Azure VMware Solution vs Native Azure: Architecture Trade-offs, Costs, and Exit Risk
Azure VMware Solution looks like the safe path out of a Broadcom licensing conversation. Your team already knows vSphere. Your tooling already maps to VMware constructs. AVS lets you move workloads to Azure without retraining anyone or rearchitecting anything. On paper, the risk profile looks low.
In practice, you’re not choosing where to run workloads. You’re choosing how hard it will be to leave later.
AVS feels like staying on-prem — just relocated into Azure’s billing model. That framing is the trap. Because AVS is not an architecture choice. It’s a migration strategy. Treating it as a destination is where most teams get it wrong, and where the financial and architectural consequences compound quietly until they don’t.
AVS doesn’t remove lock-in. It changes where the lock-in lives.
What Azure VMware Solution Actually Is
Azure VMware Solution is a managed VMware stack running on dedicated bare metal inside Microsoft’s datacenters. You get vSphere, vSAN, and NSX-T — operated by Microsoft, billed by Microsoft, sitting inside your Azure subscription. Your VMs migrate as-is. Your runbooks still work. Your ops team recognizes everything they’re looking at.
What you’re not getting is portability.
You’re not escaping VMware. You’re relocating it — into a metered, provider-controlled environment. The familiar operational surface is real. So is the new dependency structure underneath it. Microsoft controls the hardware. Microsoft controls the VMware licensing embedded in the service. Microsoft controls the upgrade cadence. You operate the guest layer. Everything below it is a managed service you cannot inspect, modify, or extract.
The on-prem model gave you hardware you owned, software you licensed, and an exit path that was physical and operational. AVS replaces that with a service construct where your exit cost is financial, architectural, and contractual — simultaneously.
That’s a different kind of commitment than most teams realize when they approve the migration plan.
The Case for AVS — Constrained Validity
AVS is not a wrong answer. It’s a correct answer under specific constraints — and only under those constraints.
The legitimate use cases are narrower than the sales motion suggests.
Regulatory environments with hard vSphere semantics. Some compliance frameworks, audit requirements, or contractual obligations are written around VMware-specific constructs. Stretched clusters, SRM-based DR, NSX-T microsegmentation policies — if your compliance posture depends on these behaviors and you cannot negotiate the underlying requirement, AVS preserves them in a cloud-delivered model. That’s real value.
Teams with deep VMware operational depth and no near-term capacity to retrain. The skill gap cost is not theoretical. If your operations team has fifteen years of vSphere expertise and zero cloud-native exposure, absorbing a full operational model shift while simultaneously migrating workloads is a recipe for incidents. AVS buys time. That’s a legitimate use of capital if the timeline is defined.
Short-horizon bridge strategies. If the plan is AVS for 24–36 months while you build cloud-native capability in parallel, migrate workload categories incrementally, and sunset the VMware layer on a committed schedule — that’s a strategy. The bridge serves a purpose. The exit is planned before the migration begins.
Hard application dependencies on VMware features. Some workloads have genuine VMware-layer dependencies that are non-trivial to abstract. These are increasingly rare but they exist. AVS is the right answer for this category — ideally while a parallel effort decouples the dependency over time.
AVS is correct in these scenarios. Outside them, the calculus changes.
VMware Migration Readiness Assessment
Before you commit to AVS, know what you’re actually migrating. The VMware Migration Readiness Assessment surfaces dependency complexity, licensing exposure, and exit risk before the architecture decision is final.
