3-2-1-1-0 Backup Rule: Modernizing Protocols for 2026 Cyber-Resilience
The 3-2-1-1-0 backup rule represents the architecture shift from legacy redundancy to adversarial resilience. The traditional 3-2-1 strategy was designed to solve for hardware failure — the 3-2-1-1-0 extension is engineered to solve for adversarial intent. In a landscape where 94% of ransomware attacks now specifically target the backup server, a “copy” is no longer a recovery asset unless it is cryptographically or physically isolated from the production plane. This is the threat model behind designing backup systems for an adversary that knows your playbook.
The 3-2-1-1-0 Backup Rule: Breaking Down the Final Two Digits
The leap from “Standard Backup” to “Cyber Resilience” happens in the final two digits of the protocol. This framework is a core component of our Cloud Learning Path, where we move from legacy redundancy to modern deterministic recovery.
- 3 (Copies of Data): Maintain three distinct instances of data—the primary production data and two backup copies.
- 2 (Different Media Types): Store copies on at least two disparate storage technologies. For hybrid architects, this often means splitting data between local NVMe and S3-compatible object storage.
- 1 (Off-site Copy): Geographically separate at least one copy to safeguard against localized physical disasters.
- 1 (Immutable or Air-Gapped): This is your Last Line of Defense. Modern immutability is enforced through S3 Object Lock or WORM (Write Once, Read Many) protocols that prevent deletion, even if admin credentials are compromised. Object Lock enforcement goes deeper than most teams configure — Compliance Mode and Governance Mode are not equivalent.
- 0 (Zero Errors / Verified Recovery): This represents Recovery Assurance. Verification must move from simple success logs to automated, script-based testing where VMs are booted in an isolated sandbox. The restore path is the most neglected part of backup design — the “0” is where that neglect becomes visible.
WORM (Write Once, Read Many): A data storage technology that allows data to be written to a storage medium once and prevents the data from being erased or modified. Air-Gap: A security measure that ensures a secure computer network is physically isolated from unsecured networks, such as the public internet or an unsecured local area network.
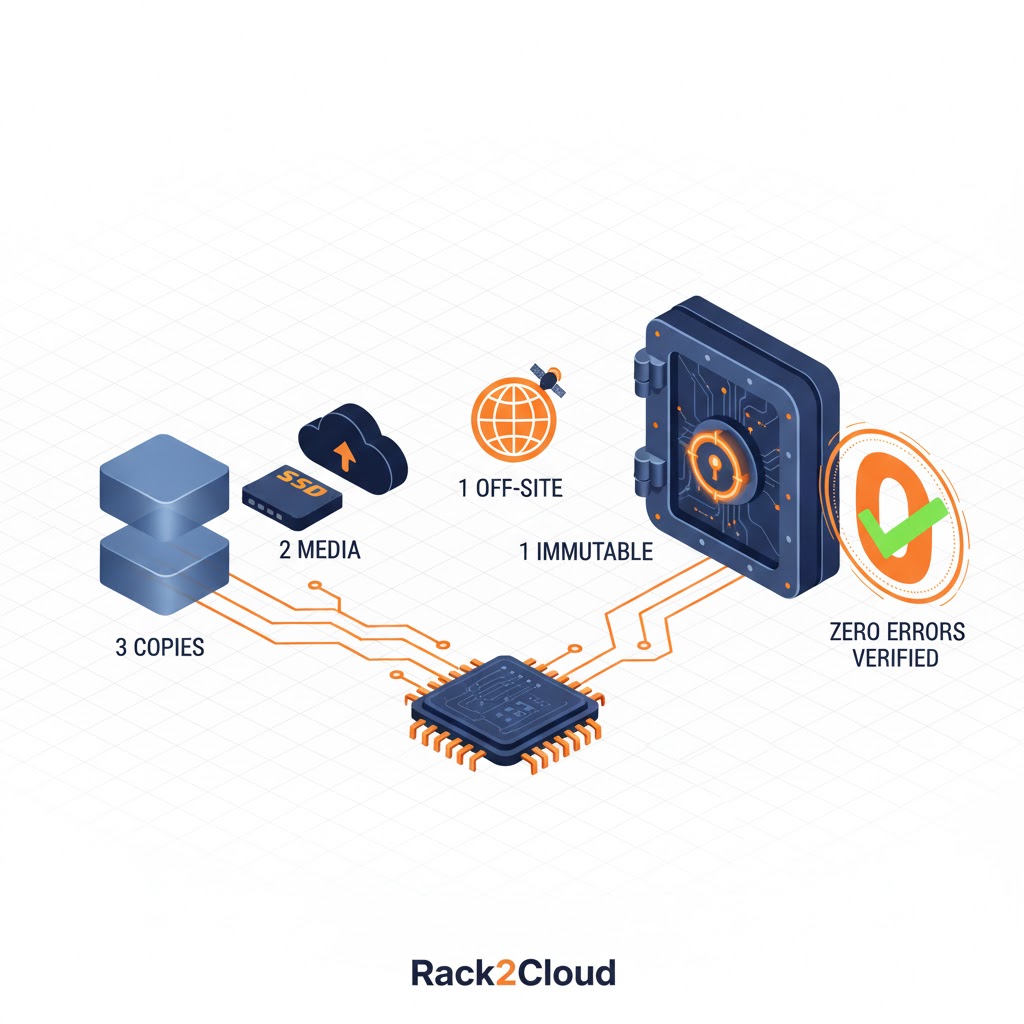
Image 1: 3-2-1-1-0 Backup Rule
Deep Dive: Competitive Immutability Architecture
Architects must distinguish between software-defined locks and hardened, immutable file systems.
