high-security environments. It is the architectural requirement that separates a compliant hardening implementation from a survivable one.
Network isolation of management APIs — the APIs that manage retention policies, immutability locks, and encryption keys must not be reachable from any network segment that a compromised workload can access. Management plane access is provisioned through separate network paths — dedicated management VLANs, separate VPCs, or out-of-band access that is physically or logically separated from production traffic paths. Configuration drift that silently reopens network paths to the management plane is how hardening architectures that were correctly built degrade over time without detection.
MFA on all destructive operations — not just on login. Every retention policy modification, every immutability lock removal, every key deletion, every backup job modification requires a second factor that is not stored in the compromised environment. MFA at login without MFA at the operation level protects the session, not the operation.
Air Gap Architecture — Logic vs Physical
An air gap is the hardening primitive that survives full management plane compromise. When the identity plane collapses, when the management APIs are owned, when every other control has been bypassed — an air-gapped copy is the only recovery path that was never reachable from the compromised environment.
A true air gap means not reachable via network, not reachable via identity, not reachable via API, and not triggerable by any automated process a compromised environment controls. The moment an “air-gapped” backup can be reached by anything the compromised environment can reach — it is not air-gapped. It is an immutable backup with a misleading label.
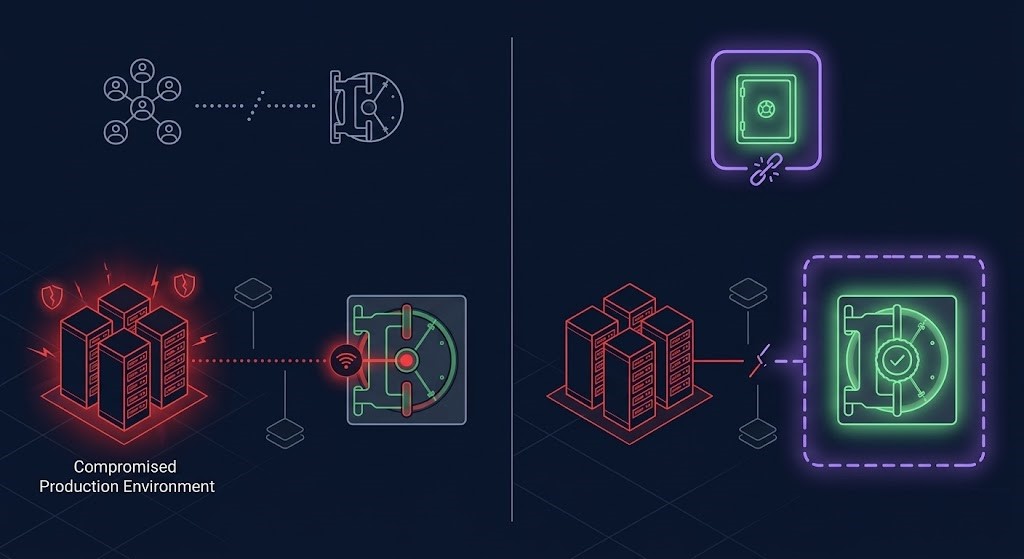
Physical air gap is the only implementation that is unambiguously true. Tape vaulted offsite, physical media rotated on a schedule that requires human action to retrieve, backup copies written to media that has no persistent network connection. The operational cost is real: retrieval time is measured in hours to days, and the restore process requires manual steps that don’t exist in automated recovery architectures. For Tier 0 workloads in highly regulated environments — federal, financial, healthcare — physical air gap is often a compliance requirement, not just an architectural option.
Logical air gap is the practical implementation for environments that cannot support physical media rotation. Network isolation enforced at the infrastructure layer, separate identity providers with no federation to the production environment, time-locked access windows that close the management API connection except during defined backup ingestion periods, and out-of-band verification before the window opens. A correctly implemented logical air gap approximates physical isolation — but only if the separation is enforced at every layer. Network, identity, API access, and automated triggering. One connected path is a connected air gap, which is compliance theater.
The cyber vault model — implemented by Cohesity FortKnox, Rubrik Security Cloud, and equivalent platforms — is the operationally practical implementation of logical air gap for enterprise environments. An isolated vault environment with an independent management plane, separate credentials, automated threat scanning before data is sealed, and a defined ingestion window that closes between backup operations. The vault has no persistent connection to the production environment. The backup software pushes data during the window; the window closes; the data is immutable and unreachable until a recovery event requires it. This is the correct architecture for environments that need air gap survivability without physical media operations. Logic-gapping in a zero-trust world covers the implementation reality in full.
