Your Cloud Bill Quietly Increased in 2026 — Here’s Where the Money Is Actually Going

Part 4 of the Rack2Cloud Cloud’2 Cloud Fragility Series
The billing behaviors driving these increases aren’t surprises — they’re the downstream consequences of provider selection decisions made without modeling cost architecture. Egress tiers, inter-AZ charges, IPv4 fees, and managed service premiums are all provider-specific and locked in at selection time. The Cloud Provider Decision Framework: AWS vs Azure vs GCP covers how cost model behavior differs across providers as a first-class axis — so the bill doesn’t explain itself after the fact.
The Boiling Frog Economy
Your cloud bill in 2026 went up. Traffic didn’t. Users didn’t flood in overnight. Your code hasn’t changed much.
Yet your invoice jumped 18%.
For years, cloud companies fought over compute prices. They slashed VM costs to pull you in. But in 2026, they changed the game. Now, it’s not about the “Engine” (Compute) anymore—it’s about the “Road” (Networking and IPs). They stopped charging for the horsepower. Now, they’re charging for every mile you drive.
Forget “Pay for what you use.” Now it’s “Pay for how you build.”
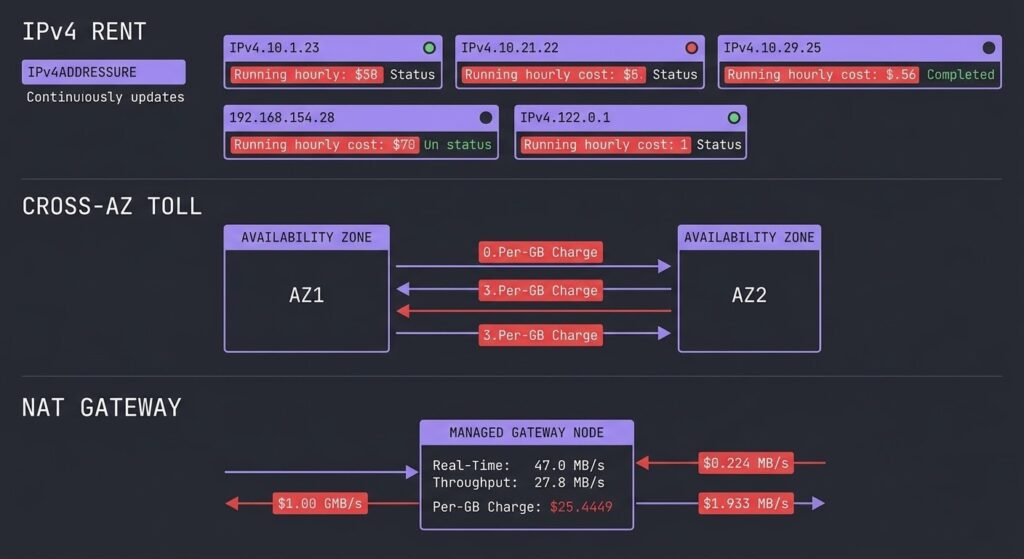
The IPv4 “Legacy Tax”
The sneakiest line on your 2026 bill? The IPv4 Surcharge.
What started as a tiny fee for public IPs turned into a full-on penalty for sticking with the old way of networking. AWS, Google Cloud, Azure—they’re all dinging you for not switching to IPv6.
Here’s the deal: You pay rent by the hour for every public IPv4 address, even if it’s just sitting there doing nothing.
If you run a Kubernetes cluster with a few hundred nodes, or still keep a pile of old load balancers around, this “rent” racks up fast. We’re talking thousands of dollars every month—just for having addresses, not for real value.
If your setup depends on public IPv4 for every node, you’re stuck paying a “Legacy Tax” that does nothing for your performance.
The Cross-AZ “Toll Road”
Next up—the Cross-Zone Data Transfer fees.
Architects love spreading workloads across multiple availability zones for redundancy. “Just stretch the database across three zones!” everyone says.
But now, sending a gigabyte from Zone A to Zone B—even if both are right across town—costs extra. Every chat between microservices in different zones (say, your app in Zone A calling a database in Zone B) rings up a charge.
We’ve seen companies burning through 30% of their EC2 bill just to let their own systems talk to each other across the street.
