The CLI Was Always the Control Plane. Now It’s Being Handed to Machines.
The CLI control plane is the most powerful — and least governed — layer in most enterprise infrastructure stacks.
Most infrastructure changes don’t happen in dashboards.
They happen in terminals.
The UI is where you observe. The CLI is where you commit. A console shows you a representation of state. A CLI invocation changes it — directly, immediately, with no intermediate abstraction layer between your intent and the infrastructure API.
That distinction is not academic. It is the difference between an environment you can govern and one you think you can govern.
The CLI Control Plane Is the Last Honest Layer
Every modern infrastructure platform ships with a console. Consoles are useful. They visualize state, surface metrics, and make complex systems navigable for teams without deep operational knowledge. But consoles are eventually consistent by design. They show you what the system last reported, filtered through an abstraction layer that is optimized for readability, not accuracy.
The CLI doesn’t describe infrastructure. It changes it.
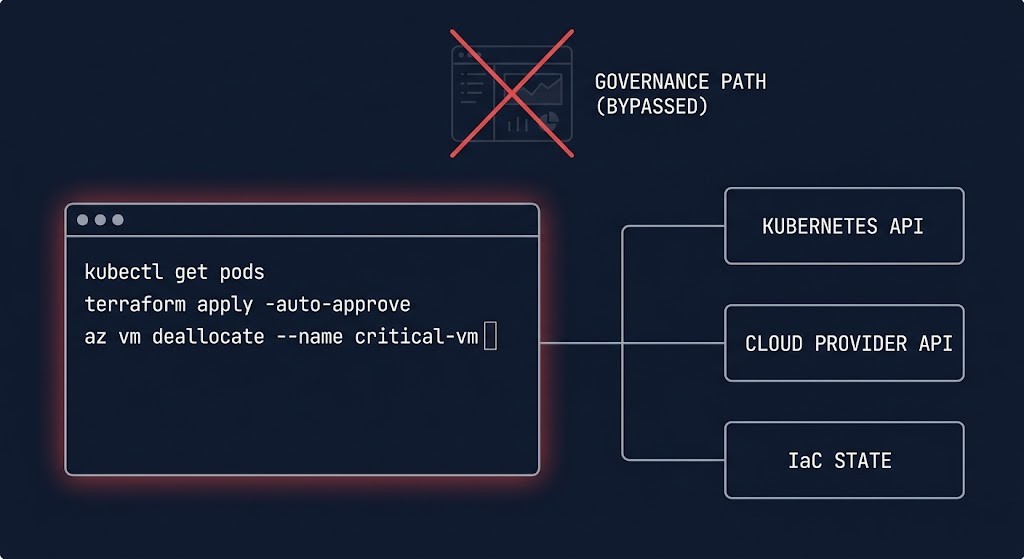
kubectl delete pod does not describe a deletion. It invokes the API. The pod is gone before the console refreshes. az vm deallocate does not suggest a deallocation. It executes one. terraform apply does not propose a state change — it commits it, against the actual infrastructure, with immediate effect.
This is why the CLI is the last honest control plane. It operates at the layer where intent becomes action, where the governance model either holds or it doesn’t, where the distance between a command and a production impact is measured in milliseconds.
That makes the CLI control plane the most accurate layer in your stack — and the most dangerous one to leave ungoverned.
The Illusion of Governance
Most organizations believe their governance model covers the CLI control plane. It doesn’t.
IAM policies govern what identities can do — but they don’t govern what engineers do with the credentials they hold. Approval workflows govern changes submitted through ticketing systems — but they don’t fire when someone runs a script from a local terminal. Dashboard-enforced constraints govern UI-initiated actions — but CLI invocations route directly to the API and bypass UI-layer guardrails entirely.
Your governance model assumes people use the console. Your outages prove they don’t.
The gap shows up in four specific patterns, and most teams have at least two of them running in production right now:
Credential leakage — local config files, environment variables, cached tokens sitting in .aws/credentials, .kube/config, shell history. Credentials that were scoped correctly at issuance and are now ambient in a developer’s local environment with no rotation, no audit, and no expiry enforcement.
Untracked execution — CLI commands run outside any pipeline have no audit trail tied to intent. You can reconstruct what happened from API logs. You cannot reconstruct why. The decision context is gone the moment the terminal closes.
Script drift — shell scripts that started as one-time fixes and became operational procedures. Nobody owns them. Nobody versions them. They embed credentials, assume environment state, and represent infrastructure decisions that exist nowhere in your IaC. Shadow control planes running as .sh files in someone’s home directory.
Bypassed guardrails — the constraints that exist in your console and ticketing workflows simply do not apply at the CLI layer. A UI might require a change ticket before allowing a security group modification. The CLI requires a credential. If the credential exists, the change executes.
And Just as We’re Realizing This, Something Changes
The patterns above are not new. Senior engineers have known about them for years. The reason the CLI governance problem is suddenly urgent is not that the problem got worse — it is that the execution surface changed.
