Azure Governance Needs More Unix: The “BSD Jail” Pattern for Landing Zones
Stop “archi-splaining” governance to your engineers.
Modern Azure landing zone governance has mutated into a bloated bureaucratic layer that tries to micro-manage every resource through 400-page PDF frameworks. Somewhere along the way, we forgot the lesson Unix taught us forty years ago: Freedom within boundaries.
A recent fintech client had 14 subscriptions, nearly 400 Azure Policy definitions, and a governance board that met weekly to approve exceptions. Despite all that “control,” they suffered three lateral movement incidents in a single quarter — simply because no one could clearly answer one question: Who actually owns what?
This wasn’t a tooling failure. It was a governance failure. Azure governance patterns built on approval bureaucracy don’t prevent incidents — they just slow everything else down while the real attack surface goes unmanaged.
We need to stop treating Azure subscriptions like billing buckets and start treating them like BSD Jails.
The Failure of the “Nanny Cloud”
The standard “Enterprise Scale” model — where Central IT approves every NSG rule, route table, and resource creation — is fundamentally broken. It tries to solve technical problems with human processes.
That centralization creates three predictable failure modes:
- Approval Bottlenecks: Change velocity collapses as tickets pile up in the “Cloud Approval” queue.
- Permission Drift: Emergency exceptions get granted to bypass the bottleneck — and then never revoked.
- Shadow Infrastructure: Frustrated teams spin up Pay-As-You-Go subscriptions outside the platform just to get work done.
Each of these increases either your breach probability or your mean time to recovery — often both. This is how you end up with the worst of all worlds: slow delivery, weak security, and zero accountability.
For a direct comparison of how Azure Landing Zone governance stacks up against AWS Control Tower’s model, see Azure Landing Zone vs. AWS Control Tower: The Architect’s Deep Dive.
The Architecture: Subscription as a BSD Jail
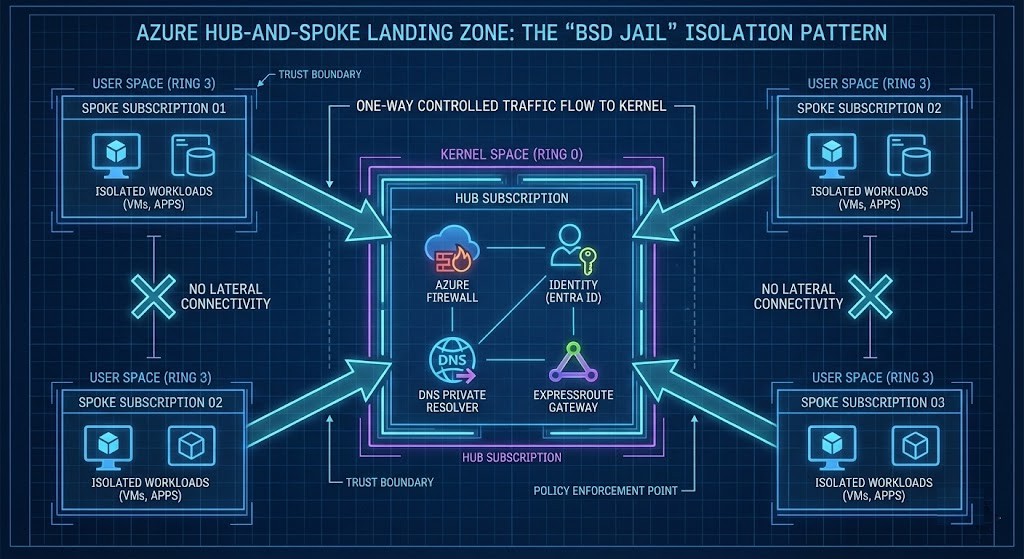
In Unix, a BSD Jail limits the scope of root. Unlike a simple chroot, it isolates users, processes, and networking. You can destroy your own environment — but you can’t touch the kernel or other jails.
