NETWORKING ARCHITECTURE PATH
DETERMINISTIC PACKET MOVEMENT, FABRIC DESIGN, AND LATENCY CONTROL.
Why Networking Architecture Matters
Compute is the brain. Storage is the permanent memory. Networking is the nervous system.
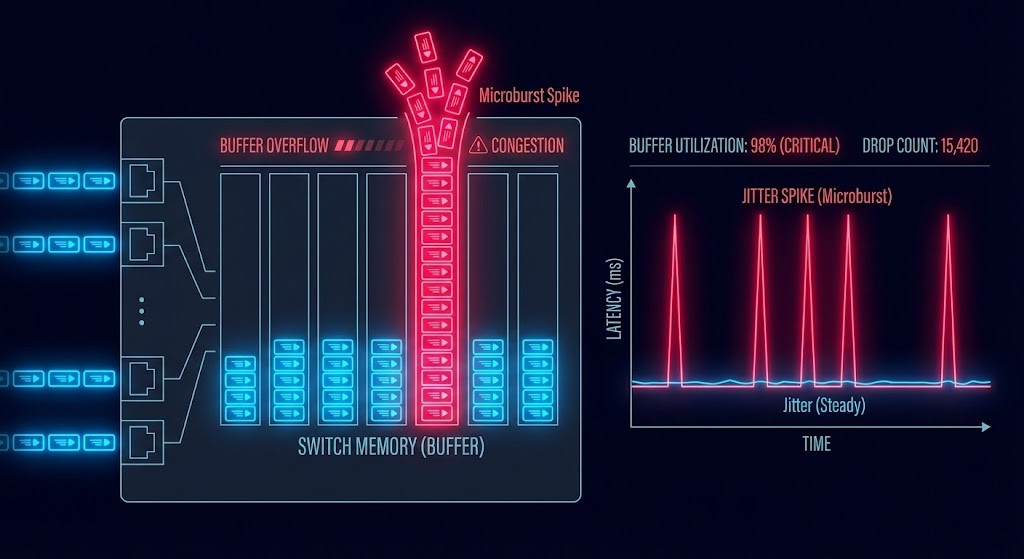
When you treat networking as “just switches and cables,” you inevitably design a bottleneck. Poorly architected networks create microbursts, asymmetric routing, broadcast storms, and unpredictable latency under load. Applications fail not because servers are weak — but because packets arrive late, out of order, or not at all.
Without a strict understanding of packet physics, buffer architecture, and routing logic, infrastructure becomes fragile under stress.
This learning path eliminates vendor marketing narratives and focuses strictly on deterministic packet delivery across private, hybrid, and public cloud fabrics.
No “infinite line-rate” myths.
No oversimplified bandwidth charts.
Just the raw physics of packet movement.
Who This Path Is For
To master the network layer, you must transition from a traditional “Network Administrator” to a “Network Architect.”
- Network & Infrastructure Engineers: Responsible for switching, routing, VLAN segmentation, and physical fabric configuration.
- Platform & SRE Engineers: Designing distributed systems where east-west traffic, latency consistency, and observability determine application reliability.
- Architects & Consultants: Senior engineers tasked with designing scalable, low-latency fabrics that balance performance, failure domains, and operational simplicity.
Note: Foundational routing and switching knowledge (subnetting, ARP, BGP fundamentals) is assumed before progressing into deterministic fabric design.
The 4 Phases of Networking Architecture Mastery
Phase 1: Topology & Packet Physics
Determinism begins at the topology layer. Before overlays, before automation, before SDN — you must understand how packets physically traverse a copper or fiber fabric.
Architects must understand:
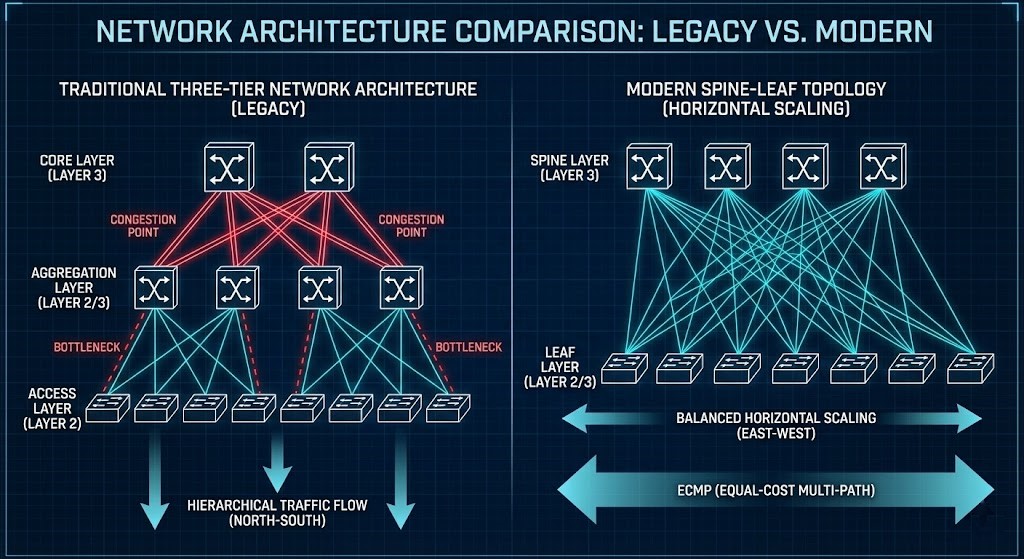
- The physical trade-offs of Spine-Leaf vs. legacy three-tier core/aggregation architecture.
