Exit Cost as a First-Class Metric: The Architecture Constraint Nobody Models
Most architectures assume mobility. Multi-cloud, failover, workload portability — these are modeled as design goals, written into strategy documents, and presented to leadership as evidence of vendor independence.
Then the bill arrives.
The ability to move a system is not determined at migration time. It is determined by the cost of moving it. If you can’t afford to move it, you don’t control it.
Exit cost architecture is the discipline of modeling that constraint before it models you. Most teams don’t. They treat egress as a pricing detail, an optimization target, a future problem. The reframe is simpler and harder: exit cost is a control boundary on system movement. You don’t discover it when you leave. You embed it when you design.
What Exit Cost Actually Is
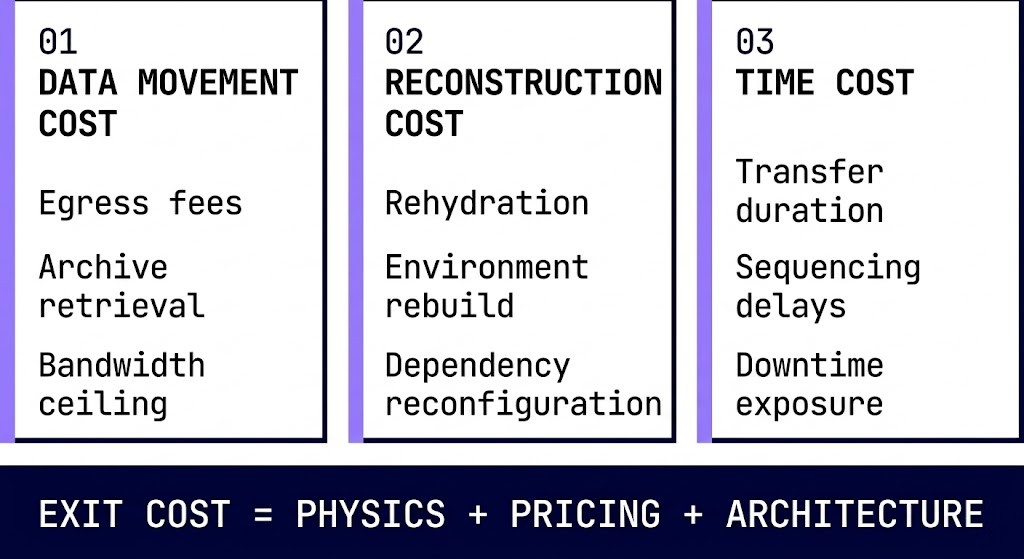
Exit cost is the total cost — financial, operational, and time — required to move data, workloads, and dependencies out of a system. It is not a line item. It is a sum of three components that most architecture reviews never model together.
Data movement cost. Egress fees are the visible surface — the number on the invoice. Beneath them are retrieval fees from archive tiers, bandwidth constraints at peak transfer rates, and the compounding cost of moving large datasets under time pressure. A petabyte that costs $20,000 to egress at standard rates costs significantly more when the business is down and the clock is running. The Cloud Repatriation Economics Engine makes that data movement cost concrete before the decision is forced — modeling egress, reconstruction, and break-even horizon against actual workload profiles.
Reconstruction cost. Data movement is only the first problem. The environment on the other side has to be rebuilt. Rehydration from deduplicated backup targets, dependency reconfiguration, environment rebuild from scratch — these are operational costs that rarely appear in egress calculators. The rehydration bottleneck alone has stranded recoveries that looked affordable on paper.
Time cost. Transfer duration is a constraint, not a variable. Sequencing dependencies introduce delays that can’t be parallelized. Downtime exposure accumulates across every hour the system is in transit. Time cost is the component that converts a financially viable migration into an operationally impossible one.
“Exit cost architecture models the sum of physics, pricing, and architecture. Most teams model one. All three must be modeled. Most teams model one.