Hardening by Workload Tier
Hardening investment scales with workload criticality and threat model. The architecture does not change — the depth of each layer and the strictness of authority-bound controls do.
| Tier | Examples | Immutability Requirement | Encryption Standard | Key Custody | Air Gap Required |
|---|---|---|---|---|---|
| Tier 0 — Mission Critical | Transaction DBs, Identity Systems, Core Infrastructure | Compliance mode WORM — hardware-enforced where possible. No governance mode override. | AES-256, CMEK with HSM-backed keys | Separate KMS, split custody, independent IAM | Yes — physical or certified logical vault |
| Tier 1 — Business Critical | App servers, file services, collaboration platforms | Compliance mode object lock. Separate management plane. | AES-256, platform or CMEK | Separate from production IAM. MFA on key operations. | Logical air gap minimum |
| Tier 2 — Operational | Dev/test, non-production, archival systems | Governance mode acceptable with documented exception | Platform-managed encryption | Standard IAM with role separation | Not required |
The Hardening Decision Framework
| Requirement | Architecture Decision | Risk if Skipped |
|---|---|---|
| Ransomware survival | Compliance mode immutability + separate identity plane + management API isolation | Retention deleted or shortened during dwell period — data gone before incident is declared |
| Real encryption boundary | CMEK with HSM-backed KMS isolated from production IAM + key rotation policy | Keys in same blast radius — encrypted data is plaintext to anyone who owns the environment |
| Regulatory compliance | Immutability with audit trail + key rotation log + retention tamper detection | Retention modification without audit trail = compliance failure at examination time |
| Zero-trust recovery | Air gap + identity isolation + clean room recovery environment with no production path | Re-infection on reconnect — recovery environment becomes second incident |
| Cloud workload hardening | Object lock compliance mode + separate AWS account or subscription + egress modeled | Governance mode override + recovery egress cost not in budget = dual failure under incident |
| Hybrid environments | Separate management planes for on-prem and cloud — no shared credential covering both | Single credential compromise covers full hybrid blast radius simultaneously |
When Hardening Fails
Honest failure conditions — the scenarios where a technically correct hardening implementation produces an unprotected environment:
Governance mode deployed as compliance mode. The most common single failure in cloud immutability architecture. The retention period is set. The lock is configured. The bypass permission exists on the admin role. During the dwell period, a compromised admin credential calls the bypass API, removes the lock, and deletes the data. The audit log records the event. The data is gone.
CMEK keys in the same IAM as production. Encryption is configured. The KMS is the same account, the same IAM role, the same credential plane. A compromised admin credential can read the data and read the key simultaneously. The encryption label is accurate. The security boundary does not exist.
Management API reachable from production network. The backup management console, the retention policy API, the snapshot schedule interface — all accessible from the production network segment that was just compromised. The attacker doesn’t need admin credentials for the backup system specifically. They need network access to the management plane, and a credential with sufficient privilege. Network reachability is the physical door; identity is the key. Both must be closed.
Air gap connected to production path. The vault is designated as air-gapped. The backup software has a persistent API connection to it for health monitoring. That connection is reachable from the compromised environment. The vault is not air-gapped — it is an immutable backup with a persistent attack surface. The monitoring convenience negated the isolation architecture.
Identity plane shared across production and backup. A single directory services compromise covers production admin, backup admin, snapshot admin, and KMS admin simultaneously. The hardening architecture was correct at every layer except the one that mattered: the identity plane was never separated. All three hardening layers collapsed with one credential event.
