Infrastructure as a Software Asset: Why Your Data Center Needs a CI/CD Pipeline
Executive Summary
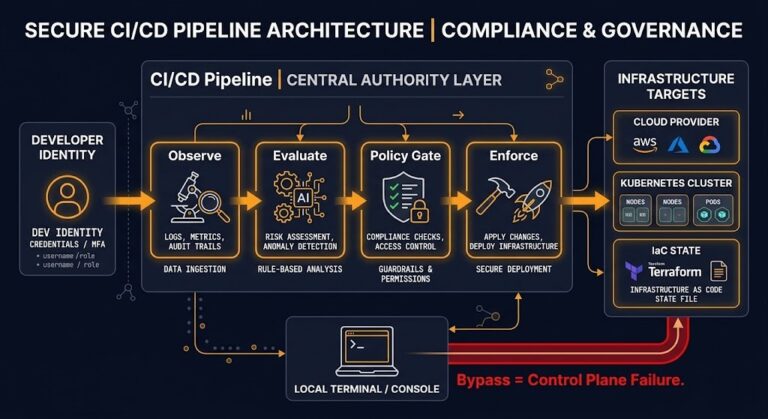
Infrastructure as a Software Asset means treating your data center like a codebase. If you’re spinning up infrastructure with an API but then managing it with a CLI, you’re not really doing Infrastructure as Code.
For years, people treated data centers like big rooms full of hardware. You are accelerating legacy IT without eliminating its entropy. The second your hypervisor has a REST API, your switches take programmable configs, or your identity provider connects through federation—your infrastructure stops being just hardware. It becomes code.
And once that happens, you have to play by software engineering rules: version control, peer reviews, automated tests, builds you can repeat, and states you can always recover. Anything less is just theater.
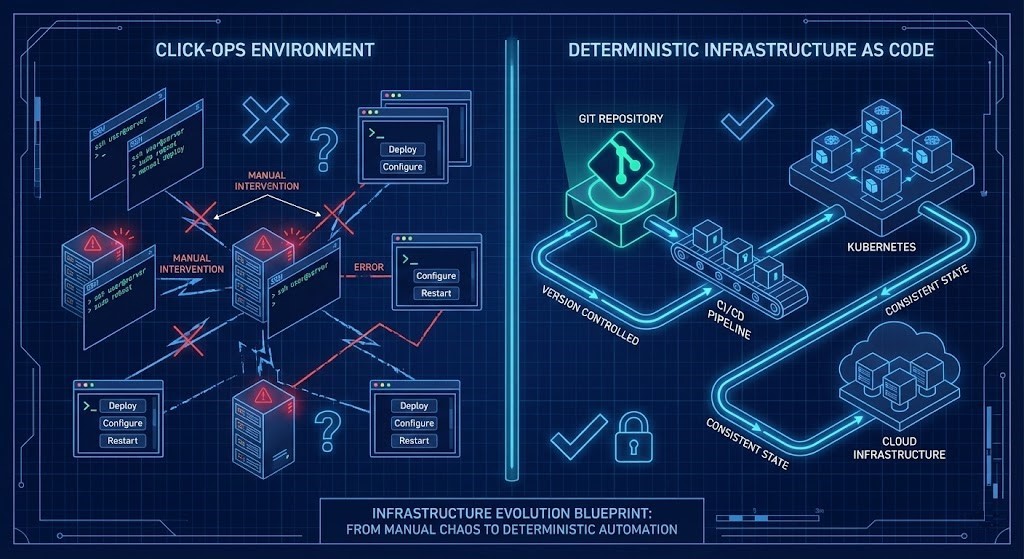
The End of the Snowflake Data Center
Handcrafted, SSH-tuned “snowflake servers” don’t show expertise anymore. They’re just risks.
Even if you’re racking up physical gear, you’re running it through control planes and APIs. APIs make your environment a software system. The problem? Most companies grab cloud-native tools but hang onto old habits:
- Manual console changes during an outage.
- Direct
kubectl applyin prod. - SSH hotfixes.
- “Temporary” firewall rules that stick around forever.
None of that is Infrastructure as Code. It is configuration drift masquerading as agility. Snowflake systems are not merely technical debt—they are recovery liabilities that expand your blast radius under failure.
The CLI Fallacy
Just because you use an API to set things up doesn’t mean you’re running things with code. Teams brag about having IaC because Terraform built their cluster. But look at what happens after launch:
- People make changes in web consoles.
