Agentic AI Has a Control Plane Problem — Because It Became the Control Plane
Agentic AI control plane governance is the architecture problem most teams are not modeling — and the one that will produce the most expensive failures in 2026.
The control plane became the most sensitive layer in modern infrastructure. So we locked it down.
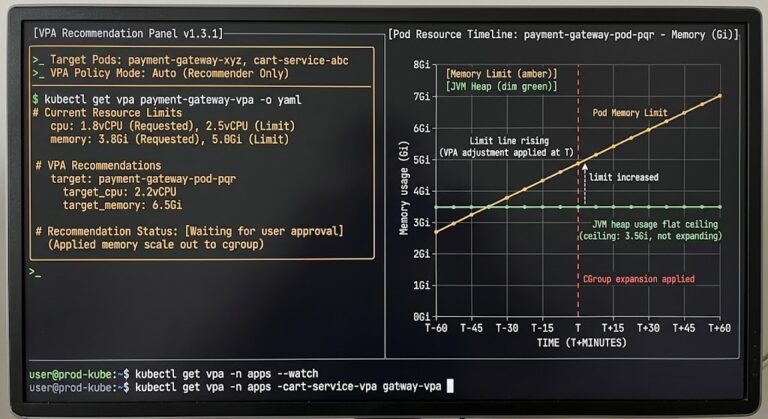
Kubernetes gave us control plane isolation — the API server, etcd, and the scheduler separated from the workloads they govern. IAM gave us least-privilege scoping — execution authority bounded to the minimum required. Cloud architecture gave us blast radius containment — failure domains designed to limit the lateral spread of a single misconfiguration or breach.
We spent a decade building these constraints. They are not theoretical. They are the operational lessons of every infrastructure failure that taught us what happens when execution authority goes ungoverned.
Agentic AI reintroduces the same problem — without the controls.
We Rebuilt an Agentic AI Control Plane and Skipped Every Safeguard
The mapping is direct. Every infrastructure concept that governs how control planes operate has an agentic equivalent. None of them carry the governance model forward.
| Infrastructure Concept | Agentic Equivalent | What’s Missing |
|---|---|---|
| Control plane API | Tool / API invocation | Policy enforcement layer |
| IAM roles | Agent credentials | Scope boundaries, auditability |
| etcd / state store | Memory / vector store | Versioning, governance, access control |
| Orchestrator | Agent runtime | Isolation boundary |
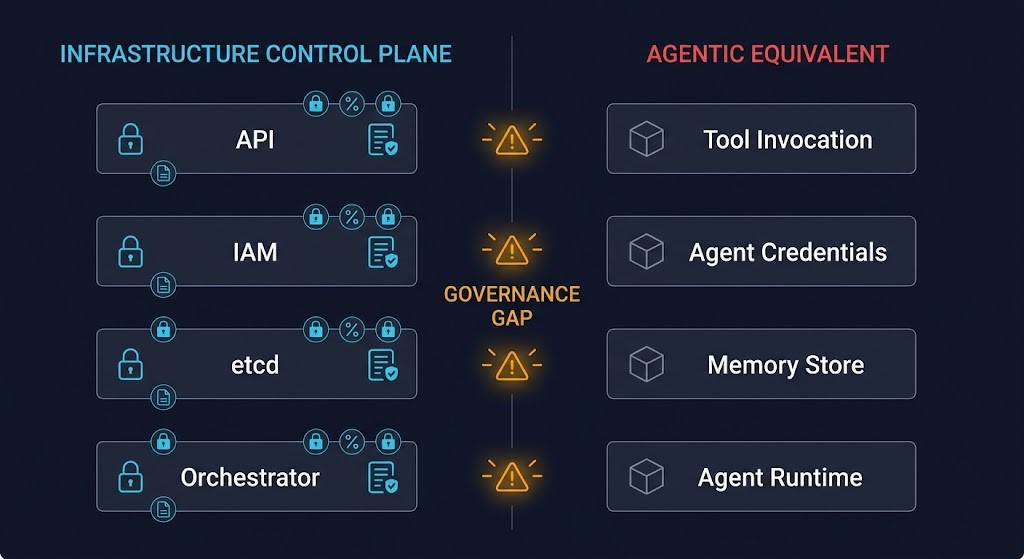
Every column on the right exists in agentic systems today. None of them carry the operational discipline that made the left column safe to run in production.