- The evolution of East-West (server-to-server) vs. North-South (client-to-server) traffic ratios.
- Layer 2 broadcast domains vs. Layer 3 routing boundaries.
- ECMP (Equal-Cost Multi-Path) hashing behavior.
- Buffer depth, queue architecture, and the destructive impact of microbursts.
>_ Deep Dive Spoke: See exactly how storage rebuild storms expose weak network fabrics in our massive data study: Nutanix AHV vs vSAN 8 I/O Benchmark.
Outcome: You will design fabrics that eliminate spanning-tree collapse and scale horizontally without localized bottlenecks.
Phase 2: Routing Logic & Distributed Control Planes
Packets follow policy. Policy follows protocol. Understanding modern routing means understanding convergence, failure domains, and route propagation behavior across distributed environments.
Architects must understand:
- BGP (Border Gateway Protocol) state fundamentals.
- OSPF vs. BGP in modern data center cores.
- Route reflectors and convergence timing physics.
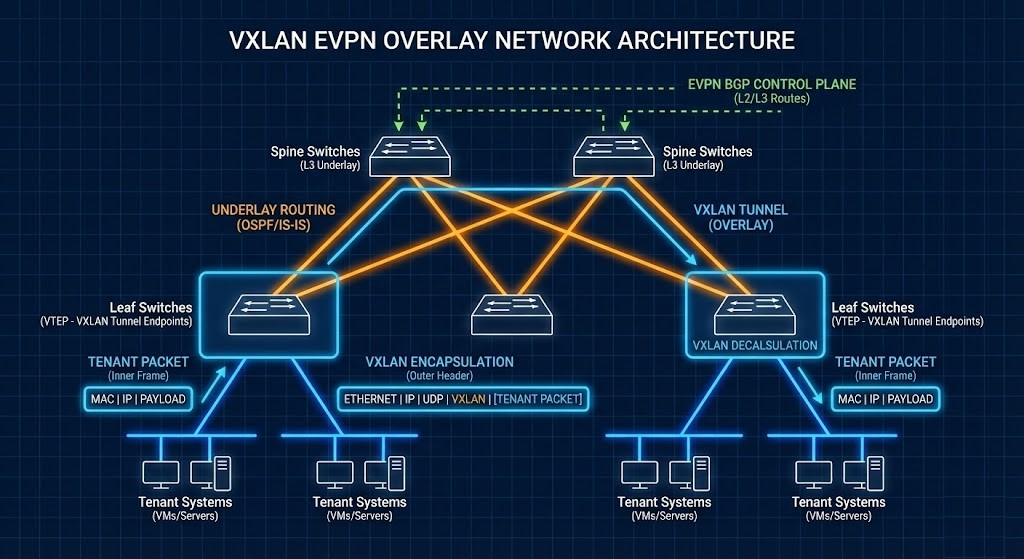
- VXLAN overlay control planes (EVPN).
- Asymmetric routing risks and stateful firewall drops.
Workbench Tool:
- NSX-T to Flow Translator: Changing your overlay network? Instantly map and audit your VMware NSX-T firewall logic to Nutanix Flow without manual translation errors.
Outcome: You will model route failure and convergence mathematically before production outages occur.
Phase 3: Performance Engineering & Latency Control
Bandwidth is not performance. Throughput without latency consistency is operational instability.
Architects must master:
- Microburst detection and queue mitigation.
- Jumbo frame consistency (MTU alignment and fragmentation penalties).
- RDMA (Remote Direct Memory Access) and RoCEv2 transport physics.
- NIC interrupt moderation and offload tuning at the hypervisor level. (To master the abstraction layer that controls these vNICs, explore our Modern Virtualization Pillar).
- Buffer tuning in high-density, hyperconverged fabrics.
Workbench Tool:
- Metro Latency Scout: Storage and compute rely on network latency. Validate your exact Round-Trip Time (RTT) thresholds to ensure synchronous replication stability across physical failure domains.
Outcome: You will design fabrics capable of sustaining AI training clusters, distributed databases, and high-frequency transaction systems.
