OpenTofu Adoption Is a Control Plane Migration — Not a License Change
OpenTofu migration is not a licensing decision. It is a control plane migration — and treating it as anything less is the fastest route to a corrupted state file, a broken provider dependency, or an operating model gap that surfaces at 2am on a production deployment.
The license change is the trigger. The migration is the event. Those are two different problems, and conflating them is why so many platform teams rush the execution and discover the risk after the fact.
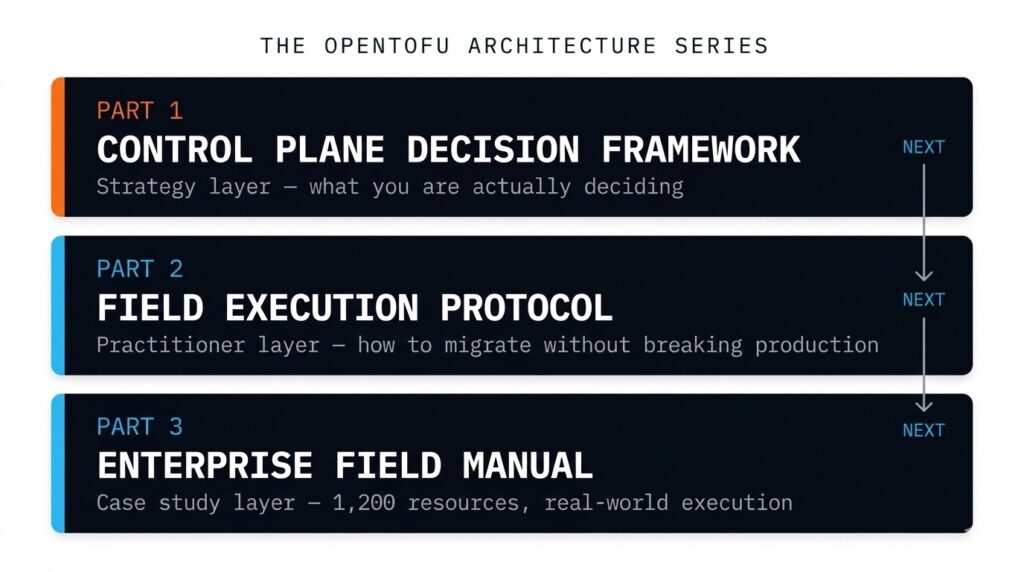
This post is not about whether OpenTofu is the right call. Part 2 of this series covers the field execution protocol. Part 3 documents a 1,200-resource enterprise migration in full. This post is about what you are actually deciding — before a single binary is swapped.
The State File Is Not a Configuration File
Every Terraform operator knows what a state file is. Fewer have thought clearly about what it represents: the authoritative mapping between every resource declaration in your HCL and its real-world identity in the provider. It is not metadata. It is not a cache. It is the control plane record that makes apply deterministic rather than destructive.
When you migrate to OpenTofu, the state file is what you are actually migrating. The binary is a 40MB download. The state file is years of infrastructure lifecycle history — and if that mapping is broken, inconsistent, or silently divergent between tools, tofu apply does not gracefully resume where terraform apply left off. It makes decisions based on a record it cannot fully trust.
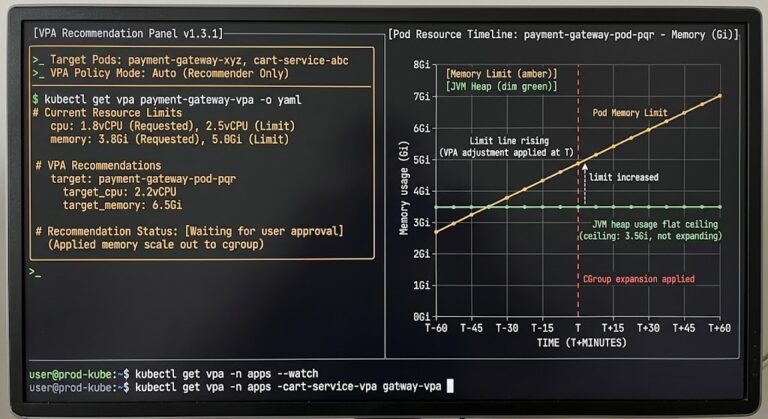
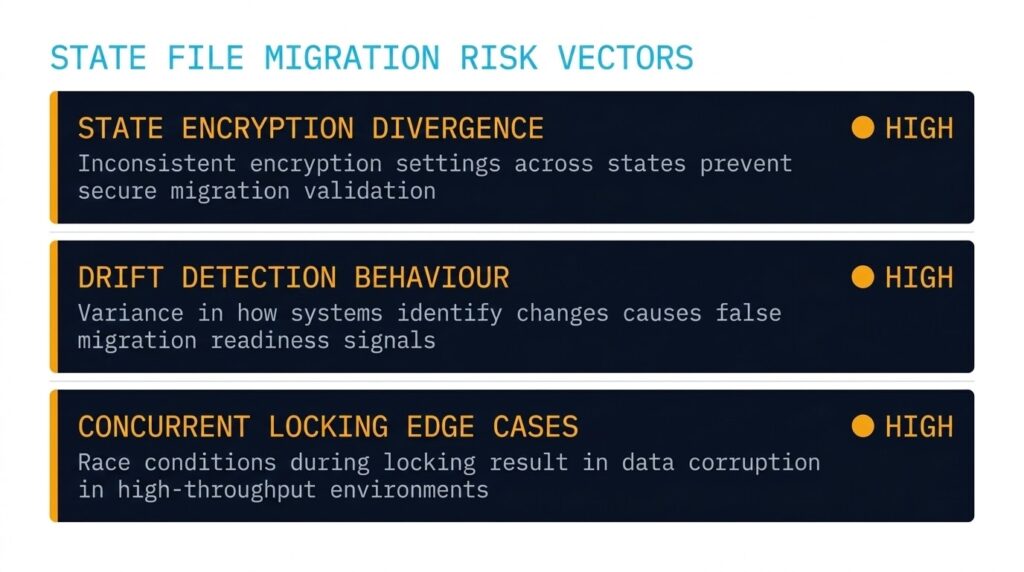
Three specific risk vectors deserve explicit modelling before migration begins:
State encryption divergence. OpenTofu introduced native client-side state encryption in v1.7 — a feature the community requested from HashiCorp for years and never received outside of Enterprise tier. If your current state is encrypted under a Terraform Enterprise or TFC-managed key, migration requires an explicit decryption and re-encryption step using OpenTofu’s key provider model. This is not a backend swap — it is a key migration with its own runbook requirements.
Drift detection behaviour. OpenTofu’s refresh logic has diverged from Terraform in edge cases involving specific provider resource types. Drift that Terraform classified as within acceptable bounds may surface as a planned destructive change under OpenTofu. Running tofu plan -refresh-only against a copy of production state before any migration activity is not a best practice — it is the minimum viable safety check.