The Cost of Hardening
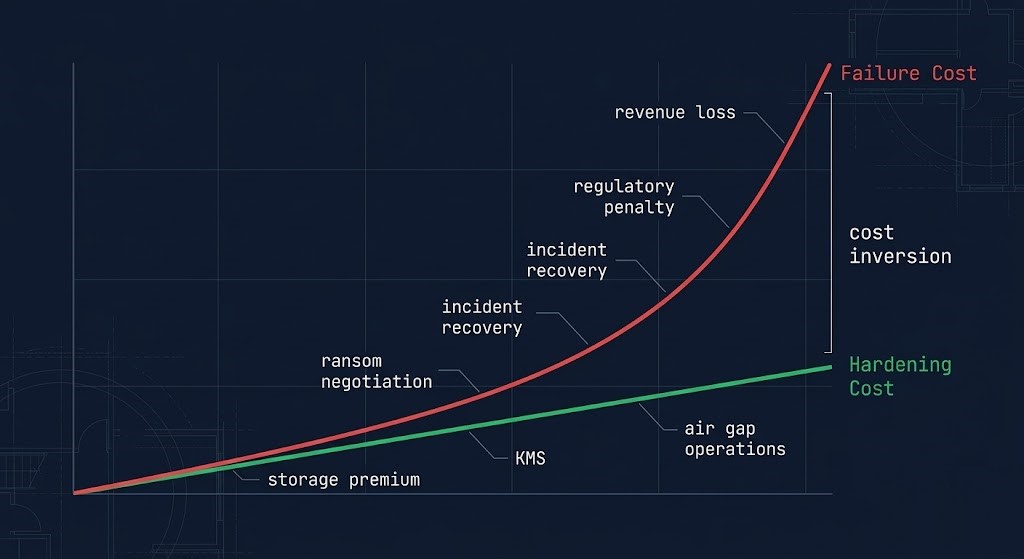
Data hardening has real costs. WORM storage in compliance mode carries a premium over standard object storage. Customer-managed encryption with HSM-backed keys adds key management infrastructure cost and operational complexity. Logical air gap architecture requires a separate vault environment with independent compute, identity, and network infrastructure. Physical air gap requires tape hardware, media rotation procedures, and offsite vault fees. Identity separation requires a second directory services implementation and the operational overhead of managing two credential planes.
These costs are linear and predictable. They appear on infrastructure budgets. They are reviewable, modelable, and defensible in any budget conversation.
The cost of hardening failure is exponential and unmodeled. Ransom negotiation against a recovery timeline you can’t meet. Extended outage revenue loss while the recovery path that was never built gets built under incident pressure. Regulatory penalties for data that was not protected to the standard the compliance framework required. Reputational damage that outlasts the incident by years. The true cost of backup analysis models the normal-operations cost accurately — but the failure-state cost is the one that dwarfs the architecture investment by orders of magnitude. Hardening costs are what you pay to make failure-state cost theoretical rather than actual. That is the budget conversation worth having before the incident makes it irrelevant.
Architect’s Verdict
Data hardening is not a storage configuration. It is an architectural posture across three integrated layers — immutability, encryption, and identity isolation — where each layer’s effectiveness depends on the integrity of the others. Immutability without identity isolation is a time-delay mechanism, not a protection mechanism. Encryption without key separation is a compliance checkbox. Identity isolation without network segmentation of management APIs is an assumption that will surface as a gap during the incident that tests it.
The time-bound vs authority-bound distinction is the mental model that separates architectures that survive adversarial conditions from architectures that look correct in documentation. Most environments have strong time-bound immutability. Almost none have explicitly designed authority-bound immutability — the identity and network architecture that determines whether the authority to modify the retention window exists anywhere the compromised environment can reach. That gap is where every immutability failure in production happens. Not in the storage configuration. In the authority model.
The encryption equivalent is the key separation boundary. Encrypted data in the same IAM plane as its keys is not encrypted data in any meaningful security sense. The encryption algorithm is correct. The security architecture is not. Separating the key from the data at the identity and network layer is the only implementation that produces a real boundary — and it is the implementation that most deployments skip because the platform default is same-account encryption, and the platform default looks like protection until it is tested under compromise conditions.
Build the three-layer model. Test each layer under the failure condition it is designed to survive — not the steady-state operation it performs without incident. Governance mode immutability survives accidental deletion. It does not survive a compromised admin credential with bypass permissions. Compliance mode immutability survives both. That is the difference that matters. Run the test that exposes which one you have.
Data hardening is one execution domain within the data protection system. Hardening without backup architecture is a lock on a door with no floor. Hardening without cybersecurity architecture leaves the identity plane exposed. Hardening without disaster recovery architecture means isolated data that cannot be recovered into a clean environment. Each domain connects to the others.
You’ve Read the Architecture.
Now Validate Whether Yours Actually Survives.
Governance vs compliance mode, key separation boundaries, management plane reachability, air gap validity — most hardening implementations look correct in documentation and fail under adversarial conditions. The triage session validates whether your specific environment can survive the failure conditions this page describes before a ransomware event does it for you.
