Rubrik vs Cohesity: Which Backup Architecture Actually Scales?
Most Rubrik vs Cohesity comparisons are useless.
Not because the features are wrong — but because neither Rubrik nor Cohesity fails in a feature checklist. They fail when your environment scales in ways the architecture didn’t expect.
The question isn’t which platform has better deduplication ratios or a cleaner UI. The question is which architectural model holds when your site count doubles, your ransomware recovery window shrinks, and your ops team stays the same size.
That’s the comparison worth having.
The backup platform decision isn’t about features. It’s about which architecture breaks last.
The Constraints That Actually Matter
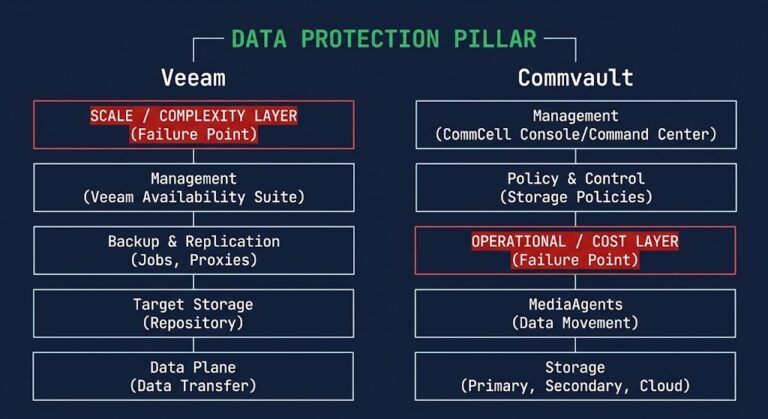
Before you evaluate either platform, map your environment against the constraints that actually determine which architecture fits. Feature checklists won’t surface these. Failure postmortems will. The Data Protection Architecture pillar maps the full decision space — but these are the five inputs that drive the platform decision specifically.
None of these appear on a vendor datasheet. All of them will determine whether your platform decision holds at scale.
Two Scaling Philosophies — And Their Breaking Points
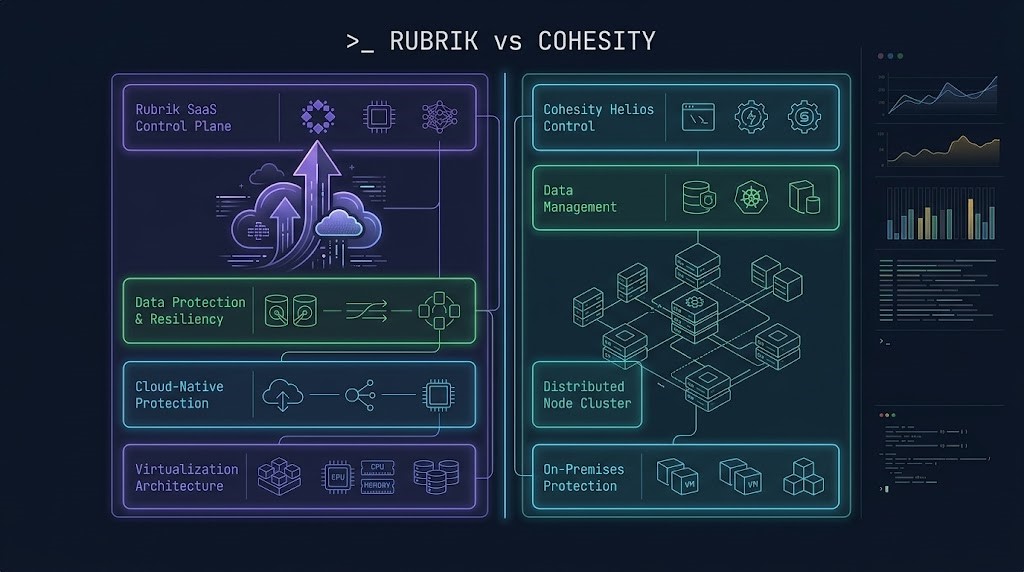
Rubrik and Cohesity are not competing on features. They are built on fundamentally different assumptions about where control should live and how scale should be managed.
Control Plane Scaling vs Data Plane Scaling
The control plane and data plane behave differently under scale pressure on each platform. Conflating them produces bad platform decisions.