Concurrent operation locking. S3 + DynamoDB locking behaves identically across both tools for standard configurations. Custom locking implementations, HCP-managed state, and edge cases involving concurrent pipeline runs are where behavioural differences surface — typically during the highest-load moments of a production deployment window.
.terraform.lock.hcl and verify each resolves identically from the OpenTofu registry.tofu plan -refresh-only against a copy of production state. Audit every proposed change before it touches live infrastructure.Audit your HCL configurations for BSL-divergent constructs and generate migration templates before touching the binary. This is gate zero — run it before the pre-migration checklist above, not after you’ve already started.
→ Run the Readiness AuditProvider Ecosystem Reality: Compatibility Is Not Parity
OpenTofu maintains a fork of the Terraform provider protocol and aims for drop-in compatibility. In most cases it delivers that. The problem is not the common case — it is the enterprise edge cases that don’t appear in compatibility matrices until a migration hits them in production.
Providers published in the Terraform Registry were built, tested, and release-cycled against Terraform’s SDK and release schedule. OpenTofu tracks this closely, but the release cadence is independent. When HashiCorp ships a provider update, OpenTofu compatibility is not guaranteed on day one — and enterprise providers are slower to add OpenTofu to their test matrices than community providers.
Where friction surfaces in enterprise environments specifically:
Advanced cloud networking configurations — Transit Gateway associations, Private Link dependencies, VNet peering with policy attachments — exercise provider edge cases that standard compatibility tests don’t cover. Security and secrets providers, particularly HashiCorp Vault’s own provider, have an obvious structural dynamic: new resource types tend to land in the Terraform provider first. SaaS integration providers (Snowflake, Datadog, PagerDuty) vary significantly in their OpenTofu testing coverage.
The reliable signal is not a vendor’s compatibility claim. It is whether the provider repo includes OpenTofu in its CI matrix. Those are different things.
Monitor the feature divergence between Terraform and OpenTofu release cycles in real time. If your migration depends on provider or feature parity, this is the signal you need to watch — not the vendor’s compatibility statement.
