Terraform vs OpenTofu: Cost, Control, and the Post-BSL Decision (2026)
The question isn’t “Terraform vs OpenTofu.”
The real question is whether your infrastructure control plane is owned by a vendor — or governed as open infrastructure. The BSL change in 2023 was the forcing function. But the architectural consequences are only fully visible now.
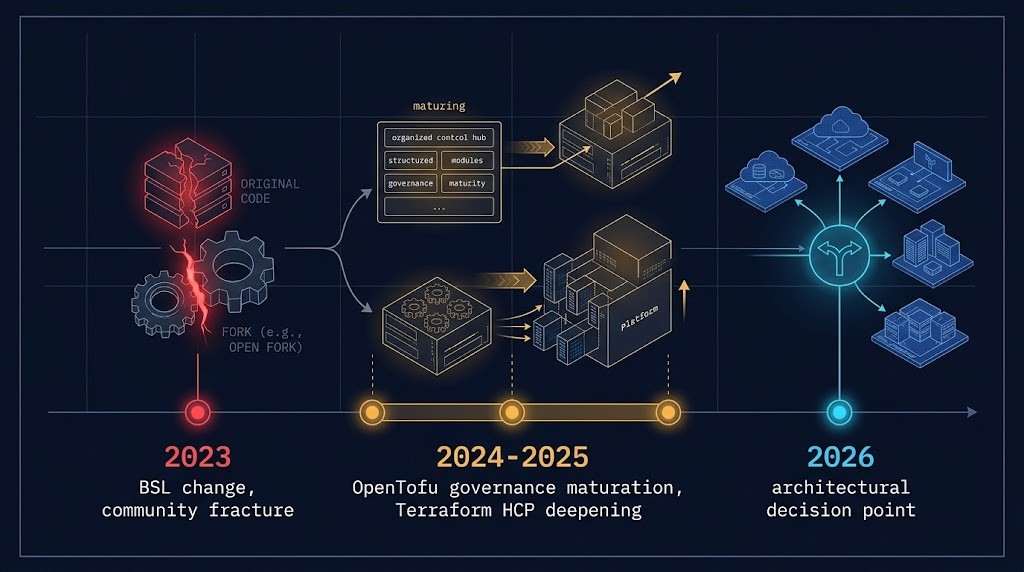
Here’s how the timeline actually played out:
2023: HashiCorp switched Terraform from MPL to BSL. Every infrastructure team debated switching. Most didn’t.
2024–2025: OpenTofu matured under Linux Foundation governance. Terraform deepened its HCP integration. The gap between the two stopped being about features and started being about platform models.
2026: The decision has real weight. Teams that delayed are now facing renewal cycles, growing HCP dependency, or organizational pressure around vendor lock-in. The window for a low-friction switch is narrowing — not closing, but narrowing.
This post is the decision framework.
What Actually Changed — Two Layers
Most posts cover the BSL change. Few cover what happened after.
- MPL → BUSL license restriction
- SaaS competitors directly impacted
- HashiCorp signaled platform consolidation intent
- Community trust fractured
- OpenTofu fork initiated under Linux Foundation
- OpenTofu: governance matured, provider compatibility stabilized, ecosystem confidence grew
- Terraform: deeper HCP integration, Sentinel expansion, increased platform dependency
- IBM acquired HashiCorp — strategic direction now corporate
- TACOS platforms added OpenTofu support
- Enterprise teams started treating OpenTofu as production-viable
OpenTofu in 2026: From Fork to Control Plane
OpenTofu didn’t just replicate Terraform. It removed the licensing constraint from the control plane. That’s a different thing entirely.
Governance. OpenTofu operates under the Linux Foundation — the same governance model that underpins Linux, Kubernetes, and the broader cloud-native ecosystem. This isn’t a community project run by a startup. It’s a foundation-backed, vendor-neutral control plane with a defined contribution model and long-term stability commitment.
Compatibility. As of 2026, OpenTofu maintains strong parity with Terraform’s core HCL syntax, provider protocol, and state file format. The overwhelming majority of existing Terraform configurations migrate without modification. Edge cases exist — primarily around features that have diverged since the fork — but for most organizations the compatibility story is solid.
Ecosystem. The OpenTofu registry mirrors the Terraform provider ecosystem. Major cloud providers (AWS, GCP, Azure), Kubernetes operators, and infrastructure platforms ship providers that work with both tools. TACOS platforms — Spacelift, Scalr, Env0, Atlantis — have all added OpenTofu support. The “ecosystem gap” argument that was valid in 2023 has largely closed.
Enterprise viability. Air-gapped environments, sovereign infrastructure requirements, and organizations with strict OSS license compliance mandates now have a production path that doesn’t require BSL acceptance. For regulated industries and government infrastructure, this is significant.
The OpenTofu Readiness Bridge tool on the Engineering Toolkit can help scope compatibility against your existing Terraform codebase.
