The European Sovereign Cloud is a Hard Fork, Not a Region
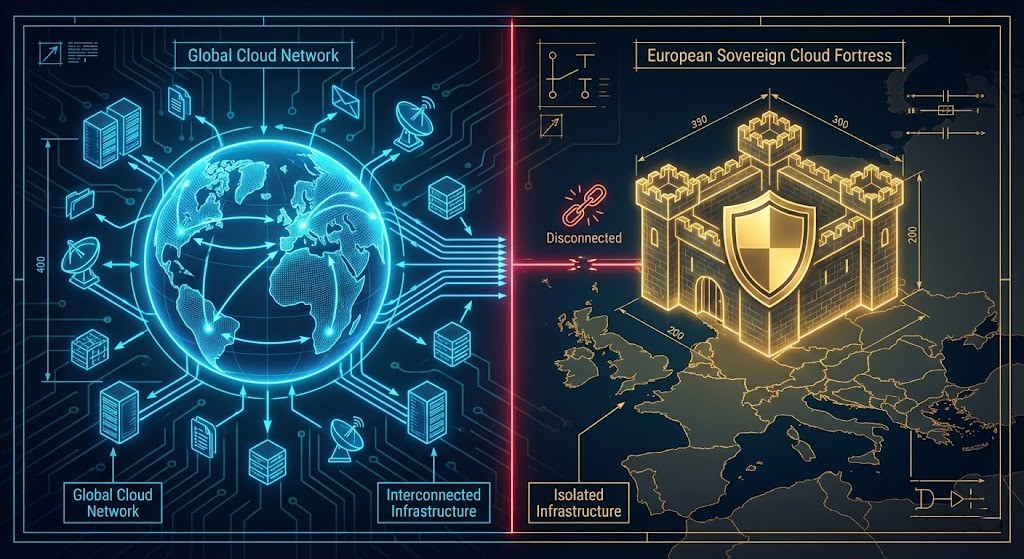
AWS European Sovereign Cloud architecture is not a region you casually select in a dropdown. Stop thinking of the AWS European Sovereign Cloud as “another region in Germany.” Architecturally, aws-eusc is a Partition — a hard fork of the AWS control plane, similar to AWS GovCloud or AWS China. It has its own IAM root, its own billing system, and its own DNS structure.
If you think you can just point your existing Terraform provider to eu-central-2 and deploy, you are going to break your pipeline.
This is a disconnected island. It launches with a massive “Service Gap” (no CloudFront, no Amplify at launch) and carries a 20–30% operational tax because you can’t reuse your global resources. Here is what the architecture actually looks like when you peel back the “Digital Sovereignty” sticker. For how sovereign infrastructure decisions interact with hybrid cloud dependency, see Sovereign Infrastructure Strategy: When Hybrid Cloud Becomes Dependency with Latency.
The End of the Borderless Cloud
I still remember a migration in 2012 — standing in a freezing London data center, trying to explain to a bank CIO that “the cloud” didn’t mean his data would float freely over the Atlantic. Back then, we sold the vision of a borderless control plane. One global identity. One billing engine. One operational universe.
We weren’t lying — but we were definitely naive.
The launch of the AWS European Sovereign Cloud in Brandenburg, Germany marks the formal end of that era. This is not a new region you casually select in a dropdown. It is a hard fork of cloud architecture — legally, operationally, and technically.
For the last decade, compliance was often a checkbox: “Just use eu-central-1 and encrypt everything.” That approach is dead. With confirmed launch customers like EWE AG and Sanoma Learning moving workloads into physically isolated racks, the bar has moved. It is no longer about Data Residency (where the bits live). It is about Operational Sovereignty — who holds the keys, who patches the hypervisor, and whose passport they hold.
AWS European Sovereign Cloud Architecture: It’s Not a Region, It’s a Partition
To design this correctly, you must understand the physics of the environment. This is a “Shared Nothing” partition — architecturally identical to the US GovCloud model. The AWS European Sovereign Cloud architecture decision is fundamentally different from any regional placement decision you’ve made before.
In a standard AWS deployment:
- IAM is global.
- Billing rolls up to a US master payer.
- DNS relies on global Route 53 zones.
