The Broadcom Legal Playbook: Why the VMware Lawsuits Are Accelerating Enterprise Exit Timelines
Breaking today: CISPE — the Cloud Infrastructure Services Providers in Europe — has filed an urgent request with EU antitrust regulators asking them to temporarily halt Broadcom’s termination of the VMware Cloud Service Provider program across Europe. The filing argues that Broadcom’s January 2026 decision to terminate all but a handful of VCSP partners constitutes an abuse of market dominance, locking European cloud customers out of a platform they depend on with no viable migration runway. This is the legal pattern this post mapped — enterprises and now entire industry bodies using regulatory and legal mechanisms to buy migration time while the architecture work catches up. The Tesco case is still active. The CISPE EU complaint is now escalating to interim measure territory. The exit clock has not slowed down.
AT&T. Siemens. Fidelity. Tesco. UnitedHealthcare. The list of enterprises suing Broadcom over VMware licensing is no longer a curiosity — it is a pattern. And what that pattern reveals is not a story about legal strategy. It is a story about migration physics.
The enterprises suing Broadcom are not doing it because they want to stay on VMware. They are doing it because a safe exit takes 18 to 36 months to execute, and Broadcom’s licensing clock does not care about that timeline.
This is the architectural read on what the lawsuits actually mean for your exit planning.
The Procurement Shockwave
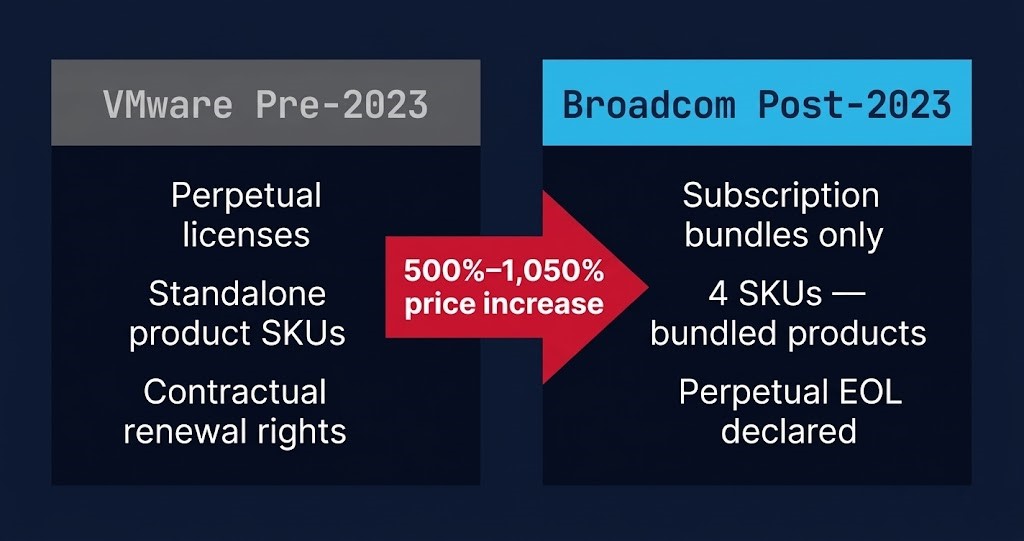
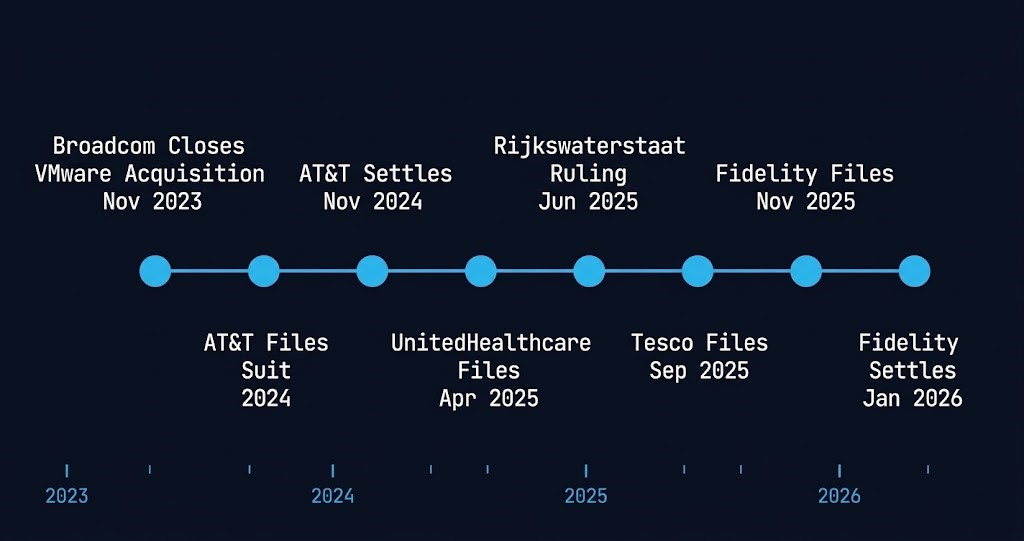
When Broadcom completed its $61 billion acquisition of VMware in November 2023, it moved immediately. Perpetual licenses — the foundation of enterprise VMware deployments built over decades — were discontinued. Hundreds of standalone VMware products were collapsed into four subscription bundles. Customers who had purchased perpetual licenses with contractual renewal rights found those rights effectively voided.
