Governing The Shadow Architecture: A 2025 Guide to Enterprise LCNC
Enterprise low-code governance isn’t optional in 2025 — it’s the difference between a managed platform and a shadow architecture that owns your data before security finds it. Around 2018, I watched a Fortune 500 financial firm lose six months of engineering velocity because a marketing sub-team built a “simple” customer intake portal using a No-Code tool that didn’t support their VPC security requirements. By the time the Security Architects found it, 50,000 PII records were sitting in an unencrypted third-party database.
This is the reality of “Citizen Engineering” in 2025. According to Gartner’s 2025 Forecast, low-code technologies will be used in over 70% of new applications. It is not a trend you can stop; it is a Shadow Architecture you must learn to govern. When you are designing for Day 2 operations, Shadow IT is no longer just about unapproved SaaS apps; it is about unvetted logic
Why Architects Choose “Shadow Architecture” Remediation
In the trenches of enterprise migration, we often treat Low-Code as a “toy” for the business units. This is a mistake. The goal of a modern architect is to provide a Managed Platform that allows non-developers to build without creating security holes, following industry standards like Microsoft’s Security Best Practices for Low-Code.
The Decison Matrix: LCNC vs. Serverless
| Feature | No-Code (e.g., Bubble/Zapier) | Low-Code (e.g., PowerApps/Retool) | Native Serverless (Lambda/Functions) |
| Primary User | Business Unit / Non-Technical | Solution Engineer / Power User | Cloud Engineer / Developer |
| Governance | Platform-locked (Difficult) | RBAC & Environment Sync | Full GitOps / Policy-as-Code |
| Data Residency | Shared Tenant (Risk High) | Dedicated / Hybrid Options | Full VPC Isolation |
| Scaling Cost | Per User / Per Workflow | Per User / Per App | Pay-per-execution (Sub-penny) |
| The “Escape Hatch” | Non-existent (Vendor Lock) | Partial (Custom Code/APIs) | Total (Portability) |
The “Guardrail API” Pattern: Engineering a Paved Road
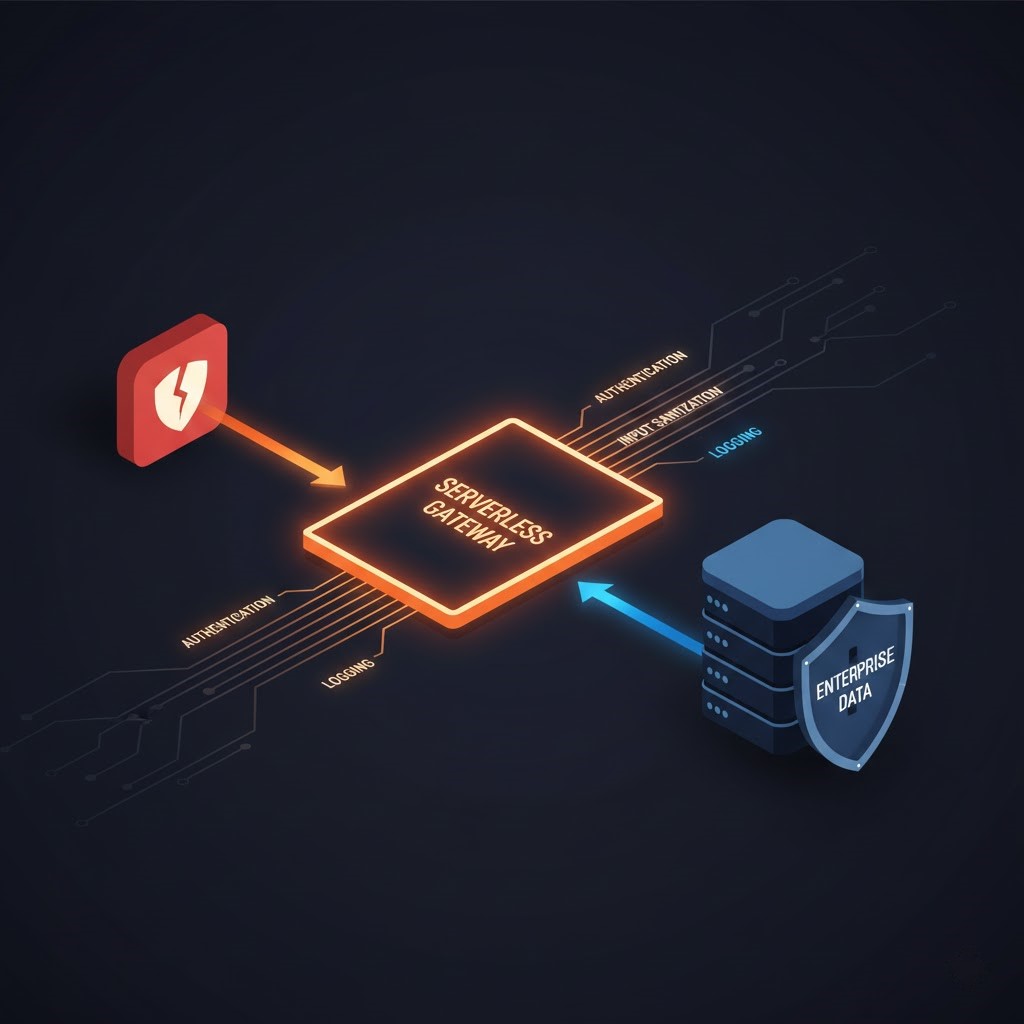
Instead of allowing a Low-Code tool to talk directly to your Production SQL or S3 buckets, I recommend the Serverless Proxy Pattern. This approach directly mitigates the OWASP Top 10 risks for No-Code/Low-Code, specifically addressing Insecure Data Integration.