Run the Assessment →Native Azure Architecture — What You’re Actually Trading For
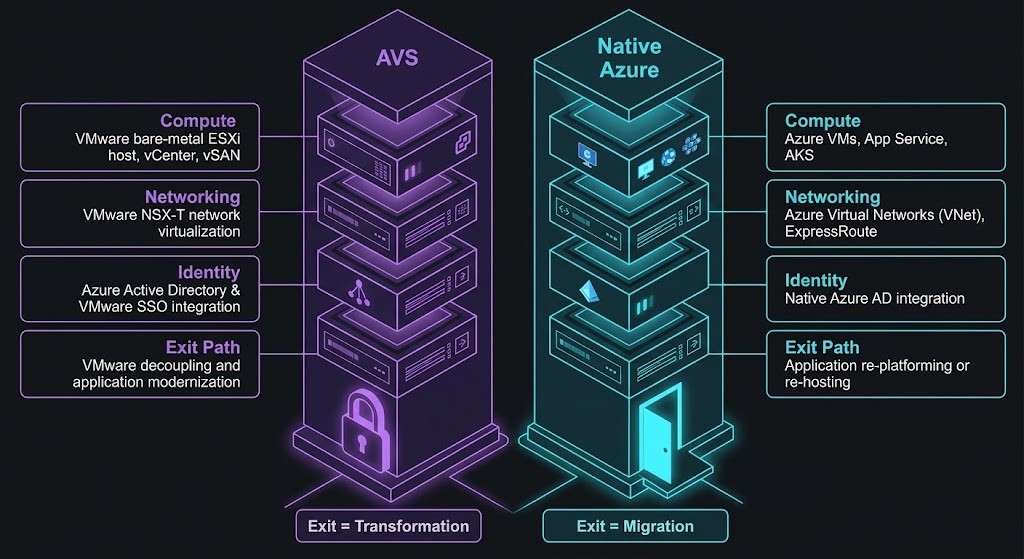
AVS preserves your operating model. Native Azure replaces it.
That’s not a criticism — it’s the design. Azure Kubernetes Service, Azure Arc, native Azure VMs, ExpressRoute, Azure Policy, Azure Monitor — the native stack is purpose-built for cloud-native operations. Teams that commit to it get better Azure service integration, better pricing leverage over time, cleaner egress economics, and most importantly, an exit path that lives in standard cloud primitives rather than a managed VMware layer.
The trade is front-loaded. You absorb the retraining cost, the tooling migration cost, and the operational model shift before you see the benefits. For brownfield VMware shops with large existing estates, that upfront cost is real and the timeline is long.
But the ceiling is higher. Native Azure workloads can take full advantage of the Azure service catalog without the translation layer that AVS introduces between your VMware environment and the rest of the Azure ecosystem. That translation layer has costs — in latency, in egress, and in operational complexity — that the native path avoids entirely.
Zero-Trust Azure Architecture Audit
If you’re committing to native Azure as the destination, the architecture decisions you make in the first 90 days define your security posture for years. The Zero-Trust Azure Architecture Audit validates your landing zone before the workloads arrive.
Get the Audit →Architecture Trade-offs — Direct Comparison
The decision isn’t about features. It’s about what each path does to your architecture over time.
| Dimension | AVS | Native Azure | Failure Mode |
|---|---|---|---|
| Portability | Low | Medium | AVS → platform lock-in at managed layer |
| Ops Model | Familiar (VMware) | New (cloud-native) | Native → skill gap drives incidents |
| Egress Costs | Higher (hidden paths) | Standard cloud model | Both → cost explosion without modeling |
| Licensing Overhead | Embedded + metered | Standard Azure pricing | AVS → bill opacity |
| Networking Complexity | NSX-T + Azure vNet | Azure-native only | AVS → dual-plane complexity |
| DR Options | SRM, stretched clusters | Azure Site Recovery, AKS | AVS → familiar but expensive |
| Azure Integration | Translation layer required | Native | AVS → service friction |
| Exit Path | Migration + transformation | Migration | AVS exit is a second transformation |
| On-Prem Comparison | Familiar model, cloud billing | Cloud model, cloud billing | AVS preserves on-prem patterns; Native breaks them |
AVS preserves on-prem operational patterns. Native Azure breaks them — by design. The question is whether you want to pay the break cost now or defer it.
Deferral has compounding interest.
Exit Cost Is the Variable Nobody Models
This is where the AVS decision gets architectural.
