Rubrik vs Cohesity: Which Architecture Holds Under Ransomware Pressure?
Rubrik vs Cohesity ransomware protection looks identical on paper — until you simulate an attack.
The marketing story for both Rubrik and Cohesity reads well: immutable snapshots, air-gapped vaults, threat detection, rapid recovery. On paper the gap between them is marginal. Under attack pressure, the architectural differences become operational consequences.
This isn’t a feature comparison. It’s a survival test.
The Attack Model: What We’re Actually Testing
Ransomware operators don’t hit backup platforms the same way they hit production. The modern attack sequence targets the backup layer specifically — because destroying recovery capability is what turns an incident into a ransom negotiation.
The three vectors that matter:
Control plane compromise — attacker gains administrative access to the backup management interface. From here they can alter retention policies, disable immutability, or schedule deletion jobs.
Credential theft — service account or API credentials exfiltrated. Used to authenticate against backup APIs and execute deletion or corruption at scale.
Backup deletion and encryption — direct targeting of backup repositories, snapshots, or replication targets before the primary environment is encrypted.
Evaluate both platforms against these vectors — not deduplication ratios or UI quality. The ransomware backup architecture guide covers the full attack taxonomy if you need the threat model before this comparison makes sense.
Rubrik vs Cohesity Ransomware Protection: Failure Points Compared
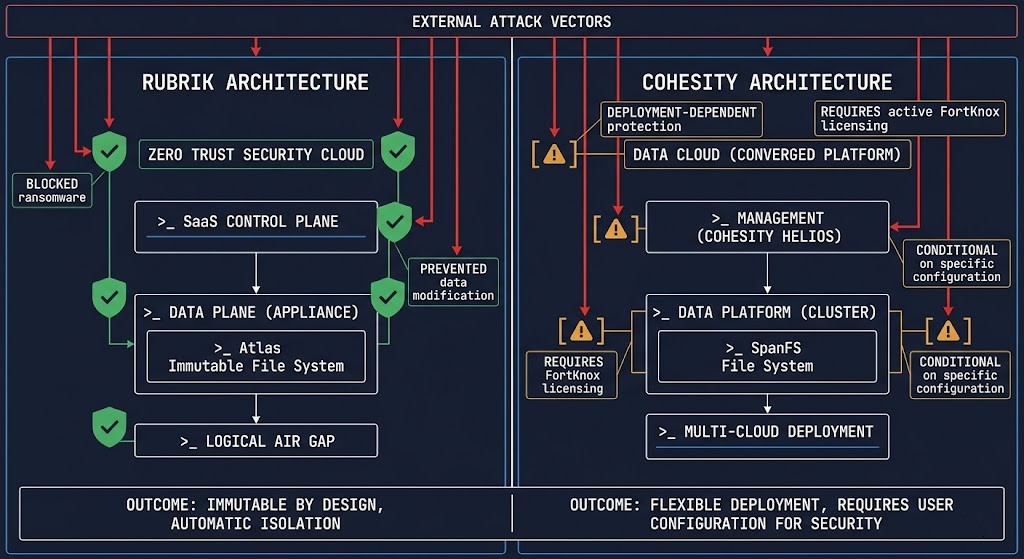
Rubrik
- Backup deletion: Zero Trust Data Management model — even admin credentials cannot delete within the immutability window
- Retention alteration: Policy changes require multi-party authorization — single credential compromise is insufficient
- Clean restore point: Threat hunting scans for indicators before surfacing restore candidates
- Control plane: Cloud-native SaaS control plane — isolated from on-prem compromise by default
Cohesity
- Backup deletion: DataLock immutability holds — but protection depends on correct deployment configuration
- Retention alteration: Quorum-based approval available but requires deliberate setup — not on by default
- Clean restore point: FortKnox provides isolated cloud vault — strongest when pre-configured before incident
- Control plane: On-prem control plane exposure varies by deployment model — hybrid setups require additional hardening
The immutable backups deep dive covers how both platforms implement immutability at the storage layer. The Cohesity FortKnox post covers the isolation architecture in detail — worth reading before forming a conclusion on Cohesity’s vault model.