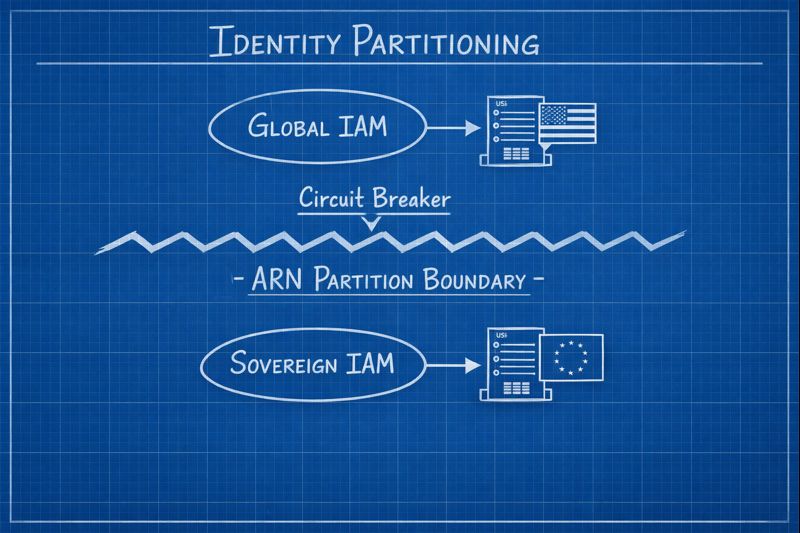
In the Sovereign Cloud (aws-eusc), that umbilical cord is cut:
The Partition Impact Matrix
| Feature | Standard AWS (eu-central-1) | AWS Sovereign Cloud | Architectural Impact |
|---|---|---|---|
| Control Plane | Global | EU-resident, EU-citizen operated | No global failover; separate pipelines required. |
| Identity (IAM) | Global | Isolated Partition | No direct role federation. arn:aws:iam vs arn:aws-iso:iam mismatch. |
| Billing | Aggregated | Separate Legal Entity | FinOps tooling must consolidate multiple invoices. |
| Connectivity | AWS Backbone | Dedicated EU Connectivity | Feels “air-gapped”; requires dedicated interconnects. |
The Architect’s Warning: If your Terraform scripts assume global IAM roles, or if your web app relies on CloudFront (currently unavailable in the sovereign partition), your deployment will fail. Not degrade. Fail.
The Sovereignty Tax: Where the Real Cost Lives
Most organizations obsess over instance pricing (OD vs RI). That is the wrong place to look. The real cost of AWS European Sovereign Cloud architecture is in Operations.
I recently modeled a sovereign migration for a defense contractor. Their biggest shock wasn’t the EC2 premium — it was that their US-based Datadog and PagerDuty instances became legally unusable for the sovereign environment. Metadata could not leave the EU partition.
The Hidden Costs:
- Tooling Duplication: You need a separate CI/CD control plane. You cannot push to
aws-euscfrom a runner inus-east-1without breaking the legal air gap. - Brain Drain: AWS restricts support access to EU residents. If your best database architect is in Seattle, they legally cannot touch production. You must hire duplicate senior talent inside the Eurozone.
- The “Missing Service” Tax: No Amplify? No CloudFront? You are now engineering your own CDNs and static hosting solutions like it’s 2015.
Architect’s Action: Before committing, model this OpEx bloat. Use our Deterministic Tools for a Non-Deterministic Cloud to compare “Global Operations” labor vs. “Sovereign” labor. If the premium exceeds 30%, challenge the compliance team to cite the exact regulation mandating the move. The FinOps framing for this decision is in Cloud Cost Is Now an Architectural Constraint.
Data Gravity Becomes Geopolitical Gravity
Here is the irony: in escaping US jurisdictional lock-in, you accept geopolitical lock-in.
Once data enters the aws-eusc partition, egress is technically easy but legally treacherous. AI training pipelines that assume global data lakes break when datasets cannot legally leave the partition. This is the same data gravity principle covered in The Law of Data Gravity: Why Compute Eventually Moves to the Data — in sovereign environments, gravity becomes law rather than physics.
The “Airbus” Lesson: While many are celebrating, it is telling that Airbus — arguably the target audience for this cloud — has publicly expressed skepticism about whether any US-owned cloud can truly offer immunity from the US CLOUD Act.
This proves the point: Sovereign Cloud is a compliance tool, not a magic shield.
Decision Framework: Do You Actually Need European Sovereign Cloud Architecture?
Zone A — Must Move (aws-eusc)
- Data: NIS2 High Criticality, National Defense, Health Data with strict localization.
- Mandate: Explicit requirement for “Operational Sovereignty” (EU-only staff).
Zone B — Stay Standard (eu-central-1)
- Data: Standard GDPR PII, Commercial IP.
- Need: Full AI portfolio, CloudFront/Edge services, Global Interconnectivity.
If your justification lives in Zone B, moving to the Sovereign Cloud is an unforced error. You are trading agility for a compliance badge that your regulator didn’t ask for. For context on how sovereign vs. public cloud compliance decisions interact, see Sovereign Cloud vs. Public Cloud: Navigating Compliance in a Non-Deterministic Landscape.
Architect’s Verdict
The “one cloud” era is over. AWS European Sovereign Cloud architecture forces modern architects to design for a world where systems span legally distinct cloud partitions. Your job is no longer just optimizing for latency or throughput — you are now optimizing for jurisdiction.
That means abstracting identity providers, designing automation for multi-partition deployment, and never assuming a service available in us-east-1 exists in eu-sovereign-1. The Azure Landing Zone vs. AWS Control Tower post covers the governance hierarchy decisions that become even more critical when operating across partitions.
The Sovereign Cloud is a fortress. Just remember: fortresses are excellent for defense — and notoriously hard to leave.
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session