Exit cost is a first-class architectural metric — not a footnote you address when it’s time to leave. The cost of extracting yourself from a platform shapes every decision you make while you’re on it. AVS is a case study in why that principle matters.
Native Azure exit is expensive. AVS exit is expensive and complex.
When you leave native Azure, you’re moving cloud-native workloads. You’re dealing with standard cloud egress physics — predictable, modelable, painful but understood. The egress cost architecture is visible. You can plan against it.
When you leave AVS, you’re not executing a migration. You’re executing a second transformation. Your workloads are running in a VMware environment that was itself migrated into Azure. Leaving means:
- Translating VMware constructs to whatever target platform you’re moving to
- Extracting from Microsoft’s managed VMware layer (not a clean export)
- Re-establishing networking, policy, and identity constructs in the destination
- Absorbing the egress costs of moving data out of Azure at scale
On-prem exit cost is physical and operational — decommission hardware, terminate licenses, move data. AVS exit cost is financial, architectural, and contractual. You’re unwinding a managed service relationship while simultaneously performing a platform migration.
AVS exit is not a migration. It’s a second transformation. Most teams don’t model this when they approve the initial AVS business case.
The vendors who sell AVS don’t lead with that.
The Hidden Costs of AVS Nobody Quotes
The published price is for compute. The real cost is in everything around it.
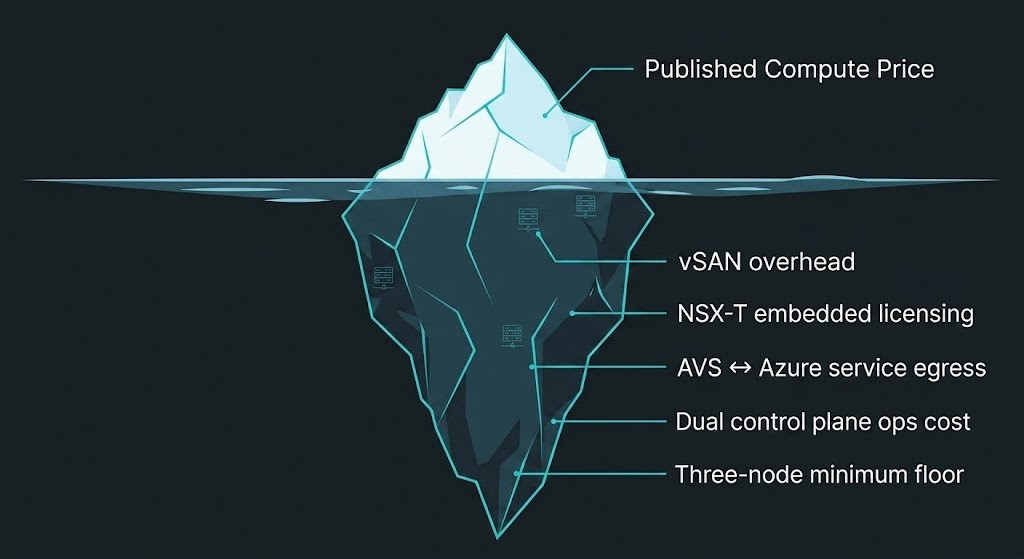
Dedicated bare metal pricing. AVS runs on dedicated hosts. You’re not sharing infrastructure. The minimum cluster is three nodes. The per-node pricing reflects dedicated hardware — you pay for capacity whether you use it or not. There is no burstable, no reserved-instance flexibility equivalent to standard Azure VM pricing. The floor is fixed.
vSAN storage overhead. vSAN has inherent storage overhead from erasure coding and redundancy. Your usable capacity is materially lower than your raw node capacity. This is not prominently advertised in the cost estimates most teams receive.
NSX-T licensing is embedded in the bill. You’re not licensing NSX-T separately — it’s baked into AVS pricing. But you’re paying for it regardless of how much of the networking capability you actually use. If you were running basic NSX on-prem, you’re now paying for enterprise-grade NSX-T utilization whether your architecture needs it or not.