Where Exit Cost Actually Comes From
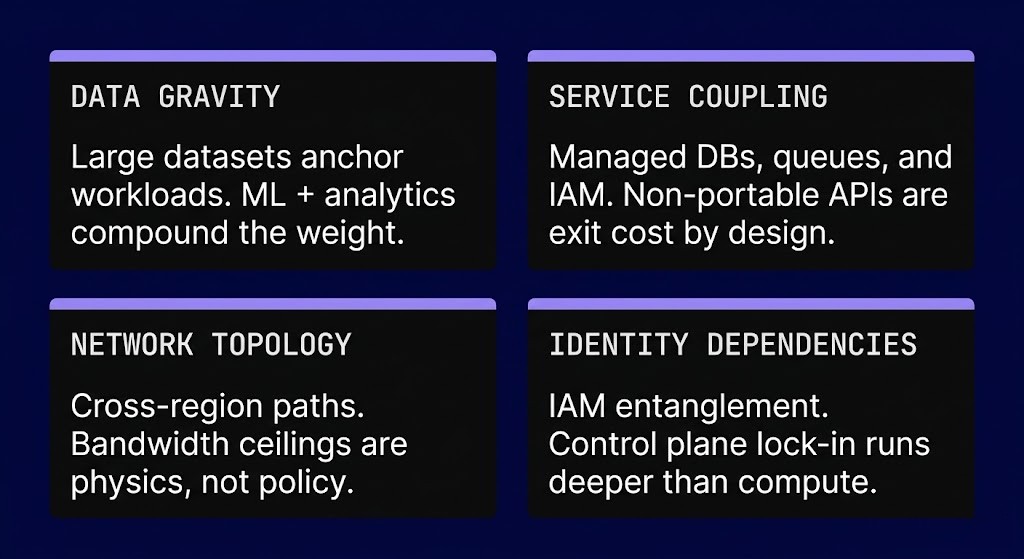
Egress fees are the entry point. They are not the problem. The problem is the architecture that makes egress fees unavoidable — and expensive at scale.
Data gravity. Large datasets anchor workloads to the provider that stores them. Data gravity compounds — ML training pipelines, analytics workloads, and data warehouses grow toward the storage layer, not away from it. The longer a workload runs in place, the heavier it becomes. Moving it later costs more than designing for locality now.
Service coupling. Managed databases, proprietary queuing systems, and cloud-native IAM are not portable abstractions — they are integration surfaces. Every dependency on a non-portable API is a weight added to the exit cost calculation. Vendor lock-in happens through service coupling, not through the APIs teams worry about. The managed service that saves six months of engineering work in year one can add six figures to exit cost in year three.
Network topology. Cross-region and cross-cloud paths introduce bandwidth ceilings and latency floors that are physics, not policy. Architectures that span availability zones within a provider absorb those costs as internal traffic. Architectures that need to move that traffic out discover the cost structure at the worst possible moment.
Identity and access dependencies. IAM entanglement is the least-modeled source of exit cost. When your workload’s authentication chain runs through a provider’s identity service, migration requires rebuilding that chain from scratch. Control plane lock-in — the dependency on a provider’s governance and policy infrastructure — is often deeper than the compute dependency it governs.
The more your system depends on what it doesn’t own, the harder it is to leave.
Why Teams Don’t Model It
Exit cost architecture is invisible during the build phase. It doesn’t appear in dashboards. It doesn’t affect day-one performance. It doesn’t trigger an alert, fail a health check, or show up in a sprint review. The architecture that embeds it looks identical to one that doesn’t — until the moment movement is required.
The incentive structure compounds the problem. Cloud cost is treated as an operational concern, not an architectural one. FinOps teams optimize within the current provider. Architecture teams make placement decisions without modeling the cost of reversing them. The gap between those two conversations is where exit cost accumulates.
Pricing complexity does the rest. Egress pricing is intentionally opaque — tiered by volume, by destination, by service type, by region. The teams making architecture decisions are not the teams reading the pricing documentation. By the time the bill is legible, the architecture has already made the decision.
Exit cost is invisible in design — and dominant in crisis.
