Your Ransomware Plan Is Fiction: 5 Recovery Metrics Nutanix, Cohesity, Rubrik & Pure Can’t Hide

Ransomware recovery metrics are the only thing standing between your recovery plan and a PowerPoint. Every vendor demo shows a single VM booting in 60 seconds. Every real ransomware recovery looks like this: the backups are intact, the ransomware is neutralized, the executives are on the bridge — and nothing is coming back online.
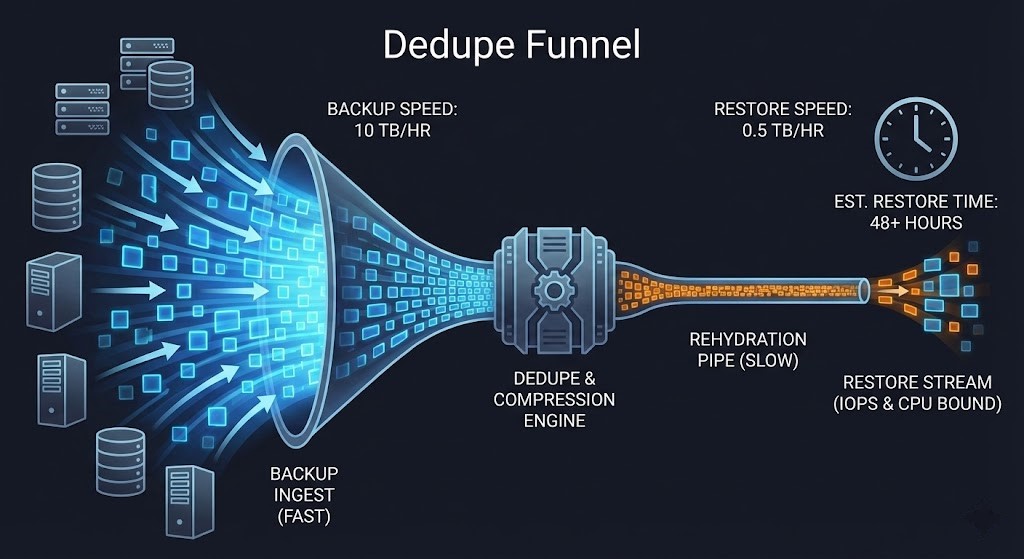
Recovery is not a software problem — it’s a physics problem. It is a war against bandwidth, IOPS, and identity limits. I audited a financial services firm after a major breach where their immutable backups were pristine. Yet recovery still took 72 hours. Rehydrating 50TB of deduplicated data back to primary storage took 18 hours. When they finally “Live Mounted” the VMs directly on the backup appliance, the SQL server crashed because the backup controllers couldn’t sustain 25% of production IOPS.
If you cannot measure the following five ransomware recovery metrics today, you do not have a plan. You have hopeware. The full anatomy of that 72-hour failure is in The 72-Hour Restore: Why “Instant VM Recovery” Failed in Production.
Ransomware Recovery Metrics #1: The Immutability Trap
The Trap: “We have immutable snapshots.” Immutability protects data. Ransomware attacks identities.
The Physics Reality: If the same admin account ([email protected]) can manage the hypervisor, the backup system, and the storage array, immutability is just a speed bump. The identity isolation architecture that closes this gap is in Immutability Is Not a Strategy: Engineering Recovery Silos for Ransomware Survival.
The Metric:
Immutability Reality Ratio (IIR) = (Capacity on Air-Gapped/Zero-Trust Storage) ÷ (Total Backup Capacity)
- Target: >75%
- Failure State: <50% = Single-credential compromise destroys everything.
| Vendor | Immutability Claim | Physics Reality |
|---|---|---|
| Nutanix | Data Lens Object Locking | NUS snapshots are vulnerable unless explicitly air-gapped from the Prism Identity Provider. |
| Cohesity | FortKnox “Virtual Air Gap” | Strongest separation via Quorum/MFA vaulting (reduces identity convergence). |
| Rubrik | Immutable Cyber Vaults | Robust proprietary filesystem, but “Blast Radius” depends on tenant isolation discipline. |
| Pure | SafeMode Admin-Proof | Array-level retention is strong, but governance still depends on who holds the keys. |
Ransomware Recovery Metrics #2: The Hydration Trap
The Trap: “Instant Restore” (or Live Mount). Vendors confuse Access (mounting a view) with Hydration (moving data back to primary storage). “Instant Access” is a temporary suspension of failure, not recovery.
The Physics Reality: Backup storage is optimized for write-once, not read-heavy production. The real bottleneck is breaking the 10:1 dedupe ratio to write raw blocks back to primary NVMe. The deduplication mechanics behind this failure are covered in The Backup Rehydration Bottleneck: Why Your Deduplication Engine Is Killing Your RTO.
The Metric:
Rehydration Velocity (HV) = (Total Dataset Size) ÷ (Hours to Move Data to Primary Storage)
- Target: >10 TB/Hour for critical stacks.
- Failure State: <5 TB/Hour = Multi-day outage at scale.
- Physics Check: Use the Universal Cloud Restore Calculator to model your egress bandwidth if you rely on cloud tiers.
| Vendor | Hydration Claim | Measured Reality |
| Nutanix | AHV “1-Click Restore” | Limited by CVM bandwidth and backend target throughput. |
| Cohesity | “Instant Mass Restore” | Excellent for access, but background hydration speed is the real RTO driver. |
| Rubrik | Parallel Recovery | Live Mount is fast, but full rehydration back to primary determines outage length. |
| Pure | SafeMode Native | Winner: No rehydration. Restores are pointer operations limited only by array headroom. |
Ransomware Recovery Metrics #3: The Forensic Drag Trap
The Trap: “Recover in 30 Minutes.” No, you can’t. Because legal won’t let you.