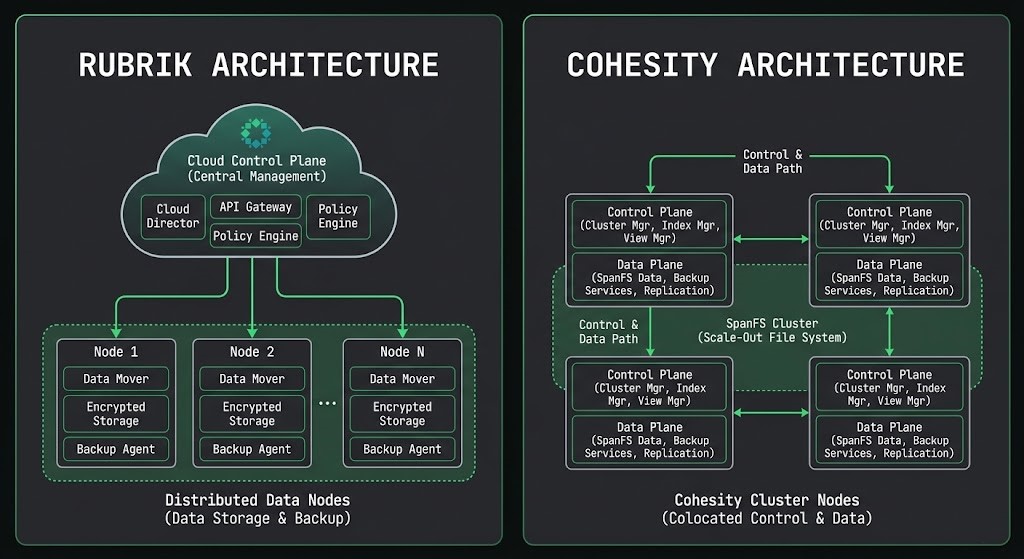
Control Plane Scaling
Rubrik’s SaaS control plane scales independently of data volume. Adding 50 new protected workloads doesn’t change the management model — the same interface, the same policy engine, the same upgrade cadence covers them automatically. The operational surface stays flat even as the data surface grows.
Cohesity’s control plane scales with the cluster. A single-site deployment is straightforward. Multi-site with cross-cluster replication requires explicit policy federation, replication configuration, and ongoing operational management of cluster relationships. The capability is there — it requires engineering to build and engineering to maintain.
Data Plane Scaling
Cohesity’s node-based expansion model is predictable. Add nodes, expand the SpanFS cluster, capacity and performance grow together. The data plane behavior under load is well-understood and deterministic.
Rubrik’s logical management model abstracts the data plane differently. Cloud-tier integration, global data management across sites, and replication topology require deliberate architecture — but the management overhead of that topology stays low because the control plane handles it centrally.
Where Each Architecture Starts to Struggle
Neither platform fails uniformly. Each has specific conditions under which the architecture starts working against you. These are the breaking points most teams discover after the purchase order, not before it.
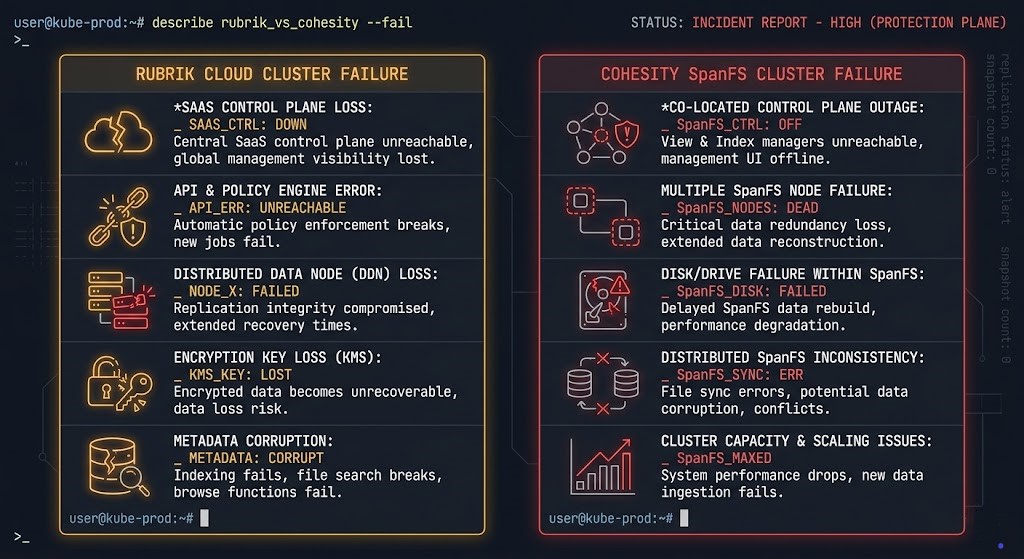
- [!] Strict air-gap requirements prohibit SaaS control plane reachability. A connected control plane and a genuine air gap are in direct tension — one has to give.
- [!] Edge environments with poor or intermittent connectivity create operational gaps in a model that assumes the control plane is always reachable for policy enforcement.
- [!] Cloud egress becomes unpredictable at scale. Recovery operations and replication workflows that route through cloud infrastructure accumulate egress costs that weren’t modeled in the initial architecture.