Data Protection Architecture Audit
Vendor-agnostic review of your hardening posture — immutability mode validation, encryption key separation audit, management plane reachability assessment, air gap architecture validity, and identity isolation across the full data protection stack.
- > Governance vs compliance mode validation
- > Encryption key separation and KMS architecture
- > Management plane reachability and identity isolation
- > Air gap validity and ransomware survivability
Architecture Playbooks. Every Week.
Field-tested blueprints from real hardening environments — governance mode bypass incidents, key management architecture failures, air gap compromise case studies, and the immutability patterns that actually survive adversarial conditions.
- > Immutability Architecture & Compliance Mode Patterns
- > Encryption Key Management & Separation Models
- > Air Gap & Cyber Vault Architecture
- > Real Hardening Failure Case Studies
Zero spam. Unsubscribe anytime.
Frequently Asked Questions
Q: What is immutable backup?
A: Immutable backup stores data under a WORM policy that prevents modification or deletion during a defined retention window. The critical implementation distinction is enforcement layer: compliance mode enforces immutability at the storage layer — no credential can override it. Governance mode allows privileged accounts to bypass the lock and is not true immutability. Immutable backup prevents catalog deletion and retention manipulation during ransomware dwell periods — but only if the management API that governs the lock is isolated from the compromised environment.
Q: What is the difference between governance mode and compliance mode in S3 Object Lock?
A: Governance mode allows accounts with the s3:BypassGovernanceRetention permission to delete or modify objects before the retention period expires. Compliance mode does not — no account, including root, can override a compliance lock during the retention window. Most architectures deploy governance mode and describe the result as immutable. Against a compromised admin credential with bypass permissions, governance mode provides no protection. Compliance mode is the only implementation that produces time-bound immutability with real authority-bound enforcement.
Q: How does ransomware defeat immutability?
A: Through authority-bound failures, not time-bound failures. Ransomware operators target the management plane — the API that governs retention policy, the identity plane that controls backup admin credentials, the network path that reaches the immutability management interface. If any of these are reachable from the compromised environment, an attacker can shorten the retention window, remove the lock, or delete the management catalog before encryption runs. The retention timer is still set. The data is gone. Immutability survives ransomware only when the management plane is completely isolated from the compromised identity and network environment.
Q: What is customer-managed encryption (CMEK)?
A: Customer-managed encryption places encryption key custody with the customer rather than the cloud provider. Instead of the platform managing keys transparently, the customer controls a KMS — AWS KMS, Azure Key Vault, Google Cloud KMS, or an on-premises HSM — where the key material is stored and rotation policy is defined. The security boundary this creates is only real if the KMS is in a separate identity domain from the data it protects. CMEK with the KMS in the same IAM account as the encrypted data provides key management control without a meaningful security separation — a compromised admin credential reaches both.
Q: What is the difference between time-bound and authority-bound immutability?
A: Time-bound immutability defines how long data cannot be deleted — the retention window. Authority-bound immutability defines who, if anyone, can override that window. All WORM implementations have time-bound immutability. Very few explicitly design authority-bound immutability — the identity and network isolation that prevents any credential in the compromised environment from reaching the API that governs the retention window. The attack surface is always the authority model, not the retention timer. Strong time-bound immutability with weak authority-bound controls is a delay mechanism against sophisticated attackers, not a protection mechanism.
Q: What is a true air gap in 2026?
A: A true air gap means not reachable via network, not reachable via identity, not reachable via API, and not triggerable by any automated process a compromised environment controls. In enterprise environments, this is implemented through physical tape vaulting or cyber vault platforms (Cohesity FortKnox, Rubrik Security Cloud) with independent management planes, separate credential stores, and time-locked ingestion windows that close between backup operations. A vault with a persistent monitoring API connection that is reachable from the production network is not air-gapped. Connected air gaps are compliance theater.
Q: What hardening controls are required to survive ransomware?
A: Three controls must work as an integrated system. First, compliance mode immutability at the storage layer — not governance mode. Second, management plane isolation — the APIs that govern retention and the identity credentials that control backup admin access must exist in a separate network segment and a separate identity provider from the compromised production environment. Third, an air-gapped copy that has no persistent connection to the production environment and is not reachable via any automated process a compromised workload controls. Any single missing layer leaves a path a sophisticated attacker will find during the dwell period before encryption runs.