| Platform | Mechanical Implementation of the “1” | 2026 Technical Distinction |
| Nutanix Objects | S3 Object Lock (Compliance Mode) | Native to AOS; leverages WORM buckets to prevent deletion even by a Cluster Admin. |
| Veeam Hardened Repo | Linux XFS Immutability | Uses the i attribute at the file system level to prevent modification of VIB/VBK files. |
| Cohesity | SpanFS + Helios | A distributed file system that uses a strict read-only snapshot architecture with DataLock. |
| Rubrik | Atlas File System | Custom, purpose-built file system that is “immutable by design.” |
Nutanix Objects: Native S3 Compliance
For organizations running Nutanix AHV in production, Nutanix Objects provides a deterministic path to 3-2-1-1-0 by utilizing native S3 Object Lock in Compliance Mode. Even if a bad actor gains access to the Nutanix Prism console, the underlying storage blocks cannot be reclaimed or overwritten until the retention timer expires.
Veeam: The Linux Hardened Repository (LHR)
Veeam addresses the “1” by leveraging the immutability flag within the Linux XFS file system. It uses the chattr +i attribute to lock backup files locally, utilizing non-root users and limited permissions. For the “0” factor, Veeam SureBackup remains an industry standard, automating heartbeat and application tests in a Virtual Lab. For a deeper comparison of how Veeam’s recovery verification stacks up against other enterprise platforms, see how enterprise backup platforms fail differently.

Platform-Specific Fiscal Logic (1PB TCO)
Managing the costs of these resilience tiers requires more than licensing math. Before modeling platform-specific TCO, it’s worth understanding what your backup costs actually include — most estimates miss rehydration, verification overhead, and media refresh cycles entirely.
- Nutanix Objects (The Sunk Cost Advantage): For shops already running AOS, the TCO for immutability is significantly lower as physical infrastructure is already accounted for. You avoid the “Infrastructure Silo Tax” of buying separate hardware.
- Veeam (The Flexibility Model): Veeam allows you to build a high-performance 3-2-1-1-0 stack using commodity hardware, lowering upfront CapEx. This is a common entry point in our Virtualization Learning Path.
- Rubrik (Premium Peace of Mind): While acquisition costs are higher, TCO shines in labor reduction. Automated malware scanning can reduce the need for a dedicated Backup Administrator by up to 50% and may lower cyber insurance premiums.
- Cohesity (Data Consolidation): SpanFS allows you to use one platform for both 3-2-1-1-0 backups and production NAS, splitting hardware costs across departments.
Strategic Recommendation: The “Sweet Spot”
Selecting the right platform for the 3-2-1-1-0 backup rule depends on scale, existing infrastructure, and recovery complexity — not vendor marketing. Here’s how the decision maps by environment size.
- Under 250TB (Nutanix Shop): Stick with Nutanix Objects. The lack of a new “silo” provides the best TCO and operational consistency.
- 250TB – 1PB (Heterogeneous): Veeam is the architectural winner. It allows you to build a high-performance stack using your choice of server hardware.
- Over 1PB / Zero-Trust Focus: Move to Rubrik or Cohesity. At this scale, global deduplication and AI-driven “0 Error” verification provide better ROI as recovery complexity outpaces human management capacity. For a direct architectural comparison of both platforms under ransomware pressure, see Rubrik vs Cohesity.
Architect’s Verdict
The 3-2-1-1-0 backup rule isn’t an upgrade to your backup strategy. It’s a replacement of your threat model. The original 3-2-1 assumed hardware fails randomly. The 1-0 extension assumes an adversary is actively trying to destroy your recovery path. If your immutable copy lives on the same credential plane as production, it isn’t immutable — it’s just a copy with a longer name.
- ✓ Enforce the immutable copy on a separate credential plane — not just a separate bucket
- ✓ Automate the “0” — boot VMs in an isolated sandbox, not just verify log success
- ✓ Match your immutability mechanism to your scale — Nutanix Objects under 250TB, Veeam LHR for heterogeneous mid-range, Rubrik/Cohesity above 1PB
- ✓ Use S3 Object Lock in Compliance Mode — Governance Mode can be overridden with admin credentials
- ✓ Treat the “0” as an architecture gate — no unverified backup counts toward your 3-2-1-1-0 posture
- ✗ Treat S3 Object Lock in Governance Mode as immutable — it isn’t
- ✗ Count your backup server as one of the “2 media types” — it’s the first target
- ✗ Assume admin credential compromise won’t reach your immutable copy — design as if it will
- ✗ Let the “0” mean “backup job completed” — it means “recovery was verified in isolation”
- ✗ Conflate off-site with air-gapped — geographic separation without credential separation is not an air gap
Additional Resources
Editorial Integrity & Security Protocol
This technical deep-dive adheres to the Rack2Cloud Deterministic Integrity Standard. All benchmarks and security audits are derived from zero-trust validation protocols within our isolated lab environments. No vendor influence.
Get the Playbooks Vendors Won’t Publish
Field-tested blueprints for migration, HCI, sovereign infrastructure, and AI architecture. Real failure-mode analysis. No marketing filler. Delivered weekly.
Select your infrastructure paths. Receive field-tested blueprints direct to your inbox.
- > Virtualization & Migration Physics
- > Cloud Strategy & Egress Math
- > Data Protection & RTO Reality
- > AI Infrastructure & GPU Fabric
Zero spam. Includes The Dispatch weekly drop.
Need Architectural Guidance?
Unbiased infrastructure audit for your migration, cloud strategy, or HCI transition.
>_ Request Triage Session





