Rubrik vs Veeam — Appliance Immutability vs Infrastructure Control
Most Rubrik vs Veeam comparisons start with the wrong question.
Not which platform has better deduplication ratios or a cleaner dashboard. Not which vendor has a stronger roadmap or a bigger channel. Those comparisons exist everywhere and they don’t help you make the decision.
The question that matters is architectural: where does operational authority live when your environment is under active attack, your identity plane is compromised, and you need to recover from zero? Rubrik and Veeam give fundamentally different answers — and the wrong choice doesn’t fail on a feature checklist. It fails at 2am during an incident.
That’s the comparison worth having.
The backup platform decision isn’t about features. It’s about where you want failure to exist.
The Constraints That Actually Matter
Before you evaluate either platform, map your environment against the constraints that actually drive the decision. Feature checklists won’t surface these. Incident postmortems will. The Data Protection Architecture pillar maps the full decision space — but these are the five inputs that determine whether Rubrik or Veeam fits your environment specifically.
None of these appear on a vendor datasheet. All of them will determine whether your platform decision holds when the environment is under pressure.
Two Models of Authority — And Their Breaking Points
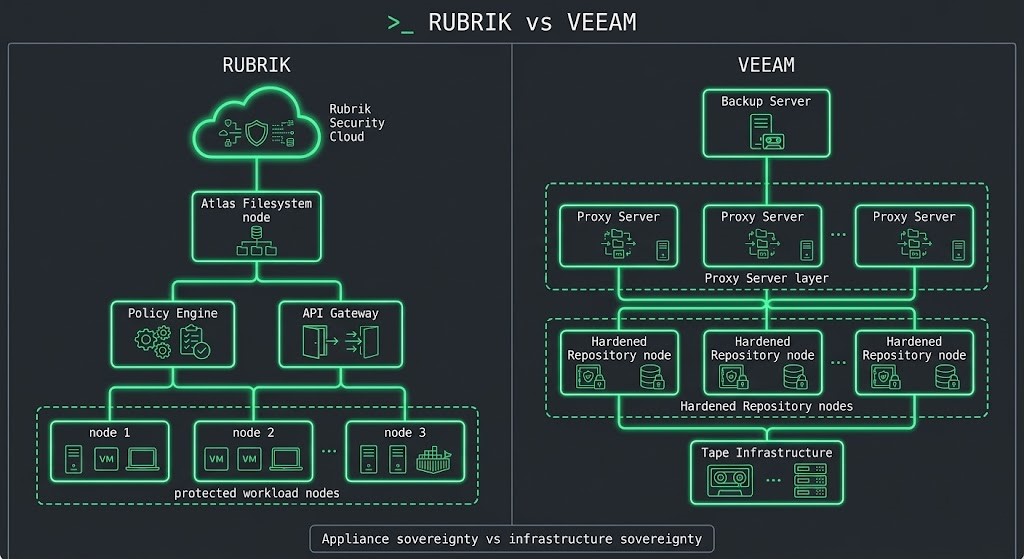
Rubrik and Veeam are not competing on features. They are built on fundamentally different assumptions about where operational authority should live and who is responsible for enforcing it.
Where Each Architecture Starts to Struggle
Neither platform fails uniformly. Each has specific conditions under which the architecture starts working against you. These are the breaking points most teams discover after the purchase order — not before it.
