Cost Visibility Is Not Cost Control
Cost visibility tells you what your architecture costs. Cost control determines whether that architecture should have existed in the first place.
These are not the same discipline. Most organizations treat them as if they are — and the FinOps data proves they have been doing so for years without fixing the underlying problem.
The State of FinOps 2026 report found that 98% of organizations are now actively managing AI spend. Tooling investment has increased. Executive ownership has expanded. Reporting has become more granular. And yet organizations without structured cost governance still waste 32–40% of their cloud budgets on idle resources, oversized instances, and structural inefficiencies that dashboards surface but cannot remove.
More visibility. Same waste. That is the signal worth paying attention to.
Visibility Is a Reporting Layer, Not a Control Layer
FinOps tools do several things well. They surface spend. They expose waste. They identify anomalies. They allocate costs across teams and workloads. These are genuinely useful capabilities — the problem is that none of them can prevent the architecture decision that created the bill.
This distinction matters because most cost governance programs are built around observation, not prevention:
- Dashboards show you where money went
- Alerts tell you spend has increased
- Tagging lets you attribute cost to a team
- Optimization recommendations identify inefficiency
- Monthly reviews give you a structured moment to react
Every one of those mechanisms operates after the decision. The commitment — the topology choice, the platform selection, the replication model, the egress dependency — was made upstream. By the time FinOps sees the number, the architecture has already answered the cost question.
Cloud cost is now an architectural constraint — but that constraint only bites when you treat cost as a design variable rather than a reporting output. Visibility is lagging telemetry. It tells you what happened. It does not determine what was allowed to happen.
That distinction is the entire argument.
The Spend Decision Horizon
There is a point in the architecture lifecycle where cost becomes structurally committed and no longer meaningfully adjustable through reporting. Call it the Spend Decision Horizon.
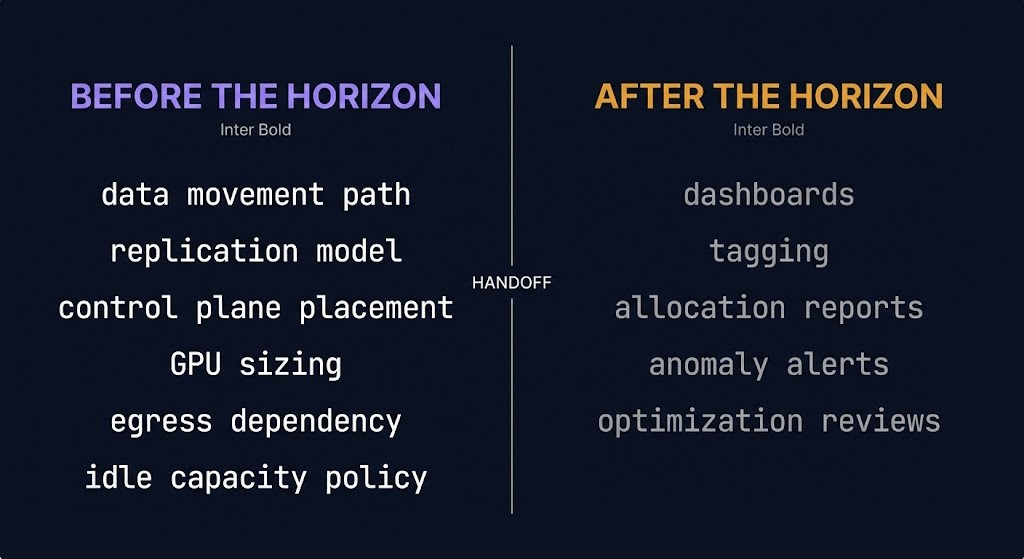
Before that horizon, cost is a design variable. Service topology, data movement paths, replication models, control plane placement, GPU sizing, retention architecture, egress dependencies, idle capacity policy — these decisions are live. The architect is in the room. The cost outcome is still shapeable.
After that horizon, cost is an observation. Dashboards appear. Tagging spreads. Allocation reports get generated. Anomaly alerts fire. Monthly optimization reviews happen. None of those activities change the architecture that produced the number.
The Spend Decision Horizon is not a concept. It is a handoff. Before it, the architect owns cost. After it, FinOps has the receipt.
