Architecture for Data Authority and Control Plane Independence.
Sovereign infrastructure is not a data residency policy. It is not a private cloud deployment. It is not a compliance checkbox.
It is the architecture that answers one question with proof, not documentation: if every external control plane became unreachable tomorrow, could your systems still operate, your data remain protected, and your workloads move without vendor permission?
Most organizations believe they have sovereignty because they have a region locked to their jurisdiction, a private cloud contract, or an encryption layer with customer-managed keys. None of those things are sovereignty. They are conditions that can exist alongside sovereignty — or alongside complete control plane dependence. The distinction is in the architecture, not the contract.
This page covers what sovereign infrastructure actually requires at the architecture level: the control plane model that defines sovereignty, the failure modes that break it in practice, the spectrum from cloud-dependent to fully sovereign, and the minimum viable architecture that makes sovereignty a provable state rather than an assumed one.
The Sovereignty Illusion
Every enterprise has a sovereignty assumption. Very few have a sovereignty architecture.
The gap between those two things is not visible in documentation. It is not surfaced by a compliance audit. It appears when an external control plane becomes unreachable, when a vendor changes its terms, when a jurisdiction issues a data access order, or when a ransomware operator targets the backup control plane specifically because they know recovery depends on it.
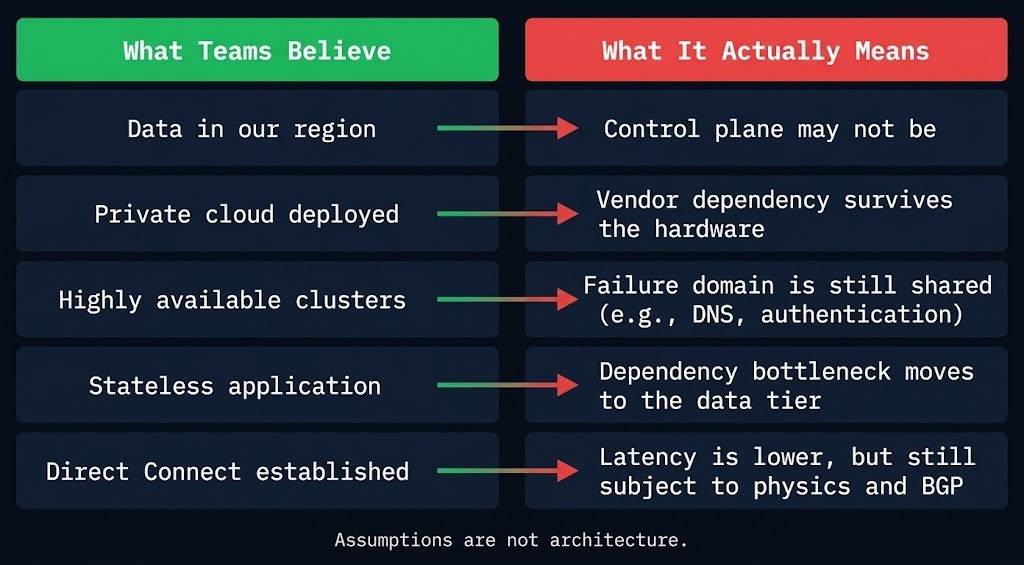
| What Teams Believe | What It Actually Means |
|---|---|
| Data is in our region | The data is local. The control plane managing it may not be. |
| We use private cloud | Infrastructure dependency is reduced. Software and identity dependency may be unchanged. |
| We control encryption | You hold keys. Key custody defines control — and KMS tied to a cloud provider transfers it back. |
| We can exit cloud | An exit path exists on paper. A tested exit path that has never been executed is an assumption. |
| Air gap = sovereign | Physical isolation is real. API reachability to an external service breaks it regardless. |
The illusion is maintained because most sovereignty gaps are invisible at rest. The control plane dependency isn’t exercised under normal operations. The untested exit path isn’t triggered during routine workloads. The identity coupling isn’t exposed until the primary provider is unreachable.
Sovereignty is provable or it is assumed. There is no middle state.
What Sovereign Infrastructure Actually Means
Sovereignty has a testable definition. Not a regulatory one, not a contractual one — an architectural one.
The three conditions are not independent. Control plane independence is the enforcement mechanism for data control. Exit capability is the proof that control plane independence is real. All three must be true simultaneously. Two out of three is a partial architecture — and partial architectures fail completely under the conditions that sovereign infrastructure is designed to survive.
