The Cloud Bill Is Your Real Org Chart
The meeting starts the same way every quarter. Someone pulls up the cloud bill. The number is higher than last quarter. Six teams are in the room, and somewhere in the line items — usually buried between data transfer charges and a cluster of snapshot storage entries — there is a resource nobody can explain.
It has been on the bill for eighteen months.
Nobody claims it. Platform team assumes it belongs to one of the application teams. The application teams assume it belongs to platform. Networking is certain it is not theirs. FinOps flags it, opens a ticket, and the ticket sits unresolved because there is no team with the authority or the incentive to close it.
That resource is not an anomaly. It is a data point. And your cloud bill org chart — the one nobody in that meeting is reading correctly — is full of them. The cloud bill org chart problem is not a pricing problem. It is an organizational legibility problem.
What the Cloud Bill Is Actually Telling You
The standard framing treats the cloud bill as a pricing problem. If the number is too high, the solution is reserved instances, rightsizing, or a better rate negotiation. These are valid levers, and they will reduce your bill. They will not fix what the bill is measuring.
Every line item that persists without escalation is an ownership signal. The egress charges nobody disputes because both teams assumed the other was responsible. The idle compute that survived three quarterly reviews because the team that provisioned it reorganized six months ago. The snapshot accumulation running at fractions of a cent per gigabyte per month — invisible in isolation, a significant number in aggregate, and owned by no one.
These are not operational oversights. They are audit trails. Your cloud bill is recording every decision made without an owner attached, and every decision that nobody had the authority — or the mandate — to close. It is the most honest org chart on your infrastructure stack in the building, and most organizations are reading it as a pricing document. The cloud bill org chart is the document your architecture reviews never produce — because nobody is asked to draw it.
The Ownership Topology
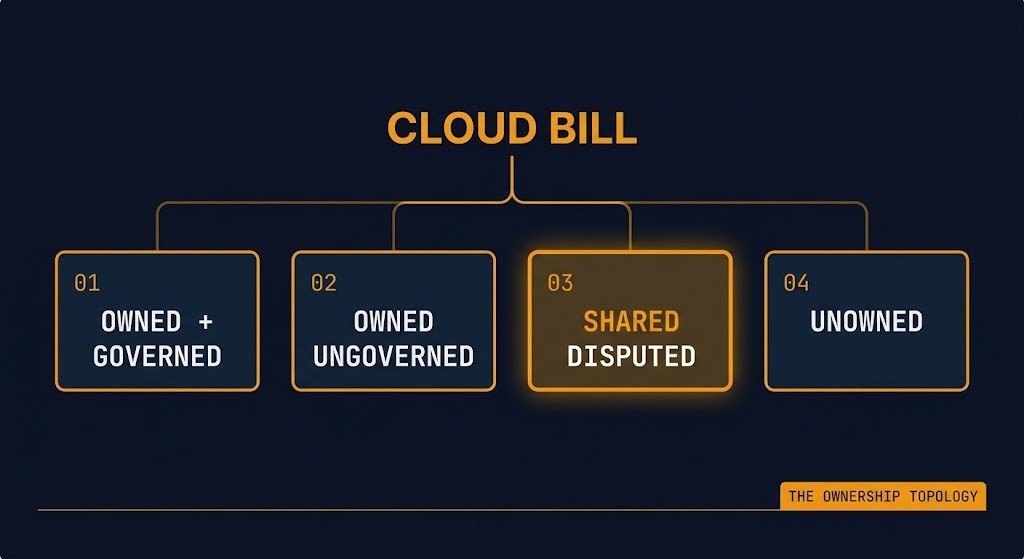
Not all ungoverned spend looks the same. Before you can address the failure, you need a framework for classifying what you are actually looking at. The Ownership Topology is the framework for reading your cloud bill org chart accurately — it identifies four states that every cloud resource falls into.

01 — OWNED AND GOVERNED
Clear owner. Defined lifecycle. Budget authority attached at provisioning time. Change requires authorization. Decommission has a trigger and a team responsible for pulling it.
02 — OWNED BUT UNGOVERNED
A team claims it. Lifecycle discipline does not exist. The resource persists past its useful life because nobody has a decommission mandate or the operational incentive to exercise one. Often the highest-volume category in mature environments.
03 — SHARED BUT DISPUTED
Multiple teams consume it. No team can independently govern it. Platform, networking, security, application owners, and FinOps all partially own it — which means no team truly does. NAT gateways, shared Kubernetes clusters, transit networking, observability stacks, egress routing. Governance requires the authority to act unilaterally. No team has it. The spend is structurally sticky.
04 — UNOWNED
Residual infrastructure with no surviving operational authority. Provisioned by automation. Inherited from a departed engineer. Created during an incident and never reclaimed. The bill never stops running. Nobody escalates because nobody is certain it is theirs to escalate.
The third category — Shared but Disputed — is the most consequential and the least discussed. It is where politically-owned infrastructure lives. When five teams partially consume a resource, the political cost of any governance action falls on whoever moves first. So nobody moves. The resource persists not because anyone decided to keep it, but because the authority structure makes decommissioning more expensive than the bill line itself.