The reason most cost governance programs underperform is that they are built entirely on the right side of that horizon. They are sophisticated receipt-reading operations with no authority over what gets ordered.
This maps directly to what the exit cost architecture model makes visible for platform and migration decisions: the cost of a choice is not realized when you see the bill. It is committed when you make the architectural decision.
Where Cost Actually Gets Locked In
The Spend Decision Horizon is defined by five commitment points. These are the moments where spend transitions from negotiable to structural.

1. Data path design
How data moves through your architecture determines a significant portion of your recurring cost before a single workload runs. Cross-region reads, replication, egress, archive retrieval — these are not line items you optimize after deployment. They are the outcome of topology decisions made during design. Cloud egress costs are a direct function of architecture, not usage patterns. Once the data path is established, the cost model follows it.
2. Control plane decisions
Always-on orchestration, management overhead, idle infrastructure, and operational tooling all carry a cost that compounds at scale. The control plane shift describes how infrastructure decisions have converged around who owns the execution layer — and that ownership question has a direct cost implication that FinOps tools typically cannot touch. The control plane was placed before FinOps arrived.
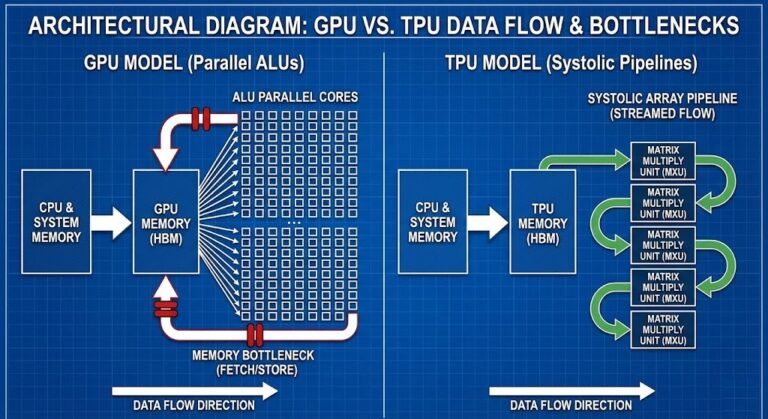
3. Capacity forecasting
Peak-sized clusters, overprovisioned GPU infrastructure, and statically allocated compute are the loudest signals in any cost audit. But the overprovisioning was a forecast decision, not a utilization decision. GPU idle is a capacity forecasting failure, not a scheduler problem — and the same logic applies across all compute layers. You cannot optimize your way out of a demand model that was wrong at provisioning time.
4. Platform abstraction choices
Managed services, proprietary data layers, and convenience abstractions trade operational simplicity for structural spend commitment. Data gravity is the mechanism: once data accumulates around a managed platform, movement cost locks in. Vendor lock-in happens through the networking layer, not through APIs — and by the time the cost is visible in a dashboard, the dependency chain is already load-bearing.
5. Recovery architecture
Standby duplication, replication tax, and restore-path cost are a function of how recovery was designed. Ransomware recovery time is an architecture problem, not a backup product problem — and the same holds for cost. The replication model, the standby footprint, and the recovery tier placement all commit spend at design time. FinOps sees the storage and compute bill. It does not redesign the recovery architecture.
Why FinOps Can See Waste But Not Remove It
This is not a criticism of FinOps. It is a description of its structural position in the decision chain.