Sovereign infrastructure exists only when all three of the following are simultaneously true:
The Sovereignty Control Plane Model
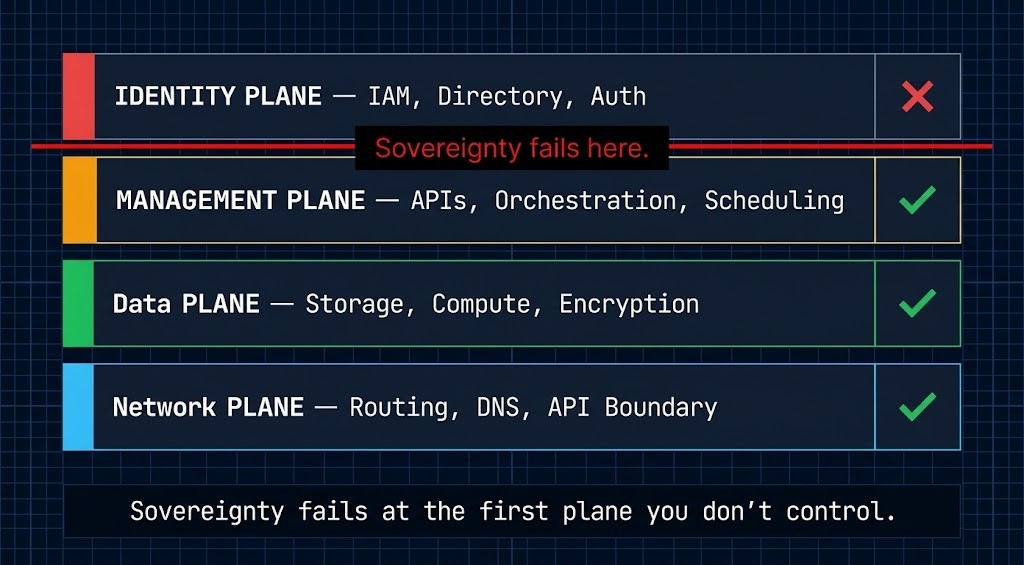
The architecture of sovereign infrastructure is defined by four control planes. Each plane represents a category of decisions your infrastructure makes continuously. Sovereignty requires that all four operate independently of external authority.
This is the Rack2Cloud Sovereignty Control Plane Model.
| Plane | What It Controls | Sovereign Requirement | Fails When |
|---|---|---|---|
| Identity Plane | IAM, directory services, authentication, authorization | Independent identity system with offline bootstrap capability | Cloud IAM required for access decisions; federated identity with external dependency |
| Management Plane | Orchestration APIs, scheduling, configuration management, patching | All management APIs reachable from within the sovereign boundary | External APIs required for orchestration decisions; cloud control plane must be online |
| Data Plane | Storage, compute, encryption, key management | HSM-backed key custody within the sovereign boundary; immutable storage under local control | KMS tied to cloud provider; storage API requires external reachability for access |
| Network Plane | Routing, DNS, API boundary enforcement, traffic decisions | DNS resolution and routing decisions made within the boundary | External DNS required; BGP control reachable only via provider network; API gateway authenticates externally |
The core rule: sovereignty fails at the first plane you don’t control.
This is not a compound failure. The Identity Plane can fail sovereignty while the Data, Network, and Management planes remain fully controlled. In practice, that means your data is local, your hardware is yours, your network is isolated — and none of it matters because every access decision routes through an external identity provider that must be reachable.
Most sovereign architecture failures are Identity Plane failures. The second most common is Management Plane coupling — orchestration systems that phone home for license validation, configuration updates, or scheduling decisions. The Data Plane is typically the most controlled. The Network Plane is typically the most neglected.
The two upcoming sub-pages in this cluster — Sovereign Identity & Access Architecture and Sovereign Networking & Control Plane Isolation — own the Identity and Network planes respectively. The existing sub-pages cover the Data and Management planes: Bare Metal Orchestration, Hardware Security (HSM), and Private Cloud Sovereignty.