Where It Breaks
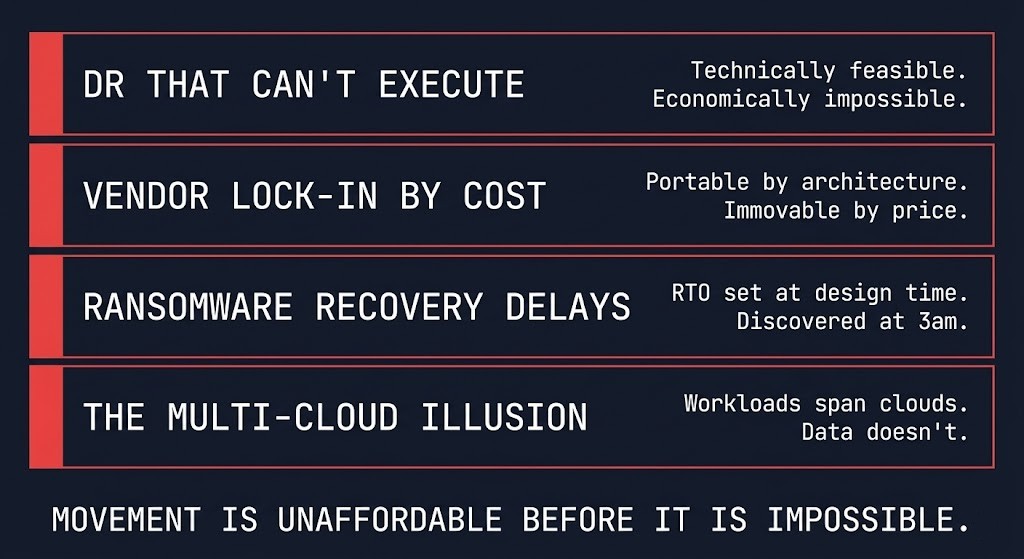
Exit cost becomes visible at exactly the moments when it is most expensive to discover it.
DR that can’t execute. Failover architectures are modeled for technical feasibility — can the workload run in the secondary environment? The question that breaks them is economic: can the data get there in time, at a cost the business can absorb? Failover that requires moving terabytes under an RTO of four hours may be technically possible and operationally impossible. RTO isn’t a target — it’s the output of constraints, and exit cost is one of those constraints.
Vendor lock-in by cost. Technical portability and economic portability are different properties. A workload can be containerized, documented, and theoretically movable while being practically immovable because the cost of the move exceeds the cost of staying. This is not lock-in by contract. It is lock-in by architecture — and it was created at design time.
Ransomware recovery delays. Mass restore operations are exit events under the worst possible conditions. Ransomware recovery time is an architecture problem — the retrieval cost, the bandwidth ceiling, and the rehydration time were all set before the incident. Teams that modeled their backup architecture without modeling the exit cost of recovery discover the gap at 3am during an active incident.
The multi-cloud illusion. Multi-cloud architectures assume workloads span providers. Data doesn’t move as easily as compute. An architecture that places workloads across AWS and Azure while anchoring its data layer to one provider’s storage tier hasn’t achieved multi-cloud resilience — it has achieved a multi-cloud billing model with single-cloud exit economics.
Architectures don’t fail because movement is impossible. They fail because movement is unaffordable.
Exit Cost Architecture as a Design Constraint
The correct reframe for exit cost architecture is simple. Stop asking: “Can we move this?” Start asking: “What would it cost to move this under pressure?”
Those are different questions. The first is answered by documentation. The second is answered by architecture.
Designing for exit cost as a constraint means making explicit decisions about data locality — where data lives relative to the workloads that consume it, and what the cost structure of moving it looks like at scale. It means treating replication and retrieval as a tradeoff with a price, not a configuration option. It means minimizing cross-boundary dependencies not because they’re technically wrong but because they accumulate cost that compounds under pressure. It means designing for partial mobility — the ability to move the most critical components first, independently, without triggering a full-stack migration.
Mobility is not a feature. It is a budgeted capability.
The connection to control is direct. Control means the ability to act — to fail over, to migrate, to respond. When exit cost is too high, that ability disappears. You cannot fail over if the data transfer cost exceeds the incident budget. You cannot migrate if reconstruction cost exceeds the contract savings. You cannot respond if the time cost exceeds the recovery window.
Exit cost is a control plane constraint disguised as a pricing model. The provider selection decision and the sovereignty posture are both downstream of how seriously exit cost was modeled at design time. Teams that treat it as a billing artifact make those decisions without understanding the constraint they’re accepting.
The Real World Egress Calculator is a starting point for making the data movement component concrete before an incident makes it urgent.
Architect’s Verdict
Exit cost architecture determines which systems retain control — not the ones with the lowest costs, but the ones that can move when they need to. They are the ones that can move when they need to — under real conditions, under time pressure, under adversarial circumstances that don’t wait for a maintenance window.
Exit cost determines whether that movement is possible. It is set at design time, embedded in every coupling decision, every data placement choice, every managed service dependency. It accumulates silently and surfaces suddenly.
If you haven’t modeled the cost of leaving your system, you haven’t modeled the system. Exit cost doesn’t show up when you leave. It determines whether you can leave at all. The same principle applies to governance authority. Organizations that discover their operating model never transferred governance responsibility to the cloud are facing an exit cost problem that was never on the invoice — the cost of rebuilding the governance layer they delegated away.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session