The pricing impact was not marginal. AT&T alleged a price increase of 1,050% in its lawsuit. Other enterprises reported increases ranging from 500% to over 1,000% on VMware renewal costs. The mechanism was deliberate: customers who needed support for perpetually licensed software had no path to renewal except through the new subscription bundles — bundles that included products they did not need at prices calibrated to a captive audience.
The legal theory across every major case is consistent: Broadcom is refusing to honor contractual renewal rights that existed before the acquisition. The breach is not accidental. It is the business model.
For the full exit decision framework — platform selection, licensing exposure modeling, and migration sequencing — see the Broadcom Exit Strategy.
The Case Docket — What Is Actually Happening in Court
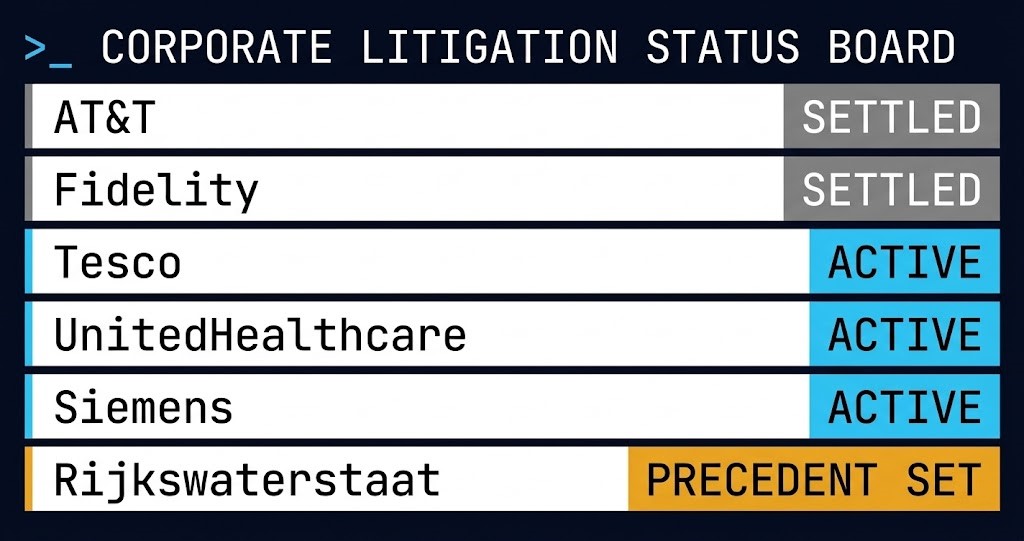
| Company | Filed | Status | Key Claim |
|---|---|---|---|
| AT&T | 2024 | Settled Nov 2024 | 1,050% price increase on renewal |
| Fidelity | Nov 2025 | Settled Jan 2026 | Renewal rights violated — 50M customers, $17.5T AUM at risk |
| Tesco | Sep 2025 | Active | £100M+ — perpetual EOL declared mid-contract, supply chain in litigation |
| UnitedHealthcare | Apr 2025 | Active | Healthcare infrastructure, federal compliance obligations |
| Siemens | 2025 | Active | Breach of contract + copyright infringement, multi-jurisdictional |
| Rijkswaterstaat | — | Precedent set Jun 2025 | Court-ordered continued support until migration complete |
Understanding the lawsuits requires separating settled cases from active ones.
