The Configuration Drift Discovery During a Drill
Quarterly recovery drill. Backup job green for four months. Restore executes cleanly — data intact, VM boots, database service starts. The application fails on the first transaction.
Three hours disappear into backup triage before anyone checks the environment.
The backup was not the problem. It never was. This is recovery configuration drift — and it belongs to the same class of data protection failure where the protection plane reports success and the recovery plane produces nothing useful.
What the Drill Was Testing (and What It Wasn’t)
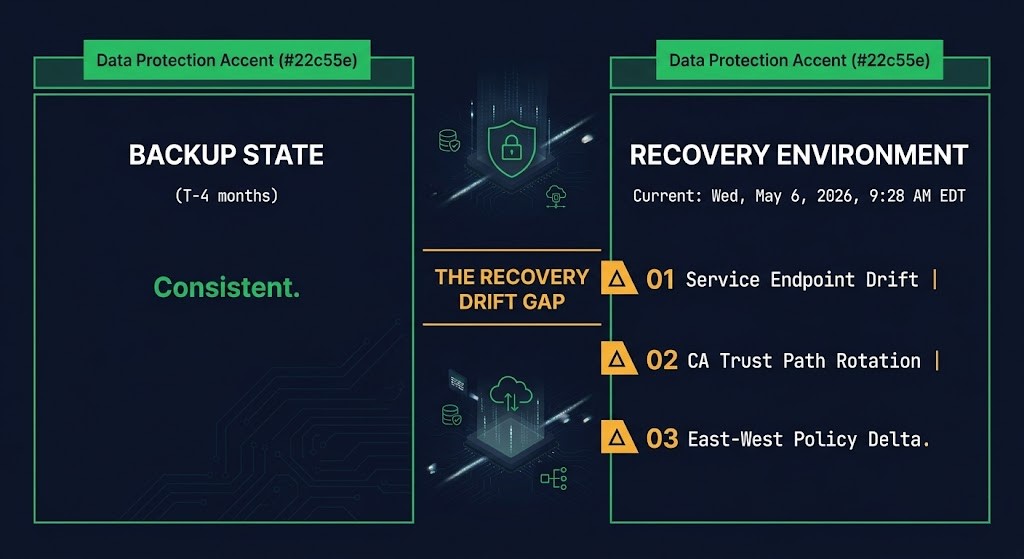
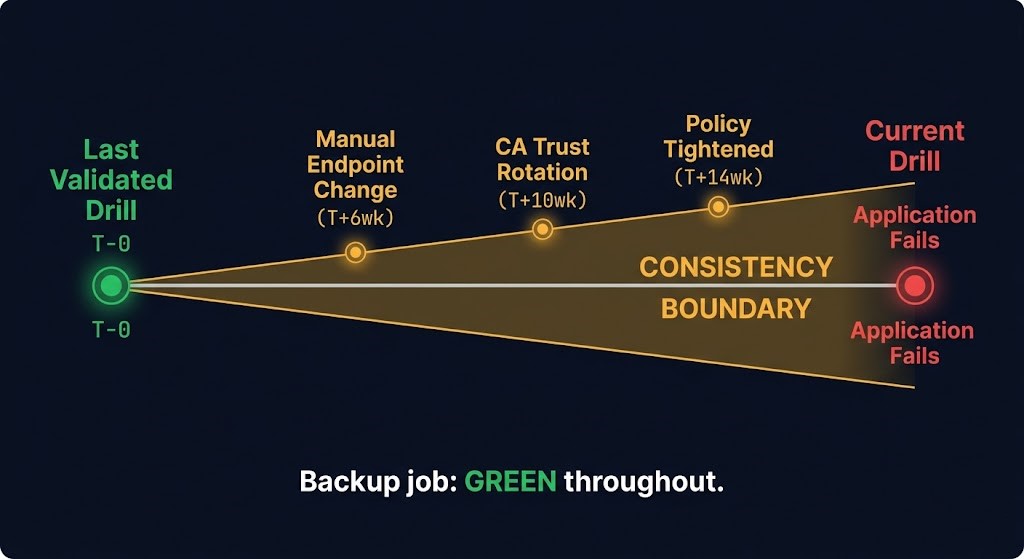
The drill validated backup integrity and restore mechanics — the protection plane. It did not validate environment state — the recovery plane. Four months of silent drift had accumulated between the backup capture point and the recovery target. The backup job reported green throughout. Nothing surfaced the gap until the restore ran into an environment that had moved on.
Three drift vectors accumulated silently over those four months. Each individually invisible. Each fatal at the application layer on restore.
01 — SERVICE ENDPOINT CHANGED
An internal service endpoint was updated — manual change, never committed back to IaC. The recovery config still pointed at the old dependency. The restored application reached out to an endpoint that no longer existed in that form. First transaction failed. The backup had nothing to do with it.
02 — INTERNAL CA TRUST PATH ROTATED
The internal CA trust path had been rotated by an automated process. The config reference was never updated. The restored application could no longer validate upstream auth — certificate chain validation failed silently on the first authenticated call. The backup was application-consistent at the point it was taken. The trust chain it assumed no longer existed.
