Sovereign
Identity
& Access Architecture
Identity is the control plane sovereignty fails at first.
Sovereign identity is not an IAM configuration. It is not an access policy. It is not a zero-trust implementation. It is the architectural property that determines whether your infrastructure can make access decisions without asking permission from a system outside your boundary.
Most organizations that believe they have sovereign infrastructure have solved the physical and data planes. They own the hardware. They control the storage. They have implemented encryption with customer-managed keys. And then, when the failure event arrives — the one the sovereign architecture was built to survive — every access attempt leaves the boundary. Authentication calls an external IdP. Token validation checks an external JWKS endpoint. Policy evaluation queries an external engine. The data is local. The decision about who can reach it is not.
This is the identity plane failure. It is not visible during normal operations. It does not appear in monitoring dashboards. It surfaces exactly once — during the failure event that sovereign infrastructure was designed to survive.
This page answers one question: Why does identity sovereignty fail, and what must be true for it to survive?
The Identity Control Plane Model
Identity is not a system. It is a real-time dependency graph. Every access decision your infrastructure makes — every authentication, every token validation, every authorization check — traverses a chain of components. Each component in that chain is either within your sovereign boundary or outside it. Each one that is outside is a sovereignty escape point.
Identity is not where users log in. It is every place a decision depends on a trust assertion.
That definition changes the architecture problem. You are not designing a login system. You are designing a dependency graph — and auditing every node in that graph for external reachability.
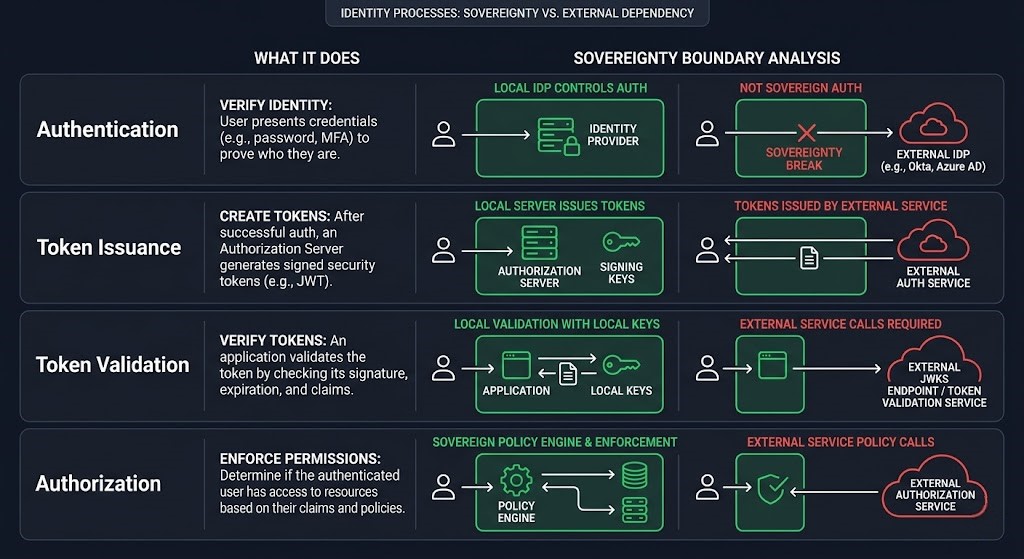
| Layer | What It Does | External Dependency Risk | Sovereignty Test |
|---|---|---|---|
| Authentication | Proves identity — validates that a principal is who they claim to be | IdP reachability — if the provider is unreachable, authentication fails | Can authentication complete with all external network paths severed? |
| Token Issuance | Generates the trust artifact — the signed token that downstream services accept as proof of identity | Signing authority location — if the signing key is held externally, the issuer requires external reachability | Is the signing authority within the sovereign boundary? |
| Token Validation | Confirms the trust artifact — verifies the signature and claims on every incoming request | JWKS endpoint / introspection — if token validation requires an external key discovery call, every service call is an external dependency | Can tokens be validated without calling an external endpoint? |
| Authorization | Decides what an authenticated principal is permitted to do | Policy engine location — if access decisions are evaluated by an external policy store, authorization is externally controlled | Can access decisions be made without external policy system reachability? |
The table above describes four independent sovereignty failure points in a single access request. Most sovereign architecture reviews examine the first layer — authentication — and declare the identity plane controlled. The remaining three layers are left unaudited. In practice, the token validation layer is the most consistently overlooked: organizations that have deployed local IdPs still validate tokens against external JWKS endpoints, exporting sovereignty through the back door of every API call.