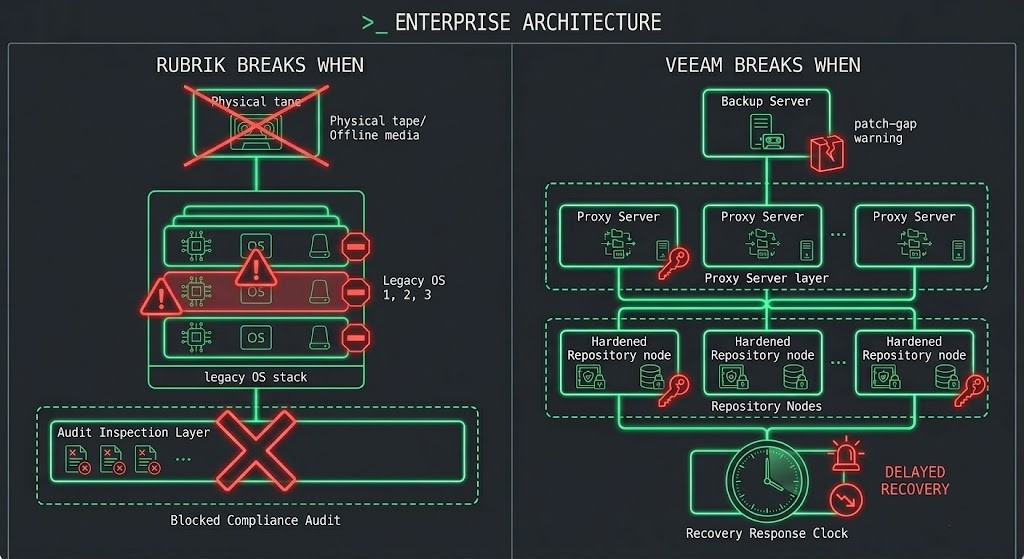
- [!] Physical air-gap compliance requires tape vaulting, offline rotation, and manual custody chains. Rubrik’s architecture assumes logical isolation — it has no answer for environments where humans must move the media.
- [!] Legacy ecosystem depth matters — physical servers, unsupported operating systems, and non-standard hypervisors push against the appliance’s integration boundaries in ways Veeam handles natively.
- [!] Audit requirements demand full OS-layer visibility and inspectable infrastructure. When the compliance posture requires seeing every layer, a black-box appliance architecture creates documentation and audit gaps.
- [!] Immutability hardening is misconfigured or incomplete. Veeam’s hardened repository model is sound — but it requires deliberate configuration. The gap between “Veeam installed” and “Veeam hardened” is where most ransomware incidents find their entry point into backup infrastructure.
- [!] Staffing is limited and patching discipline slips under operational load. Every component in the Veeam stack — Backup Server, Proxy, Repository — is a patch surface. In lean teams, this overhead compounds directly into security exposure.
- [!] Recovery speed is the primary metric. Veeam can recover fast — but recovery performance depends on the repository and proxy architecture you built. Rubrik’s recovery speed is baked into the appliance design. You configure Veeam’s; Rubrik’s is the baseline.
Day-2 Operational Reality
[PARAGRAPH] The platform decision you make on day one becomes your operational inheritance on day 365. These are the day-2 realities that surface after the implementation team leaves.
Patch burden. Veeam’s distributed architecture means the Backup Server, Proxy Servers, and Hardened Repositories all carry independent patch cycles. In environments with rigorous change management, this is manageable. In lean teams operating under incident load, it is the most common source of backup infrastructure exposure. Rubrik’s appliance model shifts patch responsibility to the vendor — which removes the overhead and removes your control over timing.
Credential hardening. Veeam requires deliberate credential isolation — service accounts, repository access controls, and backup server hardening are not defaults. Rubrik’s API-mediated architecture makes credential-based lateral movement structurally harder. The attack surface difference is meaningful, but only if Veeam’s hardening steps are actually completed and maintained.
Upgrade blast radius. Veeam upgrades are self-managed — full control over scheduling and sequencing, full ownership of any upgrade-related incidents. Rubrik’s appliance model means vendor-managed upgrade cadence, which removes coordination overhead at the cost of timing control. Neither is inherently better; one fits teams that want operational autonomy, the other fits teams that want to hand off the maintenance cycle.