We spent a decade separating execution from control. Agentic AI collapses that boundary again — and it does it through the same ungoverned layer it always has: the CLI control plane
The Agent Is No Longer an Application
This is where the architecture regression becomes a structural risk.
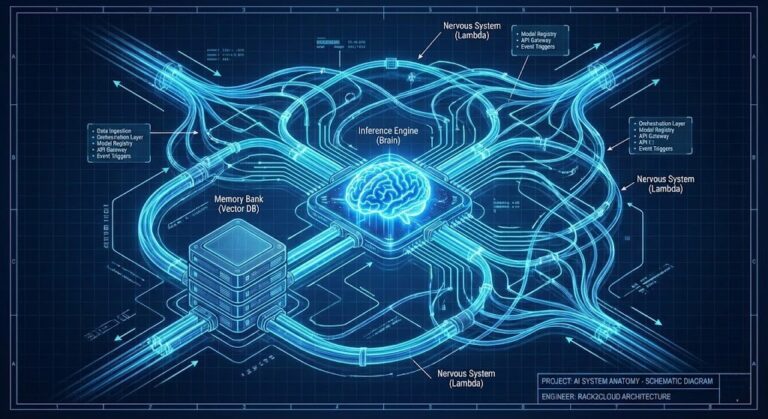
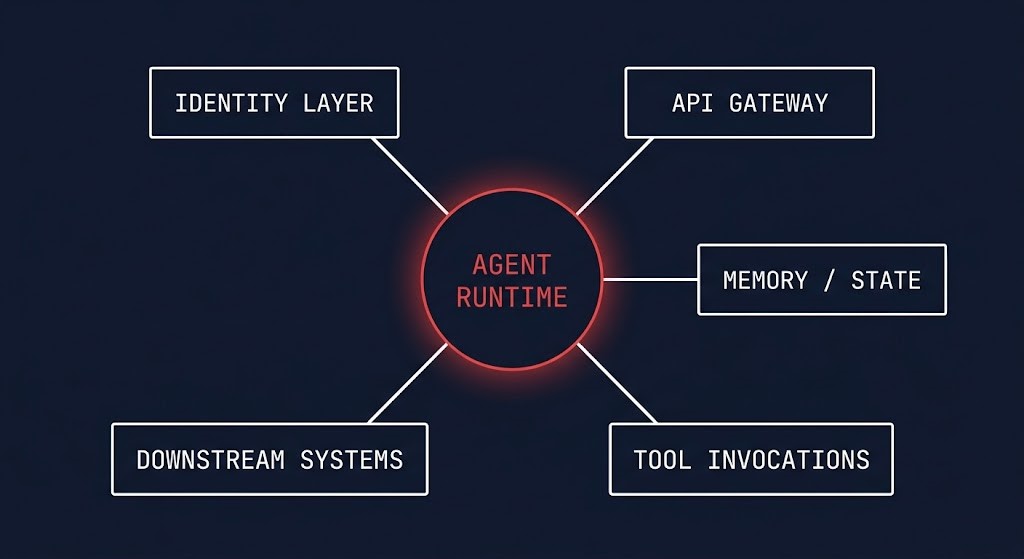
An application calls an API. An agent invokes tools, persists state, chains actions across systems, and makes decisions that trigger further actions — autonomously, at machine speed, across infrastructure it does not own.
That is not an application. That is a control plane with execution authority.
The distinction matters because the entire governance model for applications assumes bounded execution. An application has a defined scope. It calls what it is told to call. It does not decide. An agent decides — and those decisions have downstream effects across every system it can reach.
