The Connected Air Gap: Why Most Backup Isolation Fails
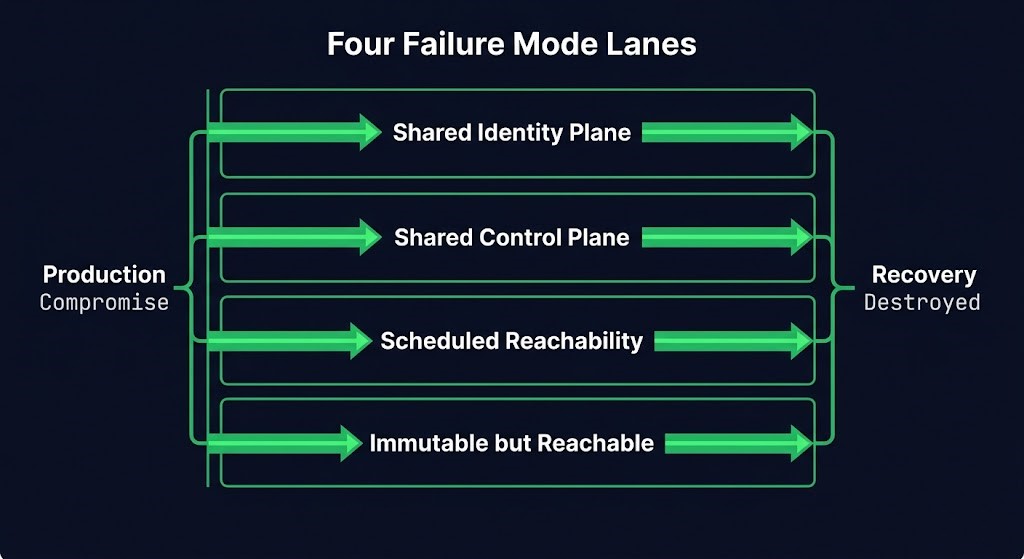
Most backup architectures marketed as air-gapped are not isolated. They are reachable systems with better storage controls. Shared identity, shared control plane, scheduled connectivity, and immutable-but-addressable storage all produce the same outcome: production compromise can still destroy recovery without touching backup data.
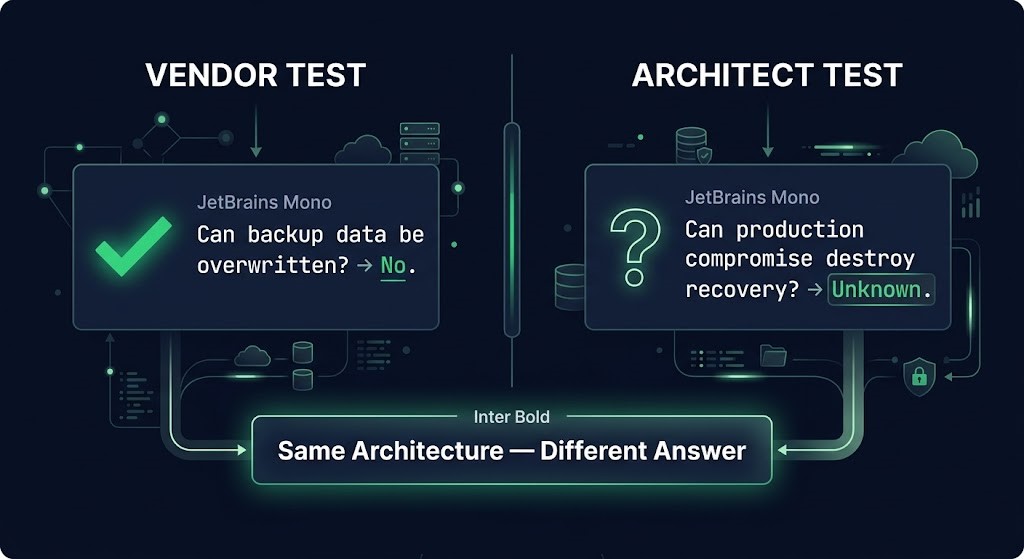
Data protection and blast-radius isolation are different architectural properties. Data protection answers whether backup blocks can be overwritten. Blast-radius isolation answers whether production compromise can destroy recovery capability entirely. Most backup assessments test the first property. The connected air gap fails on the second. The question that cuts through both is this: Can a compromised production control plane still issue a destructive command against recovery? If the answer is anything other than a clean no, the air gap is connected.
What “Connected Air Gap” Actually Means
An air gap is not a storage property. It is a control-plane boundary — the architectural condition under which no production-privileged actor can reach, command, or disable recovery. Four conditions break that boundary without touching backup data: a shared identity plane, a shared management control plane, a scheduled replication window that opens a live path to the backup target, and a storage tier that is immutable but still addressable by production-level credentials. Any one is sufficient. Under active compromise, an attacker does not need to corrupt backup data. They need to find one of those four conditions and use it.