The Identity Sovereignty Illusion
The illusion of identity sovereignty is maintained by a set of beliefs that are individually reasonable and collectively wrong. Each belief describes a real security investment. None of them describes sovereignty.
| What Teams Believe | What It Actually Means |
|---|---|
| Cloud SSO = enterprise identity | SSO is a convenience layer on top of an external IdP. Every authentication call leaves the boundary. The provider controls the trust anchor. |
| OIDC tokens are stateless — no external calls needed | OIDC tokens require the issuer’s JWKS endpoint for signature verification. Every validation call is an external network dependency. Stateless tokens are not sovereignty — they are deferred external calls. |
| MFA = secure = sovereign | MFA adds authentication security. It has no relationship to identity sovereignty. Cloud-hosted MFA increases external dependency at the authentication layer. |
| On-premises Active Directory = sovereign identity | On-premises AD with Azure AD Connect sync has an active replication dependency to Azure AD. Authentication decisions may prefer on-prem — but the trust chain has external components. AD alone without auditing all sync and federation dependencies is not sovereign. |
| Zero-trust architecture = sovereign identity | Zero-trust is an access model — never trust, always verify. Sovereign identity is an independence model — verify using only resources within the boundary. Zero-trust implemented with an external IdP is a security posture improvement with zero sovereignty gain. |
| Air-gapped network = sovereign identity | Physical network isolation prevents external access. It does not prevent internal components from requiring external reachability to function. An air-gapped system that cannot authenticate users because the IdP is unreachable is not sovereign — it is unusable. |
The illusion persists because identity sovereignty gaps are invisible at rest. The external dependency is not exercised under normal operations. When the cloud provider is reachable — which is almost always — the authentication call completes, the token validates, the policy evaluates. The sovereignty gap only activates when reachability fails. By which point it is too late to fix it.

What Sovereign Identity Actually Requires
Sovereign identity has a testable definition. Not a policy definition. Not a compliance definition. An architectural one.
Three conditions must be simultaneously true. All three. Not two out of three — a partial sovereign identity architecture fails completely under the conditions it was designed to survive.
The Identity Call Path
Abstract dependency graphs are easy to dismiss. Concrete failure paths are not. Below is a single authentication request — the kind that occurs thousands of times per hour in any enterprise environment — mapped against its sovereignty dependencies.
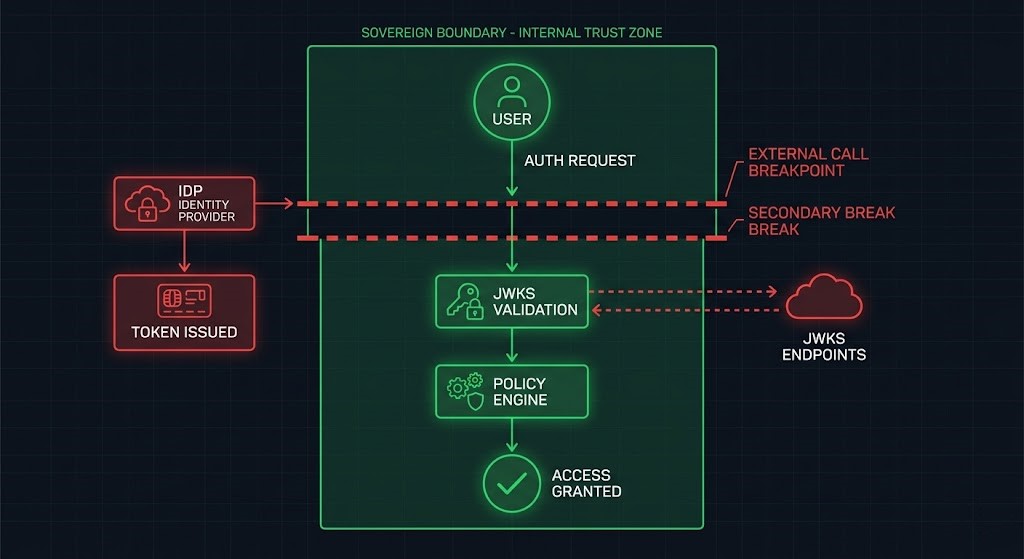
The flow: a user or service attempts to access a protected resource. Authentication is delegated to the IdP. The IdP issues a signed token. The receiving service validates the token signature. An authorization policy is evaluated. Access is granted or denied. Six steps. Four external dependency points. Any one of them breaks sovereignty.
| Step | External Dependency | Failure Outcome When Unreachable | Cross-Pillar Impact |
|---|---|---|---|
| Authentication | Cloud IdP — Azure AD, Okta, Google, Cognito | No login possible. All human access fails. | DR failover environment cannot authenticate operators. BC degradation ladder cannot execute — operators cannot log in to trigger it. |
| Token Issuance | External signing authority — key held outside boundary | Tokens cannot be issued. All service-to-service calls fail immediately. | Ransomware recovery requires authenticated operator access. If token issuance fails, recovery cannot begin. |
| Token Validation | JWKS endpoint — external key discovery | All API requests fail validation. Services reject every incoming request as unverifiable. | Data hardening access controls cannot evaluate access. Encrypted data is inaccessible not because of encryption — but because validation failed. |
| Authorization | External policy engine — OPA cloud, cloud IAM policy store | Access decisions cannot be made. Services fail open or fail closed — neither is acceptable in a regulated environment. | Business continuity routing decisions require authorized operator access. If authorization fails, degradation ladder execution is blocked. |
| Revocation | External CRL / OCSP endpoint | Compromised credentials cannot be verified as revoked. Certificates appear valid past their revocation. | Ransomware credential compromise cannot be neutralized — revocation information is unreachable. Blast radius expands for the full incident duration. |
The revocation step deserves specific attention. In a non-sovereign identity architecture, the window between credential compromise and successful revocation is bounded by external CRL/OCSP reachability. In an incident where the network is degraded or isolated — exactly the conditions where identity sovereignty matters most — revocation cannot be confirmed. Compromised credentials remain operationally valid. The blast radius of a credential compromise expands for the entire duration of the network isolation event.
