Azure Private Endpoint DNS Issues: Fix Recursive Loops and Prevent Subnet Exhaustion Before 2026
On March 31, 2026, Azure retires default outbound access. Thousands of organizations are deploying Private Endpoints in response—and many are discovering their DNS architecture was never designed for Private Link.
If you are seeing intermittent 404s, “Address already in use” errors, or DNS resolution that works in the portal but fails in the shell, you have fallen into the Private Endpoint trap.
Failure Signals: Signs You’re in a Recursive DNS Loop
Before the outage becomes permanent, look for these early warning signs:
- Intermittent 404s on private endpoints during high-load periods.
- Name resolves in Azure Portal (which uses a different path) but fails via
nslookupon-premises. - High DNS query latency (> 200ms) as packets bounce between resolvers.
- Random timeouts during blob storage or Key Vault access.
- Success from an Azure VM but consistent failure from your on-premises workstations.
The Mechanism: Why DNS Loops Occur
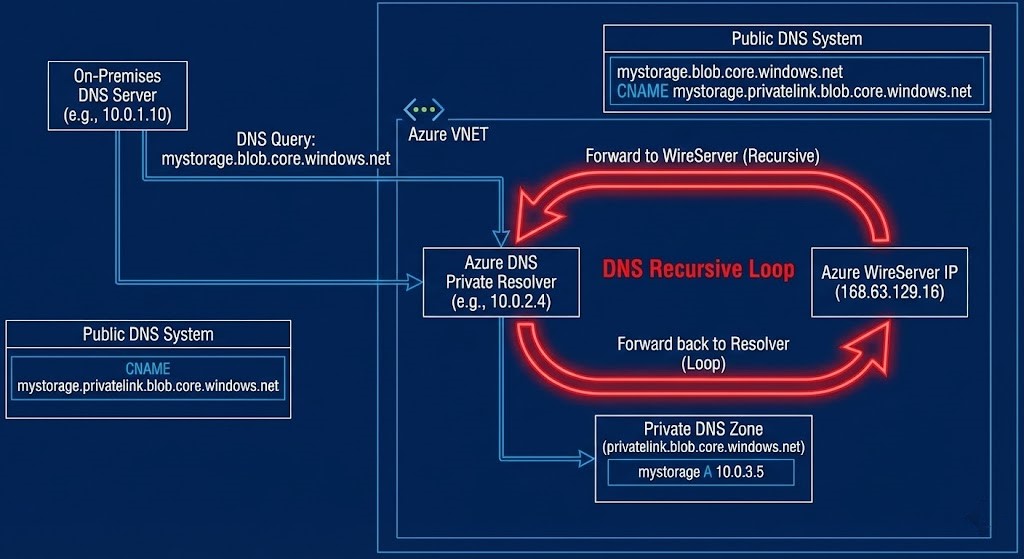
Azure doesn’t “send packets back” in a traditional sense. The loop is a logic failure in your forwarding chain:
- On-prem DNS receives a request for
mystorage.blob.core.windows.netand forwards the broadblob.core.windows.netzone to Azure. - Azure Private DNS Zone only contains the
privatelink.blob.core.windows.netrecord. - The Azure Resolver (or your proxy) attempts public resolution for the original FQDN.
- The Request Bounces: Because of broad forwarders, that request is sent back to your on-premises environment.
- Recursion Depth: The query bounces between resolvers until a timeout is reached.
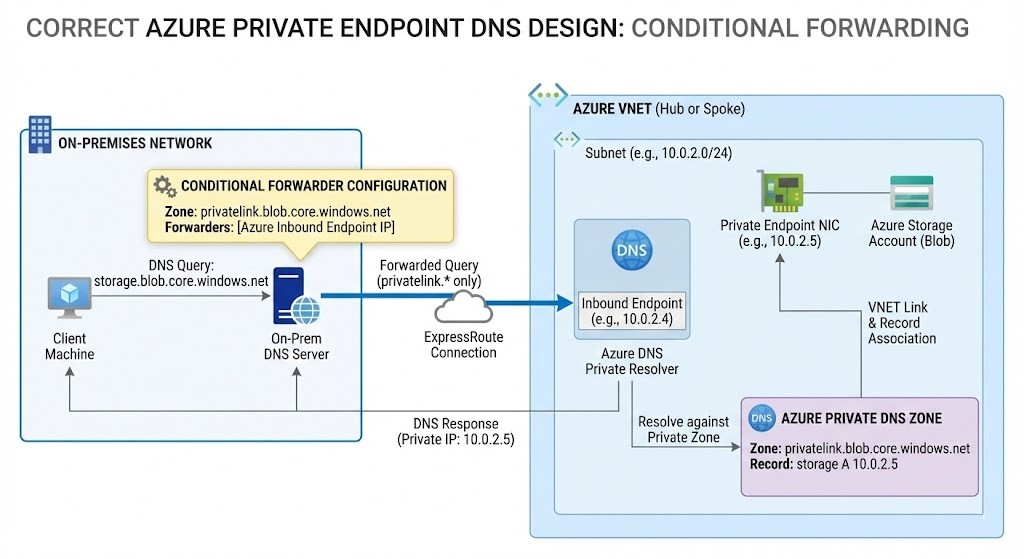
The Technical Fix: Deterministic Forwarding
To break the loop, you must treat the Azure WireServer IP (168.63.129.16) as a non-routable platform service.
- It is not reachable over VPN or ExpressRoute: You cannot query this IP directly from your data center.
