-
-
-
Cloud Native | Amazon AWS | AWS Architecture | Azure Architecture | Business Continuity | Disaster Recovery | Microsoft Azure
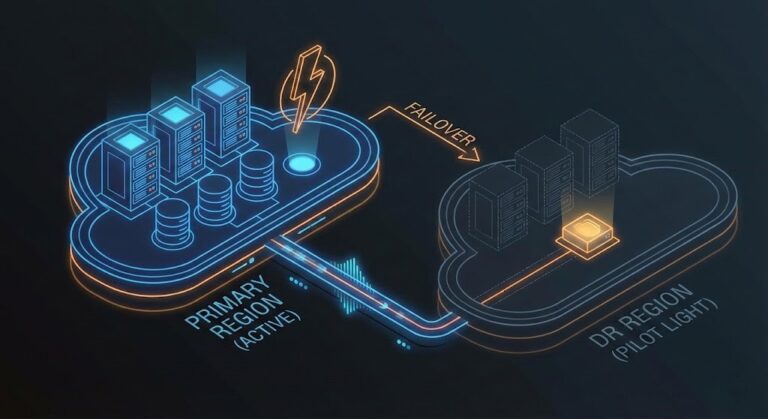
Building a Practical Disaster Recovery Plan for Your First Cloud Project
A cloud disaster recovery plan isn’t a backup strategy — it’s an architectural commitment that determines whether your business survives a region failure or spends 14 hours rebuilding databases by hand. I still remember the first “cloud” Disaster Recovery (DR) plan I reviewed back in 2012. The team assumed that because their app was running…
-
Slicing the Veeam “API Tax”: A 2025 Architect’s Guide to Immutable Object Storage
When you’re designing a Veeam-to-Cloud architecture, the per-GB storage price is the “marketing number.” But for those of us building for Day 2 operations, the number that actually matters is the IOPS-to-Object ratio. I’ve seen too many architects treat S3 like a tape drive, only to be blindsided by a monthly bill where 40% of…
-
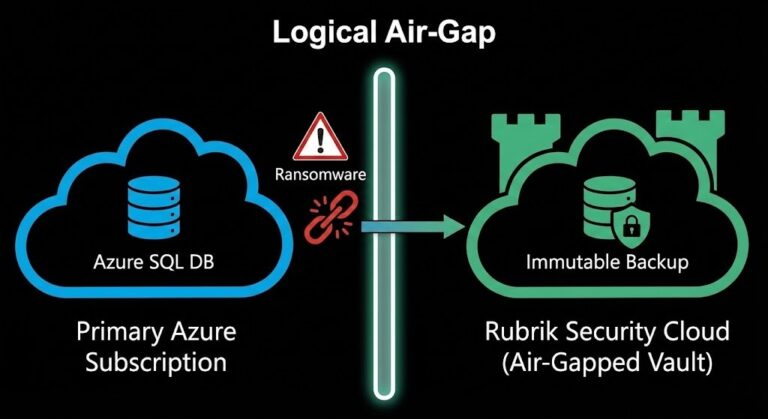
Azure SQL Backup Security: Why Native Protection Has a Gap Rubrik Closes
When you migrate to Azure SQL Managed Instance (MI) or Azure SQL Database, one of the biggest sighs of relief is handing backup management over to Microsoft. Out of the box, Azure provides excellent operational recovery capabilities. You get automatic full, differential, and transaction log backups. You get Point-in-Time Restore (PITR). You get geo-redundancy to…
-
Ransomware-Ready Backup Architecture: The Three-Pillar Engineering Framework
In 2020, the advice was “have good backups.” In 2025, that advice is dangerously incomplete. Today, backup infrastructure is not the remediation; it is the primary target. Modern ransomware cartels know that if they encrypt your production data, you will restore. But if they delete your backups first, you will pay. Attackers now spend weeks…
-
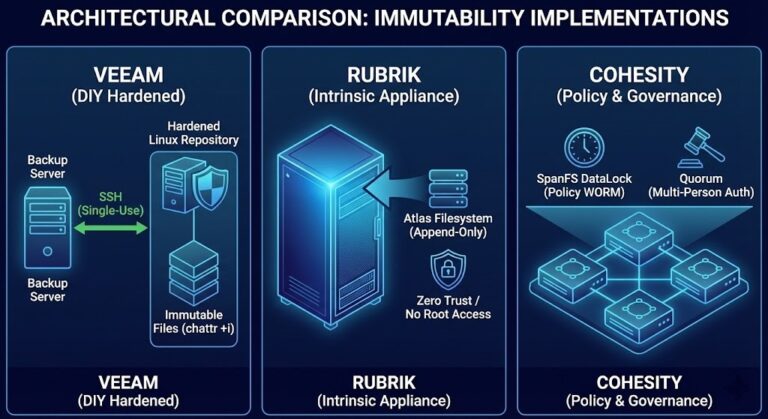
The Indestructible Vault: How Veeam, Rubrik, and Cohesity Architect Immutable Backups
Introduction: The Day Your Backups Betrayed You Modern ransomware doesn’t just target production data. Sophisticated attackers spend weeks reconnoitering your network specifically to locate, compromise, and delete your backups before triggering the encryption event. If your backups are delete-able, they are not backups. They are just delayed victims. The answer is immutable backup architecture —…