The Sovereignty Spectrum
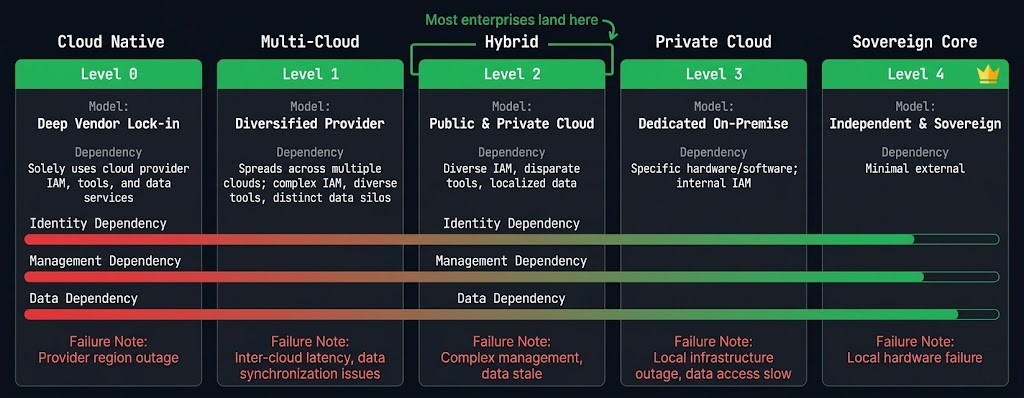
Sovereignty is not binary. It is a spectrum of control plane independence — and the right position on that spectrum depends on workload classification, threat model, and operational capability.
| Level | Model | Control Plane Dependency | Breaks When |
|---|---|---|---|
| 0 | Cloud Native | Full vendor — all four planes | Provider outage, contract change, or jurisdiction shift |
| 1 | Multi-Cloud | Reduced vendor — shared control planes across providers | Shared identity or DNS fails; simultaneous provider issue |
| 2 | Hybrid | Partial control — identity still coupled to cloud in most implementations | Identity provider unreachable during primary site failure |
| 3 | Private Cloud | Infrastructure control — software and license dependency remains | Vendor withdraws software support; license validation fails offline |
| 4 | Sovereign Core | Full control plane independence | Operational capability gap — sovereignty maintained but at engineering cost |
Most enterprises currently operate at Level 2. Hybrid architecture with a cloud-coupled identity plane is the standard landing zone for organizations that have invested in data center infrastructure while adopting cloud services. This is not a failure — it is a deliberate trade-off between operational convenience and sovereignty risk.
The transition from Level 2 to Level 3 is an infrastructure decision. The transition from Level 3 to Level 4 is an identity and network decision — which is why those two planes have dedicated sub-pages in this cluster.
Level 4 is the target for regulated workloads, defense environments, adversarial-threat scenarios, and any architecture where the failure conditions at lower levels would be existential. It is not the correct default for every workload — and the Decision Framework section covers when each level is architecturally appropriate.
The Three Sovereignty Domains
The Control Plane Model defines the what. The Three Sovereignty Domains define the where — the physical, logical, and operational boundaries that the control planes operate within.
| Domain | What It Controls | Sovereign Requirement | Failure Mode |
|---|---|---|---|
| Physical | Hardware location, firmware, supply chain | Owned or leased hardware under your physical control; firmware auditable and controlled | Supply chain compromise; firmware backdoor; hardware confiscation under jurisdiction |
| Logical | Network segmentation, API boundaries, air gaps | Network isolation enforced at the boundary; API reachability bounded by the perimeter; logical air gaps verified rather than assumed | API reachability bypass — an “air-gapped” system with a vault API that reaches the public internet; undocumented management network |
| Operational | Identity, key management, audit trail, credential lifecycle | Independent credential management; key custody in locally controlled HSM; audit trail immutable and locally retained | Credential compromise via external identity provider; key escrow with the cloud KMS; audit logs stored in the provider’s logging service |
The three domains map directly to the control plane layers. The Physical Domain protects the Data and Management planes at the hardware level. The Logical Domain protects the Network Plane. The Operational Domain protects the Identity Plane.
A sovereignty architecture that controls two domains but not the third is not sovereign. The Operational Domain — identity and key management — is the most commonly incomplete. Organizations that have invested heavily in physical and logical sovereignty frequently retain an identity coupling that invalidates both.
Sovereign vs Private Cloud
Private cloud replaces infrastructure dependency. Sovereign infrastructure removes control plane dependency. They are not the same architecture.
Private cloud answers: who owns the hardware? Sovereign infrastructure answers: who controls the decisions the hardware makes?
