Your CI-CD Pipeline Is Your Real Infrastructure Control Plane
Terraform defines desired state. Kubernetes reconciles workload state. Cloud consoles expose state. None of those systems decides whether infrastructure state is allowed to change. The ci-cd control plane does — or more precisely, the CI-CD pipeline is the only system in most environments that can hold that authority. That distinction — between storing state and having authority over state change — is the one most modern infrastructure & IaC teams haven’t made explicitly. It’s the gap that explains where drift originates, why security posture degrades without a visible trigger, and why “we have IaC” and “we have control” are not the same statement.
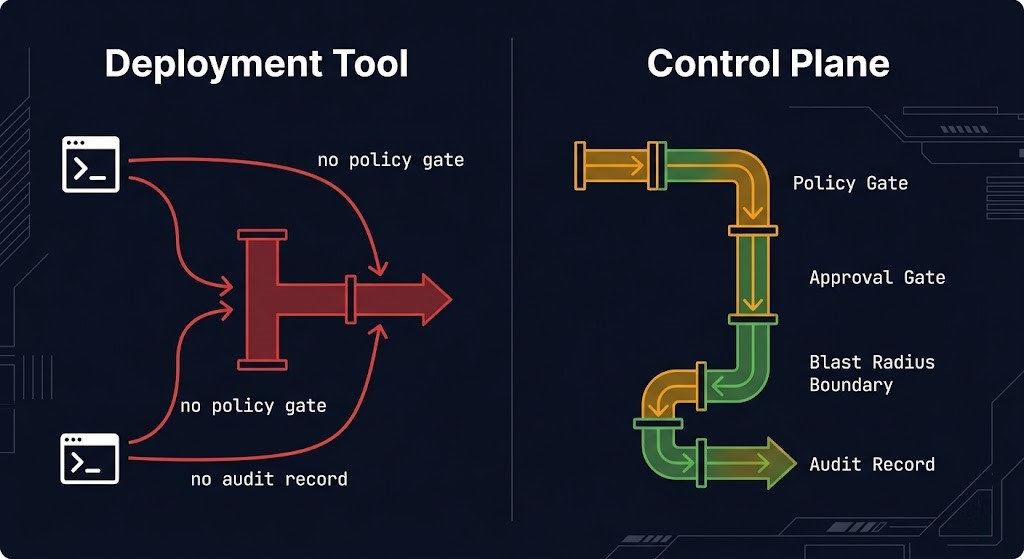
Automation is not authority. A pipeline that automates deployment is not automatically a ci-cd control plane. It becomes one when infrastructure cannot change without it. Most pipelines are on the wrong side of that line — fast, convenient, and bypassable by anyone with cloud console access or a local Terraform install. That is a deployment tool with an opt-in usage policy, not a control plane.
What a Control Plane Actually Is
A control plane is not the system that stores state. It is the system that has authority over state change.
That definition changes the answer to a question most infrastructure teams think they’ve already answered. Terraform manages state, but apply authority belongs to whoever runs it — a developer’s local terminal, a shared CI runner, a manually triggered workflow. The authority is in the hands holding the keyboard, not in the tool. Kubernetes has genuine reconciliation authority over workload state within the cluster, but it has no authority over the infrastructure beneath it — the node pool, the VPC, the security groups, the IAM roles that workload state depends on. Google’s May 2026 control plane boundary shift is the clearest recent illustration of this: when the managed control plane moves, every assumption about where cluster authority ends gets re-examined. The cloud console has no authority at all in the architectural sense: it exposes every possible change to anyone with sufficient IAM permissions, enforces no policy, applies no approval gate, and produces an audit log that records what happened without recording whether it was supposed to.