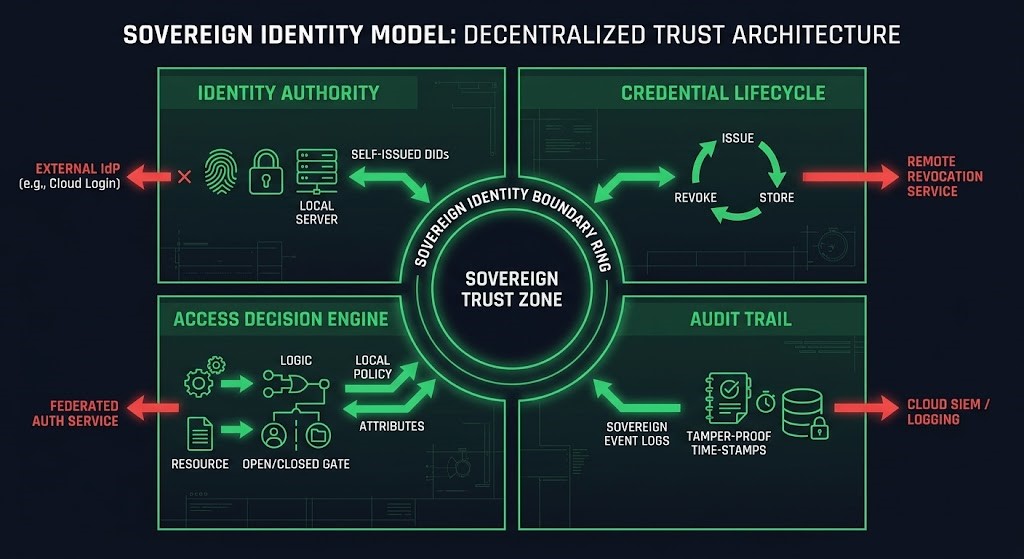
The Rack2Cloud Sovereign Identity Model
Sovereign identity requires four components. Each component must operate within the sovereign boundary. Any single component that escapes the boundary breaks the model — not degrades it. Breaks it. The identity plane is not partially sovereign. It is sovereign or it is not.
This is the Rack2Cloud Sovereign Identity Model.
| Component | What It Owns | Sovereign Requirement | Fails When | Detection Test |
|---|---|---|---|---|
| Identity Authority | The root of trust — the system that asserts who principals are | Operates entirely within the sovereign boundary; no external reachability required for any authentication decision | Cloud IdP is the authority; on-prem system federates to cloud for ultimate trust | Sever all external network paths. Can users authenticate? |
| Credential Lifecycle | Issuance, rotation, revocation, expiry — the operational management of trust artifacts | All credential operations (issue, rotate, revoke) execute without external calls; revocation information served locally | Certificate rotation requires external CA call; revocation checks external CRL/OCSP; credential refresh calls cloud vault | Disconnect external network. Issue and revoke a test credential. Does it complete? |
| Access Decision Engine | Policy evaluation — translates identity assertions into access decisions | Policy store and evaluation engine within the boundary; no external policy source required for runtime decisions | OPA bundles pulled from cloud storage; IAM policies evaluated by cloud provider; RBAC dependent on cloud-hosted policy service | Isolate the network. Make an access request. Does policy evaluate locally? |
| Audit Trail | Immutable record of all identity events — authentication, issuance, revocation, access decisions | Audit log stored locally with immutability guarantees; no dependency on external logging service for record creation | Audit logs forwarded exclusively to cloud SIEM; local log storage not implemented; log immutability enforced by external service | Disconnect external logging endpoint. Generate authentication events. Are they locally recorded? |
The Audit Trail component is the most frequently dismissed. Architects accept that authentication, credential management, and policy evaluation must be sovereign — but treat log forwarding as a secondary concern. It is not. An audit trail that only exists in a cloud SIEM is an audit trail that disappears during the incident it was designed to document. In regulated environments, the loss of audit continuity during a security incident is itself a compliance failure, independent of what the incident caused.
Identity Plane Failure Modes
These are the architectural failure modes that break identity sovereignty in deployments that appear sovereign on paper. Unlike a credential breach — which is visible — these are structural conditions that maintain the appearance of sovereignty while eliminating its substance. They are present at rest and only reveal themselves under failure conditions.
Cryptographic Sovereignty
Identity sovereignty rests on a cryptographic foundation. The trust assertions that authentication, token issuance, and certificate validation rely on are only as sovereign as the cryptographic material that anchors them. That material has a physical location. That location is either within your boundary or outside it. There is no cryptographic sovereignty without physical key custody.
