Exposing Dark Matter: PowerShell Script to Find All Untagged Resources
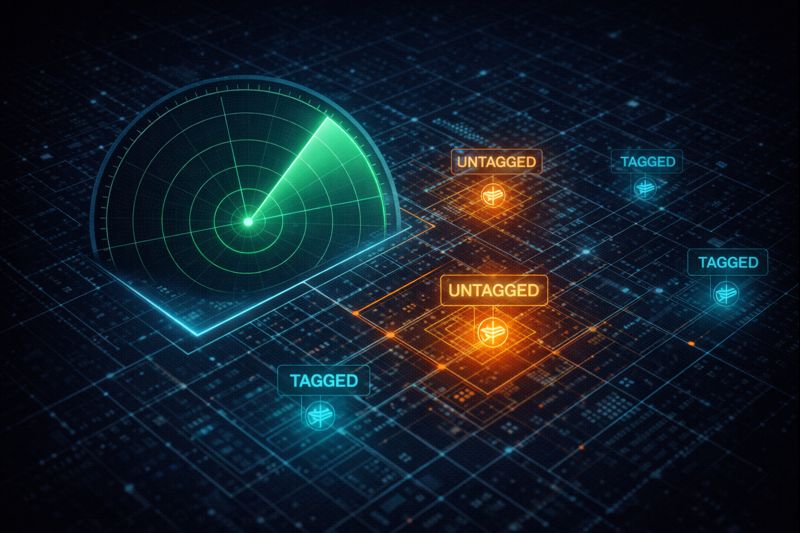
An Azure untagged resources script is the flashlight you need before you go anywhere near enforcement mode. I’ve walked into too many “cloud migrations” where the client thinks they’re running lean, only to find $12k a month in “Dark Matter” — resources floating in the periphery with no owner, no tag, and no purpose. If you don’t have a tag, you don’t exist in the eyes of the finance department, yet you’re still on the invoice.
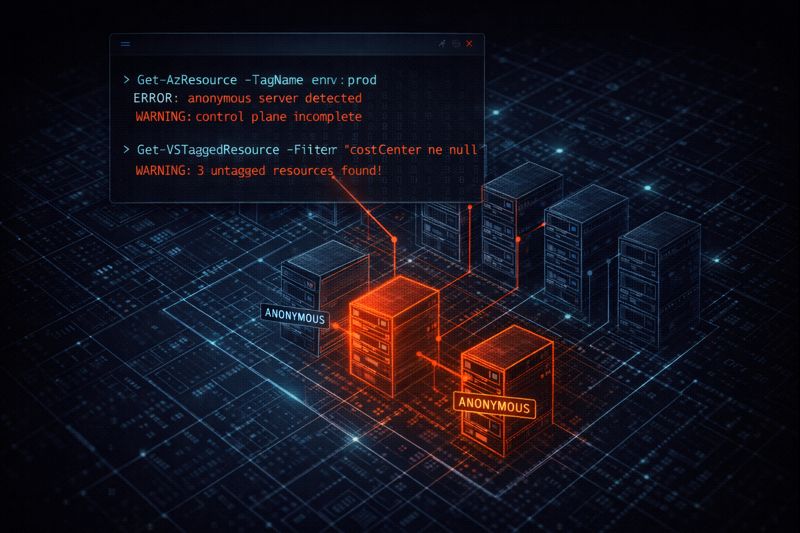
Before you enable Azure Policy in enforcement mode, you need to audit the damage first. Running enforcement against an unaudited estate means policy will block new resources while the existing dark matter keeps billing. This script gives you the full picture before you pull the trigger.
The tagging governance pattern this feeds into is covered in Azure Management Groups vs. Subscriptions: Where Policy Lives — the audit script and the enforcement layer are two steps of the same workflow.
The Azure Untagged Resources Script: The “Dark Matter” Finder
This script is deliberately lightweight. It doesn’t just look for “missing tags” — it looks for resources where the tag object is null or completely empty. The distinction matters: a resource with an empty tag block passes some tooling checks but is still invisible to cost attribution.
PowerShell
# Get all subscriptions you have access to
$subs = Get-AzSubscription
$results = foreach ($sub in $subs) {
Set-AzContext -SubscriptionId $sub.Id -Force | Out-Null
Write-Host "Scanning Subscription: $($sub.Name)" -ForegroundColor Cyan
# Fetch resources where tags are null or empty
Get-AzResource | Where-Object { $_.Tags -eq $null -or $_.Tags.Count -eq 0 } | Select-Object `
@{Name="SubscriptionName"; Expression={$sub.Name}},
Name,
ResourceType,
ResourceGroupName,
Location
}
# Output to GridView for quick inspection or CSV for the boss
$results | Out-GridView
$results | Export-Csv -Path "./UntaggedResources_Jan2026.csv" -NoTypeInformation
Write-Host "Audit Complete. Found $($results.Count) untagged resources." -ForegroundColor Yellow
How to Run
- Open Azure Cloud Shell (PowerShell) or your local terminal.
