Project Phoenix: An Enterprise Field Manual for the Great OpenTofu Migration
The “Sovereignty” ROI
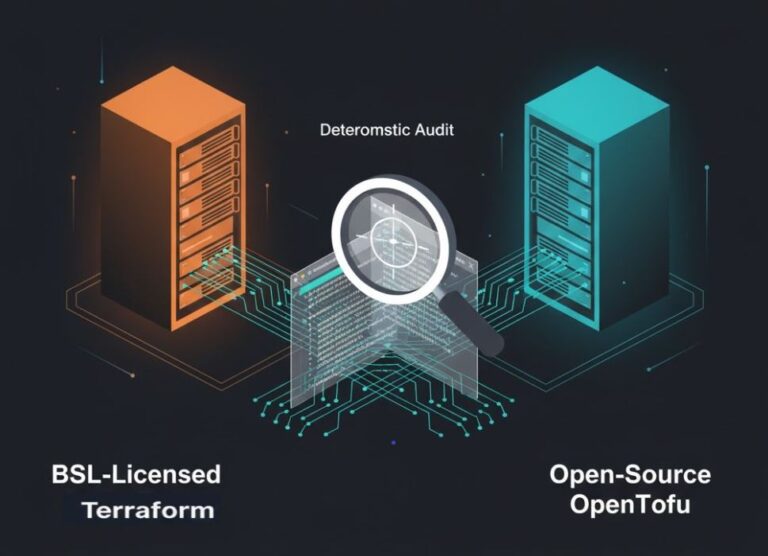
Don’t wait for the March 31, 2026 deadline to find out your infrastructure is locked.. Project Phoenix—our enterprise case study involving 1,200+ managed resources—proved that a move to OpenTofu v1.11 isn’t just about avoiding a $15,000/year “resource tax.” It’s about ensuring your engineering velocity isn’t dictated by a vendor’s licensing shifts. The key to a “boring” (successful) migration isn’t the binary swap; it’s the Deterministic Audit performed before you change your CLI.
The Reality Check: Why We Migrated
We’ve all seen it: a “free” SaaS helper becomes a mission-critical tool, only to have the billing model pivot overnight. For Project Phoenix, staying on the proprietary BSL path meant a mandatory shift to resource-based billing—a five-figure line item for code that previously cost $0 to run.
This is the classic Refactoring Cliff: the point where technical debt and licensing costs collide. But the real risk wasn’t just the bill; it was Version Divergence. Since the fork, features like Terraform 1.10’s Ephemeral Values have drifted from the open-source engine. If you adopt these without a bridge, you aren’t just migrating; you’re refactoring under fire.

Phase 1: The Sovereign Audit (Zero-Trust Protocol)
“I didn’t want my team guessing which modules would break on a Friday afternoon,” says our lead architect. We started with a Zero-Trust Audit using the OpenTofu Readiness Bridge.
The “War Room” Findings:
- Ephemeral Divergence: Project Phoenix relied on TF 1.10’s
ephemeralblocks for secret rotation. - The Landing Zone: The audit confirmed a requirement for OpenTofu v1.11, the native landing zone designed to handle these modern HCL constructs without syntax errors.
Step-by-Step Execution: The Phoenix Protocol
Step A: The Backend Evacuation
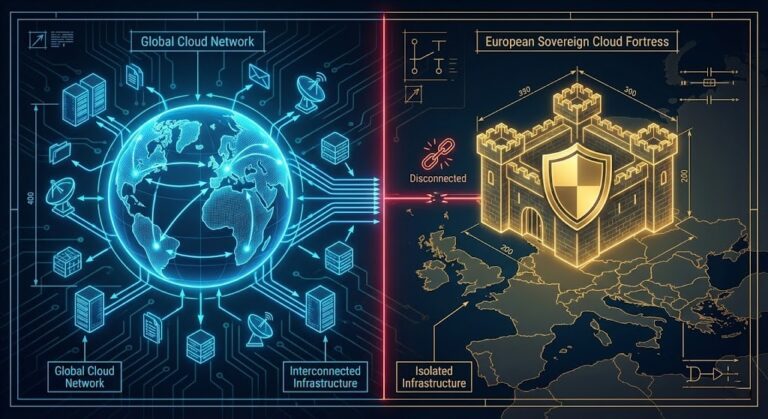
You must move your state file while your legacy “handshake” still works. We moved from HCP SaaS to a private Nutanix Objects S3 bucket to ensure metadata never leaves the data center.
- Prep the Sovereign Storage: Ensure your Nutanix S3 bucket is active.
- Update
backend.tf: Terraformterraform { backend "s3" { bucket = "sovereign-state-phoenix" key = "prod/terraform.tfstate" endpoint = "https://s3.nutanix.local" region = "us-east-1" skip_region_validation = true } } - The Shift: Run
terraform init -migrate-state. Human Tip: Don’t just trust the terminal. Check your S3 bucket manually to verify the.tfstatefile is present before unlinking your old account.

Step B: The Engine Swap
- Clean the Path: Remove the
terraformbinary to prevent version ghosting. - Install OpenTofu v1.11: Bash
curl -s https://get.opentofu.org/install-opentofu.sh | sh tofu --version # Ensure it reports v1.11.x - The New Handshake: Run
tofu init. Because we audited, this should be a “silent” success.
Step C: The Post-Migration Health Check
Once the engine is swapped, we verify the Sovereign Drift to ensure the engine change didn’t trigger unintended resource modifications.
Copy-Paste Verification Script:
Bash
if [ $? -eq 0 ]; then
echo "✅ Success: Sovereign State is Clean."
else
echo "⚠️ Warning: Drift detected. Audit HCL blocks immediately."
fiTroubleshooting the Real-World “Breakers”
| The Headache | The Root Cause | The Human Fix |
| Registry 403 Forbidden | Hard-coded registry.terraform.io paths. | Use a tofu provider alias to redirect to the OpenTofu registry. |
| State Lock Stale | HCP SaaS didn’t release the lock. | Use tofu force-unlock <LOCK_ID>. Reclaim your data ownership. |
| Ephemeral Errors | Syntax mismatch between TF and Tofu 1.10. | Ensure you are on Tofu v1.11—the version built for this specific landing. |
Architect’s Final Verdict
Infrastructure is only as “sovereign” as the license it runs on. Project Phoenix wasn’t just a technical win; it was a business victory that secured the environment against the March 31, 2026 cutoff.
Your Next Move: Don’t guess your migration path. Use the OpenTofu Readiness Bridge today and see where your “Integrity Gap” really lies.
Additional Resources:
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session