Support model. Veeam’s infrastructure model means your team owns first-line troubleshooting across every component. Rubrik’s appliance model means vendor support has direct visibility into the platform state. In a major incident, the difference between “open a ticket and wait” and “own the diagnosis” matters — which direction you prefer depends on your team’s capability and your tolerance for vendor dependency.
Operational ceiling. Veeam scales with the engineers who operate it. A strong infrastructure team running a well-hardened Veeam deployment is a formidable recovery architecture. That same deployment under a generalist IT team with competing priorities is an incident waiting to happen. Rubrik’s ceiling is lower in absolute terms but more consistent — the platform is designed to stay manageable regardless of team depth.
Ransomware Reality Check: Immutability by Design vs Immutability by Configuration
Both platforms can protect backup data from ransomware. The architectural question is how that protection is implemented — and what happens when implementation is incomplete. The full recovery system design is covered in the ransomware backup architecture post, but the platform-specific implications are worth addressing directly.
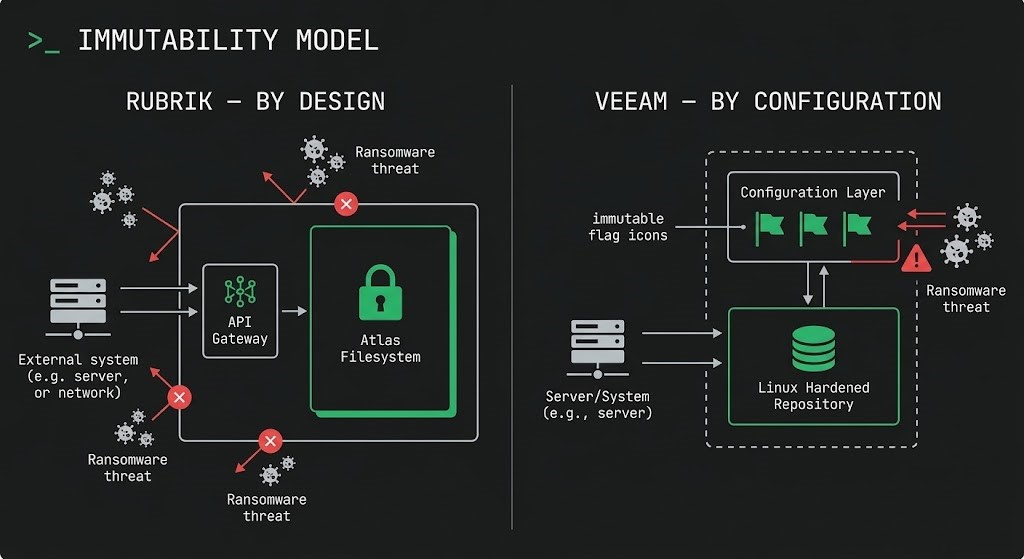
Rubrik’s immutability model. The Atlas filesystem makes backup data non-mountable and non-modifiable by design. There is no path to the data that bypasses the API. Ransomware that successfully reaches the network segment containing a Rubrik appliance still cannot encrypt the backup data — the architecture eliminates the attack vector at the filesystem level, not through configuration policy.
Veeam’s hardened repository model. Veeam’s immutable backup implementation uses Linux hardened repositories with immutable storage flags and single-use credentials. When correctly configured, this is a strong model. The word “correctly” is doing significant work in that sentence. The gap between a standard Veeam deployment and a hardened one requires deliberate steps most organizations haven’t fully completed — and that gap is exactly what ransomware operators target when they specifically hunt backup infrastructure before triggering encryption.
Recovery under adversarial conditions. If your production Active Directory is compromised, Rubrik’s recovery orchestration operates independently — the appliance has its own identity model and doesn’t depend on the production identity plane to execute recovery. Veeam’s recovery capability depends on the Backup Server being intact, accessible, and operating with credentials that haven’t been compromised. In a full-environment compromise, the order of operations matters: you need backup to recover identity, but you need identity to operate backup.