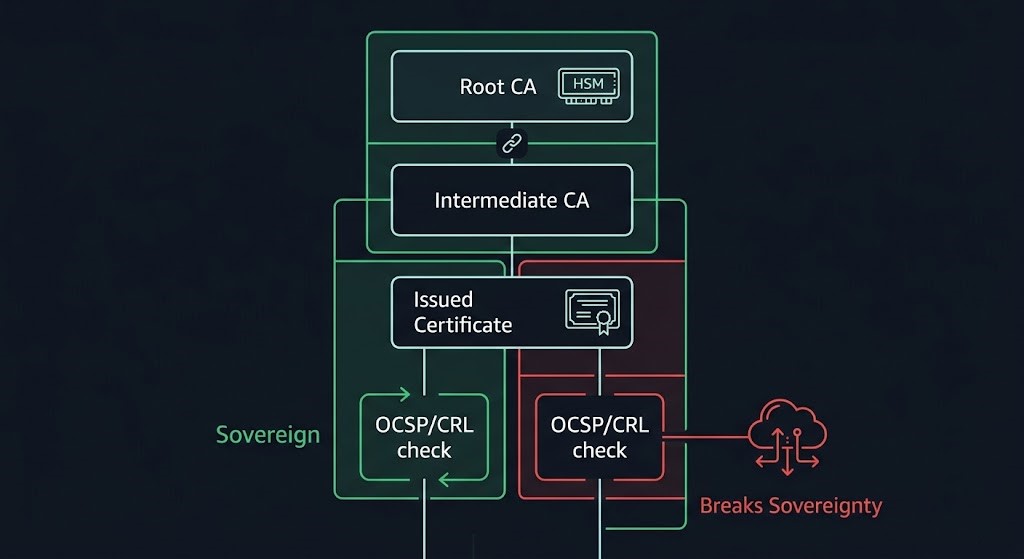
If your root of trust is outside your boundary, your identity is borrowed.
Root CA Location = Sovereignty Boundary. The root certificate authority is the origin point of every trust decision in a PKI-based identity system. If the root CA is hosted by a cloud provider — AWS Private CA, Azure Certificate Services, DigiCert, Let’s Encrypt — the trust anchor is external. Intermediate CAs signed by that root inherit the dependency. Certificates issued by those intermediates carry the external dependency through to every endpoint. The entire trust chain is as sovereign as its root. A root CA outside your boundary means no certificate in your environment is issued under sovereign authority — regardless of where the intermediate or issuing CAs are deployed.
Intermediate CA Compromise Risk. The intermediate CA is the operational signing authority — the component that actually issues certificates to services and users. Compromise of an intermediate CA allows an attacker to issue valid certificates for any identity within the domain it covers. In a sovereign PKI design, intermediate CA private keys are stored in HSM hardware within the sovereign boundary, operations require multi-party authorization, and the intermediate CA has no network reachability from production systems. In most enterprise deployments, intermediate CA keys are stored on a server with network access, protected by a password stored in a secrets manager.
The OCSP and CRL External Dependency Problem. Certificate revocation is the mechanism that makes compromised credentials stop working. Online Certificate Status Protocol (OCSP) and Certificate Revocation Lists (CRL) are the two standard revocation mechanisms. Both require a reachability path from the validator to the revocation service. In most enterprise deployments, OCSP responders and CRL distribution points are internet-hosted — either by the CA provider or by a cloud distribution service. The consequence: in an isolated environment, certificates cannot be confirmed as not-revoked. Systems that enforce revocation checking will reject all certificates. Systems that fail open will accept potentially revoked certificates. Neither outcome is acceptable in a sovereign environment.
Key Custody vs Key Usage Separation. Key custody is physical control of the cryptographic material — who holds the private key, where it is stored, under what physical security. Key usage is the operational act of signing or decrypting using that key — which systems can invoke signing operations, under what authorization, with what audit trail. Sovereign cryptography requires both. Key custody within the boundary — HSM hardware physically inside the sovereign perimeter — and key usage governed by local policy without external authorization calls. Cloud KMS provides a key usage interface. It does not provide sovereign key custody. The key material exists on the provider’s infrastructure and is subject to the provider’s jurisdictional obligations regardless of what the customer agreement says.
The execution layer for cryptographic sovereignty — HSM hardware selection, physical security requirements, key ceremony procedures — is covered in the Hardware Security (HSM) Architecture sub-page. This section defines what cryptographic sovereignty requires. That page covers how it is built.