AVS to native Azure service egress. This is the most consistently overlooked cost. Traffic between your AVS environment and native Azure services — Azure SQL, Azure Storage, Azure Monitor, anything in the broader Azure service catalog — is not always free. The paths matter. The pricing depends on where your AVS instance lives relative to the services consuming it. This adds up quickly at scale, and it almost never appears in the initial cost modeling.
Operational overhead on two control planes. When you run AVS alongside native Azure services — and almost every AVS deployment does — you’re operating two networking models, two identity planes, and two sets of tooling simultaneously. That operational complexity has a cost in engineering time that doesn’t show up in any Azure invoice.
Vendor lock-in almost always happens through networking, not APIs. AVS is a clean example of why.
When to Choose AVS vs Native Azure
The decision comes down to where you are in your cloud maturity, what constraints you’re operating under, and whether you’re treating this as a bridge or a destination.
Choose AVS if
- Compliance requirements mandate vSphere-specific behaviors you cannot renegotiate
- Your team has deep VMware expertise and no capacity to absorb an operational model shift during migration
- You have a defined, dated exit plan to move off AVS within 3–5 years
- Specific workloads have hard VMware dependencies with no near-term abstraction path
AVS as a deliberate bridge is defensible. AVS without an exit plan is not.
Choose Native Azure if
- Workloads are net-new or have no hard VMware dependencies
- Your team has cloud-native capability or the timeline and budget to build it before migration
- You’re making a long-term Azure commitment and want the ceiling that native integration provides
- Exit optionality matters to your organization’s architecture principles
If you don’t have an exit plan, AVS becomes your destination by default.
A destination nobody planned for is a different category of problem than a migration strategy that outlived its purpose.
For architects who have committed to an on-premises or HCI path rather than AVS, the VMware Migration Strategy Track maps what follows the platform decision: the execution
physics, failure domains, policy portability, and governance normalization work that determines whether the migration holds together operationally after cutover.
Before You Finalize This Decision
Run one check.
The AVS Decision Test
Are you using AVS to:
Buy time for a defined migration?
This is what AVS is designed for. The bridge has a purpose if the exit is planned.
Avoid retraining your team?
You’re deferring a cost that compounds. The skill gap doesn’t close while you’re on AVS.
Delay re-architecting legacy workloads?
The architecture debt doesn’t dissolve in Azure. You’ll pay the transformation cost on exit — on top of everything spent deferring it.
Only one of these is a strategy. The others are deferrals.
The deferral isn’t free. You’re paying for it in AVS node costs every month while the underlying architecture problem remains unsolved. When you eventually exit — and exit you will, because AVS as a permanent destination is an expensive endpoint — you’ll pay the transformation cost on top of everything you spent deferring it.
Model the exit before you commit to the entry.
Architect’s Verdict
If you’re using AVS as a deliberate bridge with a committed exit timeline — this is the correct call. AVS with a 3-year migration roadmap, defined workload categories, and a parallel cloud-native capability build is a rational use of the platform. You’re buying operational continuity while building toward the destination. The costs are real and modelable. The path is defensible.
If you’re treating AVS as a permanent destination — AVS without a defined exit path is not a strategy. It’s deferred lock-in. You’ve traded Broadcom’s licensing model for Microsoft’s managed service model, paid a premium for the familiar operational surface, and left yourself with an exit that is more expensive and more complex than the on-prem environment you left. The lock-in didn’t go away. It changed addresses.
If you’re moving brownfield VMware workloads directly to native Azure without a plan — the operational model shock is real and the skill gap will drive incidents before it drives competence. Native Azure is the right destination. Arriving there without preparation is its own category of risk. Use AVS as the bridge it was designed to be, not as a shortcut you skip because the native path looks harder.
The platform decision isn’t the hard part. The hard part is knowing what you’re deciding.
AVS doesn’t remove lock-in. It changes where the lock-in lives. The Architect’s job is to know where that is before signing the migration order.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session