AT&T — Settled confidentially in November 2024. AT&T alleged the 1,050% price increase and reached terms that have not been disclosed. The settlement precedent matters: Broadcom will negotiate when litigation risk is credible.
Fidelity — Filed November 2025 in Massachusetts state court. Fidelity has managed VMware infrastructure since 2005 — virtualization software is embedded in trading systems, account access platforms, and internal operations serving 50 million customers and $17.5 trillion in assets under management. When Broadcom refused to honor Fidelity’s renewal rights and insisted on a larger bundle, Fidelity sued and warned the court that sudden termination would cause massive outages across its platforms. Settled January 2026 before the hearing — Broadcom agreed to continue providing software access to a Fidelity subsidiary. Like AT&T, the settlement terms are not public.
Tesco — Filed September 2025, still active as of March 2026. Tesco purchased perpetual VMware licenses in January 2021 covering approximately 40,000 virtual workloads — cash register systems, logistics, supply chain infrastructure. The contract ran to January 2026 with a four-year extension option. Broadcom declared the perpetual software end-of-life and refused to honor the extension. Tesco is seeking at least £100 million in damages. The case has since drawn in Computacenter (the reseller) and Dell (the distributor), both of whom filed counter-claims. The supply chain of VMware’s own distribution network is now in litigation.
UnitedHealthcare — Filed April 2025, active in Minnesota federal court. Healthcare infrastructure, federal compliance obligations, and patient-facing systems at stake.
Siemens — Multi-jurisdictional case, discovery phase. Includes copyright infringement claims in addition to breach of contract.
Rijkswaterstaat (Netherlands) — The District Court of The Hague ruled in June 2025 that Broadcom must continue providing support to the Dutch water management agency until migration to an alternative is complete. This is the precedent that matters most for enterprise architects: courts will order continued support if migration requires it.
Why Enterprises Are Suing Instead of Migrating Immediately
The question the lawsuits actually answer is not “why are these companies fighting Broadcom?” It is “why haven’t they already left?”
Fidelity’s court filing answered it directly: the company told the court it would need 18 to 24 months to migrate off VMware given how deeply the platform is embedded across its systems. A sudden cutoff was, in Fidelity’s words, “technologically impossible” without risking massive outages.