The Four Failure Modes
Vendors describe these conditions as solved. They are not solved — they are shifted. Each failure mode below follows the same logic: what the architecture appears to isolate, what remains shared, and how recovery dies without the backup data being touched.
Failure Mode 1: Shared Identity Plane
The vault is separate. The backup system is on a dedicated network segment. The credentials authenticating the backup agent, the replication job, or the vault API are issued by the same identity provider as production workloads. That is a connected air gap.
A compromised domain admin, an exfiltrated service principal, or a hijacked SSO session can authenticate against the backup platform using production-derived credentials. The network isolation is real. The identity isolation is not. In enterprise environments this surfaces through Active Directory service accounts shared across production and backup agents. In cloud-native architectures it surfaces through IAM roles granted to workload identities that manage both production and backup — the same team, the same account, the path of least resistance.
If recovery shares production trust, recovery shares production blast radius. The fix is architectural: separate IdP tenants, separate cloud accounts, or hardware-rooted credential stores with no traversable trust relationship to the production identity boundary. Not a separate role in the same tenant. Separation.
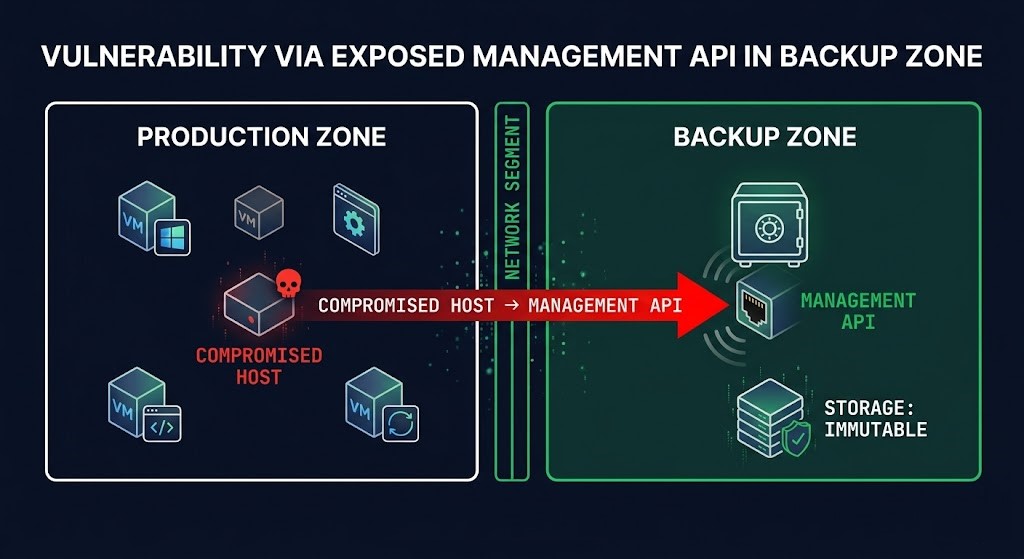
Failure Mode 2: Shared Control Plane
Most backup platforms do not fail because backup storage is reachable. They fail because backup control is.
Even with separate credentials, the backup management plane — the server API, the vault console, the snapshot orchestration layer — is frequently reachable from the production management network. A compromised host with network access to that API does not need backup credentials to cause damage. Purge operations, retention policy modifications, recovery point deletions: the exposure depends on what the management API surfaces without authentication and what the network ACLs actually enforce, not what the architecture diagram shows.
Cloud backup vaults concentrate this risk. When a vault lives in the same subscription or account as the protected workloads, subscription-level compromise does not need to overwrite backup data. It needs to delete the vault. Immutability protects the objects inside the vault. It does not protect the account that owns it — unless vault deletion protection is explicitly enabled, separately locked, and tested under adversarial conditions. Most environments have immutable backup configured. Few have confirmed that subscription-level compromise cannot destroy the vault entirely.
Failure Mode 3: Scheduled Reachability
True air-gap architectures accept a recovery time penalty in exchange for genuine isolation. Most production environments trade that penalty for a replication window — a scheduled period during which production can reach the backup target, followed by disconnection. The architecture is described as near air-gap. The replication window is described as controlled.
The replication window is the gap in the air gap. It is also deterministic. An attacker with persistent production access and visibility into the backup schedule — which is frequently available through agent logs, scheduler configurations, or backup console dashboards reachable from production — can time destructive actions to execute during the open window. The backup data replicates. The window closes. The target has been poisoned before isolation restores.
Scheduled reachability is not air-gap isolation. It is a windowed attack surface with a known open time.
Failure Mode 4: Immutable but Reachable
Immutability prevents overwrite of existing backup data. It does not prevent an attacker from revoking the credentials that perform restores, destroying the catalog that maps recovery points, deleting the vault or bucket that contains the data, or modifying the retention policy before the lock period expires if the policy lock itself is not separately protected.
If an attacker can revoke restore authority, destroy the catalog, or disable orchestration, the backup survives and recovery still fails. The data is intact. The recovery capability is not. Under time pressure — which is the condition under which every serious recovery occurs — those outcomes are functionally equivalent to data loss.