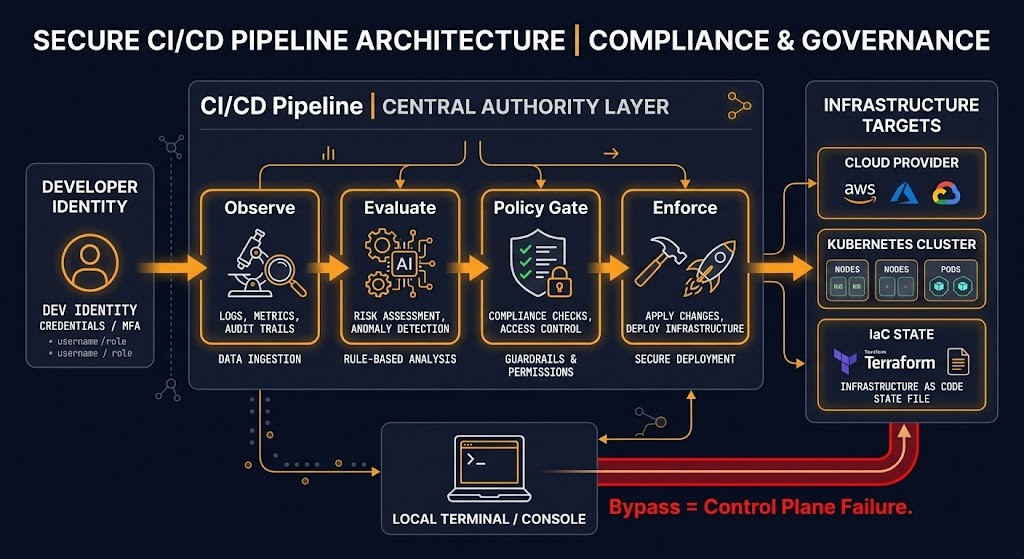
The CI-CD pipeline is the only system in most environments positioned to hold genuine authority over state change — because it is the only system that can be designed as the mandatory path for every infrastructure change, with policy enforcement, approval gates, blast radius boundaries, and a complete audit record connecting change to intent. Whether it has been designed as a true ci-cd control plane is a different question. Most haven’t.
What a CI-CD Control Plane Actually Does
Four functions define a control plane. The question for any given system is which of those four it actually performs — and whether it performs them with authority or just with access.
| Function | Terraform alone | Kubernetes alone | CI/CD pipeline |
|---|---|---|---|
| Observes current state | Partial — declared state + provider read, not authoritative observation | Yes — cluster state via etcd | Yes — if designed for drift detection and audit |
| Evaluates desired vs current | Yes — plan | Yes — reconciliation loop | Yes — pre-flight and policy checks |
| Enforces delta | Yes — apply | Yes — controller | Yes — pipeline execution |
| Gates who has authority to trigger enforcement | No | No | Yes — if designed for it |
Terraform’s honest position is clear in that table. It was never designed to be the authority over who can change what and when — it was designed to translate desired state declarations into provider API calls reliably. That applies equally to Terraform and OpenTofu — the toolchain choice doesn’t change what the tool is. That is a genuinely useful thing. It is not a control plane. Kubernetes is closer: it has a reconciliation loop that continuously evaluates and enforces desired state for workloads. But its authority ends at the cluster boundary. The infrastructure layer beneath it is outside its reconciliation scope.
The pipeline’s fourth row is the one that matters. Gating who has authority to trigger enforcement is what separates a deployment tool from a control plane. Terraform and Kubernetes don’t do this. A well-designed CI-CD pipeline does — and it is the layer where platform engineering architecture either holds together or falls apart, because the pipeline is where the platform’s ownership model is enforced or abandoned.
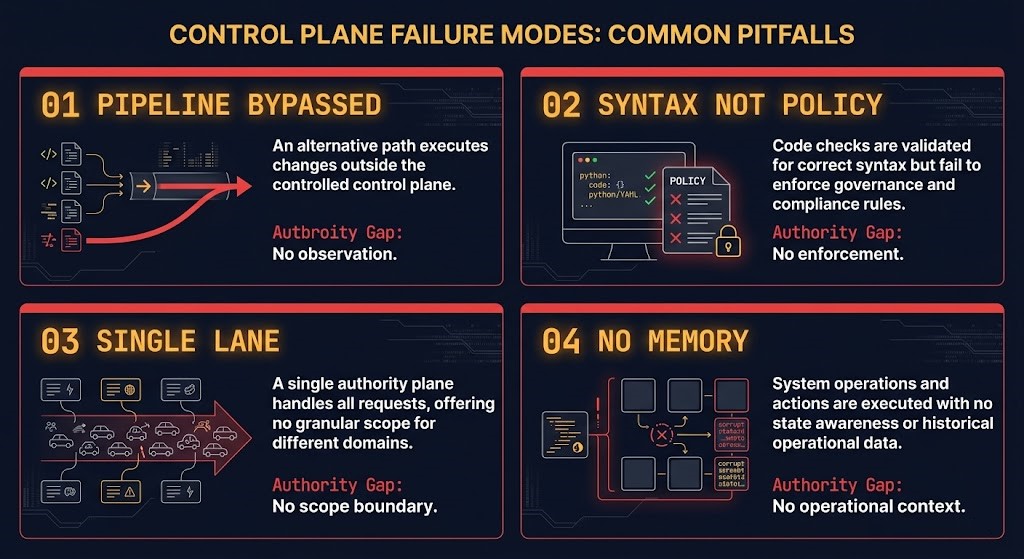
Four Ways Pipelines Fail as Control Planes
The failures are not exotic. They are the defaults — the way pipelines are configured when nobody has explicitly designed them as a ci-cd control plane.