In Azure, we apply the same logic. The Subscription is the Jail.
- Kernel Space (Hub): Managed by Platform Engineering. Contains the firewall, identity infrastructure, ExpressRoute, DNS, and routing controls. Immutable to workload teams.
- User Space (Spoke): Managed by the workload team. They have freedom within boundaries to deploy what they need — as long as they cannot route out of their jail or modify the kernel.
The explicit threat model. This Azure landing zone governance pattern is explicitly designed to prevent:
- Lateral Movement: An identity compromised in Spoke A has zero permissions in Spoke B.
- Privilege Escalation: Even Contributors cannot modify peering, UDRs, or control-plane routes.
- Subscription Breakout: Hard quotas and deny policies prevent accidental blast radius expansion.
The goal isn’t to prevent mistakes. The goal is to make mistakes survivable.
Case study: The CI/CD wipe. A SaaS provider using standard CAF Enterprise Scale suffered a breach when a compromised CI/CD identity escalated to Subscription Owner and wiped three environments. Under the BSD Jail Pattern, that identity would have been trapped inside a single Resource Group — turning a catastrophic business event into a minor incident ticket. Recovery would have taken minutes, not weeks.
For hub-and-spoke refactoring patterns specifically, see Azure Landing Zone Refactors: The Hub-and-Spoke Reality Check.
The Dark Art of RBAC Delegation
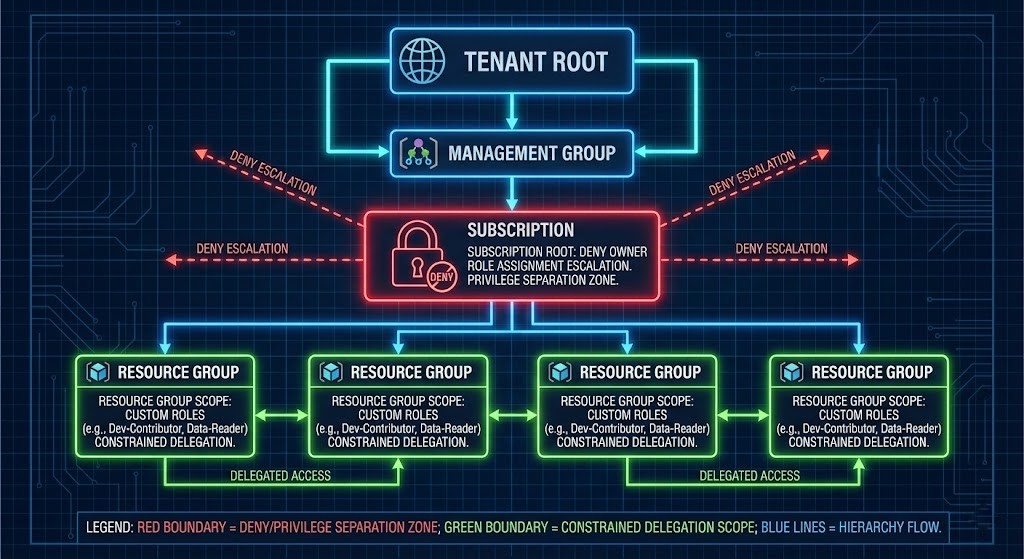
Most Landing Zones fail because Azure RBAC forces a false binary: Reader (useless) or Contributor (dangerous). The fix is constrained delegation — Azure RBAC was designed for centralized IT, not decentralized engineering teams, which is why most organizations misuse it.
Three delegation patterns that actually work:
- The Project Lead Model: Can manage Resource Groups and assign contributors downstream — but cannot assign Owner or modify subscription-level roles.
- The Platform Operator Model: Can manage compute and networking inside the subscription — but cannot modify Hub peering, DNS, or routing controls.
- The Security Observer Model: Read-only access plus security insights (Defender, Sentinel) — with zero write permissions.