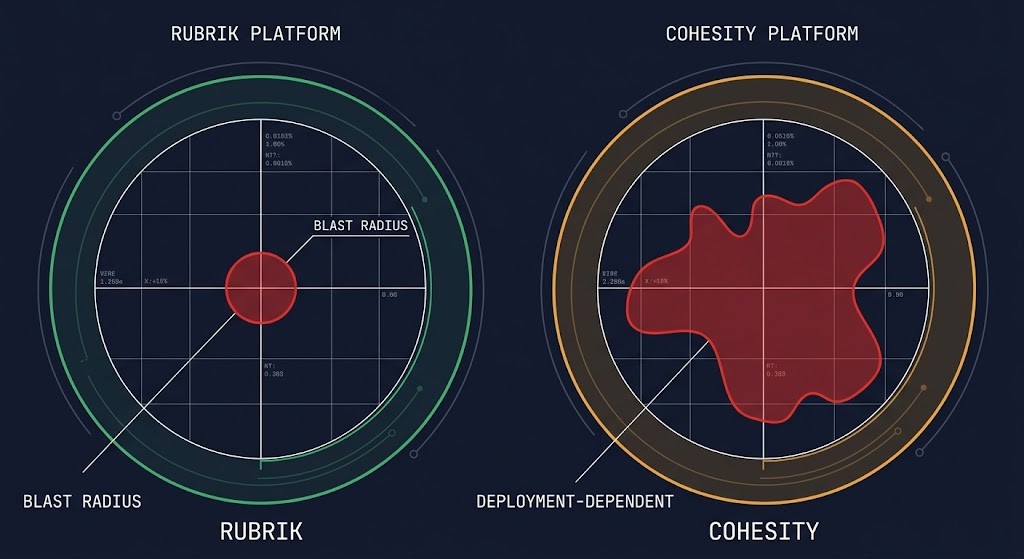
Blast Radius: How Far the Damage Spreads
Blast radius isn’t a vendor metric — it’s an architecture question. How much of your backup estate can a single compromised credential or admin session reach?
Rubrik’s blast radius is structurally bounded. The Zero Trust Data Management model enforces immutability at the data service layer, not the access control layer. Even a fully compromised admin account cannot delete protected snapshots within the retention window. The control plane living in Rubrik’s cloud further limits lateral movement from an on-prem compromise.
Cohesity’s blast radius is deployment-dependent. With FortKnox configured and DataLock enabled with quorum approval, the blast radius is similarly tight. Without those controls deliberately activated, a compromised Cohesity cluster presents a larger attack surface. The platform is capable of strong isolation — but it requires architectural intent to achieve it.
This distinction matters operationally. Rubrik’s security posture is closer to a default-secure model. Cohesity’s security posture is closer to a configurable-secure model. One requires less discipline to maintain. The other offers more flexibility at the cost of that discipline. For recovery metrics under real attack conditions, the ransomware recovery metrics post benchmarks both platforms against RPO/RTO targets. The 3-2-1-1-0 backup rule post covers how isolation architecture maps to the rule framework both vendors claim to support.
Operational Complexity vs Security Tradeoff
The question neither vendor answers clearly in their documentation: can I actually run this safely with the team and processes I have?
Rubrik trades operational simplicity for licensing cost. The platform is opinionated — fewer configuration decisions means fewer configuration mistakes. The security surface is tighter by design. The tradeoff is price and flexibility. Rubrik’s model assumes you want the platform to enforce security constraints rather than configure them yourself.
Cohesity trades flexibility for operational discipline. The platform gives you more control over deployment architecture, replication topology, and integration points. That control is valuable in complex environments — and risky in under-resourced ones. Cohesity misconfigured is meaningfully less secure than Cohesity correctly deployed.
For teams with strong backup operations practices and the cycles to maintain configuration hygiene, Cohesity’s flexibility is a genuine advantage. For teams that need security guarantees without ongoing architectural maintenance, Rubrik’s default-secure model is worth the premium. The data protection learning path covers how to assess operational maturity before making this call.
Architect’s Verdict
Rubrik wins the default-secure argument. If your team doesn’t have the operational cycles to maintain Cohesity’s configuration hygiene, Rubrik’s Zero Trust Data Management model gives you stronger ransomware protection with less ongoing maintenance overhead. The blast radius is structurally smaller, the control plane is harder to reach, and the immutability guarantees don’t depend on getting the deployment right.
Cohesity wins the flexibility argument. FortKnox is a genuinely strong isolation architecture when pre-configured correctly, and the platform’s deployment flexibility serves complex multi-site environments that Rubrik’s more opinionated model doesn’t accommodate as cleanly. The security is there — it just requires architectural intent to activate it.
Neither platform makes the wrong choice easy to recover from. Run the how to calculate true backup costs model before the vendor conversation, and pressure-test whichever platform you select against the three attack vectors above before you need them to hold.
If this comparison is part of a broader platform selection decision, the Rubrik vs Cohesity: The Enterprise Decision Framework covers the operating model test — mapping your specific environment constraints against the architecture that holds at your scale, beyond the ransomware recovery dimension alone.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session