- Emergency CLI fixes never touch Git.
- RBAC policies change on the fly.
- Network policies get patched live.
Every manual command you run in production is an untracked fork of reality. If there’s a config in prod that’s not in Git, that’s not infrastructure—it’s just someone’s memory.
Automation vs. Determinism
It is dangerous to confuse basic automation with true engineering discipline. While standard automation simply executes a configuration change across your entire environment, determinism mathematically guarantees that your infrastructure state is exactly reproducible every single time.
A Bash script can automate chaos. A CI/CD pipeline enforces the state you declare. That’s a huge difference.
Deterministic infrastructure means you declare, version, review, test, and automatically apply your state. This is where GitOps stops being a buzzword and actually controls entropy.
Immutability Is Entropy Control
Patching a live system is mutation. Mutation causes drift. Immutability kills mutation and brings controlled regeneration.
If you need to change a firewall rule:
- Update the code.
- Commit it.
- Let someone review it.
- Run the pipeline.
- Replace the state.
No live edits. No hidden changes. Drift isn’t just annoying—it’s the start of architecture rot. (See our deep dive on Managing Configuration Drift to stop this decay).
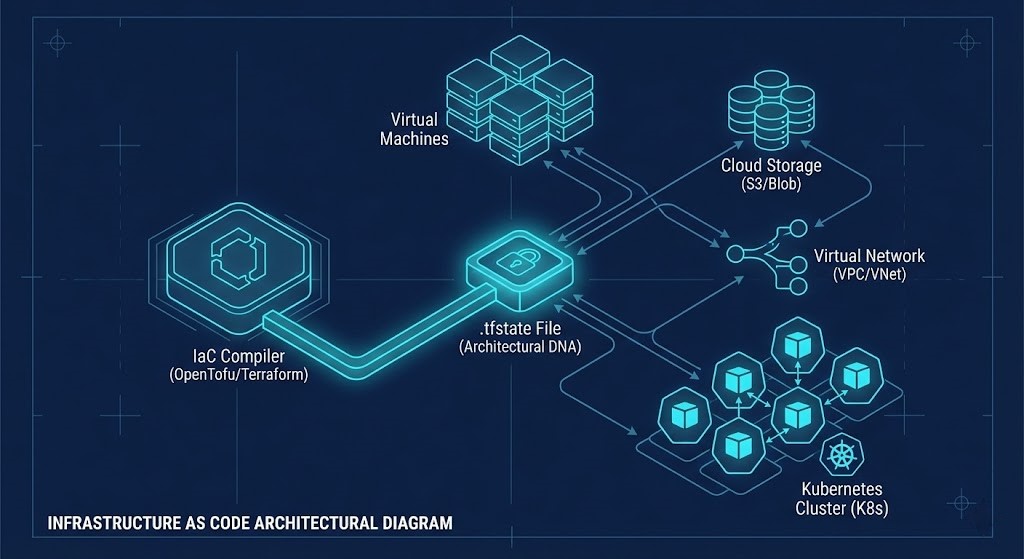
The Compiler Risk: Who Owns Your Engine?
A compiler defines the boundaries of architectural freedom. If infrastructure is software, then your IaC engine is your compiler. Whoever controls that compiler controls your upgrade path, your compatibility matrix, and ultimately your architectural sovereignty.
When Terraform changed its license, infrastructure leaders learned this the hard way. If a vendor can change your legal or operational terms overnight, you’re not really in charge. Open-source compilers like OpenTofu put determinism back in your hands.
This isn’t about open-source ideology. It’s about control. If you can’t fork your compiler, manage your upgrades, or own your state engine, you’re not in control of your infrastructure lifecycle.
The State File Is Architectural DNA
That state file isn’t just metadata. It holds resource IDs, dependencies, destructive operation maps, and drift reconciliation info. It’s basically your data center’s genome.
If your state file lives in someone else’s proprietary SaaS, you’ve handed over the keys to your kingdom. Real infrastructure control starts with owning your state.
>_ Action Step: Audit your HCL configs for licensing drift and check your compiler exposure using our OpenTofu Readiness Bridge in the Engineering Toolkit.
Kubernetes Day-2: Reconciliation as Enforcement
Kubernetes isn’t just a container runtime. It’s the smartest reconciliation engine out there. Spinning up a cluster is the easy part. Keeping it in line after launch? That’s where things fall apart.