Where Terraform Still Leads
Terraform’s advantage is no longer the CLI. It’s the surrounding platform.
Terraform vs OpenTofu: Control Plane Comparison
| Dimension | Terraform | OpenTofu |
|---|---|---|
| License Model | BUSL | MPL 2.0 |
| Governance | HashiCorp / IBM | Linux Foundation |
| Managed Platform | HCP Terraform | TACOS ecosystem |
| Policy Enforcement | Sentinel (mature) | OPA / partner tools |
| Vendor Lock-In | Higher (HCP dependency) | Lower |
| Air-Gap Support | Limited | Strong |
| Enterprise Support | Vendor-backed SLA | Community + partners |
The Switching Cost Nobody Benchmarks
This is the part most teams miss: switching cost is only half the equation. The other half is exit cost — the cost of staying.
Every additional dependency on HCP Terraform, Sentinel, or platform-native workflows increases the cost of leaving later. Lock-in doesn’t arrive all at once. It accumulates — one integration, one policy, one workflow at a time.
The decision isn’t just whether you can switch today. It’s how expensive it becomes if you wait.
Most teams evaluate syntax compatibility. The real cost is execution model disruption.
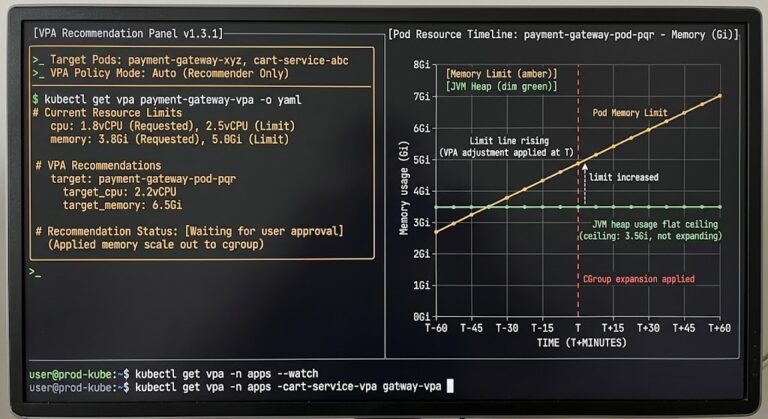
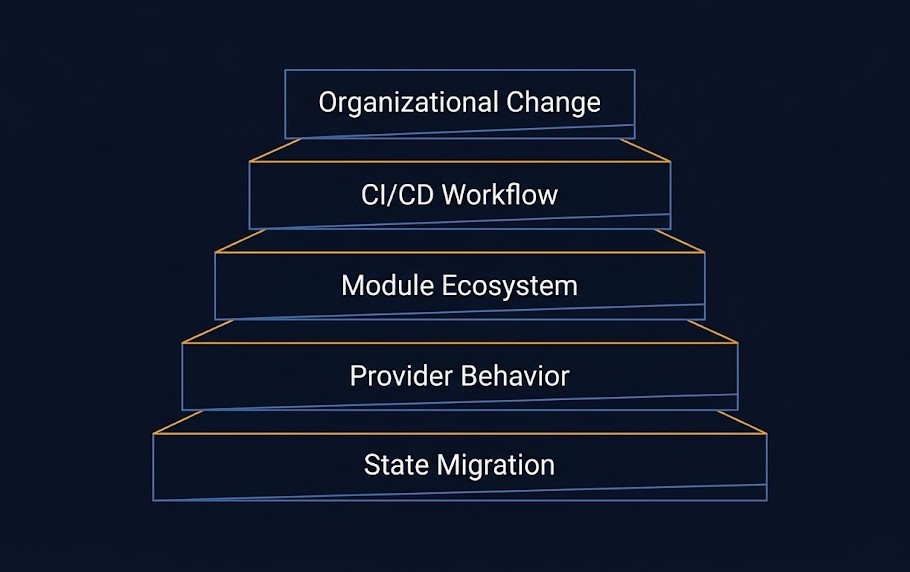
1. State Migration Reality
Your Terraform state files are portable — OpenTofu reads them natively. But state migration isn’t just a file copy. Remote backend configurations, state locking behavior, workspace structures, and drift exposure during the transition window are all real operational risks. For large environments with hundreds of state files across multiple workspaces, the migration itself becomes a project.
The OpenTofu Transition Guide covers the state migration mechanics in detail. The Terraform as State post covers why state is the real control surface — and why that matters during any migration.
2. Provider Behavior
OpenTofu mirrors the Terraform provider registry, but subtle version mismatches exist. Providers that have diverged since the fork, long-tail providers from smaller vendors, and custom internal providers built against Terraform’s plugin SDK may behave differently. Before committing to a migration, audit your provider inventory — not just the major cloud providers, but every provider your codebase references.
