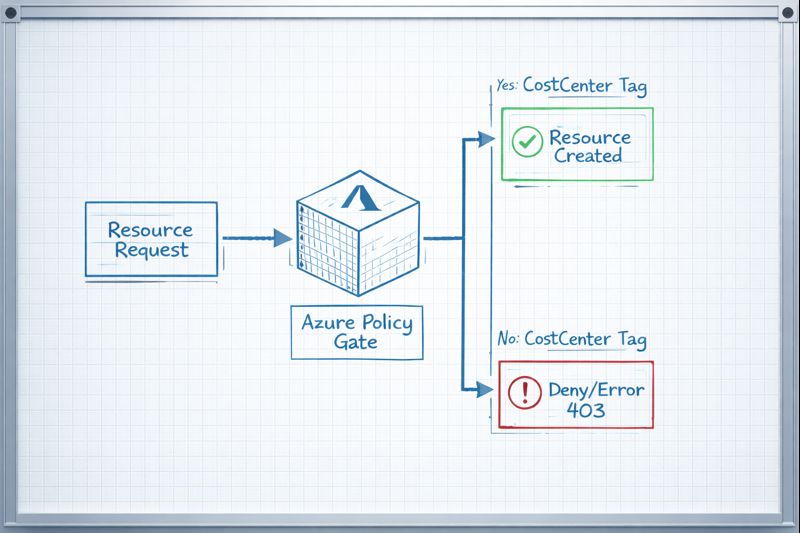
Stop the Bleed: Azure Policy to Enforce ‘CostCenter’ Tags
Azure Policy enforce CostCenter tag is the single control that separates a managed cloud estate from a sponsored black hole. I’ve spent too many Sunday nights staring at an $80k Azure bill, trying to figure out which “Dev Test” environment grew a pair of legs and started running P3v3 instances. If you can’t attribute a resource to a CostCenter, you aren’t managing a cloud — you’re writing blank checks to a cost center that doesn’t exist in your books.
Without a mandatory tag, your FinOps data is garbage. The Azure Untagged Resources Script tells you what’s already broken. This policy is what prevents it from happening again.
The Solution: JSON Policy Definition
Copy this into the Azure Portal or your Terraform azurerm_policy_definition block. This specific logic checks for the existence of the key and denies the deployment if it’s absent — not just empty, absent. The distinction matters for resources that pass an empty tag object through.
JSON
{
"properties": {
"displayName": "Enforce CostCenter Tag",
"policyType": "Custom",
"mode": "Indexed",
"description": "Denies the creation of resources if the 'CostCenter' tag is missing.",
"parameters": {},
"policyRule": {
"if": {
"field": "tags['CostCenter']",
"exists": "false"
},
"then": {
"action": "deny"
}
}
}
}
Why mode: Indexed? Indexed mode means the policy only evaluates resource types that support tags and locations. It automatically skips resource types that don’t have a tags schema — which avoids the NoTagsAllowed errors that fire when you run global tag enforcement against sub-resources. This is the exact error covered in Terraform Azure Tagging Error: Policy Deny & Unsupported Resources Fixed.
How to Deploy the Azure Policy Enforce CostCenter Tag
The 60-Second Path:
- Navigate to Policy in the Azure Portal.
- Definitions > + Policy Definition.
- Location: Select your root Management Group — don’t play whack-a-mole with Subscriptions. The governance hierarchy for this decision is in Azure Management Groups vs. Subscriptions: Where Policy Lives.
- Paste the JSON above.
- Assign: Create an Assignment. Set Enforcement Mode to
Enabledonly after running a compliance scan to see who you’re about to break.

Pre-flight checklist before enabling enforcement:
- Run the Azure Untagged Resources Script across all in-scope subscriptions and triage the CSV output.
- Verify all Service Principals used by Terraform or CI/CD pipelines have
CostCenterdefined in their variable blocks. - Set enforcement mode to
DoNotEnforceinitially and run a compliance scan. Review the non-compliant count before switching toEnabled.
Architect’s Note: If you deploy this with
denyon a Monday morning, your Slack will explode with Terraform “403 Forbidden” errors. Ensure your Service Principals have the tags defined in their variables before you pull the trigger.
Day 2 Operations: CapEx vs. OpEx Implications
The Azure Policy enforce CostCenter tag decision isn’t binary — you have three deployment modes with materially different operational profiles.
| Feature | Cost Impact | Operational Effort |
|---|---|---|
| Deny Policy | Reduces OpEx by preventing “Shadow IT” spend. | High — will break legacy CI/CD pipelines. |
| Audit Policy | Zero immediate savings; provides visibility. | Low — passive reporting only. |
| Auto-Remediation | Saves engineer time (OpEx). | Medium — requires Managed Identity setup. |
The phased approach that works in practice: start in Audit mode for two weeks, review the compliance dashboard, remediate brownfield resources using the Azure Untagged Resources Script and manual triage, then flip to Deny. Skipping the audit phase is how you break pipelines on a Monday morning.
Auto-remediation is worth the Managed Identity setup cost for large estates. The policy-based approach to tagging at creation is always cleaner than remediation tasks — as covered in Cloud Cost Is Now an Architectural Constraint, every hour a resource runs untagged is an hour of attribution data that can’t be recovered.
What Happens When Terraform Hits the Policy Gate
When this policy is active and a Terraform deployment runs without the CostCenter tag, the ARM API returns a 403 RequestDisallowedByPolicy. The fix is inline tags on the resource block, not default_tags in the provider — the full explanation with code is in Terraform Azure Tagging Error: Policy Deny & Unsupported Resources Fixed.
For teams managing this policy as code, the OpenTofu Readiness Bridge tool on the Engineering Workbench covers azurerm_policy_definition compatibility between Terraform and OpenTofu.
Architect’s Verdict
Azure Policy enforce CostCenter tag is not optional for any enterprise running more than a handful of subscriptions. The $22k hidden test environment I referenced isn’t an edge case — it’s a predictable outcome of running cloud infrastructure without mandatory attribution.
The sequence is: audit first with the untagged resources script, assign at the Management Group level not the subscription, run in Audit mode for two weeks, then flip to Deny once your pipelines are clean. Done in that order, this policy eliminates the attribution problem permanently. Done out of order, it breaks your Monday morning deployments and generates a week of Slack noise.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session