The Physics Reality: You cannot restore into production until Forensics completes analysis and Cyber Insurance approves restoration. This creates Forensic Drag. The only path forward is a Clean Room (Zero-Trust Recovery Zone). This is the same 48-hour legal hold pattern documented in The 72-Hour Restore and the clean room architecture in Engineering Recovery Silos for Ransomware Survival.
The Metric:
Clean Room RTO = Time from “Incident Declared” to “Isolated Environment Online & Scanned”
- Target: <12 Hours.
- Failure State: >24 Hours = Lawyers, not engineers, control your uptime.
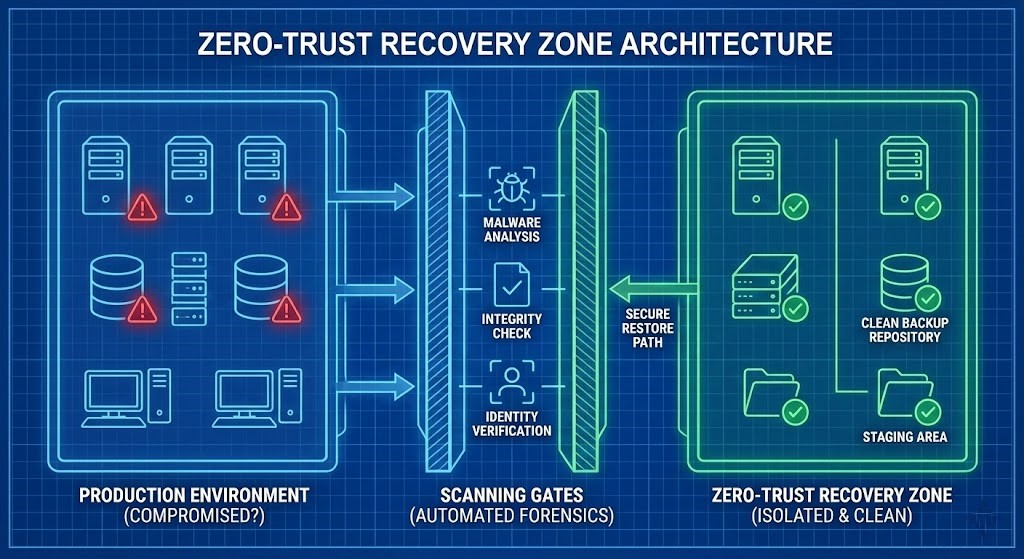
| Vendor | Clean Room Strategy | Reality |
| Nutanix | Isolated AHV Projects | Requires pre-provisioned standby cluster/project with NO routing to production. |
| Cohesity | FortKnox VLAN Recovery | Supports isolated restore environments with embedded threat scanning. |
| Rubrik | Cyber Recovery Vault | Offers orchestrated clean recovery workflows, but only if pre-staged. |
| Pure | Snapshot Clones | Clones are instant, but compute capacity must already exist manually. |
Ransomware Recovery Metrics #4: The IOPS Trap
The Trap: “Booted” = “Recovered.” Booting ≠ Functioning. SQL doesn’t care if the OS boots — it cares about sustained IOPS under load.
The Physics Reality: During recovery, your storage stack fights a two-front war:
- Ingest: Writing restored data (Rehydration).
- Serve: Handling production I/O from recovered apps. Most backup appliances collapse under this dual load.
The Metric:
Recovery IOPS Ratio = (Available IOPS During Hydration) ÷ (Baseline Production IOPS)
- Target: >70% of Production Performance.
- Failure State: <50% = Timeouts, retries, and cascading outages.
Architecture Check:
- Nutanix: Ensure CVMs have headroom for replication + VM I/O simultaneously.
- Cohesity/Rubrik: Ensure “Live Mount” traffic doesn’t starve the production path. Running Prod on a backup appliance usually kills IOPS.
- Pure: Ensure controller utilization isn’t redlined during snapshot clone + production I/O.
Architect’s Verdict: Vendor Physics Scorecard
No vendor wins all five categories. You must architect around their physics gaps.
| Metric | Nutanix | Cohesity | Rubrik | Pure |
| 1. IIR (Immutability) | Object Lock (Identity Risk) | Virtual Air Gap (Strong) | Immutable Vault (Strong) | Array-Level (Strong) |
| 2. HV (Velocity) | CVM-Bound | 10TB+/hr (Measured) | Parallel/Scale | Native (Instant) |
| 3. Clean Room | AHV Projects | VLAN/Cloud | Cyber Vault | Manual Hosts |
| 4. IOPS Ratio | Shared Resource | Low (Target Limits) | Low (Target Limits) | High (FlashArray) |
| 5. Validation | Manual | Automated | Orchestrated | Manual |
Before You Buy: The 5 Physics Tests
If you can’t answer these five ransomware recovery metrics questions, the plan is fiction:
- IIR >75%? (Show me the air-gapped capacity numbers).
- HV >10TB/hr? (Time a 50TB restore, not a 100GB VM).
- Clean Room <12hr? (Is it pre-provisioned or vaporware?).
- IOPS >70%? (Load test SQL during hydration).
- 2x/Year Tests? (Is the calendar blocked?).
If you cannot produce these five numbers today — in hours, not days — you do not have a ransomware recovery plan. You have a PowerPoint. The RTO methodology that underpins this framework is in RTO Reality: Why Your Backups Mean Nothing Without a Recovery Drill.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session