The NAT Gateway Trap
Trying to dodge public IP fees, you moved your servers to private subnets. Makes sense for security.
But how do those private servers get updates? Managed NAT Gateways.
NAT Gateways are probably the most overpriced service in the cloud. You pay every hour just to have one, and then you get slapped with a per-gigabyte fee for every byte that passes through.
Let’s say your CI/CD pipeline grabs 500GB of Docker images through a NAT Gateway every day. That’s a premium charge on bandwidth you could’ve had for free with a public IP.
The kicker? You’re shelling out extra money to be secure.
Architecture Is the Problem
Your bill didn’t spike because the cloud providers are out to get you. It’s because your architecture got sloppy.
- You stuck with public IPs because switching to IPv6 seemed like a headache.
- You spread workloads across multiple zones without thinking about the traffic because “redundancy is good,” right?
- You used Managed NATs because building your own egress proxy looked like busywork.
In 2026, Lazy Architecture = Expensive Bills.
Stop Guessing. Audit.
You can’t fix what you can’t see. Cloud billing dashboards show you the big numbers — not the leaks. You’ll see “EC2 cost $50,000” but not that $12,000 of it was wasted on IPv4 rent and cross-zone chatter. The cloud cost increase in 2026 is architectural — which means it requires an architectural audit, not a billing dashboard review.
Three things to audit immediately:
IPv4 exposure. Pull every public IP in your account and classify it — load balancer, NAT gateway, EC2 instance, idle. Anything idle is pure waste. Anything on a node that doesn’t need direct inbound connectivity is a candidate for removal. The Real World Egress Calculator models the cost delta between your current IPv4 footprint and a reduced exposure architecture.
Cross-AZ traffic patterns. Enable VPC Flow Logs if they aren’t already running and filter for traffic crossing availability zone boundaries. The volume will surprise you. Service-to-service calls that look like internal traffic on the application layer are billing events at the networking layer. Co-locating frequently communicating services in the same AZ is the architectural fix — not a networking trick.
NAT Gateway throughput. Check your NAT Gateway data processing charges line by line. If your CI/CD pipeline is pulling container images through a NAT Gateway, that’s the first target. S3 Gateway Endpoints are free and eliminate NAT charges for S3 traffic entirely. VPC Interface Endpoints for ECR cut image pull costs dramatically. These are configuration changes, not architectural rewrites.
The Architecture Fix
The cloud cost increase of 2026 is not a pricing problem — it is a design problem. The providers didn’t change what they charge for. They changed what you can no longer avoid paying for if your architecture was built for the 2019 cloud model.
The fix is straightforward in principle and tedious in execution. Reduce public IPv4 exposure to the minimum required — load balancers and NAT gateways only, never individual nodes. Route same-AZ traffic within the same AZ — co-locate services that talk frequently. Replace Managed NAT Gateways with S3 Gateway Endpoints for S3 traffic and Interface Endpoints for AWS service traffic wherever volume justifies the endpoint cost.
None of these changes require a re-architecture of your application. They require a deliberate audit of how traffic moves and a willingness to adjust placement and routing based on what that audit surfaces. The Cloud Cost Is Now an Architectural Constraint post covers the broader FinOps framework for making cost a first-class design input rather than a billing surprise.
The egress cost model is covered in detail in the physics of data egress — the mathematics behind how NAT, cross-AZ, and internet egress charges compound across a typical enterprise architecture. The cross-region egress patterns post covers the specific S3 and VPC peering traps that produce the largest unexpected charges.
Architect’s Verdict
Cloud providers didn’t raise their prices in 2026. They restructured what they charge for — and the architects who haven’t restructured their designs in response are funding the difference. The compute wars are over. Networking is the new margin.
The IPv4 surcharge, the Cross-AZ toll, and the NAT Gateway premium are not bugs in the billing model. They are incentives to build differently — to use IPv6, to keep traffic local, to use native service endpoints instead of routing everything through a managed gateway. The providers are effectively charging a design debt tax. Architectures that were built before these charges existed now pay it every month.
The specific reason most teams haven’t fixed this is not cost awareness — most engineers know the charges exist. It is prioritization. Refactoring egress architecture doesn’t make the application faster or more reliable. It just makes it cheaper. That trade never wins in a sprint planning session until the bill lands. Run the egress audit before the bill forces you to.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session