An organization running a private cloud on owned hardware, in a jurisdiction-controlled data center, with a vendor-managed orchestration platform, cloud-hosted identity federation, and cloud-linked KMS has infrastructure control and zero sovereignty. Every access decision, every orchestration call, every key operation routes through an external control plane that the “private” infrastructure is dependent on.
| Dimension | Private Cloud | Sovereign Infrastructure |
|---|---|---|
| Hardware ownership | Customer-owned or leased | Customer-owned or leased |
| Dependency removed | Infrastructure provisioning | Control plane decision-making |
| Identity | Often cloud-federated | Independent, offline-capable |
| Key management | Often cloud-linked KMS | Locally controlled HSM |
| Orchestration | Vendor-managed platform | Independently operated |
| Exit capability | Infrastructure portable | Workloads, data, and identity portable |
| Sovereignty claim | Infrastructure independence | Operational independence |
The practical consequence: private cloud is a necessary condition for sovereign infrastructure. It is not a sufficient one. Organizations that have invested in private cloud have completed the Physical Domain of sovereignty. They have not necessarily addressed the Operational or Logical domains.
The path from private cloud to sovereign infrastructure runs through the identity plane and the network plane — the two domains where cloud coupling most commonly survives a private cloud deployment.
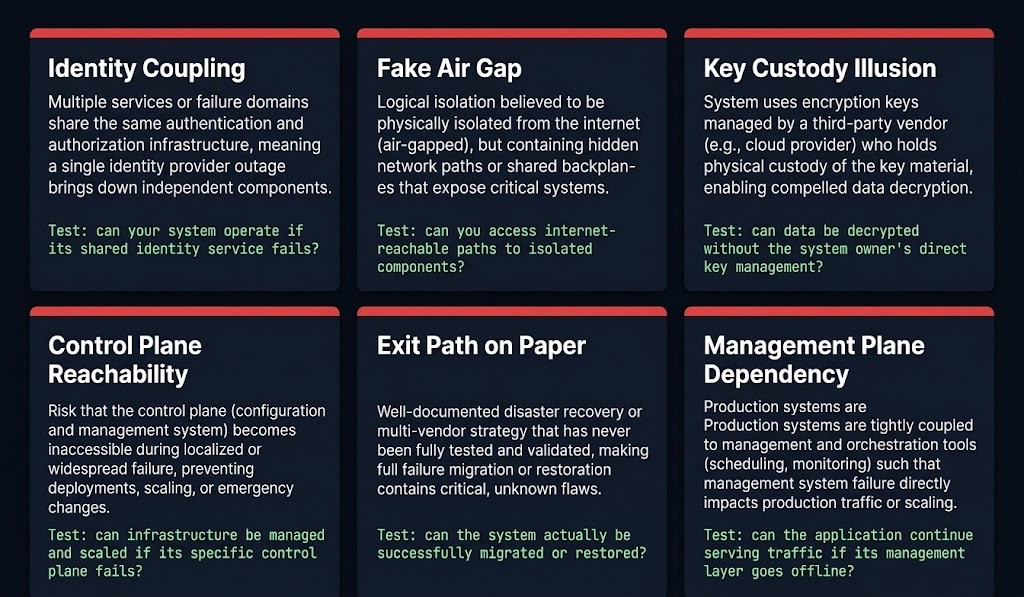
Sovereignty Failure Modes
These are the architectural failure modes that break sovereignty in deployments that appear sovereign on paper. Unlike ransomware or external breach — which are visible failures — these are silent conditions that maintain the appearance of sovereignty while eliminating its substance.
Identity Coupling Cloud IAM is still required for access decisions — even in a “private” environment. The most common form: an on-premises Kubernetes cluster with OIDC tokens validated by a cloud identity provider. The cluster is local. Every authentication call leaves the boundary. Detection test: can your system authenticate a user if the external identity provider is unreachable?
Fake Air Gap Physical network isolation exists, but an API — vault endpoint, management service, telemetry agent — has reachability to the public internet through an undocumented path. The air gap is real at the perimeter. The management network bypasses it. Detection test: perform a full egress audit on the management network. Any unexpected external endpoint fails this test.
Key Custody Illusion Customer-managed keys exist in a cloud KMS. The customer holds the key material — but the KMS API is a cloud service. If the provider’s KMS API is unreachable, decryption fails. Key custody requires the HSM to be physically within the sovereign boundary, not just logically controlled. Detection test: can you decrypt data if the cloud KMS API is unavailable?
Control Plane Reachability The orchestration platform requires the cloud management API to be online for scheduling decisions, node registration, or configuration updates. The workloads are local. The decisions about those workloads are made remotely. Detection test: disconnect the management plane from external networks. Does scheduling continue? Does configuration management function?
Exit Path on Paper A documented migration procedure exists for moving workloads off the current platform. It has never been executed. Exit capability that has not been tested is exit intent — and exit intent does not survive the failure conditions that require a real exit. Detection test: when did you last execute a full exit rehearsal?