- [!] Multi-site sprawl grows faster than the team’s capacity to manage distributed cluster relationships. Operational overhead at 15 sites is not the same as at 3 — and the gap compounds.
- [!] Upgrade coordination across clusters becomes a sequencing problem. Maintaining version consistency across multiple clusters requires operational discipline that smaller teams routinely underestimate.
- [!] Global visibility without centralization friction is difficult to achieve by default. It requires deliberate federated management architecture — not a standard configuration out of the box.
Day-2 Operational Reality
The platform decision you make on day one becomes your operational inheritance on day 365. These are the day-2 pain points that surface after the implementation team leaves.
Upgrade blast radius. Rubrik’s SaaS model means Rubrik manages upgrade cadence — which removes upgrade coordination overhead but also removes your control over timing. Cohesity upgrades are self-managed, which means full control over scheduling and sequencing, and full ownership of any upgrade-related incidents.
Support model. Rubrik’s SaaS architecture means vendor-driven support with direct visibility into your control plane. Cohesity’s on-prem model means your infrastructure team owns first-line troubleshooting. Neither is inherently better — one fits a team that wants vendor accountability, the other fits a team that prefers operational autonomy.
Policy drift across sites. Rubrik’s centralized policy engine makes policy drift structurally difficult — a policy change propagates everywhere by design. Cohesity’s distributed model requires explicit replication of policy changes across clusters, which introduces drift risk in environments without rigorous change management.
Troubleshooting complexity. Cohesity’s distributed architecture means failure diagnosis can require investigation across multiple cluster nodes and replication relationships. Rubrik’s centralized control plane provides a single pane of glass for diagnosis — at the cost of requiring that pane to be cloud-reachable.
Team skill requirements. Rubrik optimizes for operational simplicity — the platform is designed to be manageable without deep distributed systems expertise. Cohesity rewards teams that already operate distributed infrastructure and can extend that capability into data management.
Cost Doesn’t Come From Licensing — It Comes From Architecture
TCO comparisons that start and end with licensing miss the architectural cost drivers that compound over time.
Licensing model. Rubrik prices on a subscription basis tied to protected data capacity — predictable and scalable, but with costs that grow linearly with data under protection. Cohesity’s model includes both software licensing and hardware for on-prem deployments, with cloud tier options available. Upfront capital requirements differ significantly depending on deployment model.
Infrastructure footprint growth. Cohesity’s node-based scaling model means capacity growth requires hardware investment. Each expansion cycle is a procurement event. Rubrik’s cloud-tier architecture can absorb capacity growth without corresponding hardware procurement — at the cost of cloud infrastructure dependency and potential egress exposure.
Cloud dependency and egress. Rubrik’s SaaS control plane and cloud-tier integration introduce egress as a variable cost that scales with recovery operations, replication volume, and data retrieval frequency. In high-churn environments or during large-scale recovery events, egress can become a significant unmodeled cost driver. The cloud egress cost architecture is worth mapping explicitly before committing to a cloud-tier recovery model.
Operational cost. Cohesity’s distributed model requires ongoing operational investment — engineering time for cluster management, upgrade coordination, and multi-site policy governance. That cost doesn’t appear in the licensing comparison but shows up in headcount requirements. Rubrik’s SaaS model shifts that operational cost to the vendor — which has a real dollar value that belongs in the TCO calculation.
Overprovisioning risk. Cohesity’s hardware-based scaling creates overprovisioning risk if growth projections are wrong. Rubrik’s subscription model adjusts to actual usage — but capacity forecasting errors in a SaaS model translate to contract misalignment rather than stranded hardware.
Ransomware Reality Check: Recovery Model Matters More Than Backup Model
Both platforms protect backup data. The architectural question is what happens when the attack has already succeeded — and you need to recover from a position of zero trust in your production environment. The full recovery system design is covered in the ransomware backup architecture post, but the platform-specific implications are worth addressing directly.