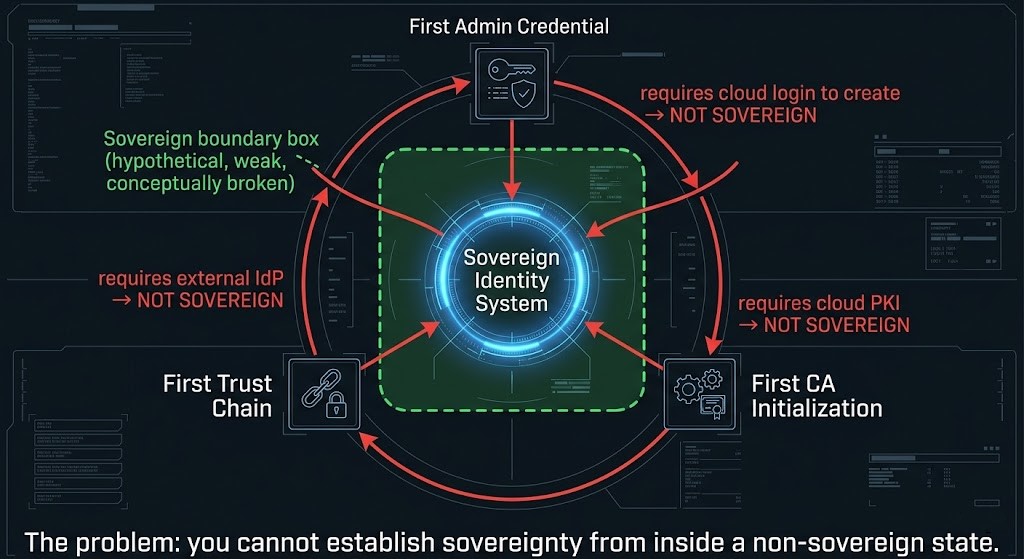
The Bootstrap Problem
Sovereign identity does not fail during steady state. Under normal operations, with external networks reachable, the cloud IdP responds, the JWKS endpoint validates, the policy engine evaluates. Nothing looks broken. Everything functions.
Sovereign identity fails during initialization.
The bootstrap problem is this: establishing a sovereign identity system requires identity. Before the system exists, there are no credentials. Before there are credentials, there is no authentication. Before there is authentication, there is no authorized access. The system that will issue credentials is the system you are trying to build — and you cannot build it without credentials to authorize the build.
This circular dependency is not theoretical. It manifests in a specific pattern: the team deploying a sovereign identity system reaches for the most convenient available credential — a cloud console login, an AWS IAM role, an Azure service principal — to initialize the system. The first administrative credential is created via cloud authentication. The first CA initialization calls a cloud PKI service. The first trust chain is established using an external root. The system is deployed. It runs. It authenticates users. It appears sovereign.
If your first credential requires external authentication, your system was never sovereign. It was sovereign-adjacent, initialized from a dependency that was never removed.
Bootstrap Failure Patterns. The most common forms of non-sovereign initialization:
The Minimum Viable Bootstrap (MVB). A sovereign identity system must be able to perform four operations without any external connectivity. These are not implementation steps — they are requirements. How they are implemented belongs to the execution layer. Whether they are possible at all is the sovereignty test.
Sovereign Identity Architecture Patterns
Six architectural patterns implement sovereign identity. Each solves a specific dependency class. None is a complete solution independently — sovereign identity requires the right combination of patterns for the specific dependency profile of the environment.
The Identity Sovereignty Test
Before treating identity sovereignty as complete, run this test. It is not a checkbox — it is a diagnostic. The scoring reveals where the architecture actually stands versus where documentation claims it stands.
Sever all external network paths. Then answer:
Can your system authenticate a user if the external IdP is unreachable for 30 minutes?
If yes: authentication sovereignty is likely intact. If no: the identity plane has failed before any other system.
Can your services validate tokens without calling an external JWKS or introspection endpoint?
If yes: token validation is sovereign. If no: every API call is an external dependency regardless of where the IdP runs.
Can your PKI issue and revoke certificates without external CA or OCSP reachability?
If issuance works but OCSP is external: partial. Certificates can be issued but revocation cannot be confirmed. Compromised certs remain operationally valid.
Can your PAM solution grant privileged access if the cloud vault is unreachable?
If no: privileged operations — including incident response — require external connectivity at exactly the moment it is most likely to be unavailable.
Can you rebuild your entire identity system from zero without any external connectivity?
If no: identity sovereignty is initialization-dependent on external systems. The system operates sovereignly at steady state and fails non-sovereignly under the conditions that require re-establishment.
When did you last test offline authentication under simulated external network loss?
Never tested = assumed sovereignty. Sovereignty is provable or it is assumed. The distinction is a test, not a design decision.
Zero-Trust vs Sovereign Identity
Zero-trust and sovereign identity are frequently conflated. They address different problems at different layers. Implementing one does not advance the other — and organizations that have invested heavily in zero-trust architecture frequently believe they have achieved identity sovereignty when they have not.
| Dimension | Zero-Trust | Sovereign Identity |
|---|---|---|
| What it answers | Who should be trusted, and under what conditions? | Can trust be established without external systems? |
| Core principle | Never trust, always verify — regardless of network location | Verify using only resources within the sovereign boundary |
| External dependency stance | Neutral — zero-trust can be implemented with cloud IdP, external policy engine, or local systems | Explicit — external dependencies are sovereignty violations regardless of how well-governed they are |
| Security posture | Improves — reduces implicit trust, enforces explicit verification | Orthogonal — sovereign identity can be insecure if poorly implemented; external identity can be highly secure |
| Compliance contribution | Strong — maps directly to NIST SP 800-207 and modern compliance frameworks | Specific — addresses jurisdictional data sovereignty requirements, not general security posture |
| Where they overlap | Identity-first governance, explicit credential verification, continuous authentication — concepts that serve both goals when implemented with sovereign components | |
| Where they diverge | Zero-trust with an external IdP is a security improvement. Sovereign identity requires that the IdP be within the boundary. Zero-trust does not constrain where the IdP lives. Sovereign identity does. | |
The practical consequence: an organization that has deployed a mature zero-trust architecture with cloud-hosted Okta as the IdP, cloud-evaluated OPA as the policy engine, and external JWKS endpoints for token validation has excellent security posture and zero identity sovereignty. The two are independent variables. Investing in one is not investing in the other.