RBAC anti-patterns to avoid:
- Contributor at Subscription Root: The lazy admin button. Grants too much control-plane power.
- Security Team as Owner: Security should audit the platform — not own the keys to the kingdom.
- Everyone gets User Access Administrator: This breaks the chain of custody for identity management.
DNS and private endpoint configuration is one of the most common sources of lateral movement risk in hub-and-spoke architectures. The Azure Private Endpoint DNS post covers the recursive loop and subnet exhaustion failure patterns that expose spoke-to-spoke paths you thought were isolated.
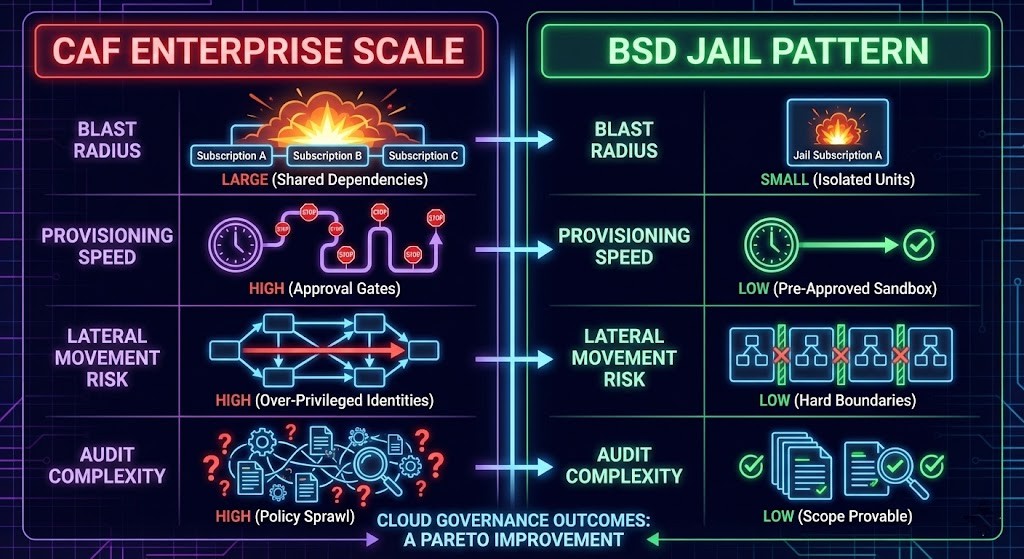
Security Outcome Matrix
Executives need measurable outcomes — not governance theater.
| Governance Model | Blast Radius | Mean Time to Provision | Lateral Movement Risk | Audit Complexity |
| CAF Enterprise Scale | Large (shared dependencies) | High (approval gates) | High (over-privileged identities) | High (policy sprawl) |
| BSD Jail Pattern | Small (isolated units) | Low (pre-approved sandbox) | Low (hard boundaries) | Low (scope provable) |
This is not a trade-off. It’s a Pareto improvement.