Identity isolation. Neither platform fully solves the problem if your recovery environment shares an identity plane with your production environment. The architectural fix for that is covered in the Rubrik vs Cohesity analysis — the identity isolation requirement applies regardless of which backup platform you operate.
Sovereign and Air-Gapped Environments
In environments where the internet may not exist, identity providers may fail, and vendors strictly cannot phone home — backup becomes something different. It becomes the last surviving control plane. The platform decision in these environments is often made before the feature comparison begins.
Physical air-gap requirements — tape vaulting, offline rotation, manual custody chains — are Veeam’s domain. The architecture assumes humans will move media. Rubrik’s logical isolation model has no equivalent answer for environments where physical separation is a compliance mandate.
Logical air-gap environments — immutable snapshots, role separation, cryptographic lockout — are where Rubrik’s architecture excels. The platform assumes software enforces the separation. In modern sovereign estates that rely on logical isolation rather than physical media movement, Rubrik’s model aligns with the operational model more naturally.
The decision point is simple: if your air-gap requirement is physical, Veeam. If it’s logical, Rubrik. If your audit posture requires full OS-layer inspection of your backup infrastructure, Veeam. If your threat model is primarily ransomware and staffing is limited, Rubrik.
The Decision Framework
This isn’t a feature matrix. It’s a constraint map. Run your environment against these conditions — not a vendor checklist.
- [+] You operate a heterogeneous estate with legacy operating systems, physical servers, or tape infrastructure that requires deep integration
- [+] Physical air-gap compliance requires tape vaulting and manual offline rotation — and your regulatory environment mandates it
- [+] Audit requirements demand full OS-layer visibility and inspectable infrastructure at every tier of the backup stack
- [+] You have a dedicated security engineering staff capable of building, hardening, and maintaining the full Veeam stack — and keeping it hardened under operational load
- [+] Sovereignty means owning the process and infrastructure — not trusting an appliance design you cannot fully inspect
- [+] You operate a modern virtualized or cloud-adjacent estate where logical isolation is the primary protection model
- [+] Ransomware is your primary threat model and you want immutability enforced by architecture rather than configuration policy
- [+] Staffing is limited — the platform needs to stay operationally manageable without deep backup infrastructure expertise on the team
- [+] Recovery speed is a design requirement, not a configuration outcome — and you want that baked into the platform rather than dependent on how well the repository was architected
- [+] Sovereignty means the architecture enforces protection — not the team’s ability to maintain a hardened configuration under pressure
Architect’s Verdict
The Rubrik vs Veeam decision is not about which platform is better. It is about where you want failure to be allowed to exist.
Veeam gives you infrastructure. You own the blast radius, the patch cycle, the hardening posture, and the recovery orchestration. When it is built and maintained correctly, it is one of the most capable and flexible backup architectures available. When it isn’t — and in most environments under sustained operational load, the hardening slips — the infrastructure you built becomes the attack surface.
Rubrik removes that variable. The immutability is architectural, not configured. The recovery capability is baked in, not assembled. The operational surface is smaller. The tradeoff is that authority shifts from your infrastructure to the appliance design — and for some environments, that is an unacceptable audit and inspection gap.
The specific reason to choose Veeam over Rubrik usually looks like one of three things: a physical air-gap mandate that requires tape and offline media rotation, an audit posture that demands full OS-layer visibility across the backup stack, or a legacy ecosystem so deep and heterogeneous that appliance-based integration coverage falls short. If none of those apply, Rubrik’s model will age better in most environments — not because it is technically superior in every dimension, but because immutability by design compounds differently than immutability by configuration.
Build to what your team can actually defend at 2am during a ransomware incident. That is the constraint that matters most.
For the full backup architecture decision space — immutability design, recovery system patterns, and sovereign environment considerations — the Data Protection Architecture pillar maps the complete framework. If you are building or stress-testing your recovery architecture from the ground up, the Data Protection & Resiliency Learning Path is the sequenced reading order.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session