Sovereign Identity for AI Workloads
AI infrastructure introduces three identity sovereignty failure modes that do not exist in traditional infrastructure. Each represents a credential or trust dependency that most AI architects have not modeled — because AI infrastructure identity is typically treated as an application security concern rather than a sovereignty architecture concern.
The Sovereign AI Mandate post covers the broader AI sovereignty surface — model weight custody, training data jurisdiction, inference endpoint governance, and prompt logging. This section covers specifically the identity dependency layer that most AI sovereign deployments leave unaddressed.
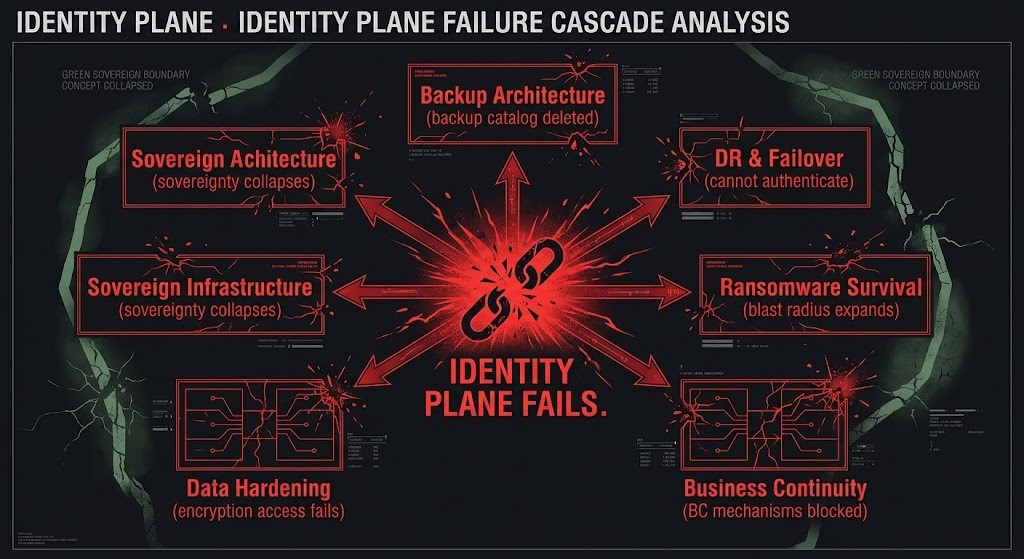
Where Identity Breaks Other Architectures
Identity sovereignty failures do not stay in the identity plane. They propagate. Every architecture that depends on authenticated access — which is every architecture — inherits the identity plane’s sovereignty status. When the identity plane fails, it takes the architectures built on top of it with it.
| Architecture | Identity Failure Impact | Specific Failure Mode |
|---|---|---|
| Backup Architecture | Backup deletion via compromised credentials — ransomware operators obtain backup management credentials and delete or encrypt the catalog before deploying the production payload | External PAM or cloud credential store compromised; backup control plane accessible via compromised identity; revocation cannot be confirmed because OCSP is unreachable |
| DR & Failover | Failover environment cannot authenticate operators or validate tokens — DR infrastructure boots, but identity plane is non-functional in the recovered environment | DR site lacks local IdP replica; token validation in recovered environment calls primary-site JWKS that is offline; PKI not replicated to DR boundary |
| Ransomware Survival | Credential compromise expands blast radius — compromised admin credentials with external IdP dependency cannot be revoked while the network is isolated; all systems accessible to the compromised credential remain at risk | External CRL/OCSP unreachable during incident; PAM vault unreachable; break-glass credentials in cloud secrets manager inaccessible; blast radius bounded only by what the attacker chooses to target |
| Business Continuity | Routing and authentication both fail simultaneously — BC architecture requires authorized operator actions to execute the degradation ladder; if identity fails, no operator can authenticate to trigger BC mechanisms | API gateway authenticating via external IdP fails alongside production services; BC control plane shares identity dependency with the failure it is meant to route around |
| Data Hardening | Encryption access controls cannot be evaluated — data hardening controls depend on authenticated access decisions; if token validation fails, encryption enforcement cannot determine who is authorized to decrypt | KMS access requires external IAM authorization; encrypted data becomes inaccessible not because of encryption integrity but because authorization cannot be evaluated |
| Sovereign Infrastructure | Entire sovereignty model collapses — all four sovereignty control planes (Identity, Management, Data, Network) require functioning identity for access decisions; identity plane failure breaks sovereignty at the first plane | Per the Rack2Cloud Sovereignty Control Plane Model: sovereignty fails at the first plane you don’t control. Identity is the most commonly uncontrolled. Everything above it is theoretical sovereignty. |
Decision Framework
| Scenario | Identity Sovereignty Requirement | Minimum Architecture | Risk if Skipped |
|---|---|---|---|
| Regulated data subject to GDPR, DORA, NIS2 | Local IdP + local JWKS + local PKI | Offline-capable directory + internal CA + local OCSP | Jurisdictional access order enforceable against cloud IdP; authentication fails during provider compliance action |
| Defense or national security workloads | Full MVB + SPIFFE/SPIRE for workload identity + offline break-glass | HSM-anchored root CA + local OIDC provider + SPIRE + air-gapped PAM | Nation-state access via provider IdP jurisdiction; credential compromise cannot be contained without external revocation |
| Healthcare or financial records, adversarial threat model | Local IdP + local PAM + offline revocation + local audit trail | Internal CA + local Keycloak or AD + offline CRL + SIEM with local write | Ransomware targets backup credentials via cloud IdP; blast radius expansion during network isolation; audit trail lost during incident |