A Migration Path from CAF to Jails
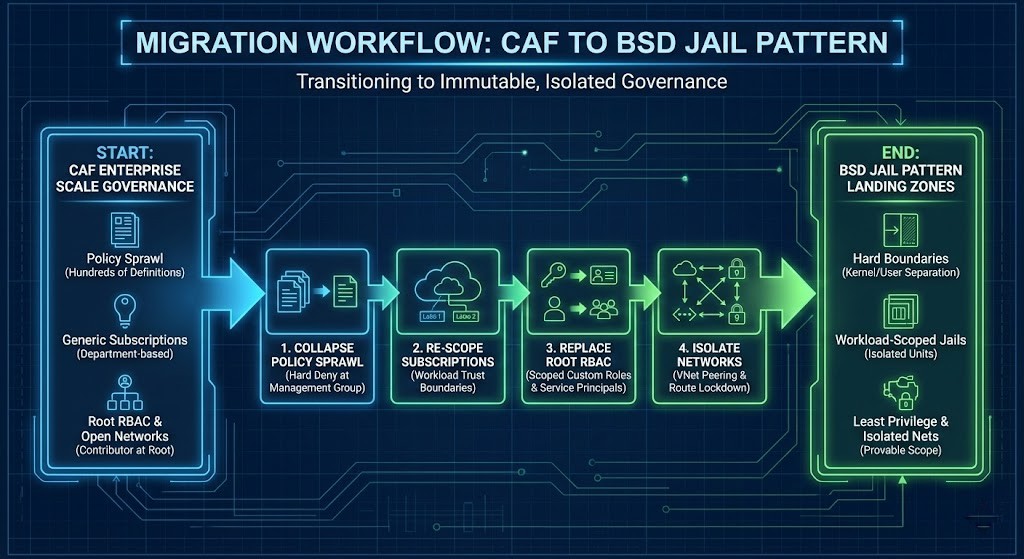
You cannot just flip a switch. Most organizations fail here — not because the model is wrong, but because they try to retrofit governance without refactoring ownership.
- Collapse Policy Sprawl: Replace hundreds of “audit” policies with a few hard deny policies at the Management Group level: Deny Public IP creation, Deny direct peering creation, Deny unsupported SKUs.
- Re-Scope Subscriptions: Move away from “Department” subscriptions (HR, Finance) and toward Workload Trust Boundary subscriptions (Payment Processor, Web Front End).
- Replace Root RBAC: Strip Contributor from the subscription root. Replace it with Modern Infrastructure & IaC service principals and scoped custom roles for workload teams.
- Isolate Networks: Enforce kernel/user plane separation by locking down VNet peerings, Route tables, and DNS/firewall paths.
Compliance & the Click-Ops Trap
Regulated readers will ask: does this work for HIPAA, PCI, or FedRAMP?
Yes — and it works better.
The Jail model strengthens compliance by making scope provable. Instead of relying on surveillance (logging everything), you rely on segmentation — mathematically proving access is impossible. Auditors don’t need more logs. They need smaller blast radii.
However, you cannot maintain this with Click-Ops. Manual governance creates systemic risk:
- Drift: What’s deployed ≠ what’s approved.
- Non-Repeatability: Every jail becomes slightly different.
- Non-Auditability: There is no git commit history for a portal click.
To succeed, you must stamp out these jails deterministically via IaC. The Modern Infrastructure & IaC Learning Path covers the full pipeline model for making this repeatable.
Architect’s Verdict
If your governance model requires a weekly steering committee, it is already broken.
Cloud complexity has tricked us into thinking we need complex controls. We don’t. We need simple, hard boundaries — and we need to stop writing rulebooks and start building jails.
If you’re running CAF Enterprise Scale today with 100+ policy definitions: You don’t have governance. You have governance theater. Start the migration by collapsing your audit policies to hard denies at the Management Group level — that single step reduces audit complexity and lateral movement risk without touching a single workload.
If you’re designing a new Azure landing zone: Don’t inherit the CAF defaults uncritically. Scope your subscriptions to workload trust boundaries from day one. Retrofitting isolation after the fact is the conversation the migration path section above describes — it’s painful and slow. Design the jails before the workloads move in.
If you’re in a regulated environment: The BSD Jail pattern is stronger for compliance than policy sprawl — because segmentation is provable and surveillance is not. Smaller blast radii mean shorter audit scope, fewer exceptions, and faster certifications.
This isn’t just an Azure concept. Whether you use AWS Accounts with SCPs or GCP Projects with Folders, the physics are the same: Isolation beats policy.
If you want an independent assessment of your current Azure architecture against these principles, the Zero-Trust Azure Architecture Audit surfaces your actual RBAC blast radius, NSG exposure, and governance gaps — scored against a production-readiness framework.
The Azure Cloud Architecture pillar is the full reference for Azure architecture on rack2cloud.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session