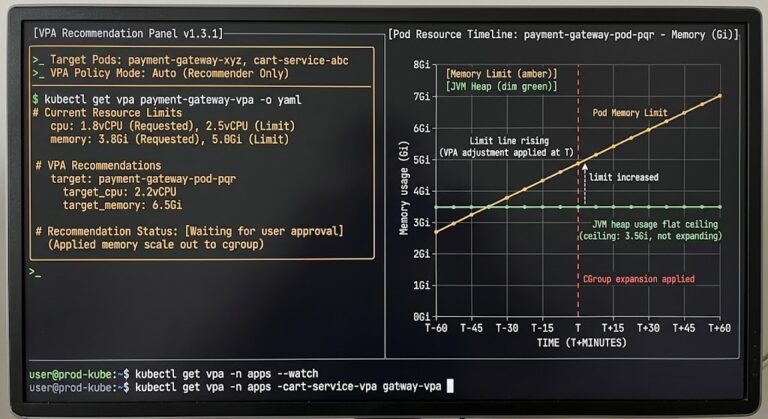
01 — PIPELINE IS BYPASSED
Console changes, terraform apply from a local machine, kubectl exec into a production pod — every manual change is a control plane failure. The pipeline didn’t observe it, didn’t evaluate it against policy, and didn’t create an audit record connecting the change to intent. The next pipeline run now operates against state it doesn’t fully know. Drift doesn’t originate from incorrect IaC. It originates from changes the pipeline never saw.
02 — PIPELINE ENFORCES SYNTAX, NOT POLICY
A pipeline that validates HCL, runs terraform plan, and gates on a clean output is a linter with deployment privileges — not a control plane. A control plane enforces policy: no public IPs in regulated environments, required cost center tagging, approved image registries, quota constraints per team. Without policy at the gate, the IaC can be syntactically correct and architecturally wrong simultaneously.
03 — PIPELINE IS A SINGLE LANE
One pipeline, no environment promotion gates, no approval workflow between dev and production, no blast radius containment. A bad merge or a pipeline credential compromise affects every environment simultaneously — the control plane has no scope boundaries. Genuine control planes have redundancy and explicit boundary enforcement. A single lane is a single point of failure for the entire infrastructure change process.
04 — PIPELINE HAS NO MEMORY
Most pipelines are stateless executors. They know what was deployed, when, and by whom. They don’t know what exception was approved, what policy was waived, what dependency was already degraded when the last change ran, or why the previous rollback happened. A control plane without operational memory executes state transitions without context — and the audit log is long but useless for post-incident investigation because it records events without recording intent.
The detection and correction patterns for failure #1 are in Detecting Manual Console Drift in Terraform. The policy-as-code patterns for failure #2 are in Deterministic IaC: Terraform Policy as Code.
⚠ COMMON MISTAKE
A pipeline that can be bypassed isn’t a control plane. It’s a deployment tool with an opt-in usage policy.
Designing the Pipeline as the Authority
Four requirements to build a genuine ci-cd control plane. None require a specific toolchain. All require an explicit architectural decision.
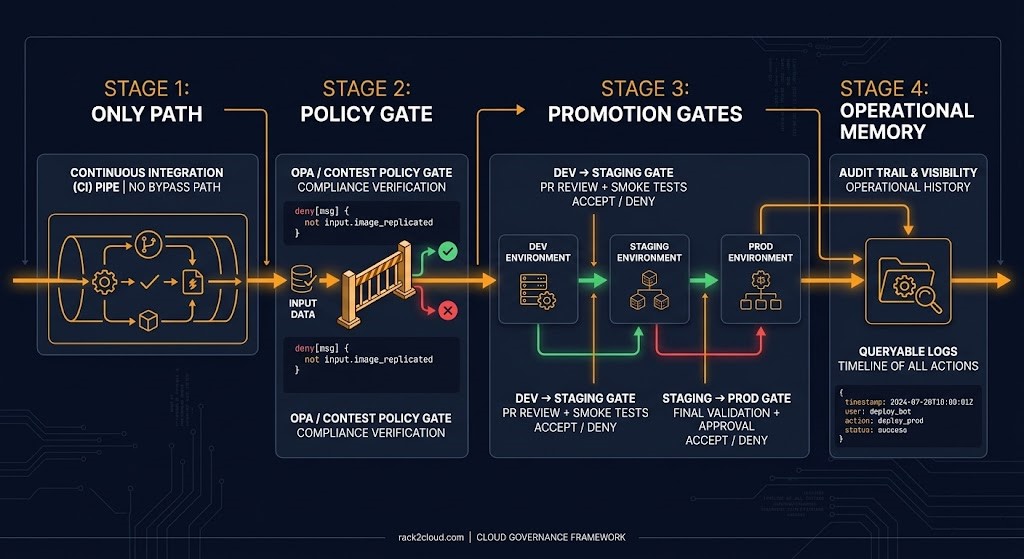
FOUR REQUIREMENTS FOR PIPELINE AUTHORITY
- Pipeline-as-the-only-path — including break-glass. Every infrastructure change goes through the pipeline. Break-glass is not an exception to the control plane — it is a controlled path with elevated requirements: a separate approval tier, a scoped credential set, and automatic incident logging. Emergencies require more rigorous tracking, not less.