By using Amazon API Gateway and AWS Lambda, you create a thin layer that handles the “dirty” work the LCNC tools cannot. This allows business users to use their visual builders while you maintain total control over the data plane.
The Guardrail API Checklist:
- Authentication: Validates the LCNC tool’s service token via OIDC.
- Validation: Sanitizes and schema-checks inputs before they hit your core database.
- Logging: Records every action into your central CloudWatch or Splunk logs for an immutable audit trail.
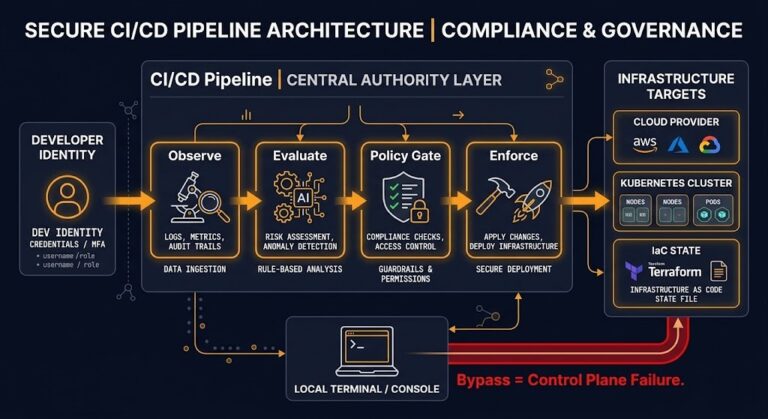
Orphaned LCNC applications create the same drift problem as manual console changes — untracked state that diverges silently from policy. The Infrastructure Drift Detection Guide covers the detection and remediation protocol.
Mandatory Cost Analysis: The “Refactoring Cliff”
Choosing an LCNC platform is often a CapEx vs. OpEx decision, but many architects overlook the Unit Cost at scale. Use our interactive calculator below to find the specific “Cliff” for your current project.
The per-user licensing model is only part of the cost exposure. For the full FinOps framework for modelling cloud unit economics — including how OpEx-heavy SaaS tools compound against native execution costs — see cloud cost basics.
Rack2Cloud
Refactoring Cliff AnalysisOperational cost comparison between Low-Code licensing and native Serverless infrastructure.
Enter your user count and monthly execution volume to find the exact crossover point where your LCNC licensing cost exceeds native serverless execution. Most teams hit the cliff between 80–150 users — the calculator shows you your specific number before it shows up on a cloud bill.
→ Find My Refactoring Cliff- Low-Code (OpEx-Heavy): Most platforms charge $20–$100 per user/month. For an internal tool with 500 users, you are looking at $60,000/year just for the right to run the application logic.
- Serverless (Efficiency-Heavy): The same logic ported to a native Serverless architecture (Lambda + DynamoDB) often costs less than $50/month, as verified by the AWS Pricing Calculator.
Architect’s Verdict
Use LCNC for MVPs and Low-User internal tools. If an app hits a “high-concurrency” state or scales beyond 100 users, the “Licensing Tax” makes a native Serverless rewrite the only fiscally responsible engineering choice.
If you’re mapping the broader governance stack — IaC policy enforcement, drift detection, and platform controls — the Modern Infrastructure & IaC Learning Path sequences the full architecture from LCNC guardrails through sovereign infrastructure.”
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session