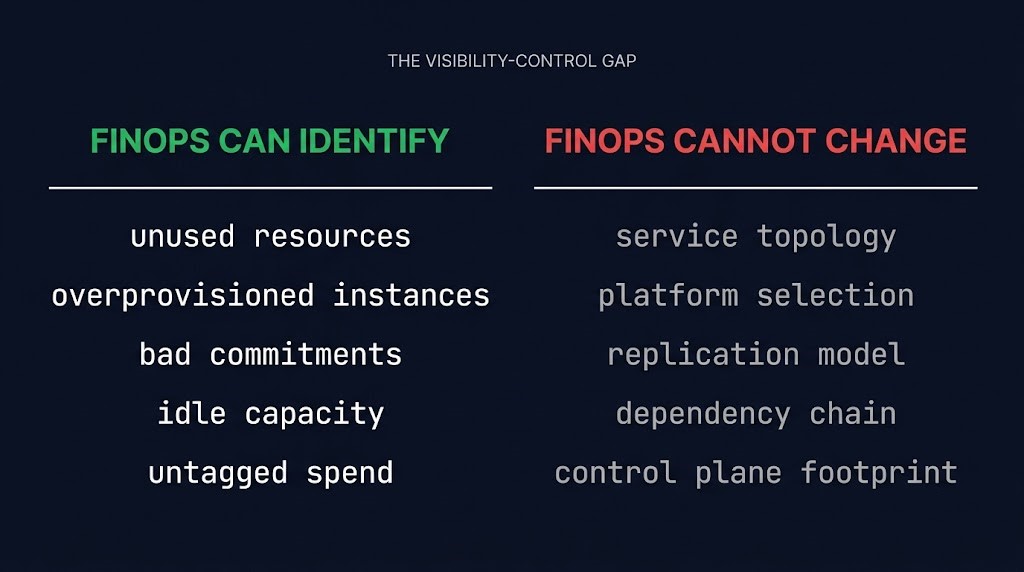
FinOps can identify unused resources, overprovisioned instances, bad commitment purchases, idle capacity, and untagged spend. That visibility is real and valuable. The problem is that identifying the consequence is not the same as owning the cause.
FinOps typically cannot change:
- The service topology
- The platform selection
- The replication model
- The dependency chain
- The control plane footprint
- The egress architecture
Those decisions were made by architects, platform teams, and engineering leads — usually without cost explicitly modeled as a design constraint. AI inference cost is the clearest current example: the decision to use a particular model, route to a particular endpoint, or replicate across a particular region commits spend that observability tooling can surface but not prevent.
There is a pattern that has emerged as FinOps has scaled into larger organizations: shared ownership becoming no ownership. When cost accountability is distributed across engineering, finance, and platform teams without clear authority over architectural decisions, the observation layer grows while the control layer stays frozen. More people watching the dashboard. Nobody with authority to change what the dashboard is measuring.
Cost-aware model routing is one of the few places where control has been pushed back left — where the routing decision itself carries cost logic rather than cost logic being applied after the routing is done. It is a useful model for what pre-horizon control looks like in practice.
Cost Control Starts Before Deployment
The corrective framing is not a checklist. It is a single shift in where cost enters the architecture conversation.
Cost control starts at:
- Architecture review, where topology and data path decisions are still live
- Workload placement, where capacity forecasting is still a design input
- Control plane design, where operational overhead is still negotiable
- Dependency design, where platform abstraction tradeoffs are still explicit
- Demand modeling, where GPU scheduling and capacity shape are still shapeable
Not after the bill arrives.
The teams that consistently achieve meaningful cost efficiency are not the ones with the best dashboards. They are the ones that treat cost as a first-class architectural constraint — alongside reliability, security, and performance — before the first resource is provisioned.
Execution budgets are an example of what this looks like in the AI inference layer: runtime cost limits designed into the system rather than imposed on it from a reporting layer after deployment. The limit is architectural. The visibility is secondary.
Cost visibility is not the problem. Visibility is useful. The problem is treating it as the solution.
Architect’s Verdict
The FinOps stack has never been more sophisticated. Spend is visible. Allocation is granular. Anomalies are caught faster. Optimization recommendations are automated. And organizations are still wasting a third of their cloud budgets on structural decisions that no amount of dashboard sophistication can undo.
Visibility is lagging telemetry. It describes the cost of decisions already made. It cannot reach back across the Spend Decision Horizon and change the topology, the platform choice, the replication model, or the capacity forecast that produced the number.
Cost control is not a reporting discipline. It is an architecture discipline. The five commitment points — data path, control plane, capacity forecasting, platform abstraction, and recovery architecture — are where spend is decided, not observed. Governance programs built entirely after those decisions are sophisticated receipt-reading operations with no authority over what gets ordered.
The Spend Decision Horizon is not a concept. It is a handoff. Before it, the architect owns cost. After it, FinOps has the receipt. The question is not whether your dashboards are good enough. The question is how much of your cost structure was already committed before FinOps was ever in the room.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session