03 — EAST-WEST NETWORK POLICY TIGHTENED
A security team policy change had tightened east-west traffic rules three months prior. The recovery runbook was never updated to reflect it. The restored application attempted to reach a service dependency on first transaction and hit a policy block. The change was correct. The recovery documentation was not.
None of these were flagged as backup problems. None appeared in backup job logs. All three were invisible until the application ran in a recovery environment that had accumulated three separate departures from the state the backup assumed.
The Recovery Drift Gap
This was a Recovery Drift Gap.
The backup was consistent. The recovery environment was not. The Consistency Boundary is where those two states diverged — the line between what the backup knows and what the environment currently is. In this case, that boundary had been widening for four months across three separate change vectors, none of which had any mechanism to propagate their state into the recovery runbook or the IaC-declared environment.
Every untracked manual change widens the Consistency Boundary. Every automated process that updates configuration without committing it back widens it. Every security policy change that doesn’t propagate to the recovery documentation widens it. The restore path treats the recovery environment as a known quantity. The Recovery Drift Gap is what happens when that assumption has been quietly wrong for months.
The gap does not announce itself. It waits for the drill — or worse, for the incident.
What a Pre-Drill Diff Actually Checks
The standard framing — “run drift detection before a drill” — is correct but not actionable. What actually gets checked in a pre-drill diff is more specific. Configuration drift detection at the IaC layer catches declared-state variance. But the Recovery Drift Gap lives in a wider surface than IaC state alone.
A pre-drill diff that is actually useful checks six things:
PRE-DRILL DIFF — WHAT ACTUALLY GETS CHECKED
- Current service endpoints — do recovery runbook references match what the environment is currently serving?
- Cert chain / trust store paths — has any CA rotation, cert renewal, or trust store update occurred since the last validated drill?
- Security group / ACL / east-west policy deltas — have any policy changes been applied that would block traffic paths the restored application depends on?
- DNS dependencies — do internal resolution paths the restored app will traverse still resolve to the correct targets?
- Secret path references — vault paths, key references, rotation state — does the restored application’s config point at secrets that still exist at those paths?
- Mount / storage path assumptions — anything the application opens on first transaction — are those paths still valid in the recovery environment?
This is not a full environment audit. It is a pre-flight against the specific failure modes that kill restores in well-maintained environments — the ones that have nothing to do with whether the backup completed successfully.
The Transferable Principle
The backup is not the unit of recovery. The backup plus the environment configuration plus the dependency graph is the unit of recovery. A drill that only validates backup integrity has validated one third of that unit — and in environments where backup integrity is mature and reliable, one third is exactly where the coverage ends.
This is the same structural gap documented in RTO and RTA measurement — the declared target assumes the recovery environment is ready. The Recovery Drift Gap is what accumulates when nobody validates that assumption between drills. It is also why ransomware recovery architectures that depend on clean restores fail in practice — the backup survives the attack; the environment configuration that the backup assumes may not.
Backup integrity tells you the restore can start. It tells you nothing about whether the application can recover.
DIAGNOSTIC QUESTION
“When did you last verify the recovery target environment matches the configuration state of what you’re restoring?”
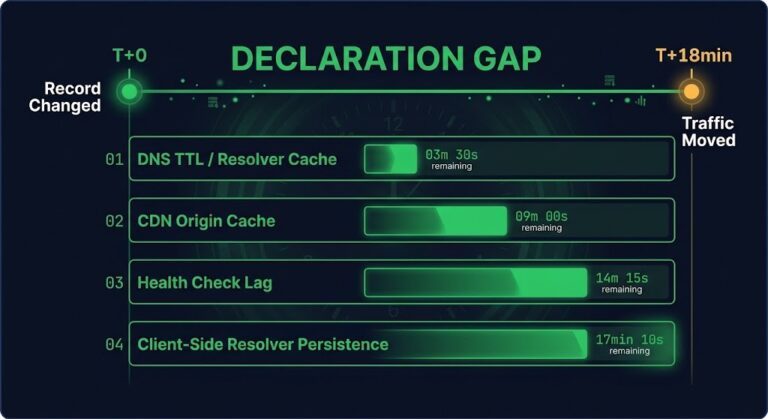
The FN-01 post in this series covered the Declaration Gap in DNS failover — every layer behaving correctly while the system failed operationally. The Recovery Drift Gap is the same failure class at a different layer. The backup mechanics are correct. The environment state is not. The combination produces a restore that completes and an application that doesn’t.
The backup restored exactly as expected. The environment didn’t. Only one of them was being tested.
Architect’s Verdict
Recovery configuration drift is the silent accumulator between every backup and every restore. It doesn’t announce itself. It doesn’t appear in backup job logs. It accumulates in the delta between what the backup assumes the environment looks like and what the environment actually is — and it widens every time a manual change goes untracked, every time an automated process updates config without committing it back, every time a security policy change doesn’t propagate to recovery documentation.
Drills are designed to test backup integrity. That design structurally excludes the failure mode that actually causes restore failures in mature environments — because once backup integrity is reliable, the gap moves somewhere else. It moves into service endpoint references, trust chain assumptions, policy deltas, and secret path state. None of those are backup problems. All of them are recovery problems. Most drill designs never reach them.
The drill that never surfaces a Recovery Drift Gap is either running in a perfectly maintained environment or testing the wrong thing. In most production environments, it is the latter.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session