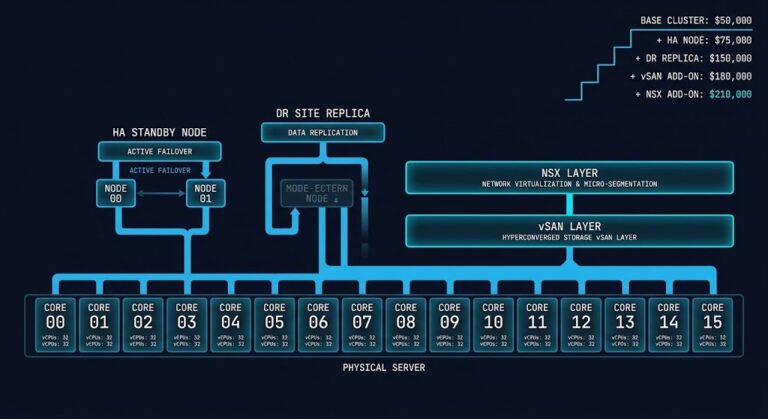
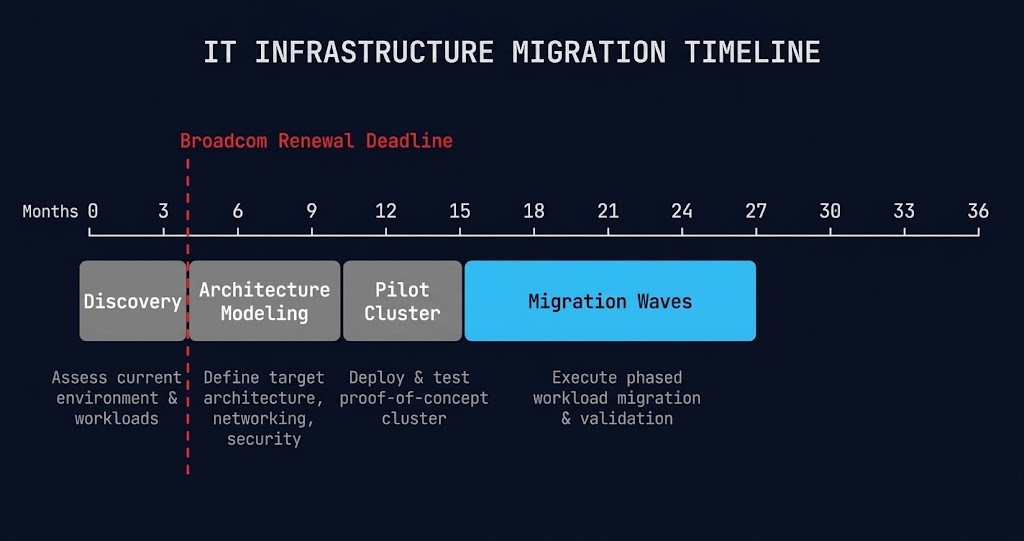
This is not a Fidelity-specific problem. It is the physics of enterprise VMware migration. A VMware estate built over 10 to 20 years is not a configuration file — it is execution physics. As covered in Part 1: Beyond the VMDK, migrating that estate requires translating execution physics, not copying disk images. The four phases that make up a safe exit:
| Phase | Duration | What Happens — and What Breaks Without It |
|---|---|---|
| Discovery | 2–3 months | Complete inventory of workload dependencies, storage profiles, network topology, and licensing exposure. Most enterprises do not have this at migration-ready fidelity. Discovery surfaces the surprises that break migration timelines — not a checkbox. |
| Architecture Modeling | 2–4 months | Target platform design, validation, and approval per workload class. AHV has different execution physics than ESXi. Proxmox has different storage I/O characteristics. K8s introduces a different operational model entirely. This is where Controller Tax analysis and HCI resource contention modeling happen — not during cutover. |
| Pilot Cluster | 1–2 months | Architecture proven against real workloads in non-production. Surfaces edge cases the model missed — the application that assumes a specific NIC driver, the database that depends on a storage latency profile that does not translate cleanly. |
| Migration Waves | 6–18 months | Workloads move in sequenced waves — K8s-ready first, legacy last. High-I/O cutovers require specific sequencing discipline to avoid data loss. Each wave has rollback criteria and a validation gate before the next begins. |
The Hidden Timeline Problem
The Rijkswaterstaat ruling in The Hague is the most important legal development for enterprise architects — more important than any of the settlements. The Dutch court ruled that a customer cannot be left without support if the migration to an alternative requires time to execute safely. Broadcom was ordered to continue support until the migration is complete.
That ruling creates a legal template. Enterprises with documented migration plans and demonstrable timeline constraints have a credible basis for seeking injunctive relief — not to stay on VMware indefinitely, but to stay on VMware long enough to leave safely.
