The Indestructible Vault: How Veeam, Rubrik, and Cohesity Architect Immutable Backups
Introduction: The Day Your Backups Betrayed You
Modern ransomware doesn’t just target production data. Sophisticated attackers spend weeks reconnoitering your network specifically to locate, compromise, and delete your backups before triggering the encryption event.
If your backups are delete-able, they are not backups. They are just delayed victims.
The answer is immutable backup architecture — and it is not a marketing buzzword. It is a fundamental architectural shift required to survive the current threat landscape. In this deep dive, we move past the sales brochures to examine how the three market leaders — Veeam, Rubrik, and Cohesity — actually implement immutability at the storage layer, and why the architectural differences between them matter more than the marketing claims.
For environments with sovereign, air-gapped, or regulatory constraints, see the companion guide: Rubrik vs Veeam in the Sovereign Estate — which covers the control-plane survivability angle in depth.
The 101: What is True Immutability?
Before comparing vendors, we must define the standard. In the context of data protection, immutability means that once data is written to the backup target, it cannot be modified, deleted, or encrypted for a specified retention period.
Crucially, this “cannot” must apply to everyone:
- It cannot be deleted by the backup software itself
- It cannot be deleted by a compromised Domain Administrator account
- It cannot be deleted by root access to the storage subsystem
True immutability creates a Write-Once-Read-Many (WORM) state. It transforms your backup repository from a readable/writable storage volume into a sealed digital vault. This is the foundation of any resilient Data Protection Architecture.
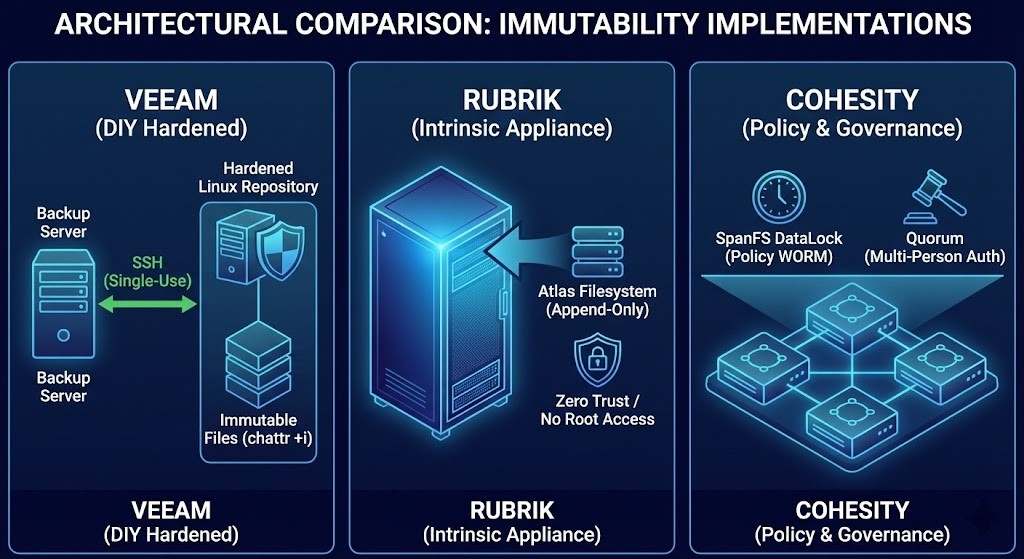
Veeam: The “DIY Hardened” Approach
Veeam’s philosophy has always been software-defined flexibility — letting you choose your own hardware. Their modern answer to native immutability is the Hardened Linux Repository (HLR).
The Mechanism: Hardened Linux Repository & Object Lock
Veeam’s primary on-prem method doesn’t rely on a proprietary file system. Instead, it cleverly leverages standard Linux operating system capabilities.