- Policy at the gate, not at the dashboard. OPA / Conftest, Sentinel, or Checkov runs before apply as a blocking step. The pipeline rejects non-compliant changes before they reach any environment. A monitor records what happened. A gate determines what is allowed to happen.
- Environment promotion with explicit gates. Dev → staging → production is not automatic. Each promotion has its own approval requirement, its own policy check, and its own blast radius boundary. A change that breaks dev does not reach production until something explicitly promotes it.
- Operational memory built in. Pipeline execution context is stored and queryable: what changed, who approved it, what policy checks passed, what exceptions were granted. This is the layer that makes post-incident investigation possible and makes the audit trail meaningful rather than just long.
The common failure across all four requirements is treating them as independent configuration decisions rather than a single architectural commitment. A pipeline with policy gates but no promotion boundaries is still a single lane. A pipeline with operational memory but no mandatory path still has a bypass problem. The ci-cd control plane is only as strong as its weakest gate — and in most environments, that weakest gate is the one that was never built.
The Control Plane Shift: Infrastructure Decisions 2026 post frames the broader shift in how infrastructure authority is expressed — policy-as-code at the pipeline layer is one of its primary expressions. The GitOps for bare metal post extends this to physical infrastructure — when even hardware provisioning runs through the pipeline, the authority model is complete. For the state management and drift detection tooling side, see Terraform Infrastructure as State: Drift Management.
The Highest-Privilege System You’re Not Treating That Way
Most environments treat the cloud account as the highest-privilege boundary in the infrastructure stack. It usually isn’t. The CI-CD system is.
The pipeline holds credentials to every cloud provider account, every Kubernetes cluster, every deployment target simultaneously. It can mutate every environment it’s connected to. It is reachable from developer identity — the same identities that access source control, open pull requests, and trigger workflow runs. And it is frequently governed less carefully than the production environment it manages.
THE CI/CD CREDENTIAL SURFACE
- Secrets stored as environment variables rather than federated through short-lived tokens
- Service account credentials that don’t rotate and aren’t scoped per environment
- Pipeline configurations that any repository contributor can modify
- Audit logging absent on failed runs and bypassed gates — the events that matter most
A compromised CI-CD system is not a compromised deployment tool — it is a compromised control plane with credentials to the entire infrastructure estate. OIDC federation over stored long-lived credentials eliminates the static secret surface entirely. Least-privilege service accounts scoped per environment limit the blast radius of any single credential compromise. The governance patterns at the CLI and control layer are in CLI Control Plane Governance, and the Kubernetes-specific credential surface is covered in Kubernetes LLM Security Boundary.
DIAGNOSTIC QUESTION
“Is your CI/CD system governed to the same standard as the production environment it can modify?”
Architect’s Verdict
The teams treating IaC tooling as the infrastructure control plane have correctly identified where state is managed and misidentified where authority lives. Terraform does not decide whether a change is allowed — it executes changes that someone decided to run. Kubernetes does not decide whether the infrastructure beneath it can be modified — its reconciliation loop operates on workload state, not the infrastructure layer that workload state depends on. The ci-cd control plane is where infrastructure change authority actually lives, or where it should live. In most environments it lives nowhere in particular, which is how drift accumulates, how blast radius grows without a visible trigger, and how security posture degrades without a specific incident to point to.
The underlying problem is that most pipelines were built as deployment automation and inherited control plane responsibilities they were never designed to carry. The authority assumption happened implicitly: the pipeline runs changes, so the pipeline must be in charge. But a system that can be bypassed by anyone with console access, enforces no policy beyond syntax validation, retains no operational memory of the changes it has executed, and is governed less carefully than the environments it manages is not a control plane. It is a convenient path that confident engineers occasionally use and that anyone with sufficient access can walk around.
Automation is not authority. The pipeline becomes a control plane the day infrastructure cannot change without it.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session