Vendor Lock-In Happens Through Networking — Not APIs

Part 3 of the Rack2Cloud’s Cloud Fragility Series
The Great API Distraction
For the past fifteen years, we obsessed over the wrong kind of cloud vendor lock-in. Everyone worried: “If I use DynamoDB or Azure Functions, am I trapping my code forever?”
So, we poured billions of hours and dollars into building abstraction layers, adopting Kubernetes, and patching together generic Terraform providers—all just to keep our compute “portable.”
We pretty much won that battle. Now, containers run anywhere you want. Moving code isn’t that hard.
But while we were busy making our compute portable, the cloud giants were quietly making our data immovable.
These days, real vendor lock-in isn’t about APIs at all. It comes down to physics and money—the mass of your data and the toll roads built to keep it parked right where it is.
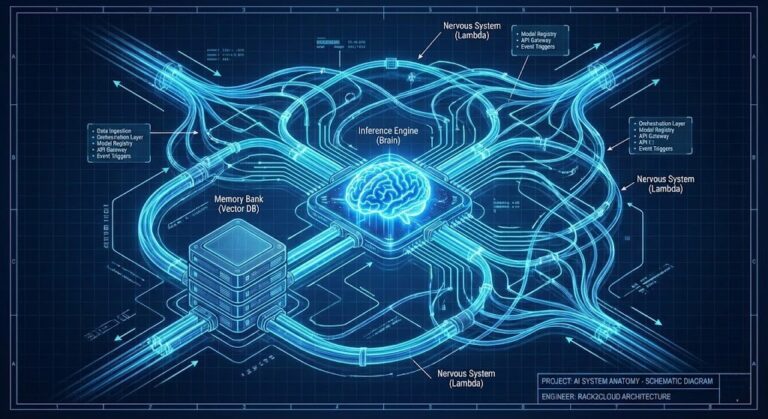
The Physics of Cloud Vendor Lock-In: Data Gravity
“Data Gravity” sounds like theory, but it’s painfully real. The more data you pile up, the harder it gets to move. Apps and services stick to it, like satellites caught in orbit.
In the AI era, data gravity isn’t just a force—it’s a black hole.
If you’ve got petabytes of training data or years of transaction logs in AWS S3, moving that mountain to Google Cloud isn’t just a “migration project.” It’s a physics problem.
Transferring that much data over the internet? It takes forever. And trying to keep live databases in sync across providers—good luck. The operational risks are huge.
Cloud providers know this. They built their pricing to make gravity work for them.
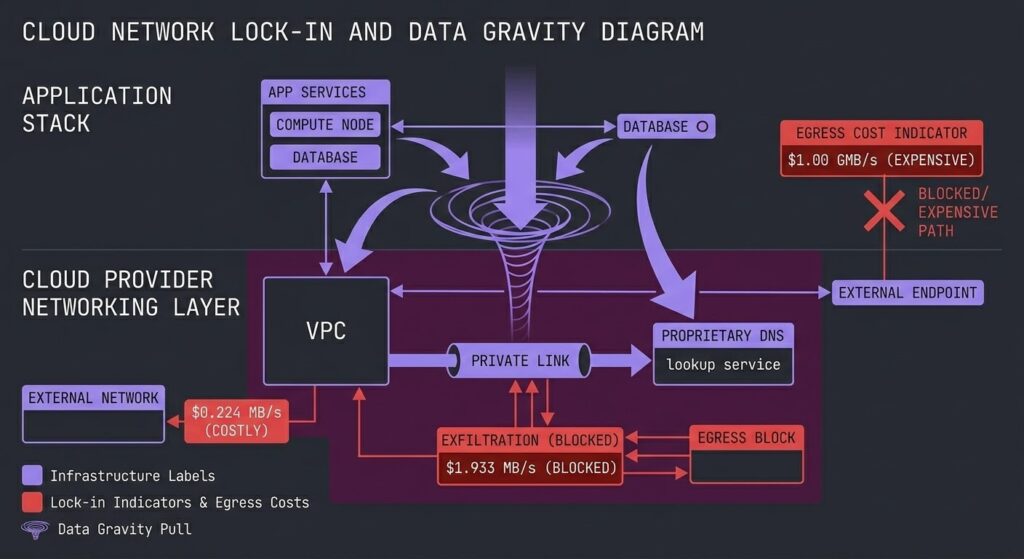
The Egress Fee Trap (The Roach Motel Model)
Here’s the trap: Egress fees.