→ Check the Feature LagWhat CNCF Sandbox Actually Means for Enterprise Planning
The CNCF Sandbox acceptance is being used as a credibility shortcut in ways that misrepresent what the maturity levels mean. This matters for enterprise teams building 3–5 year infrastructure plans.
| Stage | What It Actually Means | Enterprise Implication |
|---|---|---|
| Sandbox | Project shows promise. CNCF provides a neutral home. Governance and ecosystem still forming. | Roadmap, API surface, and governance model subject to evolution |
| Incubating | Growing adoption, defined governance, demonstrable production use cases. | Ecosystem stabilising — production adoption defensible with documented risk |
| Graduated | Proven at scale, stable governance, broad ecosystem adoption. Kubernetes and Prometheus are here. | Enterprise adoption well-supported by community and vendor ecosystem |
OpenTofu is at Sandbox. That is not a criticism — it is a planning input. Kubernetes entered Sandbox in 2016 and graduated in 2018. The trajectory matters more than the current stage, and OpenTofu’s trajectory is clearly positive. But platform teams building internal tooling on top of OpenTofu should treat the API surface as more likely to evolve than a Graduated project’s would be — and model their upgrade cadence accordingly.
The Operating Model Gap: You’re Not Replacing a Tool
This is the section most migration guides skip — because it implicates the team making the decision, not the technology.
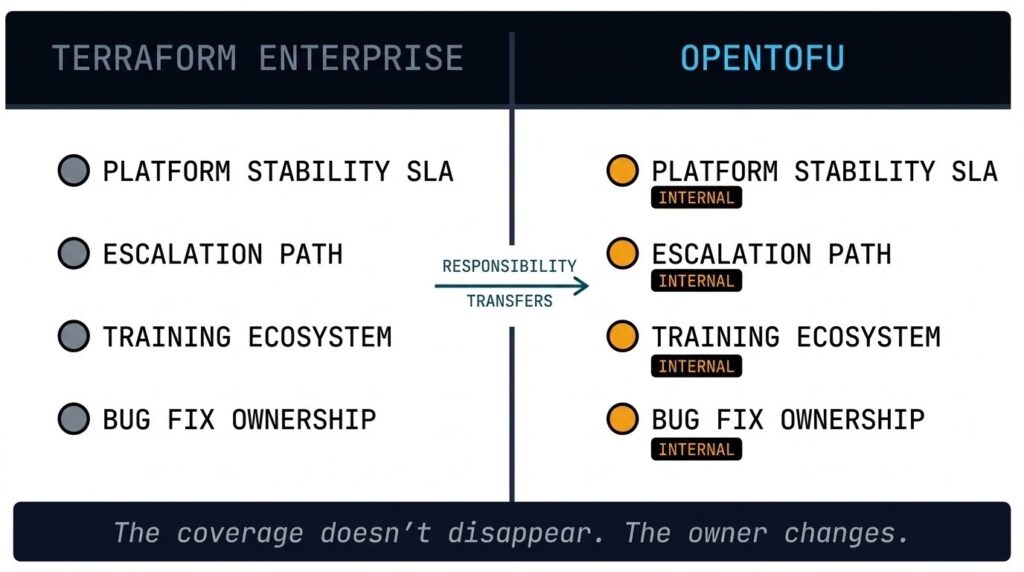
With Terraform Enterprise or Terraform Cloud, the support model is explicit. HashiCorp carries operational responsibility for platform stability, provides enterprise SLAs, maintains a training and certification ecosystem, and staffs a support organisation your platform team can escalate to when something breaks under load. That coverage is a line item in your contract that most teams never think about until it’s gone.
With OpenTofu, that responsibility transfers inward. The community is active and responsive, but community support is not an SLA. When a state locking edge case surfaces during a production deployment window, the escalation path is a GitHub issue and a Slack channel — not a support ticket with a contractual response time.
The honest reframe: migrating to OpenTofu is not just changing a binary — it is shifting execution authority to the CLI control plane, which most teams have never treated as a governed layer. It is replacing a vendor support contract with internal operational ownership. Platform teams that make this migration without auditing what that contract actually covered — and mapping each coverage item to an internal owner — are accepting an operational exposure gap they haven’t modelled.
This is not an argument against OpenTofu. It is an argument for doing the capability assessment before migration, not after a production incident forces it.