| AI workloads processing regulated data | SPIFFE/SPIRE for service identity + local OIDC for operator access + local MLOps authentication | SPIRE + local Keycloak/Dex + MLOps tooling with local IdP integration | Inference endpoint access governed by cloud IAM; model lifecycle controlled by external identity; training pipeline authorization externally managed |
| Hybrid cloud with sovereignty-classified workloads | Identity segmentation — sovereign IdP for classified boundary, cloud IdP for non-classified | Identity plane separated by workload classification; no federation between sovereign and cloud identity domains | Cloud IdP federation extends into sovereign boundary; access decisions for sovereign workloads include external IdP in the chain |
| Startup or early-stage organization | Local PAM + offline break-glass minimum | Locally accessible break-glass credentials; PAM not exclusively cloud-hosted | Full Stage 3–4 sovereign identity overhead exceeds benefit at this scale; revisit at regulated workload threshold |
Identity Sovereignty Maturity Model
| Stage | State | What Exists | What’s Missing | Sovereignty Test |
|---|---|---|---|---|
| 1 | Compliant | Cloud IdP with MFA; user provisioning governed; access policies documented | All authentication dependent on external provider; no local fallback; JWKS external; no offline bootstrap path | Sever external network. Can any user authenticate? |
| 2 | Controlled | On-premises directory deployed; some local authentication possible; local PKI initiated | Cloud federation still active (Azure AD Connect sync); JWKS may still be external; break-glass credentials in cloud vault; bootstrap not tested offline | Disable Azure AD Connect. Does authentication degrade or fail? |
| 3 | Sovereign Identity | Local IdP fully independent; local JWKS; HSM-anchored internal CA; local OCSP; PAM with local vault; offline break-glass procedures | MVB not tested — offline bootstrap documented but never executed; SPIFFE/SPIRE not deployed for workload identity; machine identity still has external dependency | Full network isolation test: can every system authenticate, validate, and authorize without any external call? |
| 4 | Proven Sovereign Identity | All Stage 3 components plus: SPIFFE/SPIRE for workload identity; MVB executed and documented; offline authentication tested quarterly; audit trail locally immutable; AI identity surface addressed | Ongoing operational overhead — sovereign identity requires active maintenance, rotation discipline, and regular testing | All Identity Sovereignty Test questions answered PASS — with test results, not assumptions |
Stage 3 and Stage 4 are separated by testing, not architecture. Most organizations that have invested in sovereign identity reach Stage 3. The architecture is correct. The components are deployed. The gap between Stage 3 and Stage 4 is a single discipline: executed validation. An offline bootstrap that has never been run is an assumption. An identity system that has never been tested under network isolation is theoretical sovereignty.
Sovereign identity is the Identity Plane of the Rack2Cloud Sovereignty Control Plane Model. The pages below own the adjacent planes — the physical, management, data, and network layers that sovereign identity depends on and protects.
You’ve Read the Architecture.
Now Test Whether Your Identity Plane Actually Holds.
Cloud IdP coupling, JWKS escape, external OCSP dependency, PAM cloud link, bootstrap failure — most sovereign identity architectures look correct in documentation and surface their failure modes during the first real network isolation event. The triage session validates whether your specific environment passes the Identity Sovereignty Test before a failure event does it for you.
Sovereign Infrastructure Audit
Vendor-agnostic review of your identity sovereignty posture — IdP dependency mapping, JWKS and token validation audit, PKI chain analysis, PAM dependency assessment, bootstrap capability validation, and AI identity surface review.
- > Identity call path audit — all four layers mapped
- > JWKS and token validation external dependency scan
- > PKI chain analysis — root CA location and OCSP path
- > Bootstrap capability validation — MVB assessment
Architecture Playbooks. Every Week.
Field-tested blueprints from real sovereign identity environments — bootstrap failure post-mortems, JWKS escape incidents, PAM cloud link failure case studies, and the identity architecture patterns that held under real network isolation.
- > Identity Call Path Audits & Escape Point Mapping
- > Bootstrap Ceremony Design & MVB Validation
- > SPIFFE/SPIRE Workload Identity Case Studies
- > Sovereign PKI Architecture Patterns
Zero spam. Unsubscribe anytime.
Architect’s Verdict
Identity sovereignty is not the most visible part of sovereign infrastructure. It is the most consequential.