- The Setup: Deploy a standard Linux server (Ubuntu/RHEL) with local storage
- The Magic: Veeam leverages the Linux
chattr +icommand. When Veeam writes a backup file chain (VBK/VIB files), the transport service immediately sets the immutable flag based on your retention policy - The Security: Veeam uses single-use credentials to connect to the repository. Once deployed, SSH is not required and credentials are not stored. Even root access cannot delete files until the flag expires — without rebooting into single-user mode, which requires physical console access
For cloud targets, Veeam heavily utilizes S3 Object Lock API calls to ensure immutability on AWS S3, Azure Blob, and compatible object storage providers.
Pros: Highly flexible, cost-effective, uses existing hardware and standard Linux capabilities.
Cons: Some assembly required. You own OS security, patching, and physical security. The security boundary is the OS kernel.
Rubrik: The Intrinsic Appliance Approach
Rubrik entered the market with a fundamental goal: simplify backup by collapsing the traditional multi-tier architecture into a single hyperconverged appliance. Their approach to immutability is inherent to how their file system is built — not a feature you enable.
The Mechanism: The Atlas File System
- No Standard Protocols: Rubrik appliances do not expose backup storage via SMB or NFS. You cannot map a drive to the backup volume
- Append-Only Model: The Atlas file system is fundamentally append-only. When data is ingested, it is written, fingerprinted, and locked. The file system has no mechanisms to modify existing committed blocks
- Zero Trust Boundary: There is no root SSH access available to end-users or attackers that would allow access to underlying storage volumes. Data is only accessible via Rubrik API authenticated through their RBAC system
Pros: Extreme simplicity and high security by design. Immutability is on by default and cannot be turned off.
Cons: Requires the appliance model (hardware or virtual), higher initial CAPEX. Vendor ecosystem dependency.
Cohesity: The Policy & Governance Approach
Cohesity’s immutable backup architecture is built on their SpanFS distributed file system. Their immutability approach — branded DataLock — balances appliance-like security with rich policy governance designed to prevent insider threats.
The Mechanism: DataLock and Quorum
- Policy-Based Locking: DataLock policies applied to Storage Domains or Protection Groups start the WORM timer on ingestion
- Time-Drift Protection: Cohesity uses an internal monotonic clock resistant to external NTP manipulation — closing a common attack vector against time-based WORM systems
- Multi-Person Authorization (Quorum): Disabling DataLock, changing retention policies, or deleting a protected storage view requires approval from two or more designated security officers. This directly addresses the rogue administrator threat model
Pros: Excellent balance of platform security and granular control. Quorum is a significant differentiator for enterprises concerned about insider threats.
Cons: Platform commitment required. Governance structures need careful planning to avoid operational friction.
For the full architectural comparison of how Rubrik and Cohesity scale under production conditions, see Rubrik vs Cohesity: Which Backup Architecture Actually Scales?
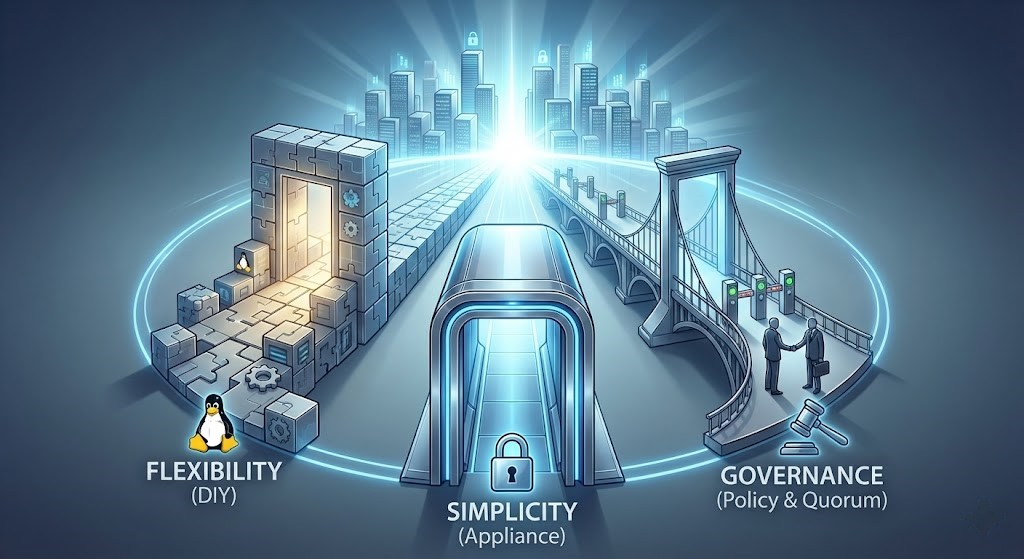
Immutable Backup Architecture: The Architect’s Cheat Sheet
Here is a visual breakdown of the core differences in how these three industry leaders implement immutable backups.