The Control-Plane Test
Apply one question to every layer of your backup architecture from the perspective of a compromised production actor:
THE CONTROL-PLANE TEST
“Can a compromised production control plane still issue a destructive command against recovery?”
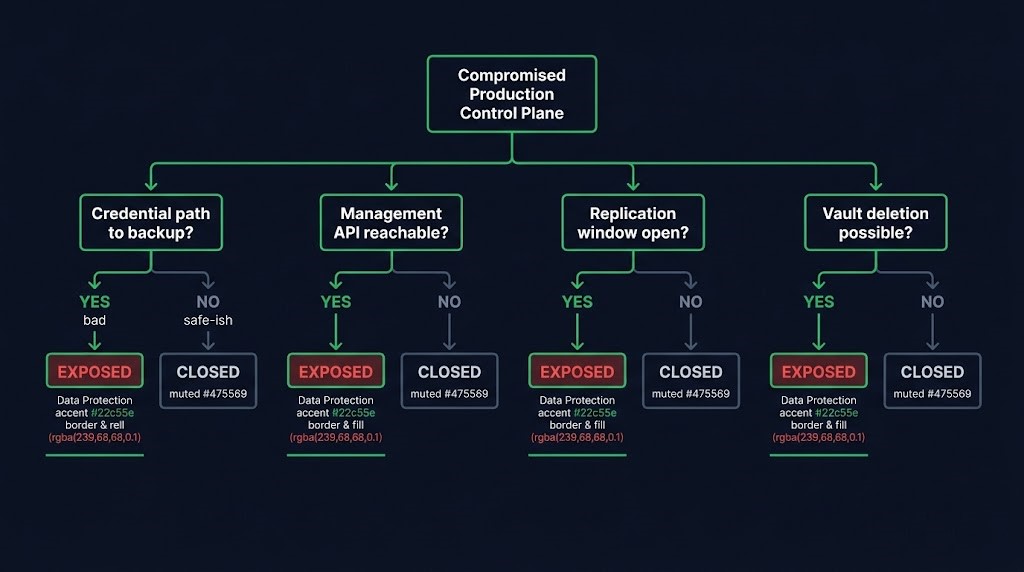
If yes, the air gap is connected. Connected systems are reachable systems. Reachable systems are not isolated systems.
Work through each layer: Does the backup agent authenticate using production-domain credentials? Can the backup management API be reached from a production subnet? Is there a replication window during which production has a live path to the backup target? Can subscription-level permissions delete the vault or revoke restore credentials? Each yes is a connected air gap condition. None of them require the attacker to touch backup data. All of them are sufficient to destroy recovery under active compromise.
The architectural response to each condition is different — identity plane separation for credential exposure, network segmentation plus API authentication hardening for management plane exposure, eliminated or cryptographically authenticated replication windows for scheduled reachability, and deletion protection plus restore-path testing for immutable-but-reachable. The post at /logic-gapping-backup-architecture/ covers how to address each gap systematically. This post’s purpose is the diagnosis.
Where Vendor Claims Break Down
Vendors validate storage integrity. Architects need to validate blast-radius isolation. Those are different tests, and they return different answers on the same architecture.
A vendor certification shows backup data is isolated and immutable. A penetration test, if it exists, typically confirms backup data cannot be overwritten. Neither test asks whether a production-privileged actor can destroy recovery capability through identity traversal, management plane access, a timed replication window, or vault deletion. The gap between what is validated and what is tested is exactly where connected air gap conditions live.
| Connected Air Gap Condition | What the Vendor Addresses | What It Leaves Open |
|---|---|---|
| Shared Identity Plane | Separate backup service account | Same IdP — production compromise traverses trust |
| Shared Control Plane | Dedicated backup network segment | Management API reachable from production subnet |
| Scheduled Reachability | Replication window with disconnection | Deterministic attack window during open phase |
| Immutable but Reachable | Object lock / WORM storage | Vault deletion, restore credential revocation |
For the full treatment of why immutability is insufficient as a standalone protection boundary, see Immutable Backup and Object Lock: Why It’s Not Enough. For how these four conditions map to ransomware attack chains specifically, see Ransomware Backup Architecture: Beyond the 3-2-1. The NIST SP 800-209 storage security guidelines provide the vendor-neutral framework against which to evaluate any air-gap claim: NIST SP 800-209.
Architect’s Verdict
An air gap is a control-plane boundary, not a storage property. Every backup architecture that shares an identity plane, a management plane, or a replication schedule with the environment it protects has a connected air gap — regardless of what the storage tier’s immutability settings say.
The failure is not a missing feature. It is a misplaced test. Backup architecture assessments validate data protection. The correct test is blast-radius isolation under production compromise. Run both tests on the same architecture and they return different answers, because they are measuring different properties. An environment that passes the first can fail the second comprehensively — and most do.
Recovery capability must be designed under the assumption that production is already hostile. Any architecture that shares trust, control, or command authority with production is not isolated. It is delayed compromise.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session