Management Plane Software Dependency The orchestration or virtualization software requires phone-home license validation, update retrieval, or telemetry reporting. Disconnecting the system from the provider’s network causes the software to degrade or stop functioning. This is a management plane dependency disguised as a software feature. Detection test: can the software operate indefinitely in a fully air-gapped environment with no external network access?
Exit Cost Is Architectural
The conventional framing of exit cost is financial — migration labor, data transfer fees, re-licensing, retraining. Those costs are real but they are not the primary exit constraint. Exit cost is architectural — and the architectural exit cost accumulates invisibly during adoption, not at exit.
Exit cost is the sum of all dependency types that prevent workloads from moving.
| Dependency Type | Exit Friction | What It Locks |
|---|---|---|
| Storage | High | Data must be exported, transformed, or re-ingested at the destination |
| Compute | Medium | VM images, container registries, and workload definitions are portable with tooling |
| Identity | Critical | Users, service accounts, tokens, and policies must be migrated and re-validated — the entire auth fabric |
| Control Plane | Absolute blocker | If workloads require the provider’s control plane to operate, they cannot move until a replacement is operational |
The architectural consequence: organizations that adopted cloud services without modeling exit cost at each dependency layer have accepted lock-in as a design decision they didn’t make explicitly. The data gravity architecture analysis covers how data movement economics compound this — data that stays in a platform because egress is expensive is data that defines the exit cost of everything that depends on it.
Sovereign infrastructure inverts this model. Rather than modeling exit cost at the point of exit, it designs exit capability as a first-class architectural requirement. Exit capability is not a feature of the destination. It is a property of the current architecture — specifically, whether the current control planes are designed to operate independently of any single vendor’s continued participation.
The Exit Cost as a First-Class Metric post — published Monday — covers the financial modeling framework. This section covers the architectural prerequisites that make exit cost calculable rather than theoretical.
Threat Model
Sovereign infrastructure is not primarily a compliance architecture. It is a survival architecture — designed for the failure conditions where non-sovereign systems are compromised specifically because their control planes are accessible.
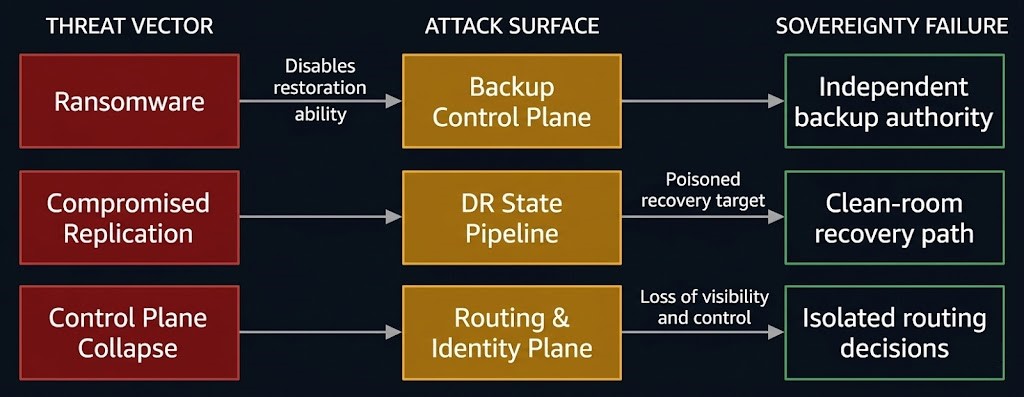
Ransomware → Backup Control Plane Attack Modern ransomware operators target the backup infrastructure before encrypting production. The attack path: compromise credentials with backup management access, delete or encrypt the backup catalog, disable scheduled jobs, then deploy the production payload. The backup control plane — the management interface for recovery — is the first target because operators understand that recovery depends on it. Backup systems designed for adversarial conditions require independent control plane authority — the backup management system must not be reachable from the production network, and credentials must not overlap.
Compromised State → DR Replication Disaster recovery architectures that replicate continuously from production to a DR site replicate compromised state with the same fidelity as clean state. An attacker with dwell time in the production environment contaminates the DR replica. When DR is triggered, recovery restores the infection. Sovereign DR architecture requires an independent clean-room recovery path — a restoration point validated outside the production control plane, with identity and access management that cannot be reached from the compromised production network.