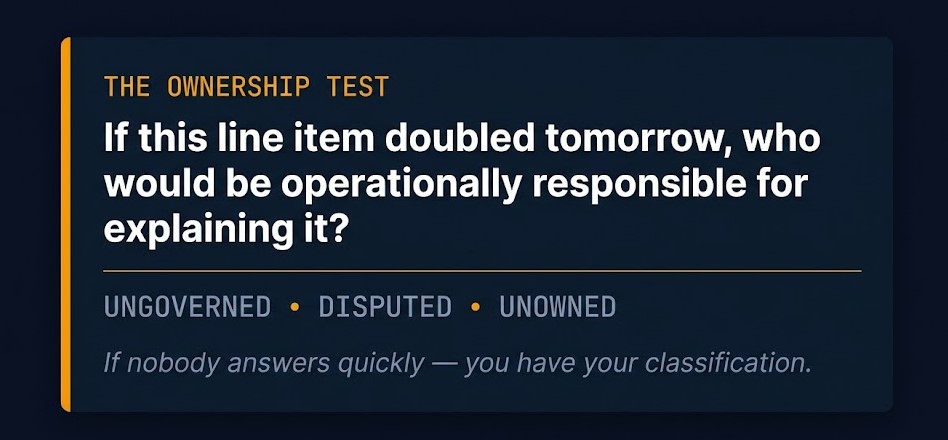
The Ownership Test
Before you read your own bill, you need a single diagnostic question. Not a cost allocation report. Not a tagging dashboard. One question that exposes the authority failure immediately.
THE OWNERSHIP TEST
“If this line item doubled tomorrow, who would be operationally responsible for explaining it?”
If nobody in the room answers quickly and without qualification, the resource is ungoverned, disputed, or effectively unowned. The Ownership Test does not require a FinOps tool to run. It requires a room, a bill, and the willingness to let silence be the answer.
Why Platform Teams Cannot Fix This Alone
FinOps tooling gives you visibility. It does not give you accountability. This is not a product criticism — it is a structural one. Visibility and accountability are different problems requiring different solutions, and most organizations have invested heavily in the first while assuming it would produce the second.
It does not. You can see every untagged resource on your bill today. You cannot force anyone to own it without a governance structure that pre-assigns operational authority at provisioning time — not at billing review time.
Tagging mandates fail for the same reason. A resource tagged owner=platform-team is not governed infrastructure. It is organizational ambiguity serialized into metadata. The tag tells you which team someone thought was responsible at provisioning time. It tells you nothing about whether that team has the lifecycle mandate, the budget authority, or the operational incentive to govern the resource through to decommission. Tagging is a reporting mechanism, not an ownership mechanism. The distinction matters.
The harder organizational truth is this: most enterprises assign responsibility for uptime long before they assign responsibility for lifecycle cost. SLAs get written on day one. Decommission authority gets written never — or gets written into a runbook nobody can find when the original engineer leaves. The cloud bill is documenting the gap between those two timelines at line-item resolution.
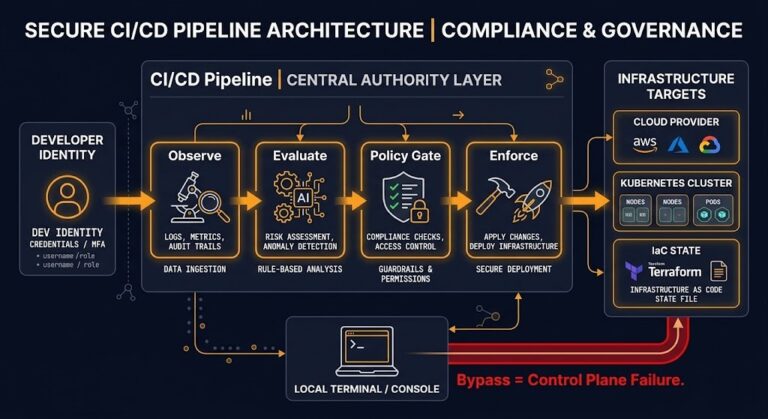
The CI/CD pipeline post makes a parallel argument about change authority — who actually controls what gets deployed versus who is nominally responsible for it. The authority gap in your bill is the same gap, operating at the resource lifecycle layer.
Reading Your Own Bill
Five line-item patterns and what each one reveals about your authority structure. Run the cloud bill org chart test against each of these before your next quarterly review.