Phase 4: Observability, Segmentation & Survival Architecture
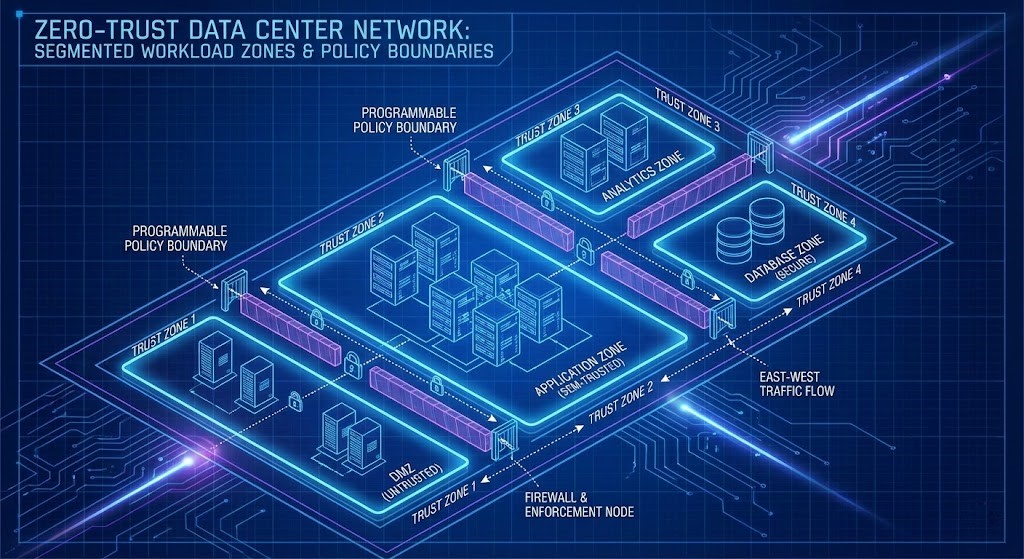
Visibility determines survivability. A network without telemetry is a liability. Whether the underlying platform comes from traditional switching vendors or open networking ecosystems, policy must be version-controlled, auditable, and secure.
Architects must design for:
- NetFlow & sFlow telemetry pipelines.
- Packet capture strategies without service disruption.
- Zero-trust segmentation and microsegmentation policy enforcement.
- Non-disruptive, traffic-draining firmware upgrades.
>_ Deep Dive Spoke: Bring CI/CD and version control to your network configuration. Read our guide: Infrastructure as a Software Asset: Why You Need CI/CD.
Workbench Tool:
- Azure PE Checker: Extending your fabric to the public cloud? Run a stateless audit on your Azure Private Endpoints to instantly detect recursive DNS loops and subnet exhaustion.
Outcome: The network becomes observable, programmable, and entirely resilient against both misconfiguration and adversarial traffic patterns.
Vendor Implementations Through an Architectural Lens
While vendors implement routing differently, the physics of convergence and packet forwarding remain constant. Architectural decisions must be physics-driven, not feature-driven.
| Platform | Fabric Model | Economic Model | Ideal Use Case |
| Cisco (Nexus/ACI) | Integrated switching & routing stack | Hardware-centric licensing | Enterprise core & campus |
| Juniper (Apstra) | EVPN-first data center fabrics | Subscription + hardware | Service provider & dense DC |
| Arista | Low-latency programmable fabrics | Software-defined EOS stack | High-frequency & AI workloads |
Continue the Architecture Path
Networking does not exist in isolation. Once you understand deterministic packet delivery, you must integrate it with the compute and storage layers it serves. Continue mastering the stack:
- Modern Virtualization Learning Path
- Modern Compute Logic
- Enterprise Storage Logic
- HCI Architecture Learning Path
- Performance Modeling Learning Path
- Data Protection & Resiliency Path
Frequently Asked Questions
Q: Is this aligned with certifications like Network+ or CCNA?
A: Yes, but it goes much further. Foundational routing and switching knowledge is assumed. This path advances strictly into architectural determinism and performance modeling at the enterprise level.
Q: Is this path vendor-neutral?
A: Yes. While we reference platforms from Cisco, Juniper, Arista, and VMware, the underlying packet physics, EVPN overlays, and routing logic apply universally across all silicon.
Q: Do I need hands-on experience for this?
A: Strongly recommended. You cannot truly understand BGP convergence behavior, MTU mismatches, or microburst packet loss until you observe them in a lab environment under controlled load.
DETERMINISTIC NETWORK AUDIT
Networking is the nervous system of your enterprise. Stop guessing at your microburst thresholds, EVPN convergence times, and cloud routing loops. Run your environment through our deterministic calculators to validate your architecture.
LAUNCH THE ENGINEERING WORKBENCH