Control Plane Collapse → Business Continuity The Business Continuity architecture establishes that the routing control plane — DNS, API gateway, traffic steering — must be isolated from the failure domain it routes around. This is a sovereignty requirement masquerading as a resilience requirement. A BC control plane that depends on external identity for its own operation fails under the same incident that triggers the continuity requirement. The control plane must be sovereign relative to the failure it governs.
Service Termination → Jurisdictional Seizure A foreign jurisdiction issues a data access order to a cloud provider operating in that jurisdiction. The provider complies. The customer has no technical recourse — because the data access path runs through the provider’s control plane, which is subject to the jurisdiction’s authority. Sovereign infrastructure removes this attack surface by ensuring that data access requires the customer’s credential chain, not the provider’s.
The AI Sovereignty Surface
AI infrastructure introduces four new sovereignty failure modes that do not exist in traditional infrastructure. Each represents a control plane dependency that most AI architects have not modeled.
Model Weights — Data with Jurisdictional Implications A trained model is organizational intellectual property. Model weights stored in a cloud object store are subject to the same jurisdictional exposure as any other data — but with a compound risk: the model encodes knowledge derived from proprietary training data. Exfiltration of model weights is exfiltration of the distilled value of that training corpus. Sovereign AI architecture requires model weights stored within the sovereign boundary under the same custody model as the training data.
Training Data — The Origin Sovereignty Problem Training data jurisdiction is not resolved by where training occurs. Data collected in one jurisdiction, transferred to a cloud training environment in another, and used to train a model creates a provenance chain with multiple jurisdictional exposure points. The Sovereign AI mandate post covers this in full. Sovereign AI architecture requires the entire data pipeline — collection, preprocessing, training — to operate within a defined jurisdictional boundary.
Inference Endpoints — Control Planes for AI Decisions Every API call to a model inference endpoint is a control plane interaction. The endpoint receives inputs, processes them through model weights, and returns outputs that influence downstream decisions. An inference endpoint hosted by a cloud provider operates under that provider’s terms of service, subject to that provider’s jurisdictional obligations, and accessible to that provider’s infrastructure team. For regulated decisions — medical, financial, legal, defense — the inference control plane must operate within the sovereign boundary.
Prompt and Output Logging — The Surveillance Surface Inference providers log prompts and outputs for platform improvement, abuse detection, and compliance purposes. In many default configurations, this logging is enabled and cannot be disabled without an enterprise agreement. For organizations processing sensitive information through AI systems — even through a “private” deployment — the logging pipeline is an uncontrolled data egress path. Sovereign AI architecture requires explicit logging control: what is logged, where logs are stored, who can access them, and under what legal authority.
| AI Sovereignty Surface | What It Exposes | Sovereign Requirement |
|---|---|---|
| Model weights | IP — distilled training value | Stored within sovereign boundary under controlled access |
| Training data | Jurisdictional chain of custody | End-to-end pipeline within defined jurisdiction |
| Inference endpoints | Decision control plane | Endpoint operated within sovereign boundary |
| Prompt/output logging | Data egress via telemetry | Logging under customer control; no provider-side retention |
For organizations building AI infrastructure on sovereign-grade requirements, the Distributed AI Fabrics strategy guide covers the hardware and fabric architecture that supports sovereign AI deployment at scale.
Maturity Model
Sovereignty maturity is measured by one criterion: is sovereignty provable, or assumed?
An organization at Stage 4 can answer the sovereignty litmus test with a test result, not a policy document. An organization at Stage 1 has a residency policy and a GDPR addendum.