The Decision Framework: When Each Path Makes Sense
| Scenario | OpenTofu | Terraform |
|---|---|---|
| Platform engineering team with strong IaC ownership | ✓ Strong fit | Paying for support you don’t use |
| GitOps-heavy environment, no CLI-level SaaS dependency | ✓ Strong fit | License compliance overhead without benefit |
| Sovereign or air-gapped infrastructure requirements | ✓ Strong fit | BSL restrictions create compliance questions |
| Regulated environment with validated TF configuration stack | Re-validation cost may not justify switch | ✓ Hold position, model exit timeline |
| Deep HashiCorp Vault / Consul automation dependencies | Provider parity gap — audit first | ✓ Vendor maintains provider parity |
| Team needs to outsource operational risk | Support model gap — build capability first | ✓ Enterprise SLA justified |
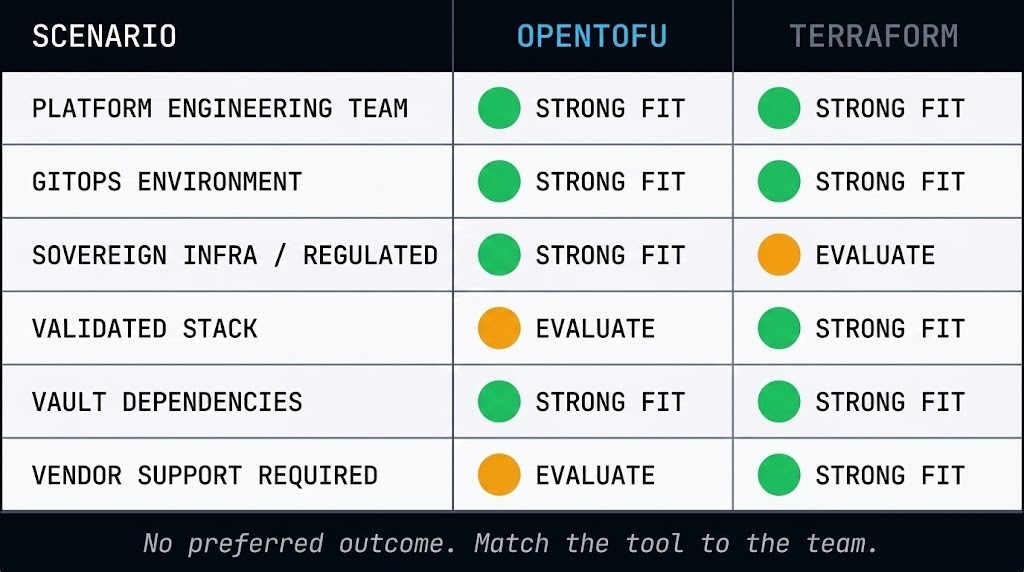
Rack2Cloud has no preferred outcome in this table. The right answer is the one that matches your team’s capability, your workload’s risk profile, and your organisation’s tolerance for open-source operational ownership — not the one that avoids a licensing conversation.
When you’re ready to execute: Part 2 covers the field protocol — registry scrub, binary swap, state encryption, and CI/CD refactor. Part 3 documents a 1,200-resource enterprise migration including backend evacuation, the sovereign audit protocol, and real-world troubleshooting.
Frequently Asked Questions
Q: What is the difference between OpenTofu and Terraform?
A: OpenTofu is an open-source fork of Terraform, created after HashiCorp changed Terraform’s license from the Mozilla Public License to the Business Source License (BSL) in August 2023. OpenTofu maintains drop-in CLI and provider compatibility with Terraform while operating under an MPL 2.0 license with CNCF governance. The tools are functionally near-identical for most workloads, with divergence emerging at the provider ecosystem level and in features where HashiCorp’s commercial interests have influenced Terraform’s roadmap.
Q: Is OpenTofu production-ready for enterprise environments?
A: Yes, with the right team capability in place. OpenTofu is running in large-scale enterprise environments globally. The qualification is operating model maturity — teams replacing a Terraform Enterprise or TFC support contract need to explicitly map what that contract covered to internal owners or community escalation paths before migration. The technology is production-grade; the organisational readiness requires deliberate assessment.
Q: How do I know if my Terraform configuration will work with OpenTofu?
A: The OpenTofu Readiness Bridge audits your HCL for BSL-divergent constructs and generates migration templates before you touch the binary. For provider-specific compatibility, check whether each provider’s repo includes OpenTofu in its CI test matrix — not just a compatibility statement in the README.
Q: What does CNCF Sandbox status mean for OpenTofu’s long-term viability?
A: Sandbox is the entry stage of the CNCF maturity model — it signals that the project is credible enough to bet on, not that the bet is risk-free. Kubernetes entered Sandbox in 2016 and graduated in 2018. OpenTofu’s trajectory is clearly positive. Enterprise teams should model the API surface and governance model as more likely to evolve than a Graduated project’s, and plan their upgrade cadence accordingly.
Q: Can I migrate from Terraform to OpenTofu without downtime?
A: For most configurations, yes. The binary swap and provider re-initialisation can be done without infrastructure downtime. The risk window is state file handling — particularly if your state is encrypted under TFC/TFE key management, or if provider drift detection behaves differently under OpenTofu for your specific resource types. Running tofu plan -refresh-only against a state copy before migration is the minimum safety check.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session