- If local, ensure you’ve run
Connect-AzAccount. - Copy-paste the block.
- Check the
UntaggedResources_Jan2026.csvfile in your root directory.
Note: The date format in the export filename has been updated from the hardcoded Jan2026 to $(Get-Date -Format 'yyyy-MM') — this makes the script reusable without editing before each run.
Decision Framework: Audit vs. Remediation
Running the Azure untagged resources script is step one. What you do with the output depends on where your estate sits in the governance lifecycle.
| Action | When to use | OpEx Cost | Risk Level |
| Manual Audit (This Script) | Initial cleanup phase / Brownfield. | High (Labor intensive). | Zero. |
| Azure Resource Graph | At scale (>100 subscriptions). | Low. | Zero. |
| Auto-Tagging (Policy) | Day 2 Operations / Greenfileld. | Lowest (Automated). | Medium (Logic errors). |
The Resource Graph path scales beyond what this script handles. For estates running hundreds of subscriptions, the Kusto query approach in Azure Resource Graph Explorer is significantly faster — the Microsoft Docs link in Additional Resources covers the query syntax. For estates still in brownfield cleanup mode, this script is the right first pass before you commit to a policy-based remediation strategy.
The connection to Terraform is direct — if you’re using default_tags in your AzureRM provider and hitting Policy Deny errors on creation, the untagged resources audit tells you what already exists that your new tagging policy will conflict with. See Terraform Azure Tagging Error: Policy Deny & Unsupported Resources Fixed for the fix.
The Financial Reality: The OpEx Trap
Every untagged resource is a leak. Deterministic cloud management requires 100% attribution. If you can’t tell me who owns a Premium SSD v2 disk, that disk should be snapshotted and killed. This is the core principle behind the Infrastructure decisions backed by deterministic tooling.
I once saw a “hidden” testing environment in East US that sat untagged for 14 months. Total cost? $22,000. That’s not a rounding error — that’s a senior engineer’s bonus.
The math scales ugly. At $12k/month in dark matter across a mid-sized enterprise, that’s $144k annually in unattributed spend. Finance can’t challenge a cost center it can’t see, which means the waste compounds quietly until someone runs a script like this one. For the broader FinOps framing, Cloud Cost Is Now an Architectural Constraint covers what attribution failure costs at the organizational level.
Once you have your CSV, the next step is deciding whether to enforce tags via policy at the Management Group level — the full governance hierarchy for that decision lives in Azure Management Groups vs. Subscriptions: Where Policy Lives.
Architect’s Verdict
Run this Azure untagged resources script before you do anything else with Azure Policy enforcement. Brownfield estates are full of resources that will immediately fail enforcement gates — the audit gives you the remediation backlog so you can clean house before policy blocks new deployments.
The workflow is: audit with this script → triage the CSV → apply inline tags to critical resources → enforce at the Management Group level for greenfield going forward. Don’t skip the audit phase. Enforcement without inventory is how you end up blocking your own pipelines.
Additional Resources
Editorial Integrity & Security Protocol
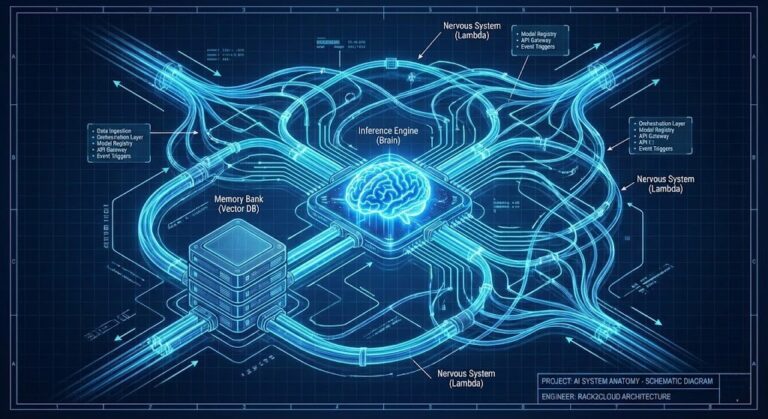
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session