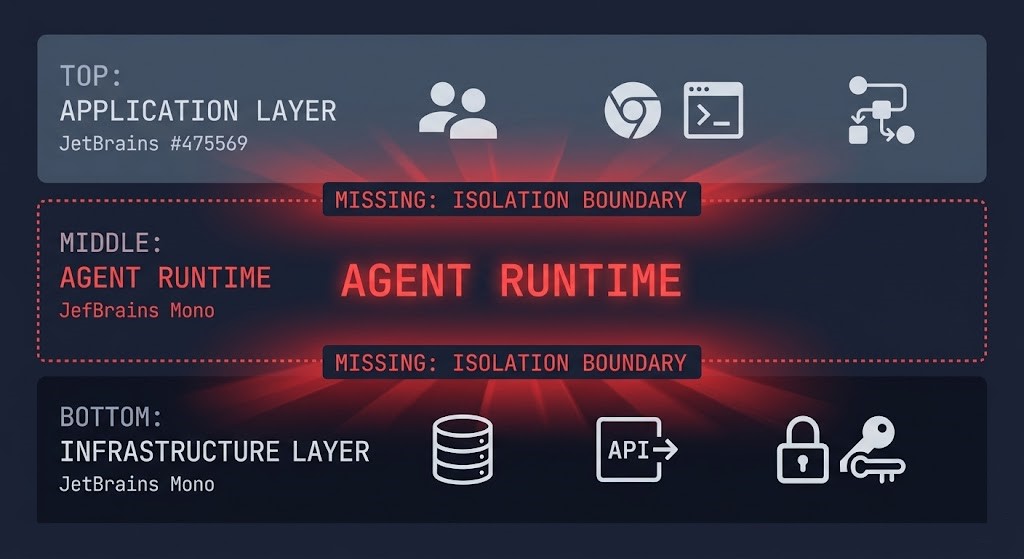
Most teams are treating agentic AI as a new class of application. They are deploying it inside the application layer, scoping its credentials like a service account, and monitoring it with the same observability stack they use for stateless workloads.
This is the architectural mistake. The agent is not operating at application scope. It is operating at control plane scope. And when a control plane runs without isolation, without enforced policy, and without bounded execution authority — you already know how that ends. You’ve seen it at the infrastructure layer. The security boundary that governs what an LLM can invoke before execution reaches your infrastructure is where that containment starts — covered in detail in Kubernetes Is Not an LLM Security Boundary.
The conditions that allow an agent to operate at control plane scope without governance are set before the agent is ever deployed. The inference routing layer, the orchestration runtime, and the observability pipeline it depends on are themselves invisible AI infrastructure operating outside any authority model — the Runtime Authority Vacuum that makes ungoverned agent execution the default rather than the exception.
The authorization boundary problem extends beyond the security layer into runtime identity — when an agent acts, the question of whether that action was ever authorized by a defined identity is covered in The Model Answered. Nobody Asked Who Authorized That.
This class of risk has a name: Unbounded Control Planes — a control plane that can create actions, without enforced policy, across systems it does not own.
Kubernetes failed closed. Agentic systems fail open.
The Four Failure Modes That Only Surface in Production
Credential Amplification
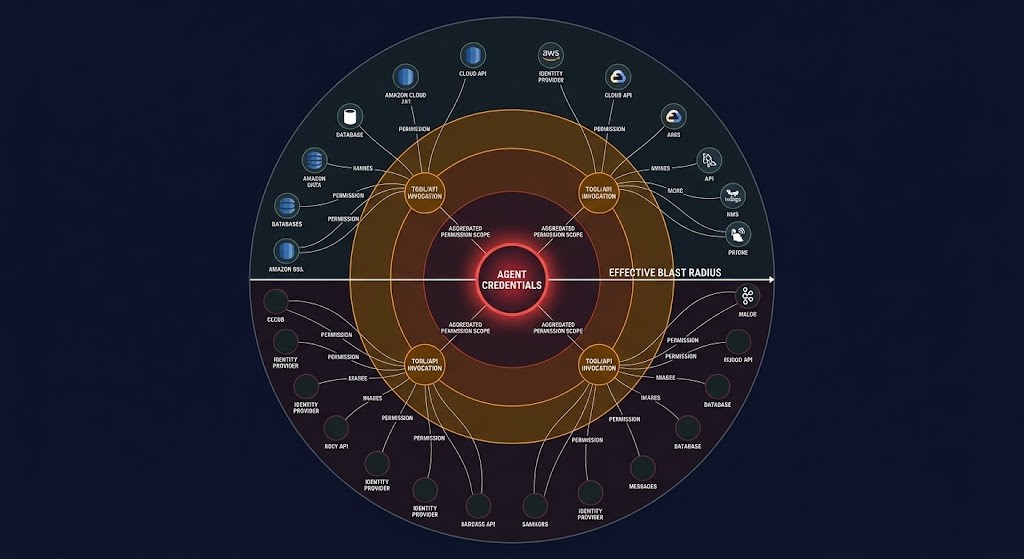
Agents aggregate permissions across every tool they can invoke. The effective access scope is broader than any single IAM role you reviewed at deployment. Blast radius is not the agent’s scope — it is the union of every system it can reach.