The Terraform Feature Lag Tracker surfaces these gaps against your specific provider versions.
3. Module Ecosystem
Private module registries built on Terraform’s registry protocol work with OpenTofu. Public modules from the Terraform Registry are accessible. But if your organization has invested in internal Terraform modules with HCP-specific features — remote runs, Sentinel policy attachments, or workspace-level configuration — those modules require refactoring before they’re OpenTofu-compatible.
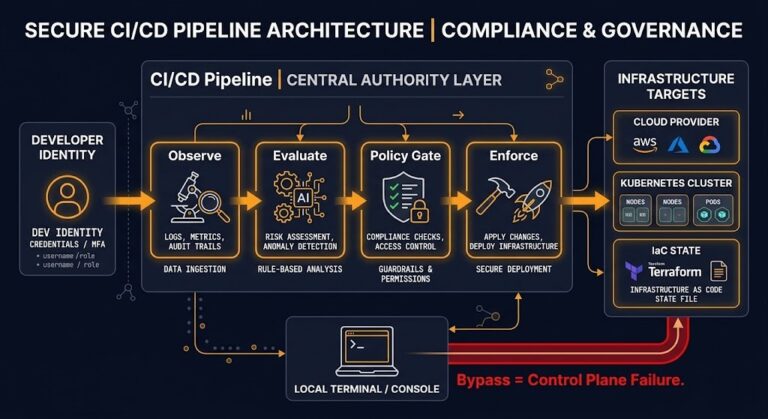
4. Workflow and CI/CD Disruption
This is the most underestimated cost. Your CI/CD pipelines, GitOps workflows, PR automation, and cost estimation tooling are all built around Terraform’s execution model. Switching isn’t a find-and-replace on the binary — it’s an audit of every pipeline stage that touches infrastructure. Policy enforcement changes (Sentinel → OPA or partner tools) require rewriting governance logic. Team muscle memory runs deep.
5. Organizational Change
Infrastructure teams that have operated Terraform for years have embedded operational patterns — how they structure workspaces, how they handle drift, how they manage state, how they onboard new engineers. That institutional knowledge doesn’t transfer automatically. The retraining and adjustment period doesn’t show up on a tooling comparison matrix, but it shows up in your team’s velocity for 3–6 months post-migration.
Who Should Switch — The Decision Framework
- CLI-driven workflows with no HCP Terraform dependency
- No Sentinel policies in production
- Air-gapped or sovereign infrastructure requirements
- Strong organizational need for licensing predictability
- BSL compliance concerns from legal or procurement
- Open governance preference as an architectural principle
- HCP Terraform is central to your execution model
- Sentinel policies are embedded in compliance workflows
- Large internal platform teams built on HashiCorp toolchain
- CDKTF in active use for developer-facing IaC workflows
- Enterprise support contract required by procurement
- Mid-migration orgs with hybrid Terraform + other IaC tooling
- Teams evaluating platform consolidation
- Organizations watching the IBM/HashiCorp strategic direction
- Partial HCP usage without deep Sentinel investment
The Drift Problem — It’s Not About the Tool
Drift is a control problem. Not a tooling problem.
Terraform doesn’t solve drift. OpenTofu doesn’t solve drift. Both are state-based systems with the same fundamental limitation: they know what they deployed, not what actually exists right now in your environment. The moment a human makes a change outside the IaC workflow — a console edit, a hotfix, a manual scaling event — drift begins.
Switching from Terraform to OpenTofu doesn’t change your drift exposure. What changes your drift exposure is your operational discipline around state, your enforcement of IaC-only change workflows, and your detection tooling.
The Configuration Drift post covers the enforcement model. The Infrastructure as a Software Asset post covers why the CI/CD pipeline is the real control surface — not the IaC tool itself.
The tool is not the answer. The governance model is the answer.

Architect’s Verdict
The underlying question isn’t which tool has better syntax or a cleaner CLI. It’s whether you accept HashiCorp’s platform model — or move to open governance.
If your workflows are CLI-driven with no HCP dependency and no Sentinel policies in production — switching is viable and increasingly rational. The compatibility story is solid, the ecosystem has matured, and the licensing argument has only gotten stronger since 2023. Run a provider audit, scope your state migration, and move.
If HCP Terraform is central to your execution model and Sentinel is embedded in your compliance workflows — you are not switching tools. You are replacing a platform. That requires a platform migration plan, not a binary swap. Scope it properly over 12–18 months or don’t start.
If you’re mid-transformation or watching the IBM/HashiCorp strategic direction — run OpenTofu on a parallel workload now. Build the operational knowledge before you need it. The switch will be easier when you’ve already done it once on something non-critical.
This is not a tooling decision. It’s a control plane migration.
The OpenTofu Enterprise Adoption post covers the governance and organizational readiness model in depth. The Terraform & IaC pillar is the full reference for the Modern Infrastructure architecture.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session