| Stage | State | What Exists | What’s Missing | Test |
|---|---|---|---|---|
| 1 | Compliant | Data residency enforced; regulatory certification obtained | Provider has management access; control planes are external; no exit test | Can you prove who controls the management plane? |
| 2 | Controlled | Customer-managed keys; access guardrails implemented | KMS may be cloud-linked; identity federation intact; no exit capability tested | Can you decrypt data without the cloud KMS API? |
| 3 | Sovereign | Independent identity; locally controlled HSM; managed network boundary | Exit path documented but not tested; AI sovereignty surface unaddressed | When did you last execute a full exit rehearsal? |
| 4 | Proven Sovereign | All four control planes independently operated; exit capability tested; AI sovereignty surface addressed | Ongoing operational burden — sovereignty requires continuous validation | All litmus tests pass with test results, not assumptions |
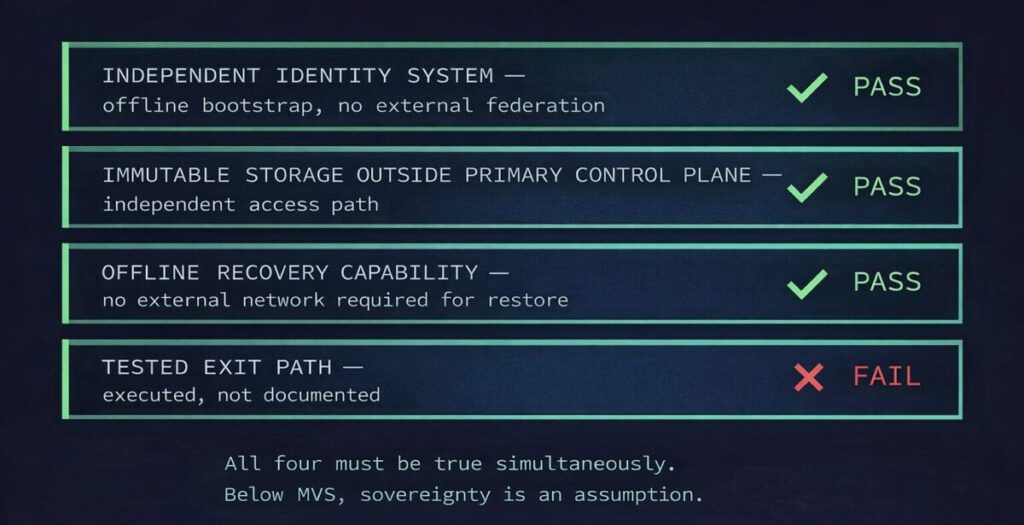
Sovereignty is provable or it is assumed. Stage 3 and Stage 4 are separated by testing, not architecture.
Most organizations that have invested in sovereign infrastructure reach Stage 3. The architecture is correct. The control planes are independent. The gap between Stage 3 and Stage 4 is a single discipline: tested exit capability. An exit path that has never been executed under failure conditions is an assumption that has never been challenged.
The BC testing model applies directly here: untested architecture is theoretical architecture. Run the exit test before the event that requires it.
Minimum Viable Sovereignty
Not every workload requires Stage 4 sovereignty. But every organization handling regulated, sensitive, or mission-critical data needs a defined minimum — below which sovereign claims are not architecturally supportable.
The Minimum Viable Sovereignty (MVS) architecture requires four conditions. All four must be true simultaneously.
Decision Framework
| Scenario | Sovereignty Requirement | Recommended Level | Risk if Skipped |
|---|---|---|---|
| Regulated data subject to data residency law (GDPR, DORA, NIS2) | Minimum Viable Sovereignty — all four conditions | Stage 3 | Jurisdictional exposure; regulatory fine; data access orders enforceable against provider |
| Defense or national security workloads | Full Control Plane Independence — all four planes | Stage 4 | Nation-state access via provider jurisdiction; supply chain compromise via hardware or firmware |
| Healthcare or financial records with adversarial threat model | Independent identity + locally controlled KMS | Stage 3 | Ransomware targeting backup control plane; credential-based access via compromised identity provider |
| AI systems processing sensitive or regulated data | AI sovereignty surface addressed | Stage 3–4 | Inference endpoint logging leaking regulated data; model weight exfiltration |
| Hybrid environments with low-sensitivity cloud workloads | Level 2 hybrid — identity coupling acceptable | Stage 2 | Acceptable for non-critical workloads; unacceptable if identity coupling extends to regulated workloads |
| Startup or early-stage organization | Backup immutability + basic access controls | Stage 1–2 | Complexity cost of Stage 3–4 outweighs benefit at this scale; revisit at regulated workload threshold |
The architectural test for every sovereign claim:
- Can you identify which of the four control planes has an external dependency?
- Can you operate each plane if the provider’s network is unreachable?
- When did you last test exit capability under failure conditions?
Any “cannot answer” is an assumed sovereignty. Any “never” on question 3 is Stage 3, regardless of how well the first two are addressed.
Sovereign infrastructure is executed at the sub-pillar level. Each domain below owns one or two layers of the Sovereignty Control Plane Model. All four control planes are now documented — Identity, Management, Data, and Network.
You’ve Read the Architecture.
Now Test Whether Your Sovereignty Claims Hold.
Control plane independence, identity coupling, key custody gaps, exit path validation — most sovereign architectures look correct on paper and surface their failure modes under the conditions they were designed to survive. The triage session validates whether your specific environment passes the sovereignty litmus tests this page defines — before a failure event does it for you.