Unbounded Execution Chains
One prompt becomes twelve API calls across three systems before a human sees any output. Each step can trigger the next. There is no circuit breaker, no step boundary, no re-evaluation gate. The execution chain is only visible after the damage is already distributed.
State Persistence Without Governance
Agent memory is not a cache. It is a state layer that shapes every future decision. It is not versioned, not scoped, not audited. When it influences a cross-system action six interactions later, the dependency is invisible — until a failure event forces the trace.
No Control Plane Isolation
The agent runtime lives inside the application layer. Its credential scope operates at infrastructure authority. There is no isolation boundary between where the agent executes and what it can modify. The application perimeter does not contain infra-level execution authority.
Each of these failure modes is a direct consequence of deploying an agentic AI control plane without the governance constraints that infrastructure architects learned the hard way.
What Architects Need to Get Right (Before This Breaks in Production)
The answer is not a new security framework. It is the governance model you already built for infrastructure — applied deliberately to a layer that is behaving like infrastructure whether you designed it that way or not.
1. Treat Agent Credentials as Control Plane Credentials
If an agent can invoke APIs, it holds infrastructure authority — not application scope. No shared tokens. No implicit trust. Scoped, auditable, revocable — the same standard you apply to anything that can modify state at the infrastructure layer.
Agent identity is not app identity. It is control plane identity.
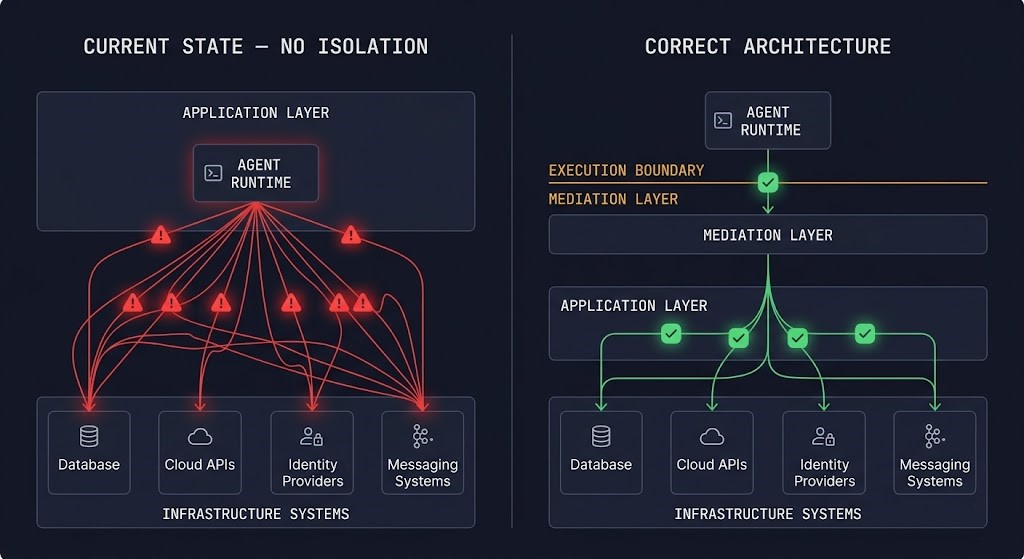
2. Isolate the Agent Runtime from the Systems It Controls
An agent should not operate inside the same blast radius as the resources it can modify. The execution boundary needs to be explicit — separate runtime, no direct lateral access, mediation layer between the agent and the systems it reaches.
If the agent lives inside your application layer, your control plane is already compromised.