- Deploy Azure DNS Private Resolver: This fully managed service replaces your legacy DNS forwarder VMs, eliminating the management overhead of HA and patching.
- Surgical Suffix Forwarding: Configure your on-premises DNS to forward only the
privatelinksuffixes (e.g.,privatelink.database.windows.net) to your Azure resolver inbound endpoint.
>_ Deep Dive Spoke: Where does the Azure DNS Private Resolver actually live? To prevent deploying fragmented resolvers everywhere, centralize your DNS routing. Read our architectural guide on Azure Landing Zone Refactors: The Hub-and-Spoke Reality Check.
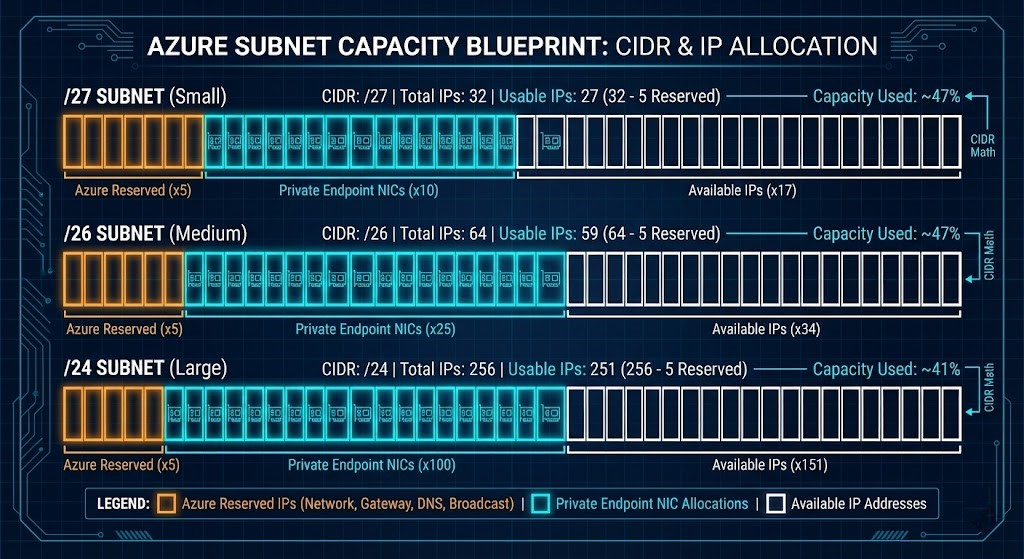
The “Silent Killer”: Subnet Exhaustion
Private Endpoints are NIC-backed resources that consume IP addresses even if the underlying service is unused. In 2026, architects must perform “Subnet Math” before every deployment:
- Fixed Allocation: Private Endpoints cannot share IPs and cannot be moved between subnets after creation.
- Azure Reservations: Azure always reserves the first four and the last IP in every subnet (5 IPs total).
| CIDR | Total IPs | Usable IPs | Safe PE Capacity (80%) |
|---|---|---|---|
| /27 | 32 | 27 | ~20 PEs |
| /26 | 64 | 59 | ~45 PEs |
| /24 | 256 | 251 | ~200 PEs |
>_ Deep Dive Spoke: Private Endpoints are the foundation of strict, zero-trust network boundaries. Learn how to architect impenetrable workload isolation in our piece: Azure Governance Needs More Unix: The “BSD Jail” Pattern for Landing Zones.
Engineering Workbench Integration
Validate Your Azure Private Endpoint Architecture Before 2026
Before deploying another Private Endpoint, validate your DNS chain and subnet headroom, run our stateless auditor:
>_ Launch Tool: Azure PE Checker
Detect recursive DNS loops, validate suffix forwarding, and calculate safe IP capacity instantly. Our tool validates your Private Link DNS logic and IP headroom against Azure’s 2026 networking standards.
Environments Most Likely to Break
- Hybrid environments using legacy Windows DNS forwarders
- Broad conditional forwarders for *.core.windows.net
- High-density microservice deployments (>50 PEs)
- ExpressRoute environments without DNS Private Resolver. (To understand the routing physics behind this, review our Networking Architecture Path).
Additional Resources & Official Documentation
To validate architectural decisions against official platform behavior, review the following Microsoft references:
- Azure Private Link & DNS Integration – Azure Private Endpoint DNS Integration Scenarios
- Azure Private Endpoint Overview – What is a private endpoint? – Azure Private Link
- Azure DNS Private Resolver (Overview)
- Azure DNS Private Resolver (Architectural Guidance) – Azure DNS Private Resolver – Architecture Center
- Azure DNS Private Resolver Endpoints & Rulesets – Azure DNS Private Resolver endpoints and rulesets
- Azure Default Outbound Access Retirement – How to identify Azure resources using default outbound Internet access?
Architecture takeaway: Private Link is not just a connectivity feature — it is a DNS control-plane change. Misunderstanding that boundary is what causes recursive loops and silent subnet collapse.
PRIVATE ENDPOINT ARCHITECTURE REVIEW
We perform deterministic DNS and subnet capacity audits for Azure environments preparing for the 2026 outbound access retirement. Stop the recursive loops before they take down production.
BOOK AN ARCHITECTURE REVIEWEditorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
This architectural deep-dive contains affiliate links to hardware and software tools validated in our lab. If you make a purchase through these links, we may earn a commission at no additional cost to you. This support allows us to maintain our independent testing environment and continue producing ad-free strategic research. See our Full Policy.