Trouble creeps in with RBAC sprawl, misaligned volumes, ingress drift, and manual kubectl fixes. If incident response requires direct kubectl mutation, your control plane is advisory—not authoritative.
Real Kubernetes as Code—a methodology we operationalize in our Kubernetes Day 2 Operations Guide: The Rack2Cloud Method—means RoleBindings live in Git, NetworkPolicies are versioned, StorageClasses go through pipelines, and admission policies are enforced in code.
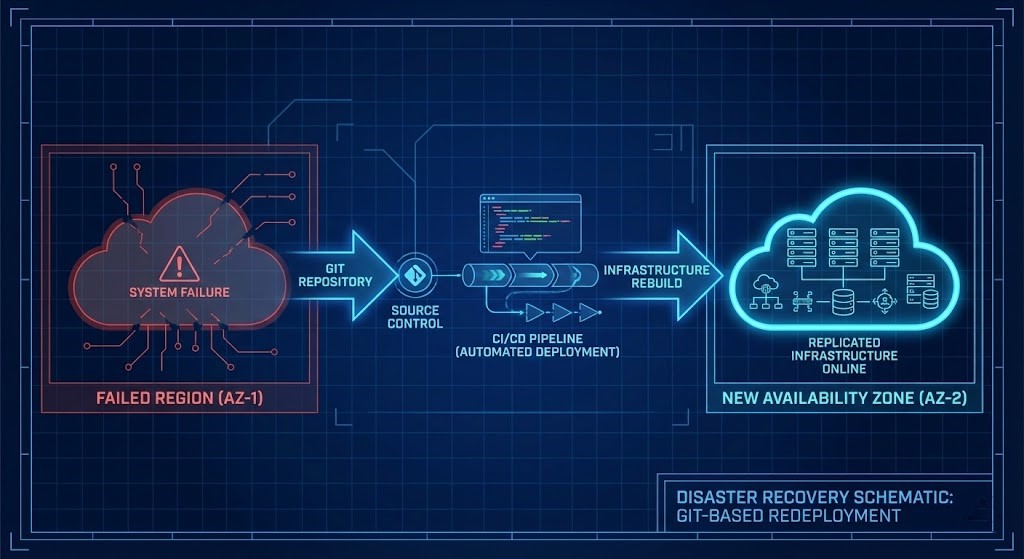
Control Plane Survivability: The Real ROI of IaC
Organizations justify Infrastructure as Code with speed. But speed is merely a side effect. The real value is recoverability.
Consider adversarial scenarios: an identity provider compromise, a root certificate revocation, a cloud region outage, or an unauthorized mutation to your control plane (which is why we mandate the workflows outlined in Deterministic IaC Pipelines: Turning Terraform Plans into Signed Contracts Between Security and Operations. How long does it take to rebuild?
- If your infrastructure is a software asset stored in a secure repository, MTTR equals pipeline execution time.
- If your infrastructure lives in consoles, CLIs, and human memory, MTTR equals guesswork.
Your Git repository is not documentation. It is your lifeboat.
The Engineering Toolkit Integration
Deterministic architecture requires measurable exposure. To operationalize this model, stop guessing and start auditing. Leverage the Rack2Cloud Engineering Toolkit to validate your supply chain:
- Sovereign Drift Auditor: Quantify unmanaged drift and audit your
terraform plan.jsonfor unencrypted storage or non-sovereign configurations. - Terraform Lag Tracker: Assess roadmap and licensing risk by tracking delays between Cloud API releases and proprietary provider support.
- OpenTofu Readiness Bridge: Generate migration templates to safely move your state engine back in-house.
Modern infrastructure is not built. It is compiled.
Conclusion
Infrastructure is either a versioned, deterministic software asset, or a fragile collection of human interventions. If you provision via API but manage via CLI, you do not have Infrastructure as Code. You have accelerated legacy IT.
And accelerated entropy still collapses.
Continue the Path
This article is part of the Modern Infrastructure & IaC Strategy Guide. To master the adjacent layers of a deterministic enterprise architecture, explore our other strategic pillars:
Additional Resources
- The OpenTofu Manifesto (Linux Foundation): Read the industry-wide response to the Terraform Business Source License (BSL) change.
- OpenGitOps Principles (Cloud Native Computing Foundation): Review the official, vendor-neutral standards for GitOps.
- DORA State of DevOps Report (Google Cloud / DORA): Dive into a decade of industry-standard research.
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session