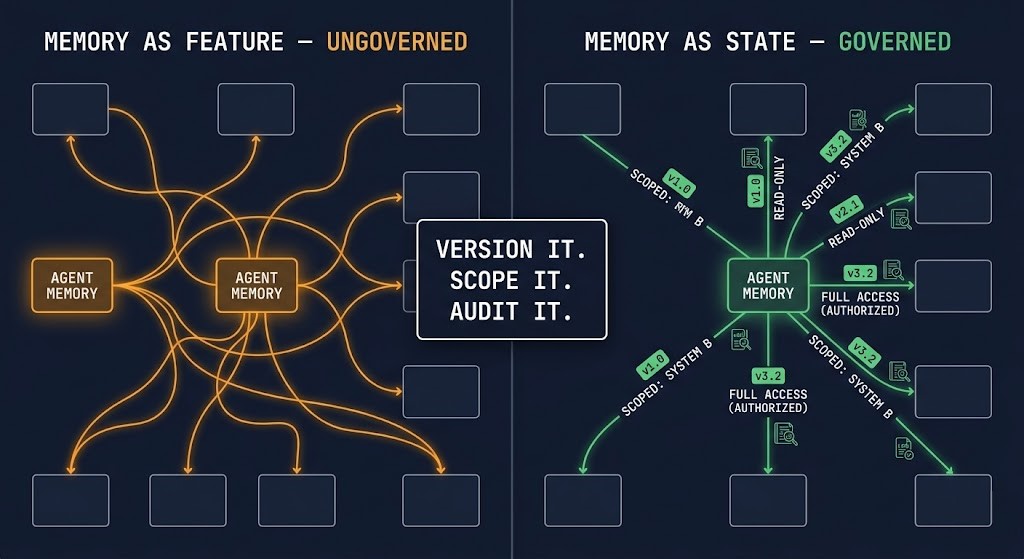
3. Govern Memory as State — Not as a Feature
Persistent memory is not context. It is a state layer that influences future actions across systems. Version it. Scope it. Audit it. Apply the same governance you would apply to any state store that participates in cross-system decision-making.
Unbounded memory creates untraceable behavior.
4. Constrain Execution — Agents Should Not Chain Without Boundaries
The risk is not a single action. It is the accumulation of actions across systems without re-evaluation gates. Limit tool chaining. Enforce step boundaries. Require explicit re-evaluation before an agent proceeds across a system boundary.
Unbounded execution is how small decisions become systemic failures.
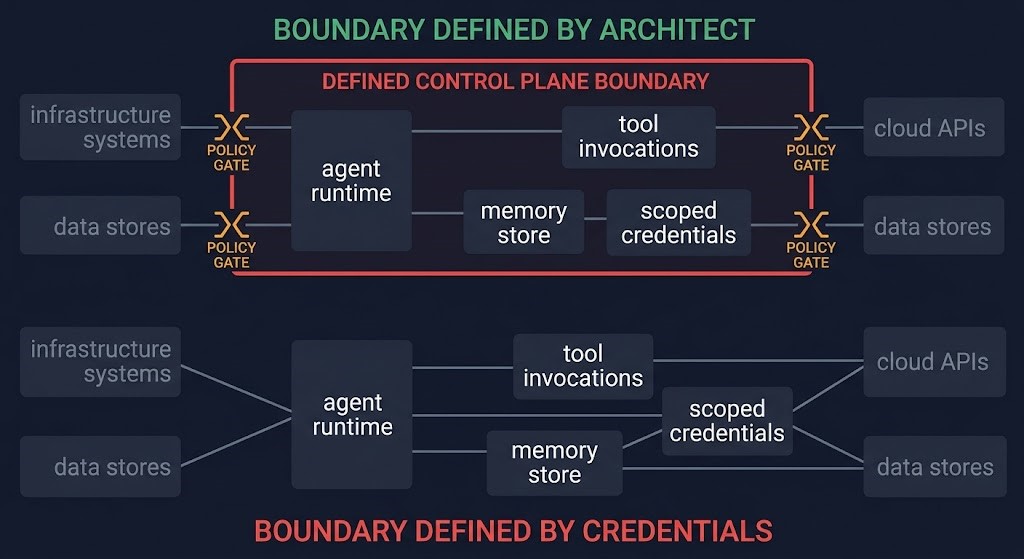
5. Reintroduce the Control Plane Boundary — Explicitly
Define where the agent’s authority begins and ends before deployment, not after the first production incident. If you do not define the boundary, the agent will — and it will define it as broadly as its credentials allow.
We did not lose control of infrastructure because systems became complex. We lost control when we stopped enforcing boundaries. Agentic AI removes those boundaries by default. Architects need to put them back — deliberately.
Architect’s Verdict
The agent is your agentic AI control plane.
If your agent can take action across systems, it is part of your control plane — whether you designed it that way or not. The governance model, the isolation requirements, the credential discipline — none of that is optional at control plane scope. You already know this. You built it once. The only question is whether you apply it again before production forces the lesson.
Additional Resources
This post is the framework. These are the deeper dives.
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session