The “Day 2” Broadcom Reality Check: VCF Operations: Decoupling the Stack When You Can’t Decouple the License

Broadcom VCF Operations in 2026 present a challenge no marketing deck prepared you for: you bought the full stack, but deploying all of it creates more operational debt than it solves. NSX, Aria, SDDC Manager — the license includes everything. The engineering question is which parts to actually run. This guide covers three strategies for managing VCF operations complexity without letting the bundle dictate your architecture.
The Problem with VCF Operations: “Shelfware as a Service”
The core friction in 2026 isn’t the cost (that battle was lost or won at the signing table); it is the Operational Tax.
When you deploy the full VCF stack via SDDC Manager, you are entering a “Lock-Step” Lifecycle Management (LCM) model. You cannot simply patch ESXi because a security vulnerability was found. You must check if that ESXi patch is validated for your current SDDC Manager version.
If you check the official VMware Cloud Foundation Release Notes, you will see the rigid “Bill of Materials” (BOM). To upgrade vSphere, you might first need to upgrade NSX, which might require an upgrade to Aria Suite Lifecycle Manager.
We call this “Bundle Bloat.” It turns agile infrastructure into a monolith.
Strategy 1: The “Lean Core” Architecture
The most effective way to manage VCF is to conceptually decouple the Commercial Entitlement from the Technical Implementation.
You own the licenses. Great. That stops the audit. It does not dictate your architecture.
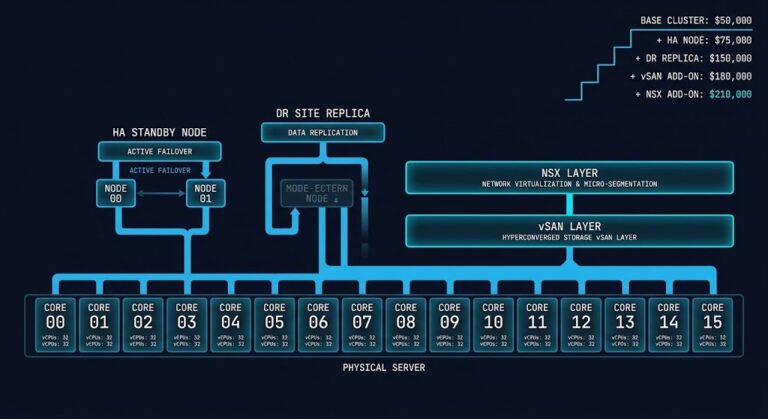
- vSphere & vSAN: Deploy these everywhere. They are the core.
- NSX: Only deploy the NSX Managers if you have a specific use case (Micro-segmentation or Overlay networking). Do not deploy it for simple VLAN-backed segments just to “light up” the dashboard.
- Aria Suite: If you don’t have a dedicated FinOps or Cloud Automation team, leave these binaries in the portal. They consume massive RAM and compute resources—resources that you are paying for per-core.
If you aren’t sure how many cores these management appliances are burning, run the numbers on our VMware VVF/VCF Core Calculator. You will often find that the management overhead alone can cost you thousands in hardware density.
Management appliances — NSX Managers, Aria Suite, SDDC Manager — consume cores and RAM that don’t show up in your VM density math. Run your environment through the Core Calculator to see exactly what the management overhead is costing you in hardware density before you commit to a full stack deployment.
→ Calculate My VCF Core TaxArchitect’s Rule: Never deploy software to solve a problem you don’t currently have, even if that software is “free.”
Strategy 2: Avoiding the “SDDC Manager” Trap
SDDC Manager is the orchestration engine of VCF. It promises “One-Click Upgrades.” In reality, for many brownfield environments, it enforces a rigid Hardware Compatibility List (HCL) and software interdependency matrix.
If you are running standard rack-mount servers (Cisco UCS, HPE ProLiant, Dell PowerEdge) and your team is comfortable with vLifecycle Manager (vLCM), you do not strictly need SDDC Manager for every cluster.
You can run VCF operations on a standard vSphere cluster without bringing every cluster under the full SDDC Manager umbrella. This preserves your ability to patch vCenter and ESXi independently—critical for rapid security responses in the age of ransomware.
Strategy 3: Decoupling the “Value Add”
If you are forced to pay for the full stack, the goal of day-2 VCF operations is to extract value without inheriting complexity.
- Instead of Aria Operations: You might stick with your existing monitoring tools (Datadog, LogicMonitor) if they are already tuned.
- Instead of NSX Security: If the complexity of NSX Distributed Firewalling is too high for your team, consider simpler, agent-based alternatives or hypervisor-agnostic tools that don’t tie you to the kernel.
We recently broke down the complexity of migrating these security rules in our guide: Translating the Stack: A Field Guide to Migrating NSX-T Security. The lesson there applies here: don’t implement complexity unless the business outcome demands it.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session