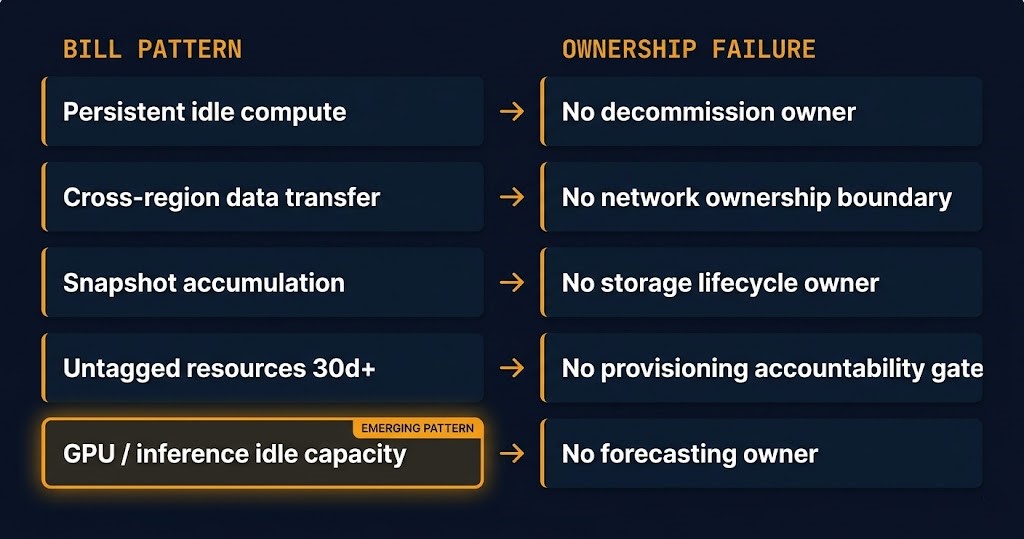
Persistent idle compute signals a decommission ownership gap. The resource was provisioned for a project, the project ended, and nobody had the authority or the mandate to terminate it. It is almost never malicious and almost always structural.
Cross-region data transfer spikes signal a missing network ownership boundary. When teams can provision workloads across regions without a cost ownership handoff, data movement cost accrues to a shared pool that nobody governs. The egress cost framing in the Cost Visibility post covers this at the architecture decision layer.
Snapshot accumulation signals the absence of a storage lifecycle policy owner. Snapshots are provisioned on demand, rarely decommissioned on a schedule, and the cost is granular enough that no single snapshot triggers an escalation. In aggregate, they represent an ungoverned lifecycle across hundreds of resources.
Untagged resources over 30 days signal provisioning without an accountability gate. If a resource can be created without an owner, cost center, and lifecycle class attached at creation time, the governance failure is in the provisioning workflow — not in the bill review.
Persistent GPU reservation or idle inference capacity is the pattern most organizations are building right now and will spend the next two years untangling. GPU scheduling decisions that made sense for training workloads — where burst capacity justifies reservation — do not translate cleanly to inference. Inference endpoints run at fractional utilization on reserved capacity, the reservation was approved by a team that no longer owns the workload, and the forecasting authority was never assigned. The result is Owned but Ungoverned infrastructure at high per-hour cost. AI workloads break traditional FinOps models precisely because the authority structure that governs inference cost was never designed for it.
⚠ THE PATTERN TO WATCH
The most dangerous line item on your bill is not the largest one. It is the line item that has been stable for 18 months and that no single person can explain without convening a meeting. Stability in an ungoverned resource is not a sign of health. It is a sign that the authority failure has become load-bearing.
The Org Chart You Are Not Drawing
Every architecture review worth running asks the same question: who owns this system? Almost none of them ask the question that the cloud bill org chart is answering: who owns the spend lifecycle of this system?
These are not the same question. They have different owners, different timelines, and different failure modes. The first question gets answered at project kickoff, written into a RACI, and filed with the architecture decision record. The second question gets deferred to the first quarterly review, then to the next one, then permanently when the team that provisioned the resource reorganizes.
The Ownership Topology is not a cost reduction framework. It is an accountability framework. Treating it as a cost tool produces tagging mandates and FinOps dashboards. Treating it as an authority framework produces provisioning gates, lifecycle policies, and governance structures that assign ownership before the resource exists — not after the bill arrives.
The cost reduction is the side effect of resolving the authority gap. It is not the goal.
If the VMware exit work happening across the industry has exposed anything at scale, it is that operational ownership does not migrate cleanly with workloads. The same pattern is running in your connected infrastructure boundaries. What the bill is measuring is not spend. It is the residue of every ownership decision your organization deferred.
Architect’s Verdict
Your cloud bill org chart is not a pricing document. It is an organizational signal encoded in line items, and most of the tooling the industry has built to interpret it is optimized for the wrong signal. Visibility without accountability produces better dashboards. It does not produce governed infrastructure.
The Shared but Disputed category is where the real problem lives, and it is the category that no FinOps platform can resolve on its own. Shared infrastructure requires organizational decisions about unilateral governance authority — decisions about which team can act without convening a committee. Those decisions are architectural, not financial. They require the same rigor as your network topology and your identity model, and they need to be made before the resource is provisioned, not after the bill review flags it.
The cloud bill org chart is the most honest representation of your authority structure you have. Most teams are reading it as a cost document. Start reading it as a governance document, and the question stops being “how do we reduce this number” and starts being “what does this number tell us about where authority stopped existing.”
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session