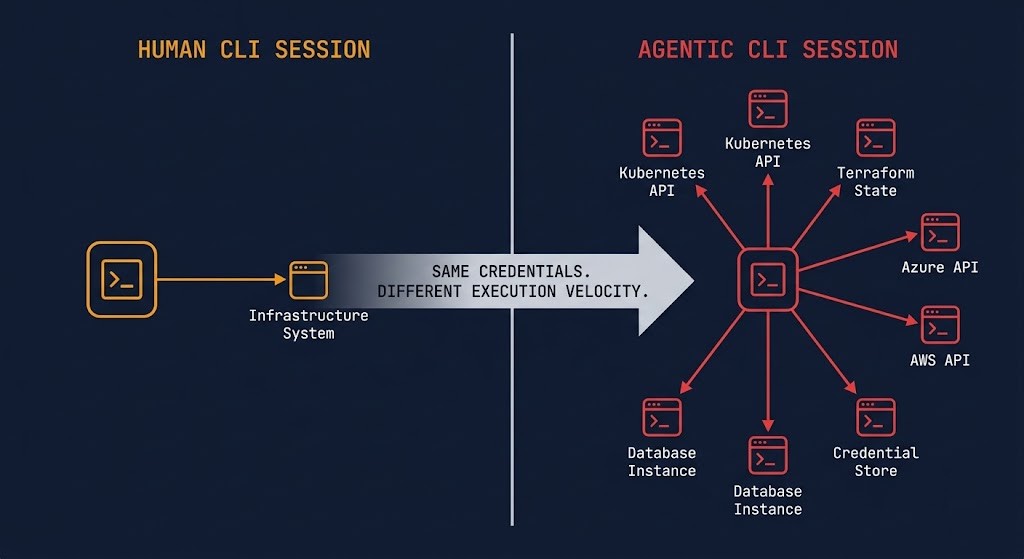
Claude Code. GitHub Copilot CLI. Agentic terminals that can read context, plan a sequence of actions, and execute them. Tools that can take a natural language instruction and translate it into a sequence of CLI invocations — kubectl, terraform, az, aws, gcloud — across multiple systems, in a single session, without a human reviewing each step.
The CLI is no longer just a human interface. It is becoming an execution surface for systems that can act.
We didn’t secure the CLI when humans were using it. Now we’re letting machines use it. And the boundary that governs what those machines can invoke starts before the terminal — at the LLM security boundary that most Kubernetes teams aren’t modeling.
The blast radius of an ungoverned CLI session scales with the credentials it holds. A human engineer with broad permissions makes one bad decision at a time. An agentic system with the same credentials can chain twelve API calls across three systems before a human sees any output. The credential scope didn’t change. The execution velocity did.
The Boundary Between Intent and Execution
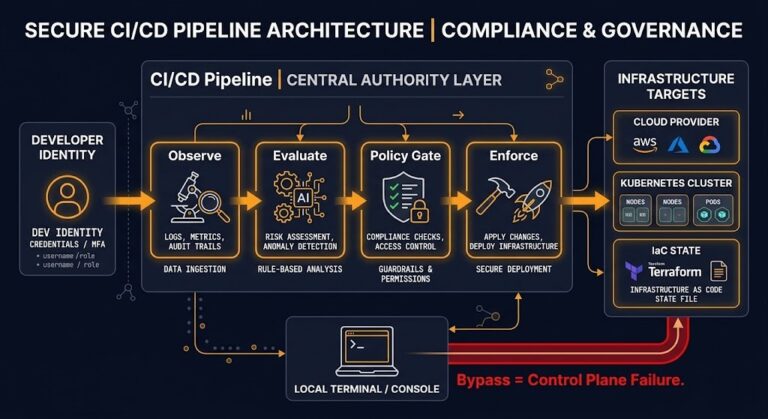
The CLI control plane is where decisions become actions. In every infrastructure governance model worth its name, that boundary is explicit — policy enforced, actions logged, scope bounded, execution isolated from the systems it governs.
The CLI collapses that boundary into a prompt and a terminal. No mediation layer. No policy gate. No isolation boundary between where the command runs and what it can reach.
Fixing this is not a new framework problem. It is applying what you already know about control plane governance to the layer that has always operated outside it.
Treat CLI credentials as control plane credentials. Scope them. Rotate them. Audit them. Run pipelines instead of local scripts wherever the action has production impact. Version the scripts that remain. Build the audit trail into the execution path, not the postmortem.
And when you extend the CLI to agentic systems — define the boundary first. Explicitly. Before deployment.
Architect’s Verdict
The CLI didn’t become the control plane. It always was.
We just treated it like a tool instead of a boundary. Now it is being integrated into automated workflows and agentic systems — without the isolation, governance, or constraints we expect from any other control plane layer.
If your CLI can modify infrastructure, it is part of your CLI control plane. And right now, most control planes are running on laptops.
Additional Resources
This post is the framework. These are the deeper dives.
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session