Cloud networking pricing works like a roach motel. Data checks in for free, but you’ll pay through the nose to get it out. Ingress? Free. They’ll run gold-plated fiber to your door to get your data onto their platform.
But try pulling 5 petabytes out of AWS us-east-1 to move it somewhere else, and suddenly you’re looking at a six-figure exit tax.
This changes how people architect systems. Instead of designing for the best tech, architects design to dodge the exit tax. You keep your data in AWS not because it’s the best place for it, but because you can’t afford the ransom to move.
When it costs $200,000 just to get your data out the door, you’re not a customer. You’re a hostage.
The “Private Networking” Handcuffs
Egress fees are the blunt tool. The sneakier, more effective lock-in comes through proprietary networking.
Services like AWS PrivateLink, Azure Private Endpoints, and Google Private Service Connect are pitched as security features. And they are—no argument there. They keep traffic off the public internet.
But they’re also dangerously sticky architectural glue.
Once you wire up your entire microservices jungle using PrivateLink endpoints, you’re stuck. Tearing that out is way harder than refactoring code. You haven’t just used their VMs—you’ve baked their proprietary networking into your app’s DNA.
Moving to another cloud means rewiring your entire nervous system.
The Brutal Reality of “Multi-Cloud Networking”
A lot of companies try multi-cloud to avoid these traps, only to end up with twice the complexity and double the cost.
Connecting AWS to Azure isn’t simple. It means expensive middlemen services, VPN tunnels with spotty performance, or dedicated fiber that takes months to set up. And if you try using the public internet for this? That’s a resilience nightmare (see our guide on Why the Public Internet is Not an SLA).
So what happens? Most “multi-cloud” setups turn into isolated islands of data that rarely talk, because the toll to connect them is just too high.
Architecting for Data Freedom
If you want real leverage over your cloud provider, you have to design for data mobility from day one—and yes, it costs more upfront.
- Acknowledge the Exit Tax: Always factor egress fees into your TCO. If a solution looks cheap but has hidden egress risks, it’s not actually cheap.
- Neutral Territory Data: For your most critical datasets, think about housing them in carrier-neutral facilities (like Equinix) on your own hardware, and connecting to clouds with dedicated, low-latency links. You own the data gravity. The clouds just rent access.
- Avoid Proprietary Plumbing When You Can: Be careful with deep networking integrations like PrivateLink. Always ask yourself, “If I had to move this to another provider tomorrow, how long would it actually take?”
Series Context
- Part 1 covered how shared dependencies cause cascading failures.
- Part 2 explained how Identity is the single control plane that can lock you out.
- Part 3 (Current) shows how Networking is the financial and physical barrier to leaving.
- Part 4 will tie this all together, explaining how these architectural traps led directly to the massive cloud bill increases seen in 2026.
The pattern is clear: The code is portable. The data is anchored.
The Architecture of Real Portability
True cloud vendor lock-in isn’t reversible with a refactor. It is reversible with architecture — but only if the architecture was designed for mobility before the data accumulated. After petabyte scale, the physics make the decision for you.
The three decisions that determine your actual exit options: where your data lives at rest, which networking primitives your services depend on, and whether your egress costs were modeled as a design constraint or discovered as a billing surprise. Teams that treat these as operational details rather than architectural decisions find out their real lock-in exposure when they try to negotiate a contract renewal.
The data gravity analysis post covers the full mechanics of how compute follows data — and why the multi-cloud portability argument falls apart at the storage layer. The physics of data egress post covers the specific cost mathematics that make large-scale data movement financially prohibitive. Read both before any architecture decision that places significant data in a single provider’s storage fabric.
Architect’s Verdict
The API portability argument won. Containers run anywhere. Kubernetes abstracts the compute layer. The infrastructure-as-code community built excellent tooling for multi-cloud compute. None of it matters if your data can’t follow.
Cloud vendor lock-in in 2026 is a storage and networking problem, not a compute problem. The providers understood this before most architects did — which is why ingress is free and egress is expensive, why PrivateLink integrations are marketed as security features, and why managed database services are priced to make self-managed alternatives look painful. Every one of these decisions is rational from the provider’s perspective and creates dependency from yours.
The counter-architecture is not exotic. Neutral-territory data for critical datasets. Explicit egress cost modeling in every TCO calculation. Careful evaluation of proprietary networking integrations before they become load-bearing. These are not multi-cloud idealism — they are leverage preservation. You don’t need to be multi-cloud to benefit from designing as if you could be.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session