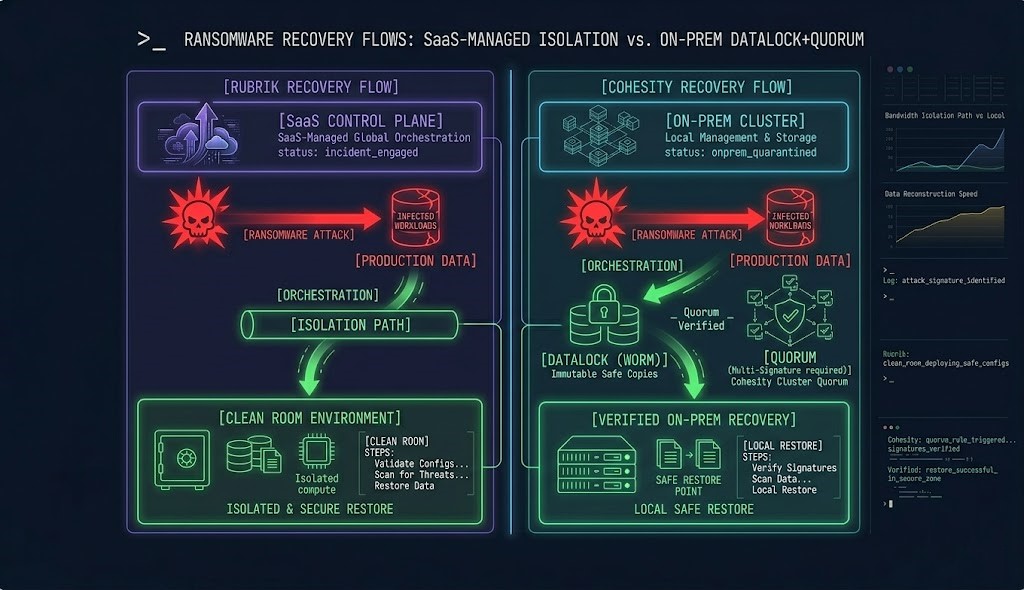
Clean room capabilities. Rubrik’s Security Cloud provides isolated recovery environments that operate outside the production identity plane. Recovery orchestration runs from the SaaS control plane, which is architecturally separated from a compromised on-prem environment. If your production Active Directory is owned, Rubrik’s control plane remains reachable and operable. That separation is the architectural value of the SaaS model under adversarial conditions.
Immutability approach. Cohesity’s DataLock implements WORM locking at the software layer within SpanFS with time-drift protection — the internal monotonic clock resists NTP manipulation attacks. The Quorum feature requires multi-person authorization for any operation that would modify or delete protected data, directly addressing insider threat and credential compromise scenarios. That governance model is a significant differentiator for environments with elevated insider threat exposure.
Recovery orchestration. Rubrik orchestrates recovery from the cloud control plane — recovery workflow execution doesn’t depend on on-prem infrastructure that may be compromised or unavailable. Cohesity orchestrates from within the cluster — recovery capability is self-contained and doesn’t require external reachability, but the cluster itself must be intact and accessible for recovery to proceed.
Identity isolation. If your recovery environment shares an identity plane with your production environment, neither platform fully solves the problem. The logic-gapping architecture covers identity isolation requirements that apply regardless of which backup platform you operate.
The Decision Framework
This isn’t a feature matrix. It’s a constraint map. Run your environment against these conditions — not a vendor checklist.
- [+] You want a SaaS operational model and accept cloud control plane dependency in exchange for operational simplicity
- [+] Your environment is cloud-adjacent and recovery workflows that touch cloud infrastructure are acceptable or preferred
- [+] Your ops team is not sized to manage distributed infrastructure and needs a platform that stays manageable as the environment grows
- [+] Vendor-managed upgrades and support visibility are preferable to operational autonomy
- [+] You need clean room recovery capabilities that operate independently of a potentially compromised on-prem environment
- [+] You operate at significant on-prem scale and need a platform whose control plane doesn’t require cloud reachability
- [+] Regulatory or sovereignty requirements prohibit SaaS control plane dependencies
- [+] You have a team with distributed infrastructure management capability and want full operational autonomy over upgrade cadence and cluster governance
- [+] The Quorum-based multi-person authorization model for immutability governance matches your insider threat posture
- [+] Your site count is manageable and won’t outpace your team’s capacity to operate distributed cluster relationships
Architect’s Verdict
Most mid-sized teams will underestimate the operational overhead that comes with Cohesity at scale. Not because the platform is poorly designed — it isn’t — but because distributed infrastructure management is a skill set that doesn’t transfer automatically from previous backup platform experience. Teams that don’t already operate distributed systems at scale should default to Rubrik unless they have a specific architectural reason not to.
That specific reason usually looks like one of three things: a sovereignty requirement that prohibits SaaS control plane dependency, a regulatory mandate that requires fully on-prem governance, or an environment with strong existing distributed infrastructure capability where Cohesity’s model extends naturally from what the team already manages.
If none of those apply, Rubrik’s operational model will age better in most environments — not because it’s technically superior in every dimension, but because operational simplicity compounds over time the same way operational debt does.
Build to what your team can actually operate at 3am during a ransomware incident. That’s the constraint that matters most.
For the full backup architecture decision space — immutability design, recovery system patterns, and platform selection for sovereign environments — the Data Protection Architecture pillar maps the complete framework. If you’re building or stress-testing your recovery architecture from the ground up, the Data Protection & Resiliency Learning Path is the sequenced reading order.
If this comparison surfaces the platform decision you’re working through, the Rubrik vs Cohesity: The Enterprise Decision Framework covers the operating model test in full — the structured framework for mapping your specific environment constraints against the architecture that holds at your scale.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session