The organizations that have invested in physical sovereignty — hardware they own, data centers in the right jurisdiction, encryption with customer-managed keys — have built the foundation. And then they have left the door open. Not a visible door. Not a door that appears in architecture diagrams or compliance audits. A door that opens the moment external network connectivity fails: the authentication call that goes to Azure AD, the JWKS validation that calls the cloud endpoint, the PAM credential that requires the cloud vault to be reachable.
If your organization has deployed cloud-federated identity in an infrastructure it describes as sovereign — the identity plane has an external dependency that invalidates the sovereignty claim at the authentication layer. This is the most common sovereign architecture gap and the least frequently acknowledged. The fix is an architectural decision, not a configuration change: deploy a local IdP, serve JWKS locally, anchor PKI within the boundary. This is Stage 2 to Stage 3 on the maturity model. It is the most impactful single identity sovereignty improvement available.
If your organization has deployed local IdP and internal PKI but has never tested offline authentication — the architecture is sovereign in documentation. Whether it is sovereign in practice is unknown. Identity sovereignty is provable or it is assumed. Stage 3 and Stage 4 are separated by a test, not by additional architecture. Run the test. Sever external network paths. Authenticate. Validate a token. Revoke a certificate. Confirm that local audit logs captured the events. The test takes hours. It has never been run in most Stage 3 environments.
If your organization has proven sovereign identity — all components local, all tests passed, bootstrap documented and executed — the identity plane is controlled. Every architecture built on top of it inherits that control. Backup systems can be accessed during incidents. DR environments can authenticate when they boot. BC mechanisms can be triggered by authorized operators. Ransomware blast radius is bounded by the reach of the compromised credential, not expanded by the inability to revoke it.
The identity plane is where sovereignty survives or fails first. Build it to survive.
Frequently Asked Questions
Q: Is Active Directory sovereign identity?
A: Depends on the configuration. On-premises Active Directory with no cloud synchronization, no Azure AD Connect, and no cloud federation can provide sovereign authentication for users and systems within the domain. However: if Azure AD Connect sync is active, if there is cloud writeback enabled, or if the AD is federated to Azure AD for any workloads, there is an active external dependency in the identity chain. AD alone is not automatically sovereign — the sovereignty depends on whether any component of the AD trust chain has an external reachability requirement.
Q: Does Zero-Trust replace sovereign identity?
A: No. Zero-trust is an access model — never trust, always verify, regardless of network position. Sovereign identity is an independence model — all trust decisions are made using resources within the sovereign boundary. Zero-trust implemented with a cloud IdP improves security posture while adding an external dependency. The access model and the sovereignty model are orthogonal. You can have strong zero-trust with no sovereignty, or sovereign identity with weak access controls. The goal is both — but investing in one is not investing in the other.
Q: What is offline bootstrap capability?
A: Offline bootstrap capability is the ability to initialize an identity system — create the first credential, establish the root of trust, begin authenticating — without any external network connectivity. It is the test of whether sovereign identity was sovereign from the beginning or was initialized with an external dependency that was never removed. An identity system that required cloud console access to deploy, or an external CA to sign the root certificate, was not sovereign at initialization and carries that dependency forward regardless of how the system operates at steady state.
Q: Is SPIFFE/SPIRE required for sovereign identity?
A: Not universally — but for environments with significant machine-to-machine communication (Kubernetes, microservices, containerized workloads), SPIFFE/SPIRE is the most practical approach to sovereign workload identity. The requirement is not SPIFFE/SPIRE specifically — it is that service-to-service trust must be established without external CA dependency. SPIFFE/SPIRE is the CNCF-graduated mechanism most organizations use to meet that requirement. Alternatives include mTLS with locally issued certificates and service mesh configurations with internal CA integration.
Q: How does sovereign identity relate to HSM?
A: The HSM is the physical anchor for cryptographic sovereignty — the hardware that holds the root CA private key within the sovereign boundary. Sovereign identity depends on HSM at the foundation: if the root CA private key is not in locally controlled hardware, the trust chain that identity depends on terminates at an external component. HSM provides the physical key custody that makes cryptographic sovereignty possible. Sovereign identity without an HSM-anchored root is an identity system with a cryptographically external trust chain.
Q: Can Kubernetes achieve sovereign identity?
A: Yes — but it requires deliberate architecture at multiple layers. Kubernetes has several identity dependencies by default: service account tokens validated against the API server (which may call external OIDC), admission webhooks that may call external policy systems, container image pull authentication that may use cloud registry credentials, and service mesh workload identity that may use external CA. Each of these must be addressed for Kubernetes to operate with sovereign identity. SPIFFE/SPIRE for workload identity, local OIDC for service account token binding, and internal CA integration for service mesh are the three most critical changes.
Q: What breaks first when identity sovereignty fails?
A: Authentication. When the external IdP becomes unreachable, human access fails first — operators cannot log in to respond to the incident that triggered the isolation. This creates a compounding failure: the identity plane fails, which prevents the operators who would diagnose and fix the identity plane failure from accessing the system. This is why break-glass procedures with locally stored credentials are a non-negotiable component of sovereign identity — they are the path back in when the identity plane is the thing that is broken.