| Feature | Veeam | Rubrik | Cohesity |
| Primary Implementation | Hardened Linux Repository (Software on BYO Hardware) | Atlas File System (Intrinsic to Appliance) | SpanFS DataLock (Policy on Platform) |
| Immutability Type | OS-Level Attributes (chattr) | Filesystem Design (Append-only) | Software Policy WORM |
| Hardware Dependency | Low (Any x86 Server) | High (Appliance/Certified Node) | High (Appliance/Certified Node) |
| Key Strength | Flexibility & Cost to implement | Simplicity & Security by design | Policy Governance & Insider Threat Protection (Quorum) |
| Ideal For | Teams who want control over hardware and love Linux. | Teams wanting a “set it and forget it” secure black box. | Enterprises needing strict governance and multi-person auth. |
Conclusion: It’s Not If, But How
In today’s threat landscape, debating whether you need immutable backups is like debating whether your car needs brakes. It is not an optional feature — it is a mandatory requirement for operational survival.
The choice between Veeam, Rubrik, and Cohesity doesn’t come down to one being ‘better’ at immutable backup architecture. They all effectively stop ransomware from deleting your data. The choice comes down to architectural philosophy:
- Do you want the flexibility to build your own hardened bunkers with Veeam?
- Do you want the simplicity of Rubrik’s intrinsic, black-box approach?
- Do you need the governance and quorum controls offered by Cohesity?
For teams operating in sovereign, regulated, or air-gapped environments, the decision goes deeper — see Rubrik vs Veeam in the Sovereign Estate for the control-plane survivability comparison.
Evaluate your team’s skillset, your budget, and your risk tolerance — and lock your data down before the ransom note appears.
Continue the Path
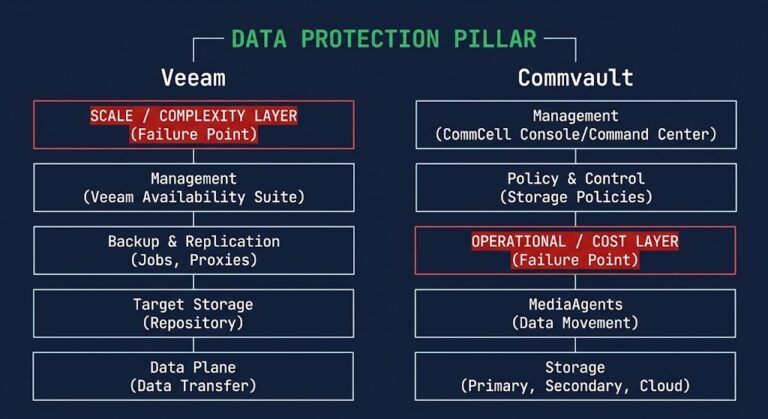
Immutability is only one layer of a sovereign disaster recovery strategy. To master the physics of enterprise resiliency, explore the full Data Protection & Resiliency Learning Path and the Data Protection Architecture Strategy Guide.
To model your exact cloud egress costs during a large-scale recovery event, use the Cloud Restore Calculator.
Additional Resources
For deeper technical context on the concepts covered in this guide:
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session