Sovereign Infrastructure Audit
Vendor-agnostic review of your sovereignty posture — control plane model audit, identity coupling identification, key custody gap analysis, exit capability validation, and AI sovereignty surface assessment for regulated AI workloads.
- > Control Plane Model audit — all four planes mapped and tested
- > Identity coupling identification and remediation path
- > Exit capability validation — documented path vs tested path
- > AI sovereignty surface assessment for regulated workloads
Architecture Playbooks. Every Week.
Field-tested blueprints from real sovereign infrastructure environments — identity isolation post-mortems, exit path execution case studies, air gap failure analyses, and the control plane independence patterns that actually held under adversarial conditions.
- > Control Plane Independence Patterns
- > Identity Isolation & Offline Bootstrap Architecture
- > Exit Path Execution & Tested Migration Playbooks
- > Sovereign AI Infrastructure Case Studies
Zero spam. Unsubscribe anytime.
Architect’s Verdict
Sovereign infrastructure is not a posture. It is a test result.
The organizations that believe they have sovereignty — and don’t — are not naive. They have invested in private cloud hardware, jurisdiction-locked data centers, customer-managed encryption, and compliance certifications. What they have not done is run the litmus test: if every external control plane became unreachable, would the architecture hold?
For most organizations operating at Level 2 or 3 on the sovereignty spectrum, the answer is no — because the Identity Plane retains a cloud dependency that no amount of physical sovereignty resolves. Authentication requires an external call. That call is the sovereignty boundary. Everything inside it is well-governed infrastructure that still answers to an external authority when access decisions are made.
The path to provable sovereignty runs through four control planes, three domains, and one test that most organizations have never run: a full exit rehearsal under failure conditions. Not a migration plan. Not a documented procedure. An executed test that confirms the exit path works when the exit is forced rather than planned.
The Minimum Viable Sovereignty architecture is the floor. All four conditions simultaneously. Below it, sovereign claims are assumptions. Above it, sovereignty is an architecture — and architectures can be audited, tested, and proven.
Sovereignty is provable or it is assumed. Build the architecture that makes the test answerable.
Frequently Asked Questions
Q: Is sovereign infrastructure the same as a private cloud?
A: No. Private cloud removes infrastructure dependency — you own or control the hardware. Sovereign infrastructure removes control plane dependency — no external authority can make decisions about your systems without your involvement. A private cloud running on vendor-managed orchestration with cloud-federated identity retains control plane dependencies that invalidate sovereignty claims, regardless of hardware ownership.
Q: Does sovereign infrastructure mean being disconnected from the internet?
A: No. Sovereign infrastructure means that connectivity to the internet — or its absence — does not determine whether your systems can function. An air-gapped system that requires an external API for key management is not sovereign. A connected system with all four control planes operating independently is sovereign. The network boundary matters for the threat model, not as a definition of sovereignty.
Q: What is the minimum required for a system to be considered sovereign?
A: The Minimum Viable Sovereignty architecture requires four simultaneous conditions: an independent identity system with offline bootstrap capability, immutable storage outside the primary control plane, offline recovery capability, and a tested exit path. All four must be true at the same time. Two out of four is a partial architecture — and partial architectures fail completely under the conditions sovereign infrastructure is designed to survive.
Q: Does sovereign infrastructure apply to AI workloads?
A: Yes — and AI introduces four new sovereignty failure modes that do not exist in traditional infrastructure: model weight custody, training data jurisdictional chain of custody, inference endpoint control plane sovereignty, and prompt/output logging governance. Organizations processing regulated or sensitive data through AI systems that do not address these surfaces have sovereignty gaps in the highest-value part of their stack.
Q: How do I know which level of the Sovereignty Spectrum my organization is at?
A: Run the control plane audit. For each of the four planes — Identity, Management, Data, Network — answer: can this plane operate if the provider’s network is completely unreachable? If any plane cannot, you are at Level 2 or below regardless of what your infrastructure topology looks like. If all four planes can operate independently but exit capability has never been tested, you are at Level 3. If all four planes are independent and exit capability has been exercised, you are at Level 4.
Q: Is sovereign infrastructure more expensive?
A: Sovereign infrastructure at Stage 3–4 carries a permanent operational overhead — the cost of running independent control planes rather than consuming managed services. That cost is real and should be modeled explicitly. The correct economic comparison is not sovereign infrastructure cost vs public cloud cost. It is sovereign infrastructure cost vs the cost of the failure events that sovereignty prevents: jurisdictional data access, ransomware that eliminates the recovery path, vendor-induced lock-in at renewal, and exit costs that only become visible when a migration is forced.