This is the actual legal strategy: not “we want to keep our perpetual licenses forever” but “we cannot safely exit in the timeframe Broadcom is demanding, and a court-ordered support extension is the only way to avoid operational harm.”
AT&T settled. Fidelity settled. Both got continued access. Neither settlement required Broadcom to change its licensing model. The pattern suggests Broadcom’s actual threshold is credible litigation risk — and that enterprises with documented migration dependencies and operational harm arguments can reach that threshold. The settlement terms are never disclosed. That is deliberate. But the pattern is visible.
The destination that migration timeline buys you time to reach — and the constraints each platform imposes on that execution window — is the subject of Proxmox vs Nutanix vs VMware: The Post-Broadcom Constraints No One Explains
The Rack2Cloud Read
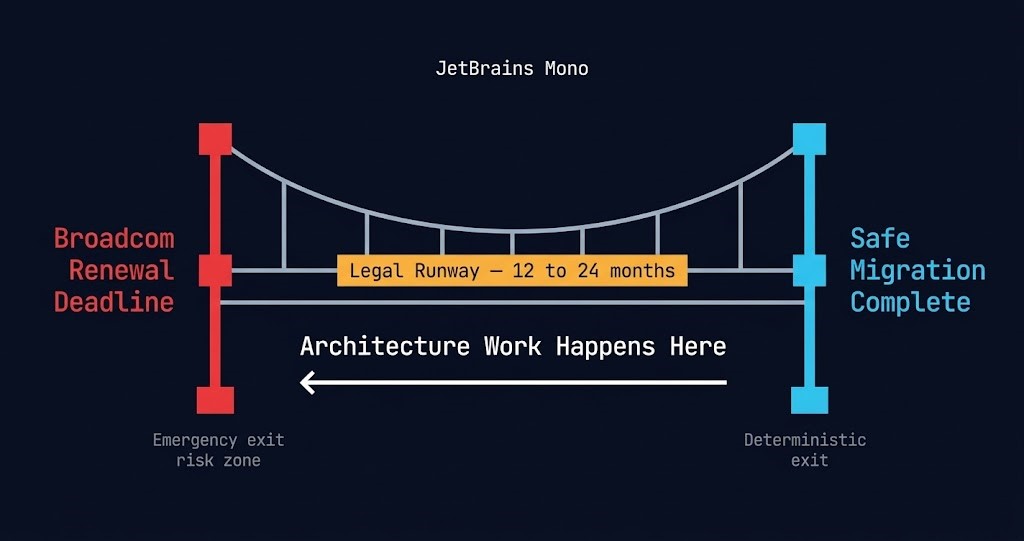
The lawsuits are not a VMware survival strategy. The enterprises filing them are not betting on courts forcing Broadcom to restore perpetual licensing. They are buying migration runway.
Every settlement buys 12 to 24 months of continued access. That is exactly the window a deliberate, architecture-first migration requires. The legal spend is not a cost — it is the price of not doing an emergency migration under time pressure, which is where data loss, operational failures, and replatforming mistakes actually happen.
What the Tesco case adds that the others do not is the supply chain dimension. Computacenter and Dell are now in litigation because of their roles in the original contract. For enterprises with reseller-mediated VMware contracts: your contractual rights may run through the reseller chain, and that chain has legal standing of its own. Document it.
For architecture leads, the operational takeaway is straightforward: if you are still in a VMware renewal conversation with Broadcom, you are already behind on the migration timeline. The Rijkswaterstaat precedent gives you a legal mechanism for buying time. The Fidelity and AT&T settlements give you the negotiating template. But none of that replaces the migration work — it just buys the time to do it correctly.
For organizations evaluating the K8s exit ramp as a parallel track alongside AHV migration — handling containerizable workloads while the VM estate migrates — see the Kubernetes VMware Exit Ramp guide. For the complete exit decision framework above both tracks, see the Virtualization Architecture Strategy.
The lawsuits are not the strategy. They are the bridge while the real work happens.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session